1. keepalived简介
Keepalived软件起初是专门为LVS负载均衡软件设计的用来管理并监控LVS集群系统中各个服务节点的状态,后来又加入了可以实现高可用的VRRP功能。因此,Keepalived除了能够管理LVS软件外,还可以作为其他服务的高可用解决方案软件。
Keepalived软件主要是通过VRRP协议实现高可用功能的,VRRP是Virtual Router Redundancy Protocol(虚拟路由器冗余协议)的缩写.VRRP出现的目的就是为了解决静态路由单点故障问题的。
Keepalived高可用故障切换转移原理
Keepalived高可用故障切换,是通过VRRP虚拟路由器冗余协议来实现的。
在Keepalived服务正常工作时,主Master节点会不断地向备节点发送(多播的方式)心跳消息,用以告诉备Backup节点自己还活着,当主Master节点发生故障时,就无法发送心跳消息,备节点无法检测到来自主Master节点心跳了,于是调用自身的接管程序,接管主Master节点的IP资源及服务。而当主Master节点恢复时,备Backup节点又会释放主节点故障时自身接管的IP资源及服务,恢复到原来的备用角色。
keepalived 有三个重要的功能,分别是:
- 管理LVS负载均衡软件
- 实现LVS集群节点的健康检查
- 作为系统网络服务的高可用性(failover)
keepalived高可用架构图

keepalived工作原理描述
Keepalived高可用对之间是通过VRRP通信的,因此,我们从 VRRP开始了解起:
- VRRP,全称 Virtual Router Redundancy Protocol,中文名为虚拟路由冗余协议,VRRP的出现是为了解决静态路由的单点故障。
- VRRP是通过一种竟选协议机制来将路由任务交给某台 VRRP路由器的。
- VRRP用 IP多播的方式(默认多播地址(224.0_0.18))实现高可用对之间通信。
- 工作时主节点发包,备节点接包,当备节点接收不到主节点发的数据包的时候,就启动接管程序接管主节点的开源。备节点可以有多个,通过优先级竞选,但一般 Keepalived系统运维工作中都是一对。
- VRRP使用了加密协议加密数据,但Keepalived官方目前还是推荐用明文的方式配置认证类型和密码。
Keepalived服务的工作原理:
Keepalived高可用是通过 VRRP 进行通信的, VRRP是通过竞选机制来确定主备的,主的优先级高于备,因此,工作时主会优先获得所有的资源,备节点处于等待状态,当主挂了的时候,备节点就会接管主节点的资源,然后顶替主节点对外提供服务。
在 Keepalived 服务之间,只有作为主的服务器会一直发送 VRRP 广播包,告诉备它还活着,此时备不会枪占主,当主不可用时,即备监听不到主发送的广播包时,就会启动相关服务接管资源,保证业务的连续性.接管速度最快可以小于1秒。
2. keepalived配置文件讲解
keepalived默认配置文件
keepalived 的主配置文件是 /etc/keepalived/keepalived.conf。其内容如下:
[root@wyt1 ~]# cat /etc/keepalived/keepalived.conf
! Configuration File for keepalived
global_defs { //全局配置
notification_email { //定义报警收件人邮件地址
acassen@firewall.loc
failover@firewall.loc
sysadmin@firewall.loc
}
notification_email_from Alexandre.Cassen@firewall.loc //定义报警发件人邮箱
smtp_server 192.168.200.1 //邮箱服务器地址
smtp_connect_timeout 30 //定义邮箱超时时间
router_id LVS_DEVEL //定义路由标识信息,同局域网内唯一
vrrp_skip_check_adv_addr
vrrp_strict
vrrp_garp_interval 0
vrrp_gna_interval 0
}
vrrp_instance VI_1 { //定义实例
state MASTER //指定keepalived节点的初始状态,可选值为MASTER|BACKUP
interface eth0 //VRRP实例绑定的网卡接口,用户发送VRRP包
virtual_router_id 51 //虚拟路由的ID,同一集群要一致
priority 100 //定义优先级,按优先级来决定主备角色,优先级越大越优先
nopreempt //设置不抢占
advert_int 1 //主备通讯时间间隔
authentication { //配置认证
auth_type PASS //认证方式,此处为密码
auth_pass 1111 //同一集群中的keepalived配置里的此处必须一致,推荐使用8位随机数
}
virtual_ipaddress { //配置要使用的VIP地址
192.168.200.16
