实验要求:

实验步骤:
1、规划IP地址,搭建拓扑:
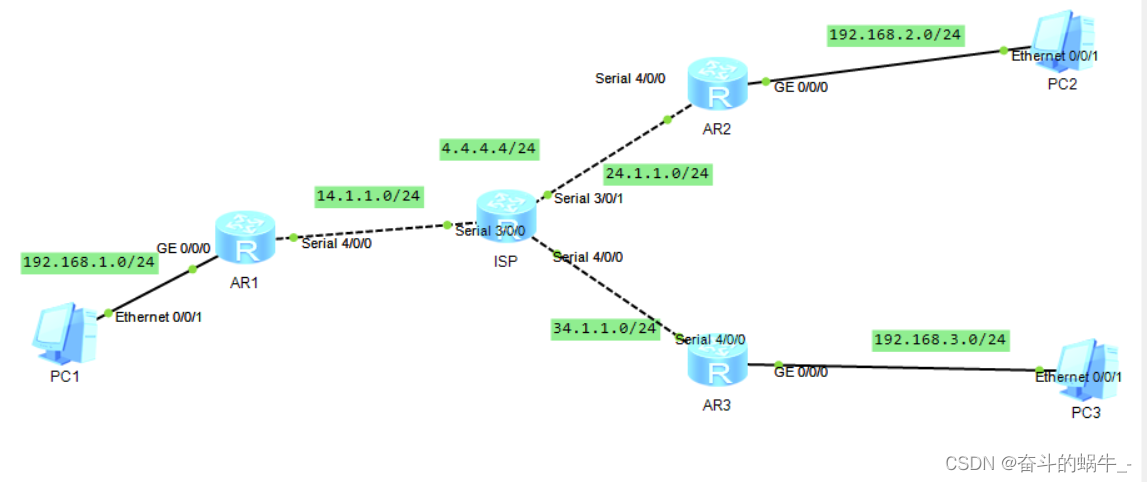
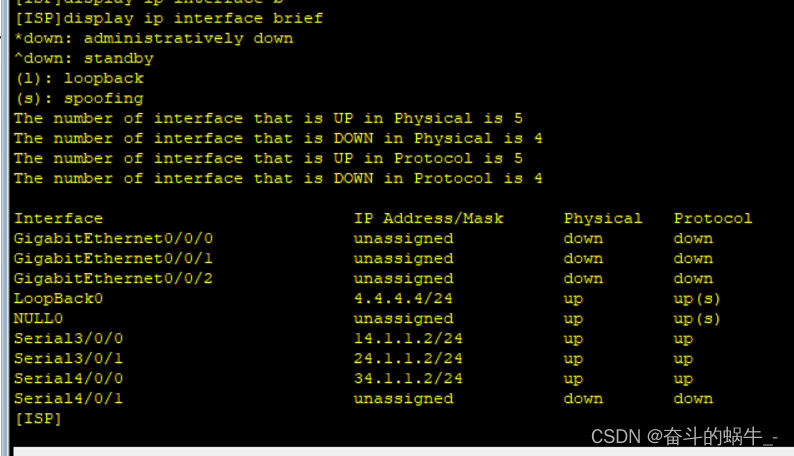
其中ISP的IP地址配置如下: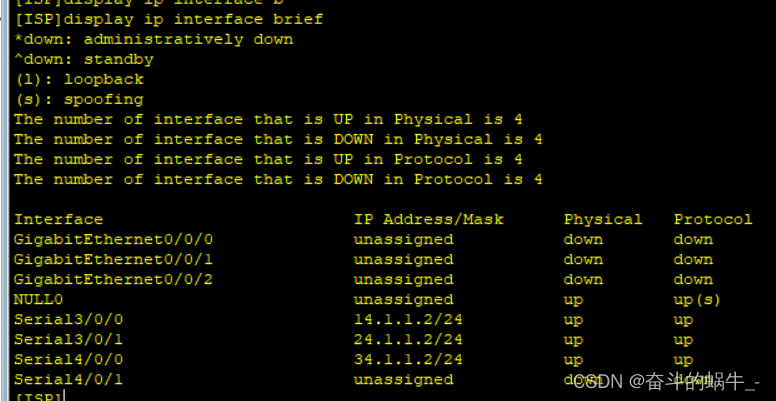
2、进行认证:
1)创建两个账号并定义服务类型为ppp
[ISP]aaa
[ISP-aaa]local-user a password cipher 123456
Info: Add a new user.
[ISP-aaa]local-user a service-type ppp
[ISP-aaa]local-user b password cipher 654321
Info: Add a new user.
