1.任务介绍
使用C语言编写一个程序实现如下功能:
- 超级终端或第三方的串口通讯软件进行RS-232通讯,由编写的程序向超级终端或第三方软件进行信息数据的发送,发送的内容见:附件1. 测试信息明文.txt;
- 向超级终端或第三方软件发送的信息数据,使用SHA-256计算信息数据的HASH值,信息数据 + HASH使用AES_ECB - 128算法加密后发送;加密发送的信息保存为:附件2. 测试信息密文.txt;
- 加密的初始化向量值为全0,使用的密钥值为:xxxxxxxxxxxxxxxxxxx(这里我就忽略了)
- 由编写的程序接收超级终端或第三方软件发送的信息数据,超级终端或第三方软件发送的信息数据长度不少于32字节,无需加密;
- 上述程序运行结果以及超级终端或第三方软件接收、发送的信息进行截图;
测试任务要求:
- C语言编写,代码编写要清晰、明了;
- 可以在WINDOWS下或者LINUX下编写编译;
- 附件1. 测试信息明文.txt中的测试信息数据是1024字节,请不要做任何的修改;
- 上述软件功能的第4点为可选项,即加分项;
2.知识点
1.超级终端(或串口软件)
电脑上的 “翻译官”+“聊天框”,帮你把文字变成设备能听懂的信号,或者把设备的信号翻译成你能看懂的文字。
2.串口
设备之间传消息的 “小路”,用几根线就能让设备互相 “递纸条”,简单、省钱,适合距离不远或者设备简单的场景(比如单片机、工业仪表)。
3.在单台电脑上实现串口通信
通过软件创建虚拟串口对(如 COM1↔COM2 或 /dev/ttyS0↔/dev/ttyS1),程序发送数据到一个端口,另一个端口就能接收,模拟两台设备通信。
参考文章虚拟串口 VSPD 的使用_vspd使用教程-CSDN博客
4.使用SHA-256计算信息数据的HASH值
需要用 SHA-256 计算原始数据的指纹,然后把「原始数据 + 指纹」一起用 AES 加密发送。
这样做的好处是:
接收方解密后,可以用同样的 SHA-256 算法重新计算指纹,对比是否和发送的一致,从而确保数据在传输过程中没被篡改。
参考文章SHA-256 哈希算法详解_sha256-CSDN博客
5.信息数据 + HASH使用AES_ECB - 128算法加密后发送
参考文章AES算法描述及C语言实现_c语言实现aes算法-CSDN博客
AES128加密算法实现(C语言:ECB加密模式实现)-CSDN博客
6.C语言程序周期接收虚拟串口发送的数据_c语言编程实现串口收发数据的程序
参考文章C语言程序周期接收虚拟串口发送的数据_c语言编程实现串口收发数据的程序例程(3)_虚拟串口发送数据-CSDN博客
3.理论形成,实践开始
1.首先我们要写一个SHA-256 和 AES_ECB - 128的头文件,或者考虑引入openssl的ddl动态库链接实现这两个方法,这里我们采取第一种方式实现,结合刚刚的参考文章
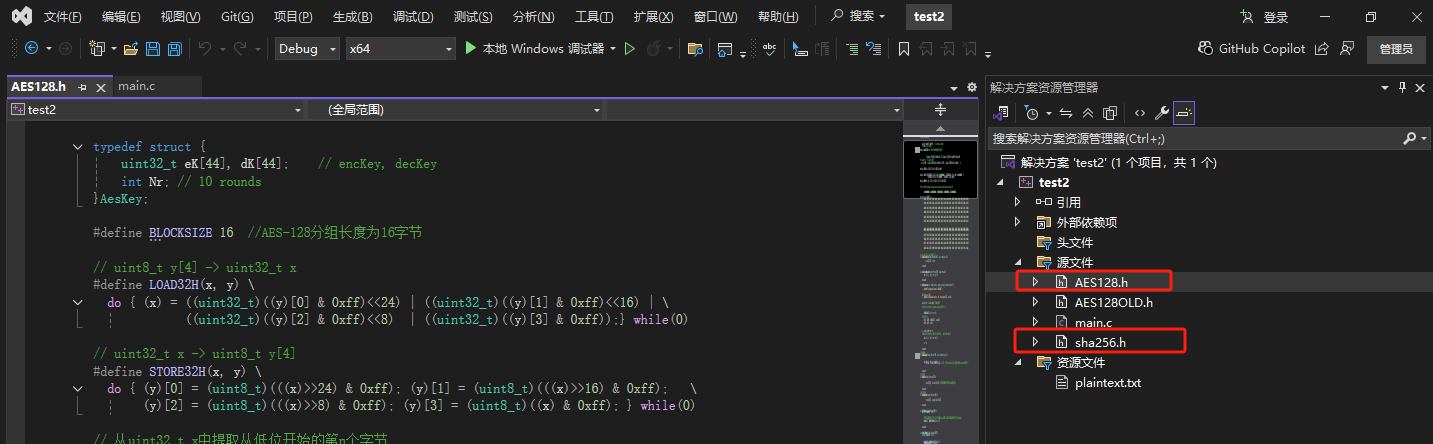
AES128.h
#include <stdint.h>
#include <stdio.h>
#include <string.h>
typedef struct {
uint32_t eK[44], dK[44]; // encKey, decKey
int Nr; // 10 rounds
}AesKey;
#define BLOCKSIZE 16 //AES-128分组长度为16字节
// uint8_t y[4] -> uint32_t x
#define LOAD32H(x, y) \
do { (x) = ((uint32_t)((y)[0] & 0xff)<<24) | ((uint32_t)((y)[1] & 0xff)<<16) | \
((uint32_t)((y)[2] & 0xff)<<8) | ((uint32_t)((y)[3] & 0xff));} while(0)
// uint32_t x -> uint8_t y[4]
#define STORE32H(x, y) \
do { (y)[0] = (uint8_t)(((x)>>24) & 0xff); (y)[1] = (uint8_t)(((x)>>16) & 0xff); \
(y)[2] = (uint8_t)(((x)>>8) & 0xff); (y)[3] = (uint8_t)((x) & 0xff); } while(0)
// 从uint32_t x中提取从低位开始的第n个字节
#define BYTE(x, n) (((x) >> (8 * (n))) & 0xff)
/* used for keyExpansion */
// 字节替换然后循环左移1位
#define MIX(x) (((S[BYTE(x, 2)] << 24) & 0xff000000) ^ ((S[BYTE(x, 1)] << 16) & 0xff0000) ^ \
((S[BYTE(x, 0)] << 8) & 0xff00) ^ (S[BYTE(x, 3)] & 0xff))
// uint32_t x循环左移n位
#define ROF32(x, n) (((x) << (n)) | ((x) >> (32-(n))))
// uint32_t x循环右移n位
#define ROR32(x, n) (((x) >> (n)) | ((x) << (32-(n))))
/* for 128-bit blocks, Rijndael never uses more than 10 rcon values */
// AES-128轮常量
static const uint32_t rcon[10] = {
0x01000000UL, 0x02000000UL, 0x04000000UL, 0x08000000UL, 0x10000000UL,
0x20000000UL, 0x40000000UL, 0x80000000UL, 0x1B000000UL, 0x36000000UL
};
// S盒
unsigned char S[256] = {
0x63, 0x7C, 0x77, 0x7B, 0xF2, 0x6B, 0x6F, 0xC5, 0x30, 0x01, 0x67, 0x2B, 0xFE, 0xD7, 0xAB, 0x76,
0xCA, 0x82, 0xC9, 0x7D, 0xFA, 0x59, 0x47, 0xF0, 0xAD, 0xD4, 0xA2, 0xAF, 0x9C, 0xA4, 0x72, 0xC0,
0xB7, 0xFD, 0x93, 0x26, 0x36, 0x3F, 0xF7, 0xCC, 0x34, 0xA5, 0xE5, 0xF1, 0x71, 0xD8, 0x31, 0x15,
0x04, 0xC7, 0x23, 0xC3, 0x18, 0x96, 0x05, 0x9A, 0x07, 0x12, 0x80, 0xE2, 0xEB, 0x27, 0xB2, 0x75,
0x09, 0x83, 0x2C, 0x1A, 0x1B, 0x6E, 0x5A, 0xA0, 0x52, 0x3B, 0xD6, 0xB3, 0x29, 0xE3, 0x2F, 0x84,
0x53, 0xD1, 0x00, 0xED, 0x20, 0xFC, 0xB1, 0x5B, 0x6A, 0xCB, 0xBE, 0x39, 0x4A, 0x4C, 0x58, 0xCF,
0xD0, 0xEF, 0xAA, 0xFB, 0x43, 0x4D, 0x33, 0x85, 0x45, 0xF9, 0x02, 0x7F, 0x50, 0x3C, 0x9F, 0xA8,
0x51, 0xA3, 0x40, 0x8F, 0x92, 0x9D, 0x38, 0xF5, 0xBC, 0xB6, 0xDA, 0x21, 0x10, 0xFF, 0xF3, 0xD2,
0xCD, 0x0C, 0x13, 0xEC, 0x5F, 0x97, 0x44, 0x17, 0xC4, 0xA7, 0x7E, 0x3D, 0x64, 0x5D, 0x19, 0x73,
0x60, 0x81, 0x4F, 0xDC, 0x22, 0x2A, 0x90, 0x88, 0x46, 0xEE, 0xB8, 0x14, 0xDE, 0x5E, 0x0B, 0xDB,