}
}
virtual_server 192.168.200.16 1358 { //配置虚拟服务器
delay_loop 6 //健康检查的时间间隔
lb_algo rr //lvs调度算法
lb_kind NAT //lvs模式
persistence_timeout 50 //持久化超时时间,单位是秒
protocol TCP //4层协议
sorry_server 192.168.200.200 1358 //定义备用服务器,当所有RS都故障时用sorry_server来响应客户端
real_server 192.168.200.2 1358 { //定义真实处理请求的服务器
weight 1 //给服务器指定权重,默认为1
HTTP_GET {
url {
path /testurl/test.jsp //指定要检查的URL路径
digest 640205b7b0fc66c1ea91c463fac6334d //摘要信息
}
url {
path /testurl2/test.jsp
digest 640205b7b0fc66c1ea91c463fac6334d
}
url {
path /testurl3/test.jsp
digest 640205b7b0fc66c1ea91c463fac6334d
}
connect_timeout 3 //连接超时时间
nb_get_retry 3 //get尝试次数
delay_before_retry 3 //在尝试之前延迟多长时间
}
}
real_server 192.168.200.3 1358 {
weight 1
HTTP_GET {
url {
path /testurl/test.jsp
digest 640205b7b0fc66c1ea91c463fac6334c
}
url {
path /testurl2/test.jsp
digest 640205b7b0fc66c1ea91c463fac6334c
}
connect_timeout 3
nb_get_retry 3
delay_before_retry 3
}
}
}
定制主配置文件
vrrp_instance段配置
nopreempt //设置为不抢占。默认是抢占的,当高优先级的机器恢复后,会抢占低优先 \
级的机器成为MASTER,而不抢占,则允许低优先级的机器继续成为MASTER,即使高优先级 \
的机器已经上线。如果要使用这个功能,则初始化状态必须为BACKUP。
preempt_delay //设置抢占延迟。单位是秒,范围是0---1000,默认是0.发现低优先 \
级的MASTER后多少秒开始抢占。
vrrp_script段配置
//作用:添加一个周期性执行的脚本。脚本的退出状态码会被调用它的所有的VRRP Instance记录。
//注意:至少有一个VRRP实例调用它并且优先级不能为0.优先级范围是1-254.
vrrp_script <SCRIPT_NAME> {
...
}
//选项说明:
script "/path/to/somewhere" //指定要执行的脚本的路径。
interval <INTEGER> //指定脚本执行的间隔。单位是秒。默认为1s。
timeout <INTEGER> //指定在多少秒后,脚本被认为执行失败。
weight <-254 --- 254> //调整优先级。默认为2.
rise <INTEGER> //执行成功多少次才认为是成功。
fall <INTEGER> //执行失败多少次才认为失败。
user <USERNAME> [GROUPNAME] //运行脚本的用户和组。
init_fail //假设脚本初始状态是失败状态。
//weight说明:
1. 如果脚本执行成功(退出状态码为0),weight大于0,则priority增加。
2. 如果脚本执行失败(退出状态码为非0),weight小于0,则priority减少。
3. 其他情况下,priority不变。
real_server段配置
weight <INT> //给服务器指定权重。默认是1
inhibit_on_failure //当服务器健康检查失败时,将其weight设置为0, \
//而不是从Virtual Server中移除
notify_up <STRING> //当服务器健康检查成功时,执行的脚本
notify_down <STRING> //当服务器健康检查失败时,执行的脚本
uthreshold <INT> //到这台服务器的最大连接数
lthreshold <INT> //到这台服务器的最小连接数
tcp_check段配置
connect_ip <IP ADDRESS> //连接的IP地址。默认是real server的ip地址
connect_port <PORT> //连接的端口。默认是real server的端口
bindto <IP ADDRESS> //发起连接的接口的地址。
bind_port <PORT> //发起连接的源端口。
connect_timeout <INT> //连接超时时间。默认是5s。
fwmark <INTEGER> //使用fwmark对所有出去的检查数据包进行标记。