[ISP-aaa]local-user b service-type ppp
2)做认证
[ISP]int s3/0/0
[ISP-Serial3/0/0]link-protocol hdlc #做hdlc认证
[ISP]int s3/0/1
[ISP-Serial3/0/1]ppp authentication-mode pap #做pap认证
[ISP]int s4/0/0
[ISP-Serial4/0/0]ppp authentication-mode chap #做chap认证
[R1-Serial4/0/0]link-protocol hdlc
[R2-Serial4/0/0]ppp pap local-user a password cipher 123456
[R3-Serial4/0/0]ppp chap user b
[R3-Serial4/0/0]ppp chap password cipher 654321
3、写公网的路由
[R1]ip route-static 0.0.0.0 0 14.1.1.2
[R2]ip route-static 0.0.0.0 0 24.1.1.2
[R3]ip route-static 0.0.0.0 0 34.1.1.2
4、做MGRE
[R1]interface Tunnel 0/0/0
[R1-Tunnel0/0/0]ip address 192.168.4.1 24
[R1-Tunnel0/0/0]tunnel-protocol gre p2mp
[R1-Tunnel0/0/0]source 14.1.1.1
[R1-Tunnel0/0/0]nhrp entry multicast dynamic
[R1-Tunnel0/0/0]nhrp network-id 100
[R2]int t0/0/0
[R2-Tunnel0/0/0]ip address 192.168.4.2 24
[R2-Tunnel0/0/0]tunnel-protocol gre p2mp
[R2-Tunnel0/0/0]source Serial 4/0/0
[R2-Tunnel0/0/0]nhrp entry 192.168.4.1 14.1.1.1 register
[R2-Tunnel0/0/0]nhrp network-id 100
[R3]int t0/0/0
[R3-Tunnel0/0/0]ip address 192.168.4.3 24