0xE0, 0x32, 0x3A, 0x0A, 0x49, 0x06, 0x24, 0x5C, 0xC2, 0xD3, 0xAC, 0x62, 0x91, 0x95, 0xE4, 0x79,
0xE7, 0xC8, 0x37, 0x6D, 0x8D, 0xD5, 0x4E, 0xA9, 0x6C, 0x56, 0xF4, 0xEA, 0x65, 0x7A, 0xAE, 0x08,
0xBA, 0x78, 0x25, 0x2E, 0x1C, 0xA6, 0xB4, 0xC6, 0xE8, 0xDD, 0x74, 0x1F, 0x4B, 0xBD, 0x8B, 0x8A,
0x70, 0x3E, 0xB5, 0x66, 0x48, 0x03, 0xF6, 0x0E, 0x61, 0x35, 0x57, 0xB9, 0x86, 0xC1, 0x1D, 0x9E,
0xE1, 0xF8, 0x98, 0x11, 0x69, 0xD9, 0x8E, 0x94, 0x9B, 0x1E, 0x87, 0xE9, 0xCE, 0x55, 0x28, 0xDF,
0x8C, 0xA1, 0x89, 0x0D, 0xBF, 0xE6, 0x42, 0x68, 0x41, 0x99, 0x2D, 0x0F, 0xB0, 0x54, 0xBB, 0x16
};
//逆S盒
unsigned char inv_S[256] = {
0x52, 0x09, 0x6A, 0xD5, 0x30, 0x36, 0xA5, 0x38, 0xBF, 0x40, 0xA3, 0x9E, 0x81, 0xF3, 0xD7, 0xFB,
0x7C, 0xE3, 0x39, 0x82, 0x9B, 0x2F, 0xFF, 0x87, 0x34, 0x8E, 0x43, 0x44, 0xC4, 0xDE, 0xE9, 0xCB,
0x54, 0x7B, 0x94, 0x32, 0xA6, 0xC2, 0x23, 0x3D, 0xEE, 0x4C, 0x95, 0x0B, 0x42, 0xFA, 0xC3, 0x4E,
0x08, 0x2E, 0xA1, 0x66, 0x28, 0xD9, 0x24, 0xB2, 0x76, 0x5B, 0xA2, 0x49, 0x6D, 0x8B, 0xD1, 0x25,
0x72, 0xF8, 0xF6, 0x64, 0x86, 0x68, 0x98, 0x16, 0xD4, 0xA4, 0x5C, 0xCC, 0x5D, 0x65, 0xB6, 0x92,
0x6C, 0x70, 0x48, 0x50, 0xFD, 0xED, 0xB9, 0xDA, 0x5E, 0x15, 0x46, 0x57, 0xA7, 0x8D, 0x9D, 0x84,
0x90, 0xD8, 0xAB, 0x00, 0x8C, 0xBC, 0xD3, 0x0A, 0xF7, 0xE4, 0x58, 0x05, 0xB8, 0xB3, 0x45, 0x06,
0xD0, 0x2C, 0x1E, 0x8F, 0xCA, 0x3F, 0x0F, 0x02, 0xC1, 0xAF, 0xBD, 0x03, 0x01, 0x13, 0x8A, 0x6B,
0x3A, 0x91, 0x11, 0x41, 0x4F, 0x67, 0xDC, 0xEA, 0x97, 0xF2, 0xCF, 0xCE, 0xF0, 0xB4, 0xE6, 0x73,
0x96, 0xAC, 0x74, 0x22, 0xE7, 0xAD, 0x35, 0x85, 0xE2, 0xF9, 0x37, 0xE8, 0x1C, 0x75, 0xDF, 0x6E,
0x47, 0xF1, 0x1A, 0x71, 0x1D, 0x29, 0xC5, 0x89, 0x6F, 0xB7, 0x62, 0x0E, 0xAA, 0x18, 0xBE, 0x1B,
0xFC, 0x56, 0x3E, 0x4B, 0xC6, 0xD2, 0x79, 0x20, 0x9A, 0xDB, 0xC0, 0xFE, 0x78, 0xCD, 0x5A, 0xF4,
0x1F, 0xDD, 0xA8, 0x33, 0x88, 0x07, 0xC7, 0x31, 0xB1, 0x12, 0x10, 0x59, 0x27, 0x80, 0xEC, 0x5F,
0x60, 0x51, 0x7F, 0xA9, 0x19, 0xB5, 0x4A, 0x0D, 0x2D, 0xE5, 0x7A, 0x9F, 0x93, 0xC9, 0x9C, 0xEF,
0xA0, 0xE0, 0x3B, 0x4D, 0xAE, 0x2A, 0xF5, 0xB0, 0xC8, 0xEB, 0xBB, 0x3C, 0x83, 0x53, 0x99, 0x61,
0x17, 0x2B, 0x04, 0x7E, 0xBA, 0x77, 0xD6, 0x26, 0xE1, 0x69, 0x14, 0x63, 0x55, 0x21, 0x0C, 0x7D
};
/* copy in[16] to state[4][4] */
int loadStateArray(uint8_t(*state)[4], const uint8_t* in) {
for (int i = 0; i < 4; ++i) {
for (int j = 0; j < 4; ++j) {
state[j][i] = *in++;
}
}
return 0;
}
/* copy state[4][4] to out[16] */
int storeStateArray(uint8_t(*state)[4], uint8_t* out) {
for (int i = 0; i < 4; ++i) {
for (int j = 0; j < 4; ++j) {
*out++ = state[j][i];
}
}
return 0;
}
//秘钥扩展
int keyExpansion(const uint8_t* key, uint32_t keyLen, AesKey* aesKey) {
if (NULL == key || NULL == aesKey) {
printf("keyExpansion param is NULL\n");
return -1;
}
if (keyLen != 16) {
printf("keyExpansion keyLen = %d, Not support.\n", keyLen);
return -1;
}
uint32_t* w = aesKey->eK; //加密秘钥
uint32_t* v = aesKey->dK; //解密秘钥
/* keyLen is 16 Bytes, generate uint32_t W[44]. */
/* W[0-3] */
for (int i = 0; i < 4; ++i) {
LOAD32H(w[i], key + 4 * i);
}
/* W[4-43] */
for (int i = 0; i < 10; ++i) {
w[4] = w[0] ^ MIX(w[3]) ^ rcon[i];
w[5] = w[1] ^ w[4];
w[6] = w[2] ^ w[5];
w[7] = w[3] ^ w[6];
w += 4;
}
w = aesKey->eK + 44 - 4;
//解密秘钥矩阵为加密秘钥矩阵的倒序,方便使用,把ek的11个矩阵倒序排列分配给dk作为解密秘钥
//即dk[0-3]=ek[41-44], dk[4-7]=ek[37-40]... dk[41-44]=ek[0-3]
for (int j = 0; j < 11; ++j) {
for (int i = 0; i < 4; ++i) {
v[i] = w[i];
}
w -= 4;
v += 4;
}
return 0;
}
// 轮秘钥加
int addRoundKey(uint8_t(*state)[4], const uint32_t* key) {
uint8_t k[4][4];
/* i: row, j: col */
for (int i = 0; i < 4; ++i) {
for (int j = 0; j < 4; ++j) {
