本实验均在centos7.2操作
实验之前请先关闭 iptables 和 SELinux
实验1:keepalived 高可用 lvs-dr测试
拓扑图如下:

实验操作
1,先配置两台web 站点
由于是基于dr模型,因此配置和lvs-dr配置类似
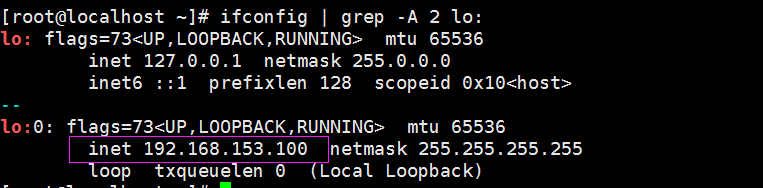
a,先配置VIP
echo 1 > /proc/sys/net/ipv4/conf/all/arp_ignore
echo 1 > /proc/sys/net/ipv4/conf/lo/arp_ignore
echo 2 > /proc/sys/net/ipv4/conf/lo/arp_announce
echo 2 > /proc/sys/net/ipv4/conf/all/arp_announce
ifconfig lo:0 192.168.153.100 netmask 255.255.255.255 broadcast 192.168.153.100 up
route add -host 192.168.153.100 dev lo:0
b,配置web服务
rs1:
yum install -y httpd
echo rs1 > /var/www/html/index.htmlrs2:
yum install -y httpd
echo rs2 > /var/www/html/index.htmlc,启动服务
iptables -F
setenforce 0
systemctl start httpd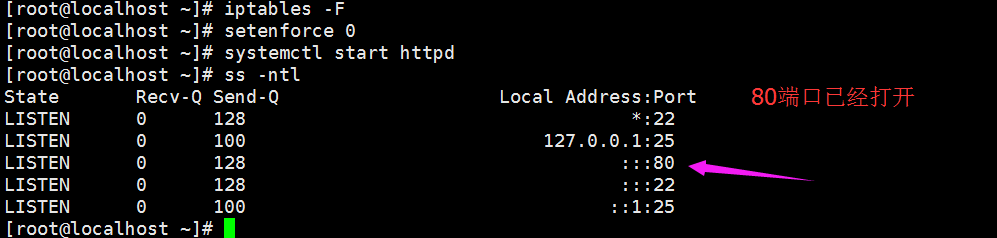
2,配置keepalived服务
a,安装程序包
yum install -y keepalivedb,修改配置文件
cd /etc/keepalived/
cp keepalived.conf{,.bak}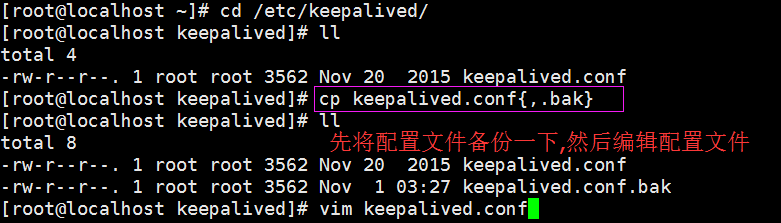
c,编写notify脚本,能够让我们及时知道服务器的运行状态
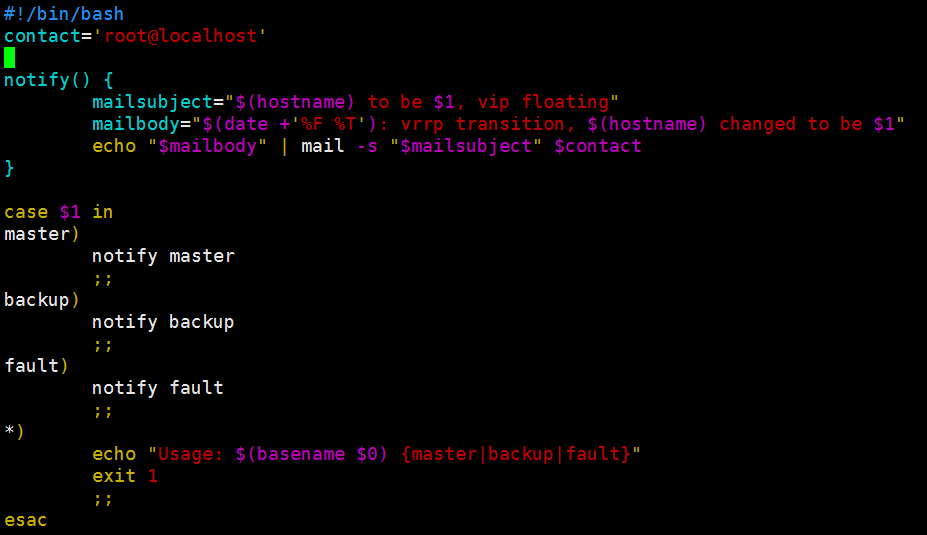
#!/bin/bash
contact='root@localhost'
notify() {
mailsubject="$(hostname) to be $1, vip floating"
mailbody="$(date +'%F %T'): vrrp transition, $(hostname) changed to be $1"
echo "$mailbody" | mail -s "$mailsubject" $contact
}
case $1 in
master)
notify master
;;
backup)
notify backup
;;
fault)
notify fault
;;
*)
echo "Usage: $(basename $0) {master|backup|fault}"
exit 1
;;
esac加上执行权限 chmod +x /etc/keepalived/notify.sh
d,生成keepalived通信的密码,最多8位,然后将密码填在

