第一部分
环境准备
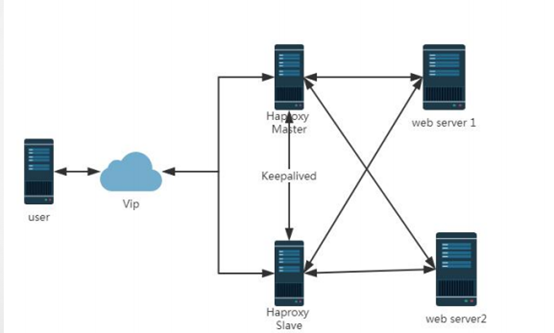
Centos系统服务器4台,两台用于做haproxy主从架构,两台作为后端server,服务器配置好yum源,防火墙关闭,各节点时钟服务同步,各节点之间可以通过主机名相互通信
在四台服务上分别执行 ntpdate 172.17.0.1(实现时钟同步)
1.关闭防火墙和selinux
iptables -F setenforce 0
2、先配置keepalived MASTER 和haproxy的MASTER
需要配置一个vip然后再配置一个DIP的VIP
vim /etc/keepalived/keepalived.conf
global_defs {
notification_email {
root@localhost
}
notification_email_from root
smtp_server 127.0.0.1
smtp_connect_timeout 30
router_id KEEPALIVED_LVS
}
vrrp_instance VI_1 {
state MASTER
interface eth1
virtual_router_id 74
priority 200
advert_int 1
authentication {
auth_type PASS
auth_pass magedu
}
virtual_ipaddress {
172.17.254.100
}
}
vrrp_instance VI_2 {
state MASTER
interface eth0
virtual_router_id 75
priority 200
advert_int 1
authentication {
auth_type PASS
auth_pass magedu
}
virtual_ipaddress {
192.168.150.163
}
实现VIP飘逸
开启路由转发vim /etc/sysctl.conf
net,ipv4,ip_forward=1
sysctl -p 生效
然后从启服务:systemctl start keepalived
配置haproxy的MASTER
vim /etc/haproxy/haproxy.cfg
global
log 127.0.0.1 local2
chroot /var/lib/haproxy
pidfile /var/run/haproxy.pid
maxconn 4000
user haproxy
group haproxy
daemon
stats socket /var/lib/haproxy/stats
defaults
mode http
log global
option httplog
option dontlognull
option http-server-close
option forwardfor except 127.0.0.0/8
option redispatch
retries 3
timeout http-request 10s
timeout queue 1m
timeout connect 10s
timeout client 1m
timeout server 1m
timeout http-keep-alive 10s
timeout check 10s
maxconn 3000
frontend http
bind 172.17.254.100:80
default_backend httpservers
stats enable
stats uri /haproxy
stats auth admin:admin
stats refresh 10s
stats admin if TRUE
backend httpservers
balance roundrobin
server http1 192.168.150.123:80 check weight 1
server http2 192.168.150.135:80 check weight 1
启动服务:systemctl start haproxy
3、配置haproxy的BACKUP和keepalived的BACKUP
vim /etc/keepalived/keepalived.conf
global_defs {
notification_email {
root@localhost
}
notification_email_from root
smtp_server 127.0.0.1
smtp_connect_timeout 30
router_id KEEPALIVED_LVS
}
vrrp_instance VI_1 {
state BACKUP
interface eth1
virtual_router_id 74
priority 190
advert_int 1
authentication {
auth_type PASS
auth_pass magedu
}
virtual_ipaddress {
172.17.250.100
}
}
vrrp_instance VI_2 {
state BACKUP
interface eth0
