第14天
配置本地yum源环境
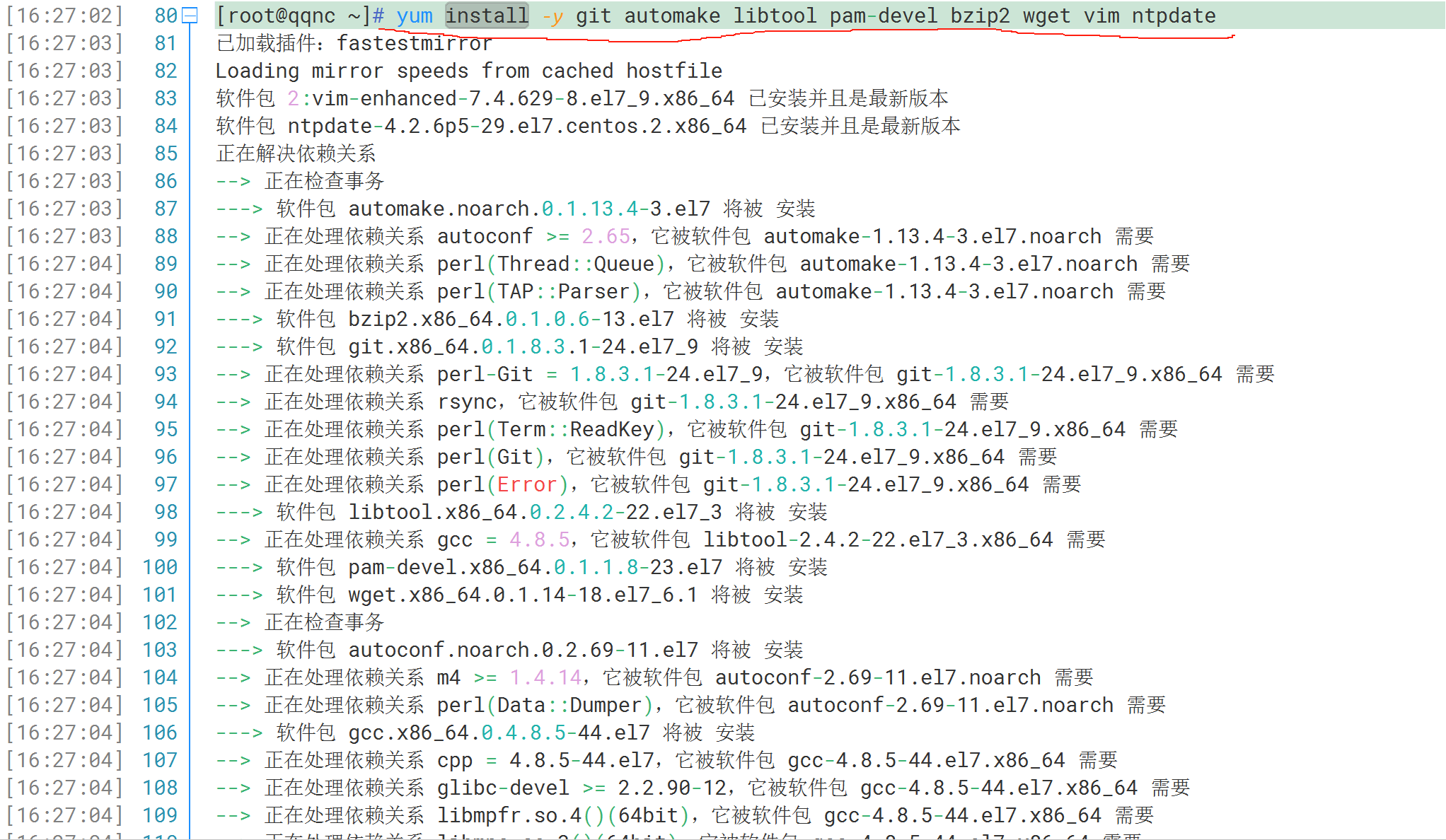
[root@localhost ~]# yum install -y git automake libtool pam-devel bzip2 wget vim ntpdate
校对时间
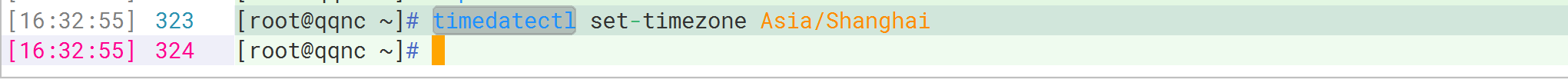
#修改时区
[root@localhost ~]# timedatectl set-timezone Asia/Shanghai
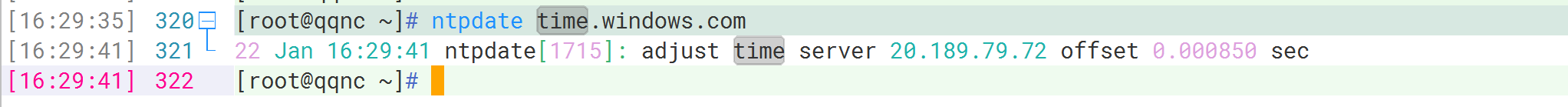
#校对时间
[root@localhost ~]# ntpdate time.windows.com
修改时区
校对时间
下载工具包
[root@localhost ~]# wget http://repository.timesys.com/buildsources/l/libpam-google-authenticator/libpam-google-authenticator-1.0/libpam-google-authenticator-1.0-source.tar.bz2
解压
[root@localhost ~]# tar -xjvf libpam-google-authenticator-1.0-source.tar.bz2