e,访问成功的状态码是200

f,对 /etc/keepalived/keepalived.conf 配置文件进行编辑
! Configuration File for keepalived
global_defs {
notification_email {
root@localhost
}
notification_email_from keepalived1@localhost
smtp_server 127.0.0.1
smtp_connect_timeout 30
router_id LVS_DEVEL
vrrp_mcast_group4 224.0.41.41
}
vrrp_instance VI_1 {
state MASTER
interface eno33554984
virtual_router_id 41
priority 100
advert_int 1
authentication {
auth_type PASS
auth_pass b8d99f88
}
virtual_ipaddress {
192.168.153.100
}
notify_master "/etc/keepalived/notify.sh master" #当前节点成为主节点时 ,然后触发该脚本
notify_backup "/etc/keepalived/notify.sh backup"
notify_fault "/etc/keepalived/notify.sh fault"
}
virtual_server 192.168.153.100 80 {
delay_loop 3 #服务轮询的时间间隔
lb_algo rr #轮询的调度方法
lb_kind DR # dr 模型的集群
protocol TCP #服务协议,仅支持TCP
sorry_server 127.0.0.1 80 #当web1,web2服务器都挂时,才启用该服务
real_server 192.168.153.130 80 {
weight 1 #服务器访问权重
HTTP_GET {
url {
path / #定义要监控的URL
status_code 200 #当请求状态码为200时,才说明该服务器健康检查通过
}
connect_timeout 1 #连接请求的超时时长
nb_get_retry 3 #重试次数
delay_before_retry 1 #重试之前的延迟时长
}
}
real_server 192.168.153.131 80 {
weight 1
HTTP_GET {
url {
path /
status_code 200
}
connect_timeout 1
nb_get_retry 3
delay_before_retry 1
}
}
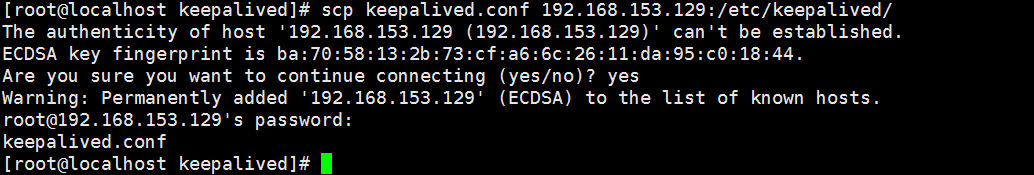
}3,将配置文件拷贝一份到备服务器,并做相应的修改
a,复制配置文件到备节点服务器
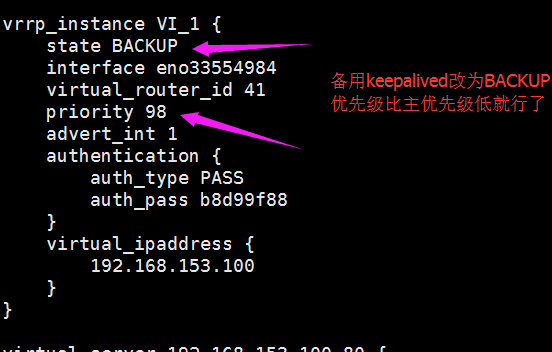
b,编辑备用配置文件
4,在keepalived上配置sorry_server
主节点:
yum install httpd -y
echo keepalived1 error > /var/www/html/index.html备节点:
yum install httpd -y
echo keepalived2 error > /var/www/html/index.html5,启动服务
iptables -F
setenforce 0
systemctl start httpd
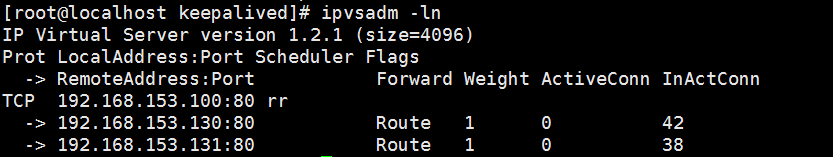
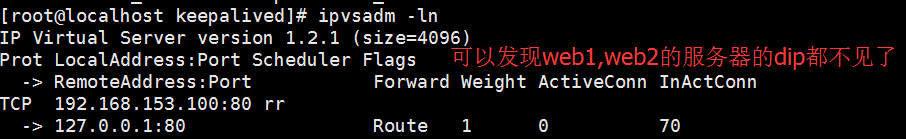
systemctl start keepalived在主节点上可以看到lvs自动配置好了
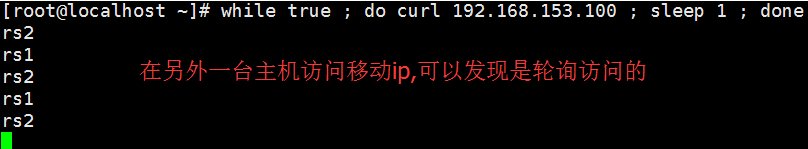
6,测试