virtual_router_id 75
priority 190
advert_int 1
authentication {
auth_type PASS
auth_pass magedu
}
virtual_ipaddress {
192.168.150.163
}
}
从启服务:service keepalived start
配置haproxy的BACKUP
vim /etc/haproxy/haproxy.cfg
global
log 127.0.0.1 local2
chroot /var/lib/haproxy
pidfile /var/run/haproxy.pid
maxconn 4000
user haproxy
group haproxy
daemon
stats socket /var/lib/haproxy/stats
defaults
mode http
log global
option httplog
option dontlognull
option http-server-close
option forwardfor except 127.0.0.0/8
option redispatch
retries 3
timeout http-request 10s
timeout queue 1m
timeout connect 10s
timeout client 1m
timeout server 1m
timeout http-keep-alive 10s
timeout check 10s
maxconn 3000
frontend http
bind 172.17.250.100:80
default_backend httpservers
backend httpservers
balance roundrobin
server http1 192.168.150.123:80
server http2 192.168.150.135:80
然后从启服务:service haproxy start
实现转发:vim /etc/sysctl.conf
net,ipv4,ip_forward=1
sysctl -p 生效
(以上的MASTER和BACKUP中web服务80端口不要和haproxy中的80端口同时启动)
4、配置realserver
把web的80端口启动:systemctl start nginx
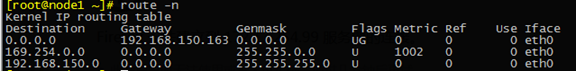
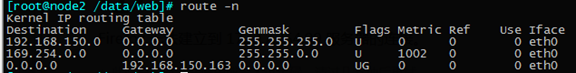
把网关指向DIP的VIP
ip route add default via 192.168.150.163
5、测试实验
curl 172.17.250.100/index.html
第二部分
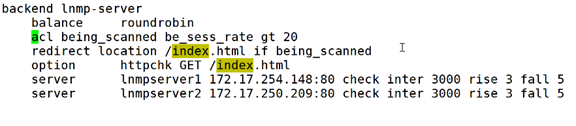
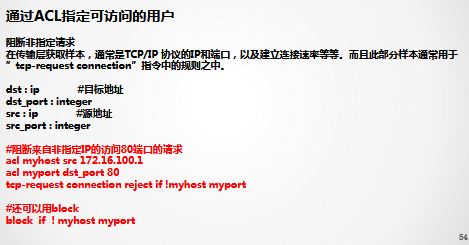
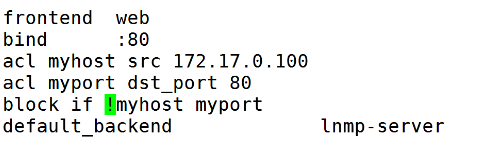
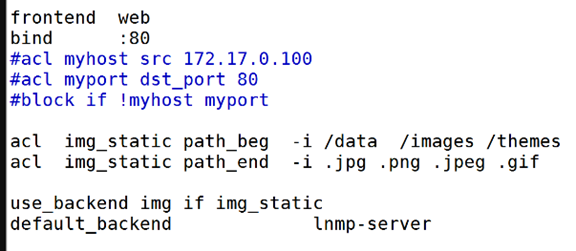
Hpaproxy访问控制ACL应用
1 通过ACL限制用户请求速率
2 通过ACL指定可访问的用户
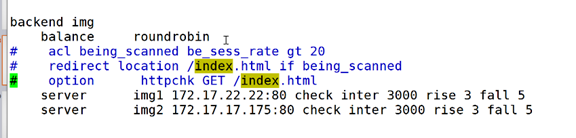
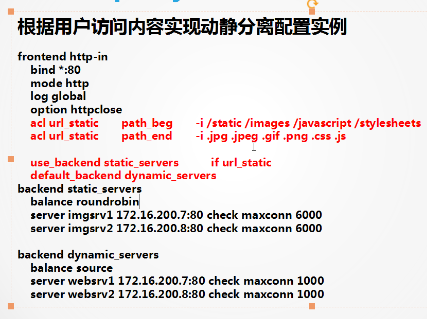
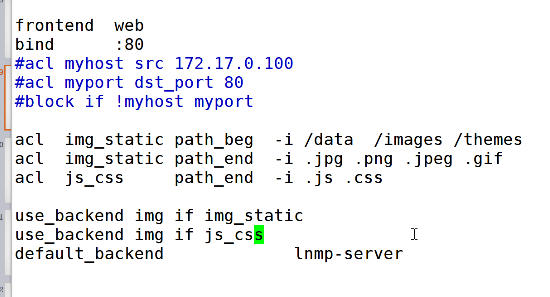
3 根据用户访问内容实现动静分离
1
2
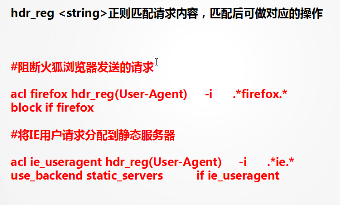
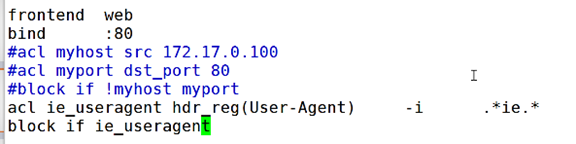
4 根据用户浏览器进行访问控制
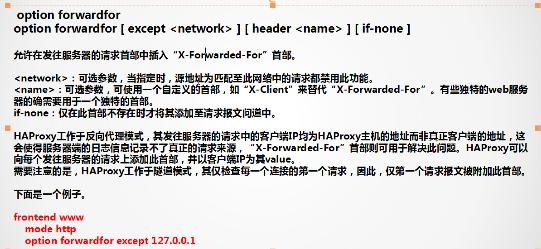
5 Haproxy实现真实日志记录
Option forwardfor
6 Haproxy实现会话保持
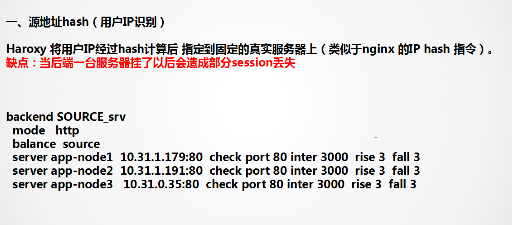
一 源地址hash(用户IP识别)
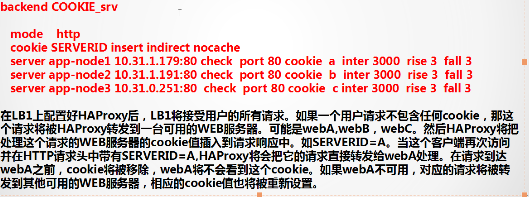
二 cookie识别
Haproxy将web服务器返回给客户端的cookie中插入Haproxy中特定的字符串(或添加前缀)在后端的服务器cooke id。
三 Haproxy性能优化参数
Option redispatch 当server对应的服务器挂掉后,强制定向到其他健康的服务器
Option dontlognull 保证haproxy不记录上级负载均衡发送过来的检后面的测状态没有数据的心脏包
Retries 3: //3次连接失败就认为服务器不可用,主要通过后面的check检查
Maxconn 30000 : //代理时所能接受的最大并发连接数,应该要比后端主机的并发总和要小























 146
146

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