k[i][j] = (uint8_t)BYTE(key[j], 3 - i); /* 把 uint32 key[4] 先转换为矩阵 uint8 k[4][4] */
state[i][j] ^= k[i][j];
}
}
return 0;
}
//字节替换
int subBytes(uint8_t(*state)[4]) {
/* i: row, j: col */
for (int i = 0; i < 4; ++i) {
for (int j = 0; j < 4; ++j) {
state[i][j] = S[state[i][j]]; //直接使用原始字节作为S盒数据下标
}
}
return 0;
}
//逆字节替换
int invSubBytes(uint8_t(*state)[4]) {
/* i: row, j: col */
for (int i = 0; i < 4; ++i) {
for (int j = 0; j < 4; ++j) {
state[i][j] = inv_S[state[i][j]];
}
}
return 0;
}
//行移位
int shiftRows(uint8_t(*state)[4]) {
uint32_t block[4] = { 0 };
/* i: row */
for (int i = 0; i < 4; ++i) {
//便于行循环移位,先把一行4字节拼成uint_32结构,移位后再转成独立的4个字节uint8_t
LOAD32H(block[i], state[i]);
block[i] = ROF32(block[i], 8 * i);
STORE32H(block[i], state[i]);
}
return 0;
}
//逆行移位
int invShiftRows(uint8_t(*state)[4]) {
uint32_t block[4] = { 0 };
/* i: row */
for (int i = 0; i < 4; ++i) {
LOAD32H(block[i], state[i]);
block[i] = ROR32(block[i], 8 * i);
STORE32H(block[i], state[i]);
}
return 0;
}
/* Galois Field (256) Multiplication of two Bytes */
// 两字节的伽罗华域乘法运算
uint8_t GMul(uint8_t u, uint8_t v) {
uint8_t p = 0;
for (int i = 0; i < 8; ++i) {
if (u & 0x01) { //
p ^= v;
}
int flag = (v & 0x80);
v <<= 1;
if (flag) {
v ^= 0x1B; /* x^8 + x^4 + x^3 + x + 1 */
}
u >>= 1;
}
return p;
}
// 列混合
int mixColumns(uint8_t(*state)[4]) {
uint8_t tmp[4][4];
uint8_t M[4][4] = { {0x02, 0x03, 0x01, 0x01},
{0x01, 0x02, 0x03, 0x01},
{0x01, 0x01, 0x02, 0x03},
{0x03, 0x01, 0x01, 0x02} };
/* copy state[4][4] to tmp[4][4] */
for (int i = 0; i < 4; ++i) {
for (int j = 0; j < 4; ++j) {
tmp[i][j] = state[i][j];
}
}
for (int i = 0; i < 4; ++i) {
for (int j = 0; j < 4; ++j) { //伽罗华域加法和乘法
state[i][j] = GMul(M[i][0], tmp[0][j]) ^ GMul(M[i][1], tmp[1][j])
^ GMul(M[i][2], tmp[2][j]) ^ GMul(M[i][3], tmp[3][j]);
}
}
return 0;
}
// 逆列混合
int invMixColumns(uint8_t(*state)[4]) {
uint8_t tmp[4][4];
uint8_t M[4][4] = { {0x0E, 0x0B, 0x0D, 0x09},
{0x09, 0x0E, 0x0B, 0x0D},
{0x0D, 0x09, 0x0E, 0x0B},
{0x0B, 0x0D, 0x09, 0x0E} }; //使用列混合矩阵的逆矩阵
/* copy state[4][4] to tmp[4][4] */
for (int i = 0; i < 4; ++i) {
for (int j = 0; j < 4; ++j) {
tmp[i][j] = state[i][j];
}
}
for (int i = 0; i < 4; ++i) {
for (int j = 0; j < 4; ++j) {
state[i][j] = GMul(M[i][0], tmp[0][j]) ^ GMul(M[i][1], tmp[1][j])
^ GMul(M[i][2], tmp[2][j]) ^ GMul(M[i][3], tmp[3][j]);
}
}
return 0;
}
// AES-128加密接口,输入key应为16字节长度,输入长度应该是16字节整倍数,
// 这样输出长度与输入长度相同,函数调用外部为输出数据分配内存
int aesEncrypt(const uint8_t* key, uint32_t keyLen, const uint8_t* pt, uint8_t* ct, uint32_t len) {
AesKey aesKey;
uint8_t* pos = ct;
const uint32_t* rk = aesKey.eK; //解密秘钥指针
uint8_t out[BLOCKSIZE] = { 0 };
uint8_t actualKey[16] = { 0 };
uint8_t state[4][4] = { 0 };
printf("aes2new.\n");
if (NULL == key || NULL == pt || NULL == ct) {
printf("param err.\n");
return -1;
}
if (keyLen > 16) {
printf("keyLen must be 16.\n");
return -1;
}
if (len % BLOCKSIZE) {
printf("inLen is invalid.\n");
return -1;
}
memcpy(actualKey, key, keyLen);
keyExpansion(actualKey, 16, &aesKey); // 秘钥扩展
// 使用ECB模式循环加密多个分组长度的数据
for (int i = 0; i < len; i += BLOCKSIZE) {
// 把16字节的明文转换为4x4状态矩阵来进行处理
loadStateArray(state, pt);
// 轮秘钥加
addRoundKey(state, rk);
for (int j = 1; j < 10; ++j) {
rk += 4;
subBytes(state); // 字节替换
shiftRows(state); // 行移位
mixColumns(state); // 列混合
addRoundKey(state, rk); // 轮秘钥加
}
subBytes(state); // 字节替换
shiftRows(state); // 行移位
// 此处不进行列混合
addRoundKey(state, rk + 4); // 轮秘钥加
// 把4x4状态矩阵转换为uint8_t一维数组输出保存
storeStateArray(state, pos);
pos += BLOCKSIZE; // 加密数据内存指针移动到下一个分组
pt += BLOCKSIZE; // 明文数据指针移动到下一个分组
rk = aesKey.eK; // 恢复rk指针到秘钥初始位置
}
return 0;
}