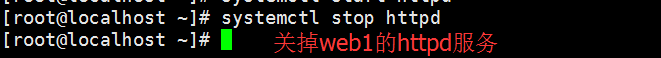
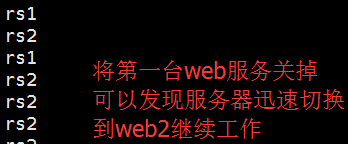
关闭web1,web2的httpd服务

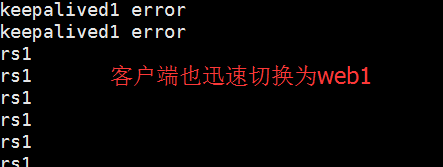
然后开启web1的服务

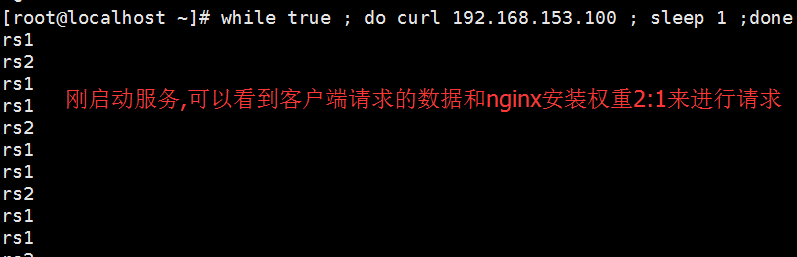
实验2:keepalived 高可用 nginx测试
1,只需要更改/etc/keepalived/keepalived.conf 配置文件
! Configuration File for keepalived
global_defs {
notification_email {
root@localhost
}
notification_email_from keepalived1@localhost
smtp_server 127.0.0.1
smtp_connect_timeout 30
router_id LVS_DEVEL
vrrp_mcast_group4 224.0.41.41
}
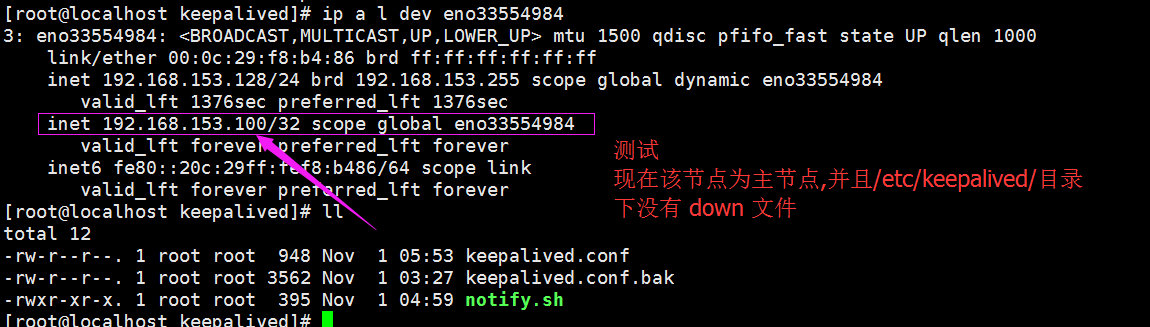
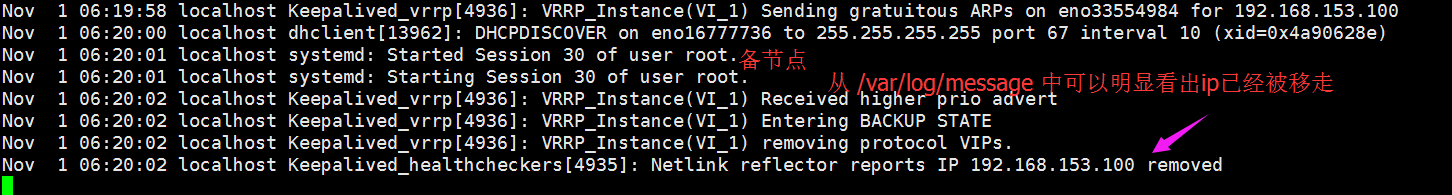
vrrp_script chk_nginx { #定义脚本
script "killall -0 nginx && exit 0 || exit 1" #当nginx进程不存在时,返回1
interval 1 #每一秒运行一次脚本
weight -5 #当返回值不是0时,执行 权重减去5 操作
}
vrrp_script chk_downfile {
script "[[ -f /etc/keepalived/down ]] && exit 1 || exit 0" #当/etc/keepalived/目录下存在 down 文件时,该节点的优先级减去5
