url地址:aHR0cHM6Ly9tcC53ZWl4aW4ucXEuY29tLw
第一步我们还是抓包分析流程

第一条数据包就是我们想要的,111111最终变成了pwd对应的值,如果是经常玩这类东西的直接可以去在线网站加密下,我常用的网站是spidertools.cn,里面东西是比较好用的,很全面。
然后跟调用栈
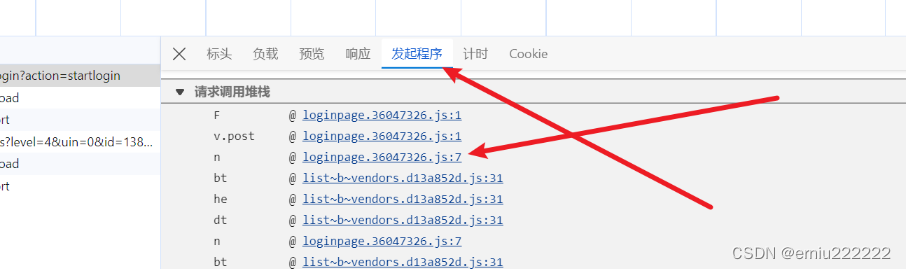
发起程序是可以看到从第一个函数到最后发起程序的函数,什么是函数调用栈,栈就是一个先进先出的一个存放东西的容器,所以说最后一个函数F是最先执行完然后出栈,然后是v.post。。。。,想更要的理解,我们可以找一个算法入门课,好好理解下,最重要的是写。
最后跟到了这里:
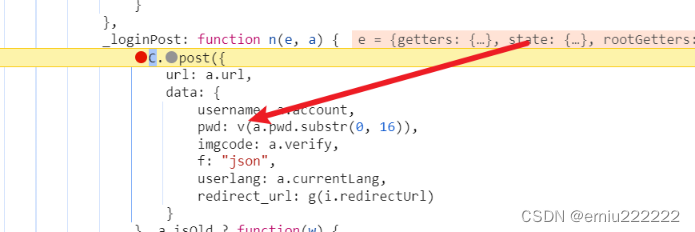
v函数此时可以把鼠标放在v函数上,然后点击FounctionLocation ,最后跳到了
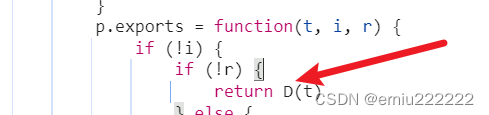
那么最重要的是D函数,我们此专栏是js逆向基础,所以比较细,尽可能讲清楚,讲透彻。
我把函数的内容给扣下来的,
function o(t, i) {
t[i >> 5] |= 128 << i % 32;
t[(i + 64 >>> 9 << 4) + 14] = i;
var r, f, j, O, $, s = 1732584193, c = -271733879, m = -1732584194, n = 271733878;
for (r = 0; r < t.length; r += 16) {
f = s;
j = c;
O = m;
$ = n;
s = S(s, c, m, n, t[r], 7, -680876936);
n = S(n, s, c, m, t[r + 1], 12, -389564586);
m = S(m, n, s, c, t[r + 2], 17, 606105819);
c = S(c, m, n, s, t[r + 3], 22, -1044525330);
s = S(s, c, m, n, t[r + 4], 7, -176418897);
n = S(n, s, c, m, t[r + 5], 12, 1200080426);
m = S(m, n, s, c, t[r + 6], 17, -1473231341);
c = S(c, m, n, s, t[r + 7], 22, -45705983);
s = S(s, c, m, n, t[r + 8], 7, 1770035416);
n = S(n, s, c, m, t[r + 9], 12, -1958414417);
m = S(m, n, s, c, t[r + 10], 17, -42063);
c = S(c, m, n, s, t[r + 11], 22, -1990404162);
s = S(s, c, m, n, t[r + 12], 7, 1804603682);
n = S(n, s, c, m, t[r + 13], 12, -40341101);
m = S(m, n, s, c, t[r + 14], 17, -1502002290);
c = S(c, m, n, s, t[r + 15], 22, 1236535329);
s = d(s, c, m, n, t[r + 1], 5, -165796510);
n = d(n, s, c, m, t[r + 6], 9, -1069501632);
m = d(m, n, s, c, t[r + 11], 14, 643717713);
c = d(c, m, n, s, t[r], 20, -373897302);
s = d(s, c, m, n, t[r + 5], 5, -701558691);
n = d(n, s, c, m, t[r + 10], 9, 38016083);
m = d(m, n, s, c, t[r + 15], 14, -660478335);
c = d(c, m, n, s, t[r + 4], 20, -405537848);
s = d(s, c, m, n, t[r + 9], 5, 568446438);
n = d(n, s, c, m, t[r + 14], 9, -1019803690);
m = d(m, n, s, c, t[r + 3], 14, -187363961);
c = d(c, m, n, s, t[r + 8], 20, 1163531501);
s = d(s, c, m, n, t[r + 13], 5, -1444681467);
n = d(n, s, c, m, t[r + 2], 9, -51403784);