// AES128解密, 参数要求同加密
int aesDecrypt(const uint8_t* key, uint32_t keyLen, const uint8_t* ct, uint8_t* pt, uint32_t len) {
AesKey aesKey;
uint8_t* pos = pt;
const uint32_t* rk = aesKey.dK; //解密秘钥指针
uint8_t out[BLOCKSIZE] = { 0 };
uint8_t actualKey[16] = { 0 };
uint8_t state[4][4] = { 0 };
if (NULL == key || NULL == ct || NULL == pt) {
printf("param err.\n");
return -1;
}
if (keyLen > 16) {
printf("keyLen must be 16.\n");
return -1;
}
if (len % BLOCKSIZE) {
printf("inLen is invalid.\n");
return -1;
}
memcpy(actualKey, key, keyLen);
keyExpansion(actualKey, 16, &aesKey); //秘钥扩展,同加密
for (int i = 0; i < len; i += BLOCKSIZE) {
// 把16字节的密文转换为4x4状态矩阵来进行处理
loadStateArray(state, ct);
// 轮秘钥加,同加密
addRoundKey(state, rk);
for (int j = 1; j < 10; ++j) {
rk += 4;
invShiftRows(state); // 逆行移位
invSubBytes(state); // 逆字节替换,这两步顺序可以颠倒
addRoundKey(state, rk); // 轮秘钥加,同加密
invMixColumns(state); // 逆列混合
}
invSubBytes(state); // 逆字节替换
invShiftRows(state); // 逆行移位
// 此处没有逆列混合
addRoundKey(state, rk + 4); // 轮秘钥加,同加密
storeStateArray(state, pos); // 保存明文数据
pos += BLOCKSIZE; // 输出数据内存指针移位分组长度
ct += BLOCKSIZE; // 输入数据内存指针移位分组长度
rk = aesKey.dK; // 恢复rk指针到秘钥初始位置
}
return 0;
}
// 以十六进制格式打印数据
void printHex(const uint8_t* data, uint32_t len, const char* label) {
printf("%s ", label);
for (uint32_t i = 0; i < len; ++i) {
printf("%02x ", data[i]);
}
printf("\n");
}sha256.h
#include <stdint.h>
#include <string.h>
// SHA-256 常量定义
#define SHA256_BLOCK_SIZE 64
#define SHA256_DIGEST_SIZE 32
// 循环右移
#define ROTR(x, n) (((x) >> (n)) | ((x) << (32 - (n))))
// SHA-256 压缩函数
#define CH(x, y, z) (((x) & (y)) ^ (~(x) & (z)))
#define MAJ(x, y, z) (((x) & (y)) ^ ((x) & (z)) ^ ((y) & (z)))
#define EP0(x) (ROTR(x, 2) ^ ROTR(x, 13) ^ ROTR(x, 22))
#define EP1(x) (ROTR(x, 6) ^ ROTR(x, 11) ^ ROTR(x, 25))
#define SIG0(x) (ROTR(x, 7) ^ ROTR(x, 18) ^ ((x) >> 3))
#define SIG1(x) (ROTR(x, 17) ^ ROTR(x, 19) ^ ((x) >> 10))
// SHA-256 上下文结构
typedef struct {
uint8_t data[64]; // 当前处理的数据块
uint32_t datalen; // 当前块中的字节数
uint64_t bitlen; // 已处理消息的总位数
uint32_t state[8]; // 哈希状态值 h0-h7
} SHA256_CTX;
// SHA-256 常量表
static const uint32_t K[64] = {
0x428a2f98, 0x71374491, 0xb5c0fbcf, 0xe9b5dba5, 0x3956c25b, 0x59f111f1, 0x923f82a4, 0xab1c5ed5,
0xd807aa98, 0x12835b01, 0x243185be, 0x550c7dc3, 0x72be5d74, 0x80deb1fe, 0x9bdc06a7, 0xc19bf174,
0xe49b69c1, 0xefbe4786, 0x0fc19dc6, 0x240ca1cc, 0x2de92c6f, 0x4a7484aa, 0x5cb0a9dc, 0x76f988da,
0x983e5152, 0xa831c66d, 0xb00327c8, 0xbf597fc7, 0xc6e00bf3, 0xd5a79147, 0x06ca6351, 0x14292967,
0x27b70a85, 0x2e1b2138, 0x4d2c6dfc, 0x53380d13, 0x650a7354, 0x766a0abb, 0x81c2c92e, 0x92722c85,
0xa2bfe8a1, 0xa81a664b, 0xc24b8b70, 0xc76c51a3, 0xd192e819, 0xd6990624, 0xf40e3585, 0x106aa070,
0x19a4c116, 0x1e376c08, 0x2748774c, 0x34b0bcb5, 0x391c0cb3, 0x4ed8aa4a, 0x5b9cca4f, 0x682e6ff3,
0x748f82ee, 0x78a5636f, 0x84c87814, 0x8cc70208, 0x90befffa, 0xa4506ceb, 0xbef9a3f7, 0xc67178f2
};
// 初始化SHA-256上下文
void sha256_init(SHA256_CTX* ctx) {
ctx->datalen = 0;
ctx->bitlen = 0;
ctx->state[0] = 0x6a09e667;
ctx->state[1] = 0xbb67ae85;
ctx->state[2] = 0x3c6ef372;
ctx->state[3] = 0xa54ff53a;
ctx->state[4] = 0x510e527f;
ctx->state[5] = 0x9b05688c;
ctx->state[6] = 0x1f83d9ab;
ctx->state[7] = 0x5be0cd19;
}
// SHA-256转换函数 - 处理一个完整的数据块
void sha256_transform(SHA256_CTX* ctx, const uint8_t data[]) {
uint32_t a, b, c, d, e, f, g, h, i, j, t1, t2, m[64];
// 准备消息调度
for (i = 0, j = 0; i < 16; ++i, j += 4)
m[i] = (data[j] << 24) | (data[j + 1] << 16) | (data[j + 2] << 8) | (data[j + 3]);
for (; i < 64; ++i)
m[i] = SIG1(m[i - 2]) + m[i - 7] + SIG0(m[i - 15]) + m[i - 16];
a = ctx->state[0];