interval 1
weight -5
}
vrrp_instance VI_1 {
state MASTER
interface eno33554984
virtual_router_id 41
priority 100
advert_int 1
authentication {
auth_type PASS
auth_pass b8d99f88
}
virtual_ipaddress {
192.168.153.100
}
track_script { #加载前面定义的脚本
chk_nginx
chk_downfile
}
notify_master "/etc/keepalived/notify.sh master"
notify_backup "/etc/keepalived/notify.sh backup"
notify_fault "/etc/keepalived/notify.sh fault"
}2,卸载httpd程序,安装nginx程序
yum remove -y httpd
yum install -y /share/nginx-1.10.2-1.el7.ngx.x86_64.rpm配置nginx服务
vim /etc/nginx/nginx.conf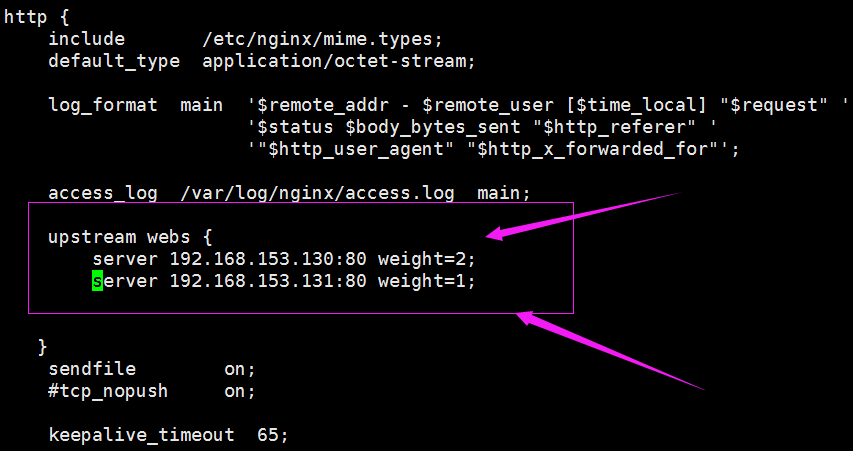
vim /etc/nginx/conf.d/default.conf
启动服务
systemctl start nginx
systemctl start keepalived测试:


























 263
263











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