warmup <INT> //指定一个随机延迟,最大为N秒。可防止网络阻塞。如果为0,则关闭该功能。
retry <INIT> //重试次数。默认是1次。
delay_before_retry <INT> //默认是1秒。在重试之前延迟多少秒。
实例
global_defs {
router_id LVS_Server
}
vrrp_instance VI_1 {
state BACKUP
interface ens33
virtual_router_id 51
priority 150
nopreempt
advert_int 1
authentication {
auth_type PASS
auth_pass wangqing
}
virtual_ipaddress {
192.168.179.200 dev ens33
}
}
virtual_server 192.168.179.200 80 {
delay_loop 3
lvs_sched rr
lvs_method DR
protocol TCP
real_server 192.168.179.128. 80 {
weight 1
TCP_CHECK {
connect_port 80
connect_timeout 3
nb_get_retry 3
delay_before_retry 3
}
}
real_server 192.168.179.129. 8080 {
weight 1
TCP_CHECK {
connect_port 8080
connect_timeout 3
nb_get_retry 3
delay_before_retry 3
}
}
}
3.keepalived实现nginx负载均衡机高可用
环境说明
| 系统信息 | 主机名 | IP |
|---|---|---|
| CentOS7 | wyt1 | 192.168.179.128 |
| CentOS7 | wyt2 | 192.168.179.129 |
keepalived安装
配置主keepalived
关闭防火墙及selinux
[root@wyt1 ~]# systemctl disable --now firewalld
Removed symlink /etc/systemd/system/multi-user.target.wants/firewalld.service.
Removed symlink /etc/systemd/system/dbus-org.fedoraproject.FirewallD1.service.
[root@wyt1 ~]# setenforce 0
[root@wyt1 ~]# sed -ri 's/^(SELINUX=).*/\1disabled/g' /etc/selinux/config
配置网络源
[root@wyt1 ~]# curl -o /etc/yum.repos.d/CentOS-Base.repo https://mirrors.aliyun.com/repo/Centos-7.repo
[root@wyt1 ~]# sed -i 's/\$releasever/7/g' /etc/yum.repos.d/CentOS-Base.repo
[root@wyt1 ~]# sed -i -e '/mirrors.cloud.aliyuncs.com/d' -e '/mirrors.aliyuncs.com/d' /etc/yum.repos.d/CentOS-Base.repo
[root@wyt1 ~]# wget -O /etc/yum.repos.d/epel.repo http://mirrors.aliyun.com/repo/epel-7.repo
[root@wyt1 ~]# yum -y install vim wget gcc gcc-c++
安装keepalived
[root@wyt1 ~]# yum -y install keepalived
查看安装生成的文件
[root@wyt1 ~]# rpm -ql keepalived
/etc/keepalived //配置目录
/etc/keepalived/keepalived.conf //此为主配置文件
/etc/sysconfig/keepalived
/usr/bin/genhash
/usr/lib/systemd/system/keepalived.service //此为服务控制文件
/usr/libexec/keepalived
/usr/sbin/keepalived
配置备keepalived
关闭防火墙及selinux
[root@wyt1 ~]# systemctl disable --now firewalld
Removed symlink /etc/systemd/system/multi-user.target.wants/firewalld.service.
Removed symlink /etc/systemd/system/dbus-org.fedoraproject.FirewallD1.service.