b = ctx->state[1];
c = ctx->state[2];
d = ctx->state[3];
e = ctx->state[4];
f = ctx->state[5];
g = ctx->state[6];
h = ctx->state[7];
// 主压缩循环
for (i = 0; i < 64; ++i) {
t1 = h + EP1(e) + CH(e, f, g) + K[i] + m[i];
t2 = EP0(a) + MAJ(a, b, c);
h = g;
g = f;
f = e;
e = d + t1;
d = c;
c = b;
b = a;
a = t1 + t2;
}
// 更新状态值
ctx->state[0] += a;
ctx->state[1] += b;
ctx->state[2] += c;
ctx->state[3] += d;
ctx->state[4] += e;
ctx->state[5] += f;
ctx->state[6] += g;
ctx->state[7] += h;
}
// 向SHA-256上下文中添加数据
void sha256_update(SHA256_CTX* ctx, const uint8_t data[], size_t len) {
size_t i;
for (i = 0; i < len; ++i) {
ctx->data[ctx->datalen] = data[i];
ctx->datalen++;
if (ctx->datalen == 64) {
sha256_transform(ctx, ctx->data);
ctx->bitlen += 512;
ctx->datalen = 0;
}
}
}
// 完成SHA-256计算并获取哈希值
void sha256_final(SHA256_CTX* ctx, uint8_t hash[]) {
uint32_t i;
// 处理最后不满一个块的数据
i = ctx->datalen;
// 填充1位
if (ctx->datalen < 56) {
ctx->data[i++] = 0x80; // 10000000
// 填充0位
while (i < 56)
ctx->data[i++] = 0x00;
}
else {
ctx->data[i++] = 0x80;
// 填充0位
while (i < 64)
ctx->data[i++] = 0x00;
sha256_transform(ctx, ctx->data);
memset(ctx->data, 0, 56);
}
// 添加消息长度(以位为单位)
ctx->bitlen += ctx->datalen * 8;
ctx->data[63] = (uint8_t)ctx->bitlen;
ctx->data[62] = (uint8_t)(ctx->bitlen >> 8);
ctx->data[61] = (uint8_t)(ctx->bitlen >> 16);
ctx->data[60] = (uint8_t)(ctx->bitlen >> 24);
ctx->data[59] = (uint8_t)(ctx->bitlen >> 32);
ctx->data[58] = (uint8_t)(ctx->bitlen >> 40);
ctx->data[57] = (uint8_t)(ctx->bitlen >> 48);
ctx->data[56] = (uint8_t)(ctx->bitlen >> 56);
sha256_transform(ctx, ctx->data);
// 大端序输出哈希值
for (i = 0; i < 8; ++i) {
hash[i * 4] = (ctx->state[i] >> 24) & 0xFF;
hash[i * 4 + 1] = (ctx->state[i] >> 16) & 0xFF;
hash[i * 4 + 2] = (ctx->state[i] >> 8) & 0xFF;
hash[i * 4 + 3] = ctx->state[i] & 0xFF;
}
}
// 便捷函数:直接计算消息的SHA-256哈希值
void sha256(const uint8_t data[], size_t len, uint8_t hash[]) {
SHA256_CTX ctx;
sha256_init(&ctx);
sha256_update(&ctx, data, len);
sha256_final(&ctx, hash);
}
有了这两个文件,下面我们就要编写程序验证这两个头文件函数是否能成功加密,解密我们的程序了
main.c
/*
AES加解密:采用对称分组密码体制
待加解密字符串:32字节长度字符串明文
算法模式: ECB (Electronic Code Book , 电子密码本) 模式
秘钥长度:秘钥长度输入key应为16字节长度,输入长度应该是16字节整倍数,
秘钥:key[]="1234567890123456"
秘钥偏移量:None
补码方式:None
输出编码:十六进制(Hex)
*/
#include "AES128.h"
int main()
{
/* 加密步骤
1.申明秘钥 key2[]
2.明文 *data
3.加密 aesEncrypt
*/
//****************************************************************************//
// 16字节字符串形式秘钥
const uint8_t key[] = "1234567800000000";
// 32字节长度字符串明文
const uint8_t* P = (uint8_t*)"WOSHINIANGQINGDEGONGCHENGSHI111";
//外部申请输出数据内存,用于存放加密后数据
uint8_t Encrypted_data[32] = { 0 };
//外部申请输出数据内存,用于存放解密后数据
uint8_t Decrypted_data[32] = { 0 };
//加密32字节明文
aesEncrypt(key, 16, P, Encrypted_data, 32); //加密
//****************************************************************************//
printf("\n原始明文:\n%s\n", P); //原始明文数据
printHex(Encrypted_data, 32, "加密编码(HEX):");//加密后Hex
/* 解密步骤
解密函数 aesDecrypt(key, 密钥数据长度, 加密后的数据存放的地址, 用于存放解密后的数据地址, 解密数据的长度)
*/
//****************************************************************************//
// 解密32字节密文
aesDecrypt(key, 16, Encrypted_data, Decrypted_data, 32);
//****************************************************************************//
// 打印16进制形式的解密后的明文
printHex(Decrypted_data, 32, "解密编码(HEX):"); //解密后Hex
// 因为加密前的数据为可见字符的字符串,打印解密后的明文字符,与加密前明文进行对比
printf("解密后反编译出原始明文 \n");
for (int i = 0; i < 32; ++i) {
printf("%c ", Decrypted_data[i]);
}
return 0;
}
控制台输出截图
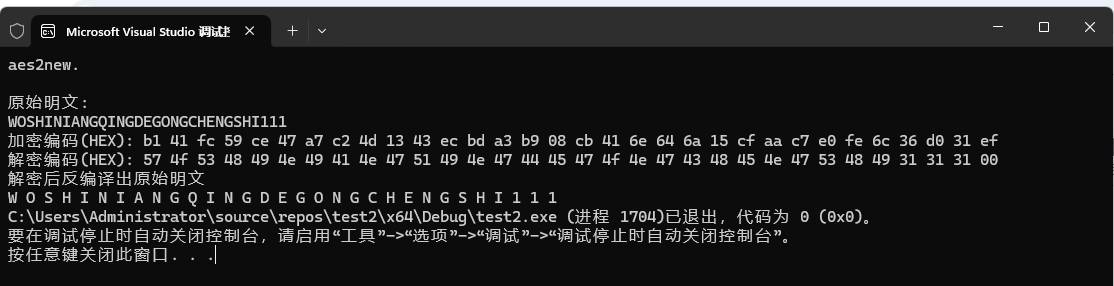
自此验证成功!,继续攻克下一个问题
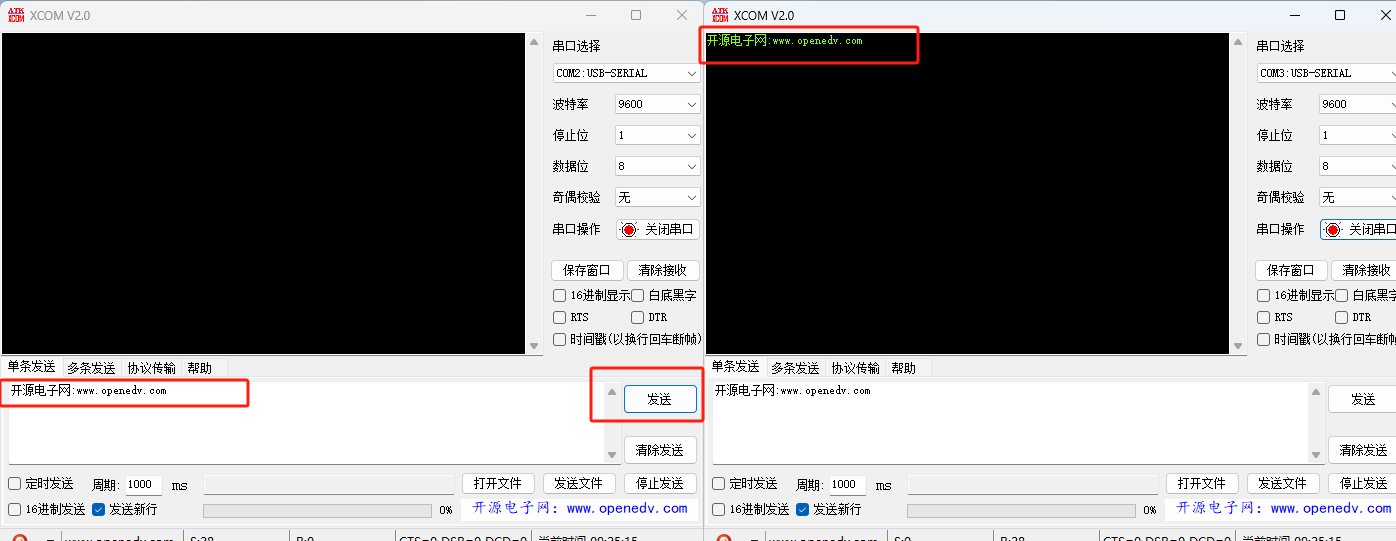
2.超级终端我们用程序1模拟,接收软件我们用程序2模拟,但是串口呢,我们要如何模拟?
