RSA
#!/usr/bin/env python3
import gmpy2
from Crypto.Util.number import getPrime
from Crypto.PublicKey import RSA
from Crypto.Cipher import PKCS1_v1_5
from base64 import b64encode
flag = open('flag', 'r').read().strip() * 23
def encrypt(p, q, e, msg):
while True:
n = p * q
try:
phi = (p - 1)*(q - 1)
pubkey = RSA.construct((int(n), int(e)))
key = PKCS1_v1_5.new(pubkey)
enc = b64encode(key.encrypt(msg))
return enc
except:
p = gmpy2.next_prime(p**2 + q**2)
q = gmpy2.next_prime(2*p*q)
e = gmpy2.next_prime(e**2)
p = getPrime(128)
q = getPrime(128)
n = p*q
e = getPrime(64)
pubkey = RSA.construct((n, e))
with open('pubkey.pem', 'wb') as f:
f.write(pubkey.exportKey())
with open('flag.enc', 'wb') as g:
g.write(encrypt(p, q, e, flag.encode()))
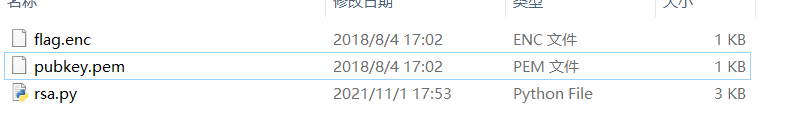
先公钥解析,得到e、n,然后在线分解n,得到p、q
e = 9850747023606211927
n = 62078208638445817213739226854534031566665495569130972218813975279479576033261
p = 184333227921154992916659782580114145999
q = 336771668019607304680919844592337860739
根据题目代码我们知道并不一定使用解出来的这几个数加密的,
打开密文我们发现,n是小于c的,所以需要先找出来真正的公钥才能解密
import gmpy2
from base64 import b64decode
from Crypto.Util.number import *
e = 9850747023606211927
n = 62078208638445817213739226854534031566665495569130972218813975279479576033261
p = 184333227921154992916659782580114145999
q = 336771668019607304680919844592337860739
c ='DWsGDe5mZXvs8l4kHjjteTLbV4rJ9JHwpUrZaQ/eqPT2YYiHwalRHZeobzcKRbBvcvqf1NYwJCuFwpDOnWK73bnQO06HaHdsSnRCqCy7slRnhs4QSIWkpeA3RlzSrDb/oNbuT8t/+HhlZbooWiCywnTsZWGjWwFvaGCvhEkZCLR17OB/7ZxXYhHaUCcyGmLGjpYEZGqGKU80Lu6VGenRRxmg4qsVI6T/GgXQjSZT43mIXCD+5g7zVUIfFAMQKYmwcYNWxOJZm7P9EbYQUTYNDU96hIgxrVCaMV7c1m5oLYdm99OkfyOk/lQ67KZLjSJIOSCmaJ3bHpuqDXdHPuxv9daB+31qu9eWQl2WuyuzM9U0Cd+oR+xMJcdGvLk/8wm+CPhkwnmMSVkYb7qXvaFZcap8/F5ZbzFAHLl+YKFsisRIq8iLQc1lttW7/E3dt4ds+ixfPakErgVUzKaziSDG1Ja/byqV9VdmqR0TCAtcIfmVZHu+doO1HnOJlmIb6IDwuBSwba825/E4sMM24RK/PscuXaAQGAkyKI+apX7PUObFE6XA7KMSDleikIQ7HYFsGJISGzbP0mX6iFn8qoUI82p98y2grsNBGKm3uBb3Zump8eqgJh5MMdiPCRir5uRPZpT6weepqr3i7uPTLy91QpXeG7b2OowRs6MmEB8vxyLkhIJvJrNTehXmb/2EXJwXQBEqiDAJ0+0QE0PUsegHqcYIoMNtHFt4UPX7Dm2p+Mi9a+fnXzC9GMUwqcL6JXG8W6V9yWSUBoG2mIhCX/dM2Cnrm3wprccV+Hi4gdnEfRKuDjuVBAJ0kBQrGjwK1JgoWbIItmwxGKu70olIwQN7LspUCiJH3Bkalo9crFTDGFJr7qBdMz2+7FBb7hYT9mLSxAo1UoZYtraQJoxNJQs81rG8IPq27upPj6xenTFYHhSRnJwEFAOvam2+rXTnyQO2DME='
c = bytes_to_long(c.encode())
while True:
if n >= c:
phi = (q-1) * (p-1)
d = gmpy2.invert(e,phi)
m = pow(c,int(d),n)
break
else:
p = gmpy2.next_prime(p**2 + q**2)
q = gmpy2.next_prime(2*p*q)
e = gmpy2.next_prime(e**2)
n=q*p
print(long_to_bytes(m//23))
运行得到

还是不对啊
在攻防世界看的题,看了WP依旧没整出来🤯

不仅仅是RSA

from flag import flag
from Crypto.Util.number import *
import random
p=getPrime(256)
q=getPrime(256)
e=random.randint(1,65537)
n=p*q
m=bytes_to_long(flag1)
c=pow(m,e,n)
print c,e,n
p=getPrime(256)
n=p*q
m=bytes_to_long(flag2)
c=pow(m,e,n)
print c,e,n
先解析两个公钥
得到
e = 41221
n1 = 10285341668836655607404515118077620322010982612318568968318582049362470680277495816958090140659605052252686941748392508264340665515203620965012407552377979
n2 = 8559553750267902714590519131072264773684562647813990967245740601834411107597211544789303614222336972768348959206728010238189976768204432286391096419456339
根据题意可以解出q和两个p
import gmpy2
q = gmpy2.gcd(n1,n2)
print(q)
#q=95652716952085928904432251307911783641637100214166105912784767390061832540987
p1 = n1//q
#p1=107527961531806336468215094056447603422487078704170855072884726273308088647617
p2 = n2//q
#p2=89485735722023752007114986095340626130070550475022132484632643785292683293897
下面就是解密了,根据拿到的附件,可以得到
c1=4314251881242803343641258350847424240197348270934376293792054938860756265727535163218661012756264314717591117355736219880127534927494986120542485721347351
c2=485162209351525800948941613977942416744737316759516157292410960531475083863663017229882430859161458909478412418639172249660818299099618143918080867132349
解密
phi1 = (q-1) * (p1-1)
d1 = gmpy2.invert(e,phi1)
m1 = gmpy2.powmod(c1,d1,n1)
phi2 = (q-1) * (p2-1)
d2 = gmpy2.invert(e,phi2)
m2 = gmpy2.powmod(c2,d2,n2)
print(long_to_bytes(m1))
print(long_to_bytes(m2))
得到
b'UNCTF{ac01dff95336a'
b'a470e3b55d3fe43e9f6}'
连起来就行了






















 6569
6569











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








