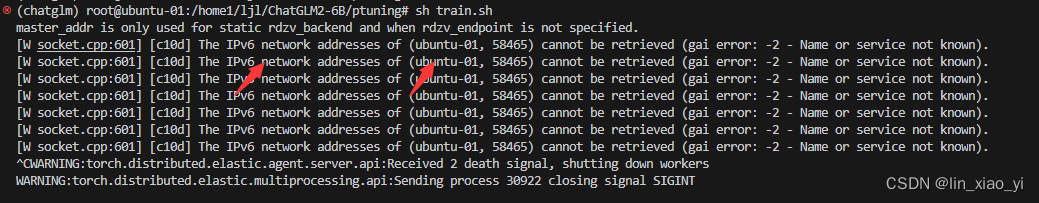
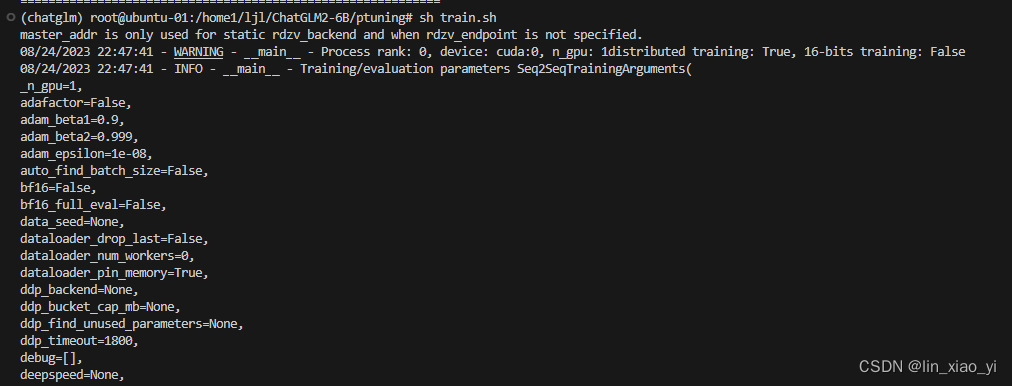
在微调chatglm2-6b模型的时候,发现服务器报错,大概意思是没能连接上本地的网络,查了很多资料都没有结果,下面这个解决方法对我有用
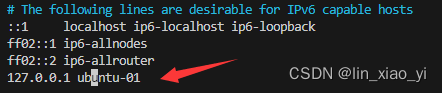
解决方案:手动添加本地网络
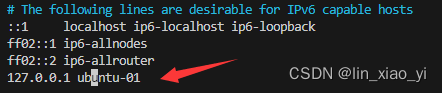
vim /etc/hosts添上本地网络
127.0.0.1 ubuntu-01
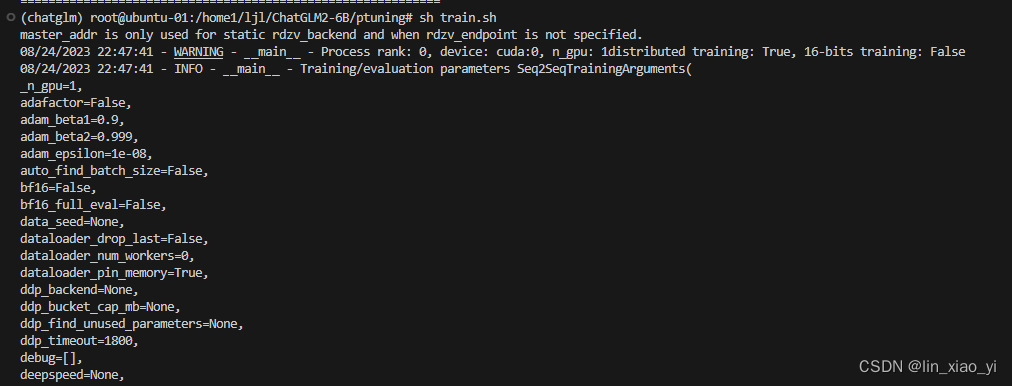
问题解决
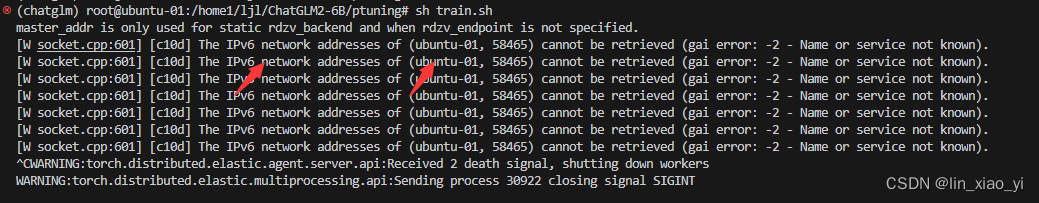
在微调chatglm2-6b模型的时候,发现服务器报错,大概意思是没能连接上本地的网络,查了很多资料都没有结果,下面这个解决方法对我有用
解决方案:手动添加本地网络
vim /etc/hosts添上本地网络
127.0.0.1 ubuntu-01
问题解决











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?