参考上面的csdn文章后我们用vspd实现了
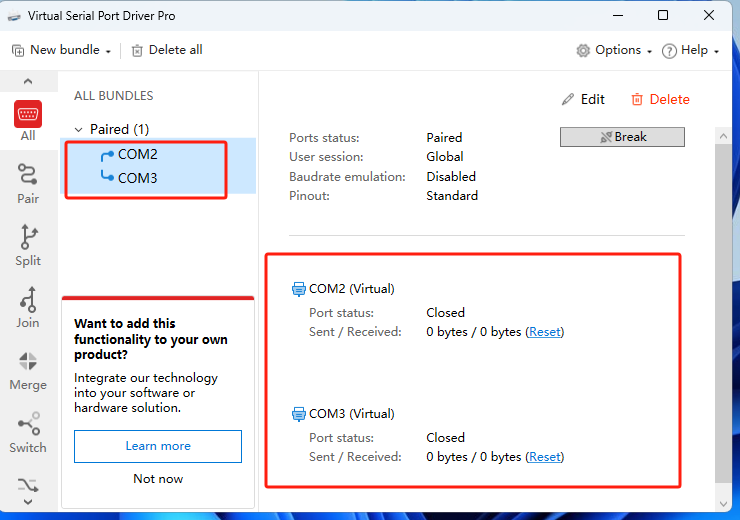
这里模拟了两个串口com2 com3
通过xcom模拟成功(这个去csdn上找个资源下一下就可以),证明确实虚拟端口可以正常使用,
那我们只需要在程序1中用c语言模拟com2发送数据,在程序2中用c语言模拟com3接收数据
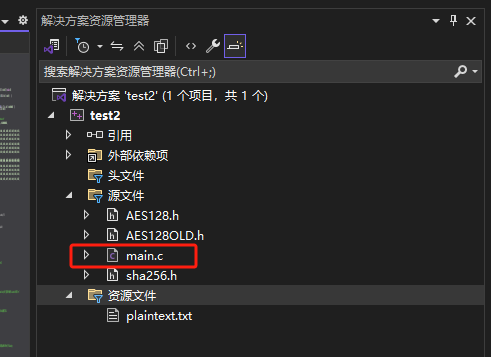
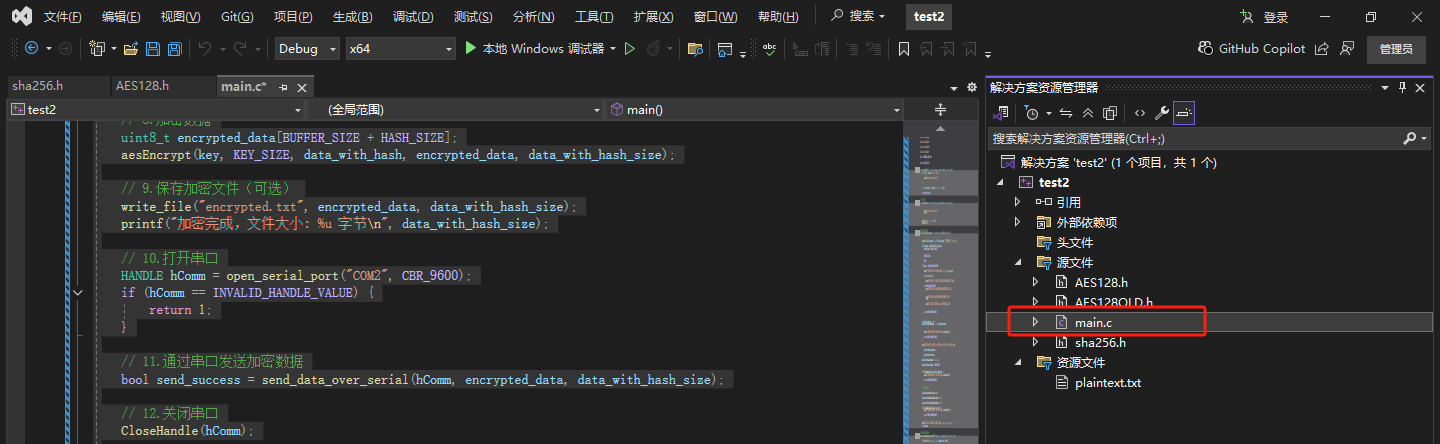
3.程序1,结构如下,需用到我们之前写的两个头文件
程序1 mian.c
#include <windows.h>
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <stdbool.h>
#include "AES128.h"
#include "sha256.h"
#define BUFFER_SIZE 1024
#define HASH_SIZE 32
#define KEY_SIZE 16
// 读取文件
size_t read_file(const char* filename, uint8_t* buffer, size_t size) {
FILE* file = fopen(filename, "rb");
if (file == NULL) {
perror("Failed to open file");
exit(1);
}
size_t bytes_read = fread(buffer, 1, size, file);
fclose(file);
return bytes_read;
}
// 写入文件
void write_file(const char* filename, uint8_t* buffer, size_t size) {
FILE* file = fopen(filename, "wb");
if (file == NULL) {
perror("Failed to open file");
exit(1);
}
fwrite(buffer, 1, size, file);
fclose(file);
}
// 配置并打开串口
HANDLE open_serial_port(const char* port_name, DWORD baud_rate) {
// 修正端口名称格式
char full_port_name[256];
sprintf_s(full_port_name, sizeof(full_port_name), "\\\\.\\%s", port_name);
HANDLE hComm = CreateFileA(full_port_name,
GENERIC_READ | GENERIC_WRITE,
0,
NULL,
OPEN_EXISTING,
0,
NULL);
if (hComm == INVALID_HANDLE_VALUE) {
DWORD error_code = GetLastError();
printf("无法打开串口 %s!错误码: %d\n", port_name, error_code);
switch (error_code) {
case ERROR_FILE_NOT_FOUND:
printf("错误原因:串口不存在,请检查端口名称和设备连接。\n");
break;
case ERROR_ACCESS_DENIED:
printf("错误原因:串口已被其他程序占用或权限不足。\n");
break;
case ERROR_GEN_FAILURE:
printf("错误原因:虚拟串口驱动可能未正确安装。\n");
break;
default:
printf("未知错误,请查阅 Windows 错误代码文档。\n");
}
return INVALID_HANDLE_VALUE;
}
// 配置串口参数
DCB dcbSerialParams = { 0 };
dcbSerialParams.DCBlength = sizeof(dcbSerialParams);
if (!GetCommState(hComm, &dcbSerialParams)) {
printf("获取串口状态失败!错误码: %d\n", GetLastError());
CloseHandle(hComm);
return INVALID_HANDLE_VALUE;
}
printf("原串口配置 - 波特率: %d, 数据位: %d, 停止位: %d, 校验位: %d\n",
dcbSerialParams.BaudRate,
dcbSerialParams.ByteSize,
dcbSerialParams.StopBits,
dcbSerialParams.Parity);
dcbSerialParams.BaudRate = baud_rate;
dcbSerialParams.ByteSize = 8;
dcbSerialParams.StopBits = ONESTOPBIT;
dcbSerialParams.Parity = NOPARITY;
if (!SetCommState(hComm, &dcbSerialParams)) {
printf("设置串口状态失败!错误码: %d\n", GetLastError());
CloseHandle(hComm);
return INVALID_HANDLE_VALUE;
}
// 设置超时参数
COMMTIMEOUTS timeouts = { 0 };
timeouts.ReadIntervalTimeout = 50;
timeouts.ReadTotalTimeoutConstant = 50;
timeouts.ReadTotalTimeoutMultiplier = 10;
timeouts.WriteTotalTimeoutConstant = 50;
timeouts.WriteTotalTimeoutMultiplier = 10;
if (!SetCommTimeouts(hComm, &timeouts)) {
printf("设置超时参数失败!错误码: %d\n", GetLastError());
CloseHandle(hComm);
return INVALID_HANDLE_VALUE;
}
printf("串口 %s 已成功打开,波特率: %d\n", port_name, baud_rate);
return hComm;
}
// 通过串口发送数据
bool send_data_over_serial(HANDLE hComm, const uint8_t* data, size_t size) {