m = d(m, n, s, c, t[r + 7], 14, 1735328473);
c = d(c, m, n, s, t[r + 12], 20, -1926607734);
s = g(s, c, m, n, t[r + 5], 4, -378558);
n = g(n, s, c, m, t[r + 8], 11, -2022574463);
m = g(m, n, s, c, t[r + 11], 16, 1839030562);
c = g(c, m, n, s, t[r + 14], 23, -35309556);
s = g(s, c, m, n, t[r + 1], 4, -1530992060);
n = g(n, s, c, m, t[r + 4], 11, 1272893353);
m = g(m, n, s, c, t[r + 7], 16, -155497632);
c = g(c, m, n, s, t[r + 10], 23, -1094730640);
s = g(s, c, m, n, t[r + 13], 4, 681279174);
n = g(n, s, c, m, t[r], 11, -358537222);
m = g(m, n, s, c, t[r + 3], 16, -722521979);
c = g(c, m, n, s, t[r + 6], 23, 76029189);
s = g(s, c, m, n, t[r + 9], 4, -640364487);
n = g(n, s, c, m, t[r + 12], 11, -421815835);
m = g(m, n, s, c, t[r + 15], 16, 530742520);
c = g(c, m, n, s, t[r + 2], 23, -995338651);
s = v(s, c, m, n, t[r], 6, -198630844);
n = v(n, s, c, m, t[r + 7], 10, 1126891415);
m = v(m, n, s, c, t[r + 14], 15, -1416354905);
c = v(c, m, n, s, t[r + 5], 21, -57434055);
s = v(s, c, m, n, t[r + 12], 6, 1700485571);
n = v(n, s, c, m, t[r + 3], 10, -1894986606);
m = v(m, n, s, c, t[r + 10], 15, -1051523);
c = v(c, m, n, s, t[r + 1], 21, -2054922799);
s = v(s, c, m, n, t[r + 8], 6, 1873313359);
n = v(n, s, c, m, t[r + 15], 10, -30611744);
m = v(m, n, s, c, t[r + 6], 15, -1560198380);
c = v(c, m, n, s, t[r + 13], 21, 1309151649);
s = v(s, c, m, n, t[r + 4], 6, -145523070);
n = v(n, s, c, m, t[r + 11], 10, -1120210379);
m = v(m, n, s, c, t[r + 2], 15, 718787259);
c = v(c, m, n, s, t[r + 9], 21, -343485551);
s = _(s, f);
c = _(c, j);
m = _(m, O);
n = _(n, $)
}
return [s, c, m, n]
}
function u(t) {
var i, r = "";
for (i = 0; i < t.length * 32; i += 8) {
r += String.fromCharCode(t[i >> 5] >>> i % 32 & 255)
}
return r
}
function b(t) {
var i, r = [];
r[(t.length >> 2) - 1] = void 0;
for (i = 0; i < r.length; i += 1) {
r[i] = 0
}
for (i = 0; i < t.length * 8; i += 8) {
r[i >> 5] |= (t.charCodeAt(i / 8) & 255) << i % 32
}
return r
}
function L(t) {
return u(o(b(t), t.length * 8))
}
function h(t, i) {
var r, f = b(t), j = [], O = [], $;
j[15] = O[15] = void 0;
if (f.length > 16) {
f = o(f, t.length * 8)