[root@wyt1 ~]# setenforce 0
[root@wyt1 ~]# sed -ri 's/^(SELINUX=).*/\1disabled/g' /etc/selinux/config
配置网络源
[root@wyt1 ~]# curl -o /etc/yum.repos.d/CentOS-Base.repo https://mirrors.aliyun.com/repo/Centos-7.repo
[root@wyt1 ~]# sed -i 's/\$releasever/7/g' /etc/yum.repos.d/CentOS-Base.repo
[root@wyt1 ~]# sed -i -e '/mirrors.cloud.aliyuncs.com/d' -e '/mirrors.aliyuncs.com/d' /etc/yum.repos.d/CentOS-Base.repo
[root@wyt1 ~]# wget -O /etc/yum.repos.d/epel.repo http://mirrors.aliyun.com/repo/epel-7.repo
[root@wyt1 ~]# yum -y install vim wget gcc gcc-c++
安装keepalived
[root@wyt1 ~]# yum -y install keepalived
配置httpd
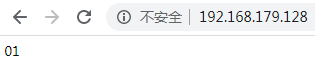
在主上面配置httpd
[root@wyt1 ~]# cd /var/www/html/
[root@wyt1 html]# echo '01' > index.html
[root@wyt1 html]# systemctl start httpd
[root@wyt1 html]# ss -antl
State Recv-Q Send-Q Local Address:Port Peer Address:Port
LISTEN 0 100 127.0.0.1:25 *:*
LISTEN 0 128 *:22 *:*
LISTEN 0 100 [::1]:25 [::]:*
LISTEN 0 128 [::]:80 [::]:*
LISTEN 0 128 [::]:22 [::]:*
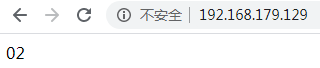
在备上面配置httpd
[root@wyt2 ~]# cd /var/www/html/
[root@wyt2 html]# echo '02' > index.html
[root@wyt2 html]# systemctl start httpd
[root@wyt2 html]# ss -antl
State Recv-Q Send-Q Local Address:Port Peer Address:Port
LISTEN 0 100 127.0.0.1:25 *:*
LISTEN 0 128 *:22 *:*
LISTEN 0 100 [::1]:25 [::]:*
LISTEN 0 128 [::]:80 [::]:*
LISTEN 0 128 [::]:22 [::]:*
keepalived配置
配置主keepalived
[root@wyt1 ~]# cd /etc/keepalived/
[root@wyt1 keepalived]# ls
keepalived.conf
[root@wyt1 keepalived]# cp keepalived.conf{,-bak} //备份
[root@wyt1 keepalived]# ls
keepalived.conf keepalived.conf-bak
[root@wyt1 keepalived]# > keepalived.conf //清空
[root@wyt1 keepalived]# vim keepalived.conf
! Configuration File for keepalived
global_defs {
router_id lb01
}
vrrp_instance VI_1 {
state MASTER
interface ens33
virtual_router_id 51
priority 100
advert_int 1
authentication {
auth_type PASS
auth_pass 123456
}
virtual_ipaddress {
192.168.179.200
}
}
virtual_server 192.168.179.200 80 {
delay_loop 6
lb_algo rr
lb_kind DR
persistence_timeout 50
protocol TCP
real_server 192.168.179.128 80 {
weight 1
TCP_CHECK {
connect_port 80
connect_timeout 3
nb_get_retry 3
delay_before_retry 3
}
}
real_server 192.168.179.129 80 {
weight 1
TCP_CHECK {
connect_port 80
connect_timeout 3
nb_get_retry 3
delay_before_retry 3
}
}
}
[root@wyt1 keepalived]# systemctl enable --now keepalived
Created symlink from /etc/systemd/system/multi-user.target.wants/keepalived.service to /usr/lib/systemd/system/keepalived.service.
配置备keepalived
[root@wyt2 ~]# cd /etc/keepalived/
[root@wyt2 keepalived]# ls
keepalived.conf
[root@wyt2 keepalived]# cp keepalived.conf{,-bak}
[root@wyt2 keepalived]# ls
keepalived.conf keepalived.conf-bak
[root@wyt2 keepalived]# > keepalived.conf
[root@wyt2 keepalived]# vim keepalived.conf
! Configuration File for keepalived
global_defs {
router_id lb02
}
vrrp_instance VI_1 {
state BACKUP
interface ens33
virtual_router_id 51
priority 80
advert_int 1
authentication {
auth_type PASS
auth_pass 123456
}
virtual_ipaddress {
! Configuration File for keepalived
global_defs {
router_id lb02
}
vrrp_instance VI_1 {
state BACKUP
interface ens33
virtual_router_id 51
priority 80
advert_int 1
authentication {
auth_type PASS
auth_pass 123456
}
virtual_ipaddress {
192.168.179.200
}
}
virtual_server 192.168.179.200 80 {
delay_loop 6
lb_algo rr
lb_kind DR
persistence_timeout 50
protocol TCP
real_server 192.168.179.128 80 {
weight 1
TCP_CHECK {
connect_port 80
connect_timeout 3
nb_get_retry 3
delay_before_retry 3
}
}
real_server 192.168.179.129 80 {
weight 1
TCP_CHECK {
connect_port 80
connect_timeout 3
nb_get_retry 3
delay_before_retry 3
}
}
}
[root@wyt2 keepalived]# systemctl enable --now keepalived
Created symlink from /etc/systemd/system/multi-user.target.wants/keepalived.service to /usr/lib/systemd/system/keepalived.service.