DWORD bytesWritten;
if (!WriteFile(hComm, data, size, &bytesWritten, NULL)) {
printf("发送数据失败!错误码: %d\n", GetLastError());
return false;
}
if (bytesWritten != size) {
printf("警告: 只发送了 %d 字节,而不是全部 %zu 字节\n", bytesWritten, size);
}
printf("成功通过串口发送 %d 字节数据\n", bytesWritten);
return true;
}
int main() {
char cwd[1024];
if (getcwd(cwd, sizeof(cwd)) != NULL) {
printf("当前工作目录: %s\n", cwd);
}
// 1.读取原始数据
uint8_t plaintext[BUFFER_SIZE];
size_t plaintext_size = read_file("附件1.测试信息明文.txt", plaintext, BUFFER_SIZE);
// 2.检查文件是否成功读取
if (plaintext_size == 0) {
printf("Error: No data read from file.\n");
return 1;
}
// 3.对文件的大小做检查,不能越界
if (plaintext_size > UINT32_MAX) {
printf("Data size exceeds uint32_t range.\n");
return 1;
}
uint32_t plaintext_size_uint32 = (uint32_t)plaintext_size;
// 4.计算 SHA-256 HASH 值
uint8_t hash[HASH_SIZE];
sha256(plaintext, plaintext_size_uint32, hash);
// 5.拼接信息数据和 HASH 值
uint8_t data_with_hash[BUFFER_SIZE + HASH_SIZE];
memcpy(data_with_hash, plaintext, plaintext_size_uint32);
memcpy(data_with_hash + plaintext_size_uint32, hash, HASH_SIZE);
uint32_t data_with_hash_size = plaintext_size_uint32 + HASH_SIZE;
// 6.验证数据长度是16字节的倍数
if (data_with_hash_size % 16 != 0) {
printf("Error: Data length must be a multiple of 16 bytes.\n");
return 1;
}
// 7.AES 密钥
const uint8_t key[KEY_SIZE] = { 1234567800000000 };
// 8.加密数据
uint8_t encrypted_data[BUFFER_SIZE + HASH_SIZE];
aesEncrypt(key, KEY_SIZE, data_with_hash, encrypted_data, data_with_hash_size);
// 9.保存加密文件(可选)
write_file("encrypted.txt", encrypted_data, data_with_hash_size);
printf("加密完成,文件大小: %u 字节\n", data_with_hash_size);
// 10.打开串口
HANDLE hComm = open_serial_port("COM2", CBR_9600);
if (hComm == INVALID_HANDLE_VALUE) {
return 1;
}
// 11.通过串口发送加密数据
bool send_success = send_data_over_serial(hComm, encrypted_data, data_with_hash_size);
// 12.关闭串口
CloseHandle(hComm);
// 13.可选:在发送后进行解密验证
uint8_t decrypted_data[BUFFER_SIZE + HASH_SIZE];
aesDecrypt(key, KEY_SIZE, encrypted_data, decrypted_data, data_with_hash_size);
uint8_t* decrypted_plaintext = decrypted_data;
uint8_t* decrypted_hash = decrypted_data + plaintext_size_uint32;
uint8_t recalculated_hash[HASH_SIZE];
sha256(decrypted_plaintext, plaintext_size_uint32, recalculated_hash);
if (memcmp(decrypted_hash, recalculated_hash, HASH_SIZE) == 0) {
printf("HASH验证成功: 数据完整\n");
}
else {
printf("HASH验证失败: 数据可能已损坏\n");
return 1;
}
return send_success ? 0 : 1;
}程序2 main.c
#include <windows.h>
#include <stdio.h>
#include <stdlib.h>
#include <stdbool.h>
#include <stdint.h>
#define BUFFER_SIZE 1024
#define LOG_FILE "附件2. 测试信息密文.txt"
// 配置并打开串口
HANDLE open_serial_port(const char* port_name, DWORD baud_rate) {
// 修正端口名称格式
char full_port_name[256];
sprintf_s(full_port_name, sizeof(full_port_name), "\\\\.\\%s", port_name);
HANDLE hComm = CreateFileA(full_port_name,
GENERIC_READ | GENERIC_WRITE,
0,
NULL,
OPEN_EXISTING,
0,
NULL);
if (hComm == INVALID_HANDLE_VALUE) {