}
for (r = 0; r < 16; r += 1) {
j[r] = f[r] ^ 909522486;
O[r] = f[r] ^ 1549556828
}
$ = o(j.concat(b(i)), 512 + i.length * 8);
return u(o(O.concat($), 512 + 128))
}
function y(t) {
var i = "0123456789abcdef", r = "", f, j;
for (j = 0; j < t.length; j += 1) {
f = t.charCodeAt(j);
r += i.charAt(f >>> 4 & 15) + i.charAt(f & 15)
}
return r
}
function I(t) {
return unescape(encodeURIComponent(t))
}
function E(t) {
return L(I(t))
}
function D(t) {
return y(E(t))
}看到这些东西不要慌,不用慌,对待编程就是因为你看的少,用的少,多了就跟自己家亲戚一样熟悉,甭提多开心了。o函数里面还有函数,我并没有全部提出来,直接复制拷贝就行了。这个地方我重点是要分析u函数和b函数,为什么,因为随着后面的网站难度越来越大,类似u函数和b函数产生的结果你会见的越来越多,然后越不怕,这个地方我们就是要弄清楚原理。这两个函数我认为在后面慢慢更新的加密混淆js文件中以及vmp网站中都是很重要的。下面我们看这两个函数:
u函数:
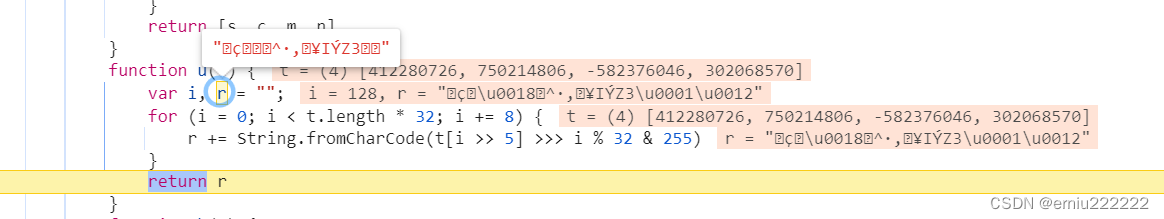
u传入了t,是一个数组,但是经过String.fromCharCode函数转换之后最后r编程了一群跟乱码的东西,是的,以后再看到这个东西不要慌,
String.fromCharCode(72,69,76,76,79) 这个就是hello字符串,为什么会显示出人们看不懂的东西,说白了这个就是因为fromCharCode传入的数字导致的比如:

还有非常多的与或非z左移右移:
r[i >> 5] |= (t.charCodeAt(i / 8) & 255) << i % 32
这些都是基于数字的二进制转换得来的。
比如说&,一般来说越来越小,因为两个数字的二进制对应位置都是1结果才是1
比如0010 和1111,最后是0010,也才是2.其他的位运算符自己考究。这些都是在vmp加密中非常常见的鹅运算,不要慌。现在把这些基础打牢了之后,后面会越来越顺了。这个地方你也可以分析下MD5的那个o函数,里面有位运算 。多看,你就慢慢会了
现在可以扣代码了。
最后全部的js代码:
function _(t, i) {
var r = (t & 65535) + (i & 65535)
, f = (t >> 16) + (i >> 16) + (r >> 16);
return f << 16 | r & 65535
}
function x(t, i) {
return t << i | t >>> 32 - i
}
function C(t, i, r, f, j, O) {
return _(x(_(_(i, t), _(f, O)), j), r)
}
function S(t, i, r, f, j, O, $) {
return C(i & r | ~i & f, t, i, j, O, $)
}
function d(t, i, r, f, j, O, $) {
return C(i & f | r & ~f, t, i, j, O, $)
}
function g(t, i, r, f, j, O, $) {
return C(i ^ r ^ f, t, i, j, O, $)
}
function v(t, i, r, f, j, O, $) {
return C(r ^ (i | ~f), t, i, j, O, $)
}
function o(t, i) {
t[i >> 5] |= 128 << i % 32;
t[(i + 64 >>> 9 << 4) + 14] = i;
var r, f, j, O, $, s = 1732584193, c = -271733879, m = -1732584194, n = 271733878;
for (r = 0; r < t.length; r += 16) {
f = s;
j = c;
O = m;
$ = n;
s = S(s, c, m, n, t[r], 7, -680876936);
n = S(n, s, c, m, t[r + 1], 12, -389564586);
m = S(m, n, s, c, t[r + 2], 17, 606105819);
c = S(c, m, n, s, t[r + 3], 22, -1044525330);