编译安装
[root@localhost ~]# cd libpam-google-authenticator-1.0
[root@localhost ~]# make && make install

修改ssh服务的配置
[root@localhost ~]# echo "auth required pam_google_authenticator.so" >> /etc/pam.d/sshd
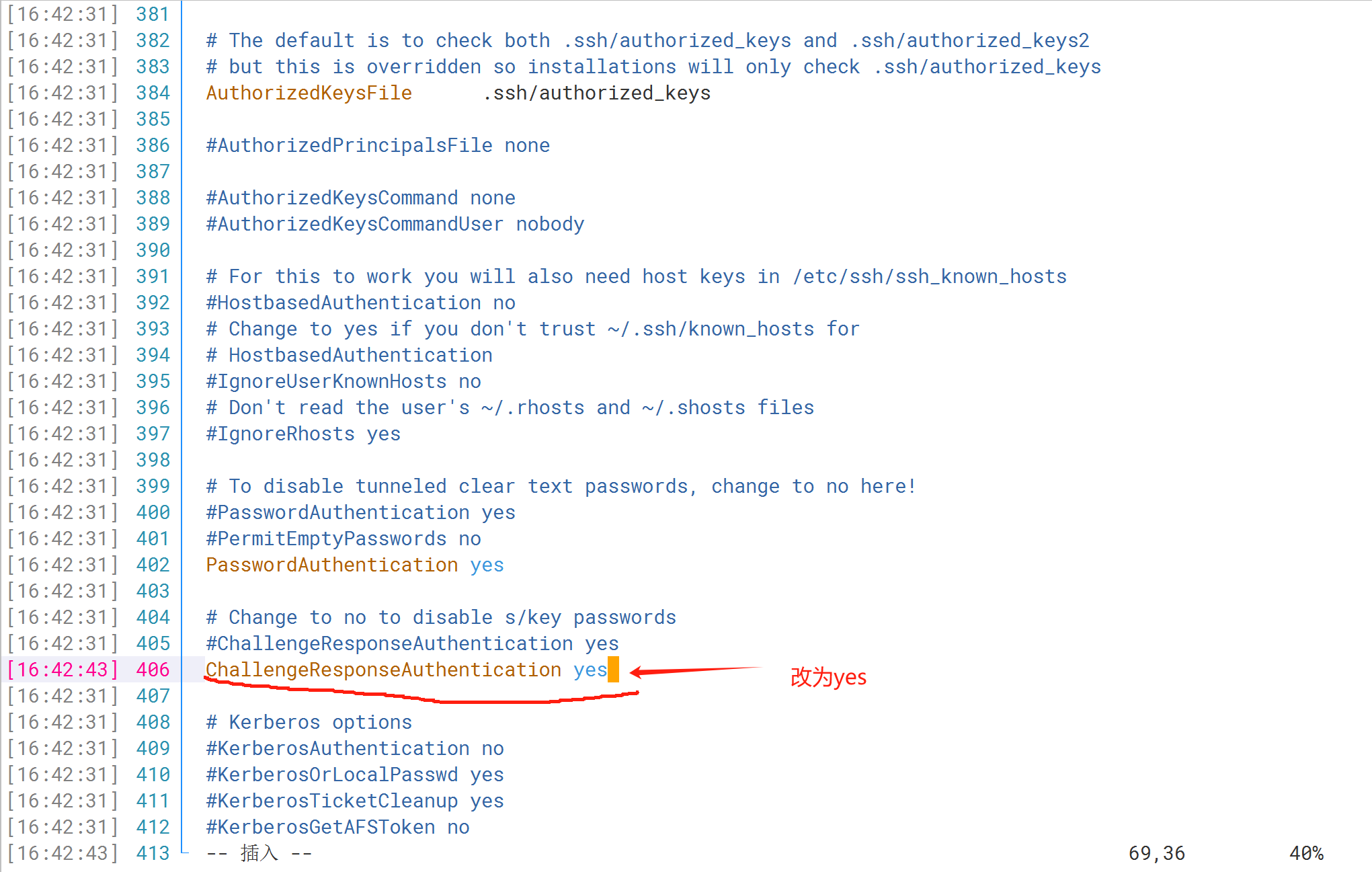
#修改sshd配置文件
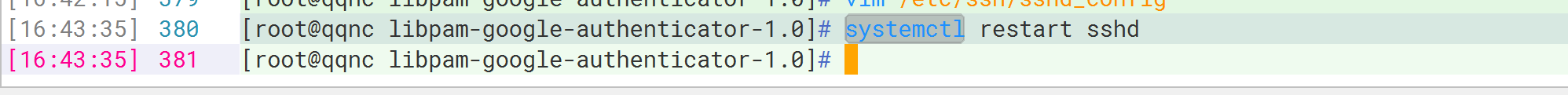
[root@localhost ~]# vim /etc/ssh/sshd_config
ChallengeResponseAuthentication yes
#重启sshd服务
[root@localhost ~]# systemctl restart sshd

使用令牌工具生成登录密钥
[root@localhost ~]# google-authenticator
google-authenticator
Do you want authentication tokens to be time-based (y/n) y
https://www.google.com/chart?chs=200x200&chld=M|0&cht=qr&chl=otpauth://totp/root@localhost.localdomain%3Fsecret%3DWLJCY4JSNGQNH454
Your new secret key is: WLJCY4JSNGQNH454
Your verification code is 635811
Your emergency scratch codes are:
18263912
56060832
39571822
20569639
90543013
Do you want me to update your "/root/.google_authenticator" file (y/n) y
Do you want to disallow multiple uses of the same authentication
token? This restricts you to one login about every 30s, but it increases
your chances to notice or even prevent man-in-the-middle attacks (y/n) y
By default, tokens are good for 30 seconds and in order to compensate for
possible time-skew between the client and the server, we allow an extra
token before and after the current time. If you experience problems with poor
time synchronization, you can increase the window from its default
size of 1:30min to about 4min. Do you want to do so (y/n) y
If the computer that you are logging into isn't hardened against brute-force
login attempts, you can enable rate-limiting for the authentication module.
By default, this limits attackers to no more than 3 login attempts every 30s.
Do you want to enable rate-limiting (y/n) n




















 579
579











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