[R3-Tunnel0/0/0]tunnel-protocol gre p2mp
[R3-Tunnel0/0/0]source s4/0/0
[R3-Tunnel0/0/0]nhrp entry 192.168.4.1 14.1.1.1 register
[R3-Tunnel0/0/0]nhrp network-id 100
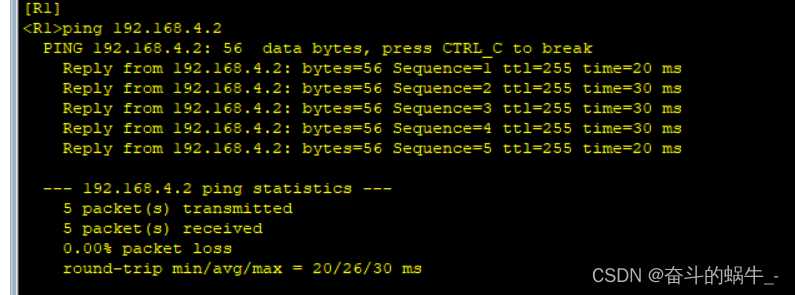
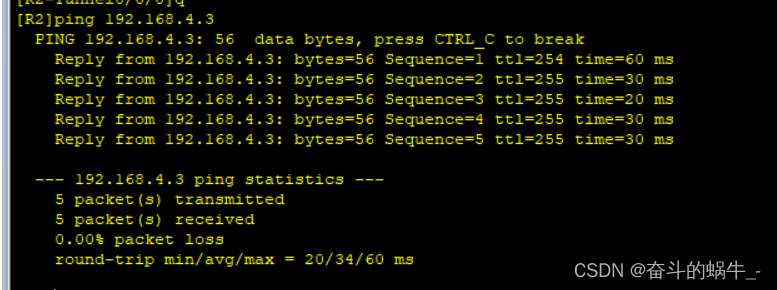
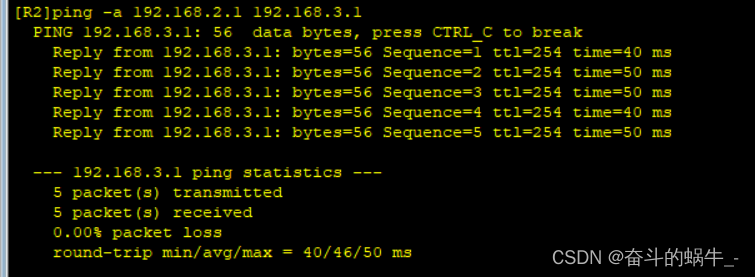
测试:
5、使用rip写路由
[R1]rip 1
[R1-rip-1]version 2
[R1-rip-1]network 192.168.1.0
[R1-rip-1]network 192.168.4.0
[R2-rip-1]network 192.168.2.0
[R2-rip-1]network 192.168.4.0
[R3-rip-1]network 192.168.3.0
[R3-rip-1]network 192.168.4.0
[R1-Tunnel0/0/0]undo rip split-horizon #由于rip有水平分割机制,需要在R1去关闭rip的水分割
6、做nat,使pc可以访问公网
[R1]acl 2000
[R1-acl-basic-2000]rule permit source 192.168.1.0 0.0.0.255
[R1-acl-basic-2000]q
[R1]int s4/0/0
[R1-Serial4/0/0]nat outbound 2000
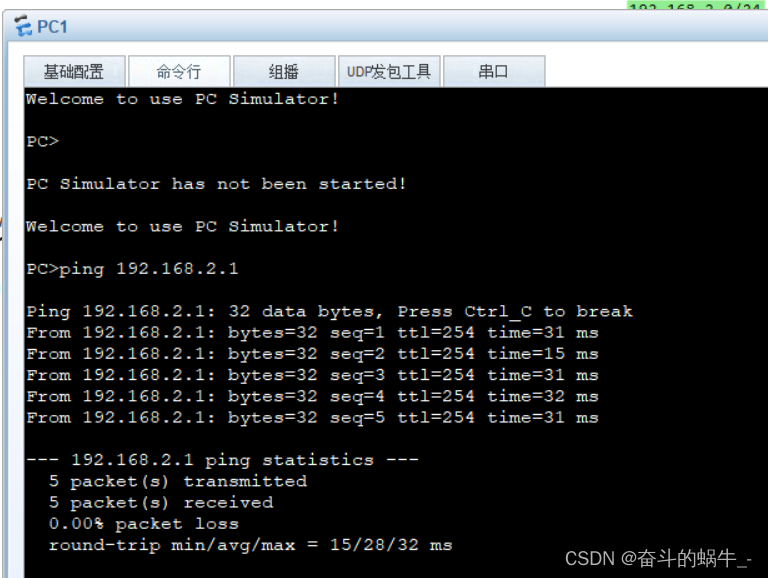
实验结果:
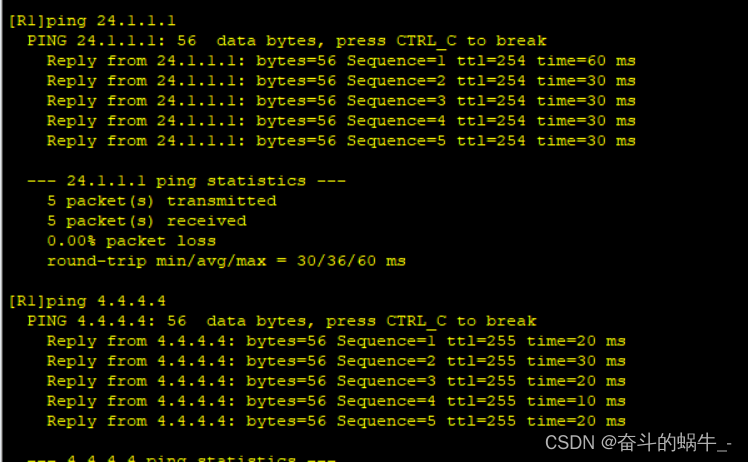
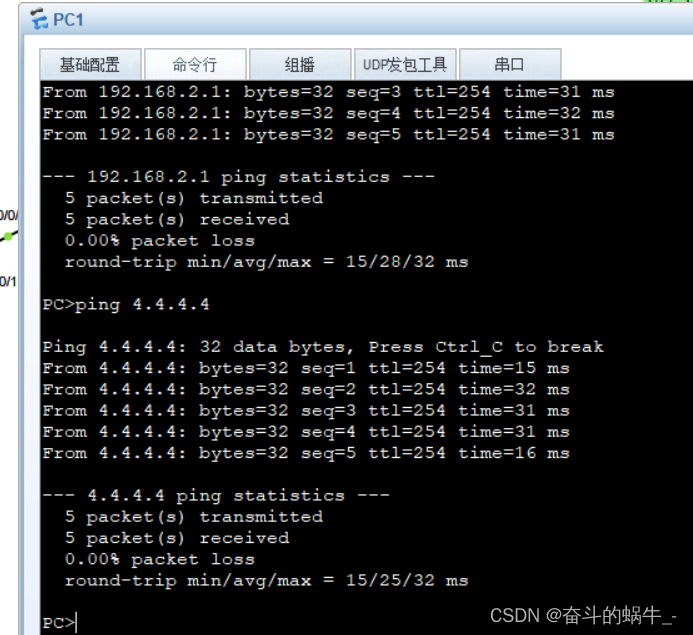
测试pc间可以相互ping通:
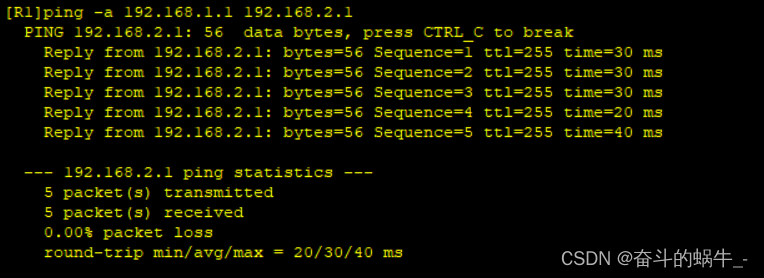
测试pc去ping通4.4.4.4环回:





















 184
184











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