s = S(s, c, m, n, t[r + 4], 7, -176418897);
n = S(n, s, c, m, t[r + 5], 12, 1200080426);
m = S(m, n, s, c, t[r + 6], 17, -1473231341);
c = S(c, m, n, s, t[r + 7], 22, -45705983);
s = S(s, c, m, n, t[r + 8], 7, 1770035416);
n = S(n, s, c, m, t[r + 9], 12, -1958414417);
m = S(m, n, s, c, t[r + 10], 17, -42063);
c = S(c, m, n, s, t[r + 11], 22, -1990404162);
s = S(s, c, m, n, t[r + 12], 7, 1804603682);
n = S(n, s, c, m, t[r + 13], 12, -40341101);
m = S(m, n, s, c, t[r + 14], 17, -1502002290);
c = S(c, m, n, s, t[r + 15], 22, 1236535329);
s = d(s, c, m, n, t[r + 1], 5, -165796510);
n = d(n, s, c, m, t[r + 6], 9, -1069501632);
m = d(m, n, s, c, t[r + 11], 14, 643717713);
c = d(c, m, n, s, t[r], 20, -373897302);
s = d(s, c, m, n, t[r + 5], 5, -701558691);
n = d(n, s, c, m, t[r + 10], 9, 38016083);
m = d(m, n, s, c, t[r + 15], 14, -660478335);
c = d(c, m, n, s, t[r + 4], 20, -405537848);
s = d(s, c, m, n, t[r + 9], 5, 568446438);
n = d(n, s, c, m, t[r + 14], 9, -1019803690);
m = d(m, n, s, c, t[r + 3], 14, -187363961);
c = d(c, m, n, s, t[r + 8], 20, 1163531501);
s = d(s, c, m, n, t[r + 13], 5, -1444681467);
n = d(n, s, c, m, t[r + 2], 9, -51403784);
m = d(m, n, s, c, t[r + 7], 14, 1735328473);
c = d(c, m, n, s, t[r + 12], 20, -1926607734);
s = g(s, c, m, n, t[r + 5], 4, -378558);
n = g(n, s, c, m, t[r + 8], 11, -2022574463);
m = g(m, n, s, c, t[r + 11], 16, 1839030562);
c = g(c, m, n, s, t[r + 14], 23, -35309556);
s = g(s, c, m, n, t[r + 1], 4, -1530992060);
n = g(n, s, c, m, t[r + 4], 11, 1272893353);
m = g(m, n, s, c, t[r + 7], 16, -155497632);
c = g(c, m, n, s, t[r + 10], 23, -1094730640);
s = g(s, c, m, n, t[r + 13], 4, 681279174);
n = g(n, s, c, m, t[r], 11, -358537222);
m = g(m, n, s, c, t[r + 3], 16, -722521979);
c = g(c, m, n, s, t[r + 6], 23, 76029189);
s = g(s, c, m, n, t[r + 9], 4, -640364487);
n = g(n, s, c, m, t[r + 12], 11, -421815835);
m = g(m, n, s, c, t[r + 15], 16, 530742520);
c = g(c, m, n, s, t[r + 2], 23, -995338651);
s = v(s, c, m, n, t[r], 6, -198630844);
n = v(n, s, c, m, t[r + 7], 10, 1126891415);
m = v(m, n, s, c, t[r + 14], 15, -1416354905);