查看VIP在哪里
在主上面查看
[root@wyt1 keepalived]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP group default qlen 1000
link/ether 00:0c:29:b3:0c:45 brd ff:ff:ff:ff:ff:ff
inet 192.168.179.128/24 brd 192.168.179.255 scope global noprefixroute ens33
valid_lft forever preferred_lft forever
inet 192.168.179.200/32 scope global ens33
valid_lft forever preferred_lft forever
inet6 fe80::20c:29ff:feb3:c45/64 scope link
valid_lft forever preferred_lft forever
在备上面查看
[root@wyt2 keepalived]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP group default qlen 1000
link/ether 00:0c:29:ff:51:47 brd ff:ff:ff:ff:ff:ff
inet 192.168.179.129/24 brd 192.168.179.255 scope global noprefixroute ens33
valid_lft forever preferred_lft forever
inet6 fe80::20c:29ff:feff:5147/64 scope link
valid_lft forever preferred_lft forever
让keepalived监控httpd负载均衡机
keepalived通过脚本来监控nginx负载均衡机的状态
在主上编写脚本
[root@wyt1 ~]# mkdir /scripts
[root@wyt1 ~]# cd /scripts/
[root@wyt1 scripts]# vim check_httpd.sh
#!/bin/bash
httpd_status=$(ps -ef|grep -Ev "grep|$0"|grep '\bhttpd\b'|wc -l)
if [ $httpd_status -lt 1 ];then
systemctl stop keepalived
[root@wyt1 scripts]# vim notify.sh
#!/bin/bash
VIP=$2
case "$1" in
master)
httpd_status=$(ps -ef|grep -Ev "grep|$0"|grep '\bhttpd\b'|wc -l)
if [ $httpd_status -lt 1 ];then
systemctl start httpd
fi
;;
backup)
httpd_status=$(ps -ef|grep -Ev "grep|$0"|grep '\bhttpd\b'|wc -l)
if [ $httpd_status -gt 0 ];then
systemctl stop httpd
fi
;;
*)
echo "Usage:$0 master|backup VIP"
;;
esac
[root@wyt1 scripts]# chmod +x *.sh //给脚本执行权限
[root@wyt1 scripts]# ll
总用量 8
-rwxr-xr-x 1 root root 142 8月 5 15:57 check_httpd.sh
-rwxr-xr-x 1 root root 434 8月 5 15:59 notify.sh
在备上编写脚本
[root@wyt2 ~]# mkdir /scripts
[root@wyt2 ~]# cd /scripts/
[root@wyt2 scripts]# vim notify.sh
#!/bin/bash
VIP=$2
case "$1" in
master)
httpd_status=$(ps -ef|grep -Ev "grep|$0"|grep '\bhttpd\b'|wc -l)
if [ $httpd_status -lt 1 ];then
systemctl start httpd
fi
;;
backup)
httpd_status=$(ps -ef|grep -Ev "grep|$0"|grep '\bhttpd\b'|wc -l)
if [ $httpd_status -gt 0 ];then
systemctl stop httpd
fi
;;
*)
echo "Usage:$0 master|backup VIP"
;;
esac
[root@wyt1 scripts]# chmod +x notify.sh //给脚本执行权限
[root@wyt2 scripts]# ll
总用量 4
-rwxr-xr-x 1 root root 434 8月 6 01:17 notify.sh
配置keepalived加入监控脚本的配置
配置主keepalived
[root@wyt1 ~]# vim /etc/keepalived/keepalived.conf
! Configuration File for keepalived
global_defs {
router_id lb01
}
vrrp_script httpd_check {
script "/scripts/check_httpd.sh"
interval 1
weight -30
}
vrrp_instance VI_1 {
state MASTER
interface ens33
virtual_router_id 51
priority 100
advert_int 1
authentication {
auth_type PASS
auth_pass 123456
}
virtual_ipaddress {
192.168.179.200
}
track_script {
httpd_check
}
notify_master "/scripts/notify.sh master 192.168.179.200"
notify_backup "/scripts/notify.sh backup 192.168.179.200"
}
virtual_server 192.168.179.200 80 {
delay_loop 6
lb_algo rr
lb_kind DR
persistence_timeout 50
protocol TCP
real_server 192.168.179.128 80 {
weight 1
TCP_CHECK {
connect_port 80
connect_timeout 3
nb_get_retry 3