DWORD error_code = GetLastError();
printf("无法打开串口 %s!错误码: %d\n", port_name, error_code);
switch (error_code) {
case ERROR_FILE_NOT_FOUND:
printf("错误原因:串口不存在,请检查端口名称和设备连接。\n");
break;
case ERROR_ACCESS_DENIED:
printf("错误原因:串口已被其他程序占用或权限不足。\n");
break;
case ERROR_GEN_FAILURE:
printf("错误原因:虚拟串口驱动可能未正确安装。\n");
break;
default:
printf("未知错误,请查阅 Windows 错误代码文档。\n");
}
return INVALID_HANDLE_VALUE;
}
// 配置串口参数
DCB dcbSerialParams = { 0 };
dcbSerialParams.DCBlength = sizeof(dcbSerialParams);
if (!GetCommState(hComm, &dcbSerialParams)) {
printf("获取串口状态失败!错误码: %d\n", GetLastError());
CloseHandle(hComm);
return INVALID_HANDLE_VALUE;
}
printf("原串口配置 - 波特率: %d, 数据位: %d, 停止位: %d, 校验位: %d\n",
dcbSerialParams.BaudRate,
dcbSerialParams.ByteSize,
dcbSerialParams.StopBits,
dcbSerialParams.Parity);
dcbSerialParams.BaudRate = baud_rate;
dcbSerialParams.ByteSize = 8;
dcbSerialParams.StopBits = ONESTOPBIT;
dcbSerialParams.Parity = NOPARITY;
if (!SetCommState(hComm, &dcbSerialParams)) {
printf("设置串口状态失败!错误码: %d\n", GetLastError());
CloseHandle(hComm);
return INVALID_HANDLE_VALUE;
}
// 设置超时参数
COMMTIMEOUTS timeouts = { 0 };
timeouts.ReadIntervalTimeout = 50;
timeouts.ReadTotalTimeoutConstant = 50;
timeouts.ReadTotalTimeoutMultiplier = 10;
timeouts.WriteTotalTimeoutConstant = 50;
timeouts.WriteTotalTimeoutMultiplier = 10;
if (!SetCommTimeouts(hComm, &timeouts)) {
printf("设置超时参数失败!错误码: %d\n", GetLastError());
CloseHandle(hComm);
return INVALID_HANDLE_VALUE;
}
printf("串口 %s 已成功打开,波特率: %d\n", port_name, baud_rate);
return hComm;
}
// 从串口读取数据并保存到文件
bool receive_and_save_data(HANDLE hComm, const char* filename) {
FILE* file = fopen(filename, "wb");
if (file == NULL) {
printf("无法创建文件 %s!\n", filename);
return false;
}
uint8_t buffer[BUFFER_SIZE];
DWORD bytesRead;
size_t totalBytes = 0;
printf("正在从串口接收数据...\n");
do {
if (ReadFile(hComm, buffer, BUFFER_SIZE, &bytesRead, NULL)) {
if (bytesRead > 0) {
fwrite(buffer, 1, bytesRead, file);
fflush(file);
totalBytes += bytesRead;
printf("已接收 %zu 字节数据\n", totalBytes);
}
}
else {
printf("读取串口失败!错误码: %d\n", GetLastError());
break;
}
Sleep(10);
} while (1);
fclose(file);
printf("数据已保存到 %s (共 %zu 字节)\n", filename, totalBytes);
return true;
}
int main() {
// 打开串口COM3
HANDLE hComm = open_serial_port("COM3", CBR_9600);
if (hComm == INVALID_HANDLE_VALUE) {
return 1;
}
// 接收数据并保存到文件
receive_and_save_data(hComm, LOG_FILE);
// 关闭串口
CloseHandle(hComm);
return 0;
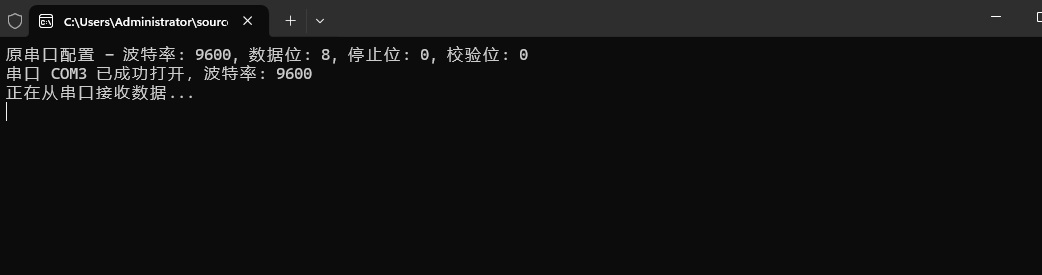
}我们先启动程序2,使用while循环模拟串口监听数据,记得把xcom关掉不然会占用串口
再启动程序1,模拟超级终端发送数据
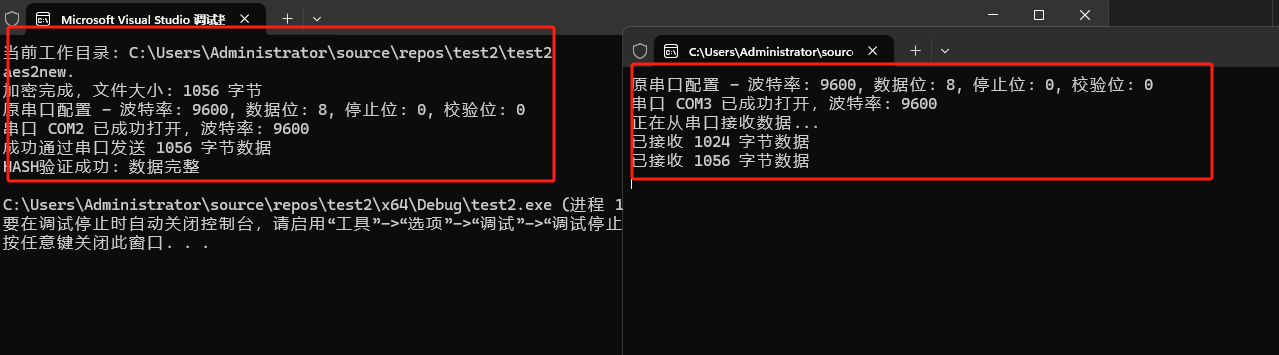
自此实现功能
4.总结
通过本次实践我们实现了一个简单的基于c语言的串口加密通信程序,主要是对sha-256和aes-ecb-128的学习,有了实现思路就能快速实现功能,但是还是有几个问题需要去处理
1.收发功能分离为两个程序,后期需整合为单程序多线程模式
2.多程序 / 终端共用 COM 端口导致信号灯超时,需协调资源占用
3.OpenSSL 库从国外网站下载耗时(10 小时),需通过镜像源或 VPN 加速
4.无单片机等硬件设备,可用软件模拟终端(如 Putty)代替程序2,在 PuTTY 中设置日志记录功能,就能够将接收到的数据保存下来

























 428
428

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