c = v(c, m, n, s, t[r + 5], 21, -57434055);
s = v(s, c, m, n, t[r + 12], 6, 1700485571);
n = v(n, s, c, m, t[r + 3], 10, -1894986606);
m = v(m, n, s, c, t[r + 10], 15, -1051523);
c = v(c, m, n, s, t[r + 1], 21, -2054922799);
s = v(s, c, m, n, t[r + 8], 6, 1873313359);
n = v(n, s, c, m, t[r + 15], 10, -30611744);
m = v(m, n, s, c, t[r + 6], 15, -1560198380);
c = v(c, m, n, s, t[r + 13], 21, 1309151649);
s = v(s, c, m, n, t[r + 4], 6, -145523070);
n = v(n, s, c, m, t[r + 11], 10, -1120210379);
m = v(m, n, s, c, t[r + 2], 15, 718787259);
c = v(c, m, n, s, t[r + 9], 21, -343485551);
s = _(s, f);
c = _(c, j);
m = _(m, O);
n = _(n, $)
}
return [s, c, m, n]
}
function u(t) {
var i, r = "";
for (i = 0; i < t.length * 32; i += 8) {
r += String.fromCharCode(t[i >> 5] >>> i % 32 & 255)
}
return r
}
function b(t) {
var i, r = [];
r[(t.length >> 2) - 1] = void 0;
for (i = 0; i < r.length; i += 1) {
r[i] = 0
}
for (i = 0; i < t.length * 8; i += 8) {
r[i >> 5] |= (t.charCodeAt(i / 8) & 255) << i % 32
}
return r
}
function L(t) {
return u(o(b(t), t.length * 8))
}
function h(t, i) {
var r, f = b(t), j = [], O = [], $;
j[15] = O[15] = void 0;
if (f.length > 16) {
f = o(f, t.length * 8)
}
for (r = 0; r < 16; r += 1) {
j[r] = f[r] ^ 909522486;
O[r] = f[r] ^ 1549556828
}
$ = o(j.concat(b(i)), 512 + i.length * 8);
return u(o(O.concat($), 512 + 128))
}
function y(t) {
var i = "0123456789abcdef", r = "", f, j;
for (j = 0; j < t.length; j += 1) {
f = t.charCodeAt(j);
r += i.charAt(f >>> 4 & 15) + i.charAt(f & 15)
}
return r
}
function I(t) {
return unescape(encodeURIComponent(t))
}
function E(t) {
return L(I(t))
}
function D(t) {
return y(E(t))
};
D("111111");新手小白可以直接在浏览器建一个脚本片段就可以了
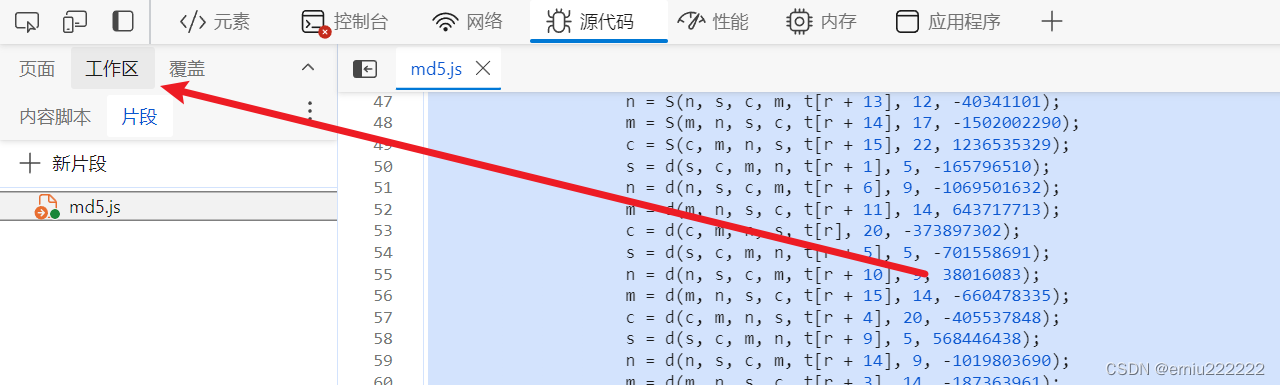
一般我都是开一个无痕的页面这样的好处是如果你安装了一些浏览器插件,他加载的js代码会有影响的
python实现md5:
import hashlib
md5 = hashlib.md5()
md5.update("1111".encode())
value = md5.digest()
print(value.hexdigest())
// 以后只要遇到字节类型的就可以往hex转换,hex是可以转换为字符
以上就是分析过程,以及需要注意的几个地方,后面随着难度的加大,这些东西都会在混淆的代码中看到的。






















 1108
1108











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