delay_before_retry 3
}
}
real_server 192.168.179.129 80 {
weight 1
TCP_CHECK {
connect_port 80
connect_timeout 3
nb_get_retry 3
delay_before_retry 3
}
}
}
[root@wyt1 ~]# systemctl restart keepalived //重启服务
配置备keepalived
! Configuration File for keepalived
global_defs {
router_id lb02
}
vrrp_instance VI_1 {
state BACKUP
interface ens33
virtual_router_id 51
priority 80
advert_int 1
authentication {
auth_type PASS
auth_pass 123456
}
virtual_ipaddress {
192.168.179.200
}
notify_master "/scripts/notify.sh master 192.168.179.200"
notify_backup "/scripts/notify.sh backup 192.168.179.200"
}
virtual_server 192.168.179.200 80 {
delay_loop 6
lb_algo rr
lb_kind DR
persistence_timeout 50
protocol TCP
real_server 192.168.179.128 80 {
weight 1
TCP_CHECK {
connect_port 80
connect_timeout 3
nb_get_retry 3
delay_before_retry 3
}
}
real_server 192.168.179.129 80 {
weight 1
TCP_CHECK {
connect_port 80
connect_timeout 3
nb_get_retry 3
delay_before_retry 3
}
}
}
[root@wyt2 ~]# systemctl restart keepalived //重启服务
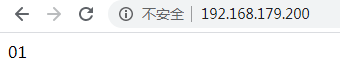
验证
[root@wyt1 ~]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP group default qlen 1000
link/ether 00:0c:29:b3:0c:45 brd ff:ff:ff:ff:ff:ff
inet 192.168.179.128/24 brd 192.168.179.255 scope global noprefixroute ens33
valid_lft forever preferred_lft forever
inet 192.168.179.200/32 scope global ens33
valid_lft forever preferred_lft forever
inet6 fe80::20c:29ff:feb3:c45/64 scope link
valid_lft forever preferred_lft forever
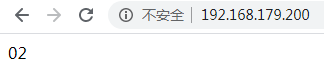
关闭主上的httpd,在访问
[root@wyt1 ~]# systemctl stop httpd
[root@wyt1 ~]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP group default qlen 1000
link/ether 00:0c:29:b3:0c:45 brd ff:ff:ff:ff:ff:ff
inet 192.168.179.128/24 brd 192.168.179.255 scope global noprefixroute ens33
valid_lft forever preferred_lft forever
inet6 fe80::20c:29ff:feb3:c45/64 scope link
valid_lft forever preferred_lft forever
查看主VIP转移到备上面
[root@wyt2 ~]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP group default qlen 1000
link/ether 00:0c:29:ff:51:47 brd ff:ff:ff:ff:ff:ff
inet 192.168.179.129/24 brd 192.168.179.255 scope global noprefixroute ens33
valid_lft forever preferred_lft forever
inet 192.168.179.200/32 scope global ens33
valid_lft forever preferred_lft forever
inet6 fe80::20c:29ff:feff:5147/64 scope link
valid_lft forever preferred_lft forever
使用systemctl stop keepalived时可能出现进程杀不干净的情况,从而导致vip无法转移到备,解决方法如下
[root@wyt1 ~]# vim /usr/lib/systemd/system/keepalived.service
[Unit]
Description=LVS and VRRP High Availability Monitor
After=syslog.target network-online.target
[Service]
Type=forking
PIDFile=/var/run/keepalived.pid
#KillMode=process //将此行注释,注释后默认关闭所有进程,process只关闭父进程,killmode的默认值是control-group,意思时所有进程都会被干掉
EnvironmentFile=-/etc/sysconfig/keepalived
ExecStart=/usr/sbin/keepalived $KEEPALIVED_OPTIONS
ExecReload=/bin/kill -HUP $MAINPID
[Install]
WantedBy=multi-user.target
[root@wyt1 ~]# systemctl daemon-reload




















 923
923











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








