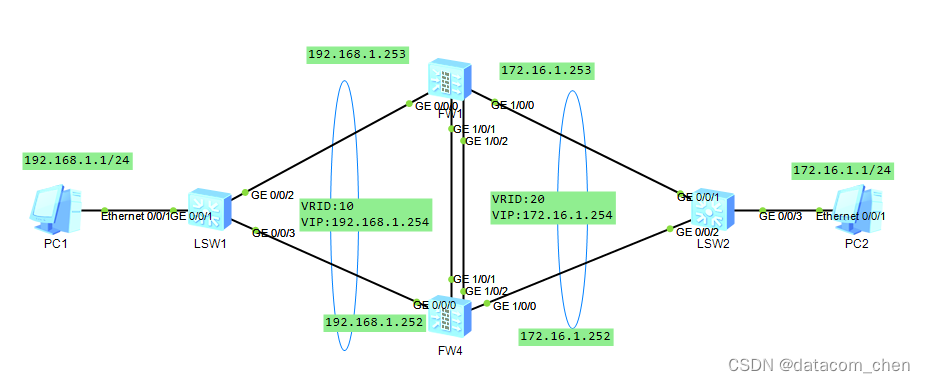
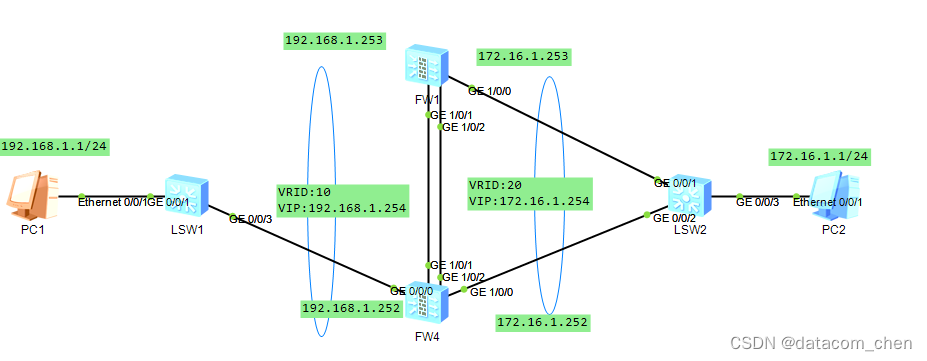
实验拓扑
双机热备技术产生的背景
传统的组网方式如下所示,内部用户和外部用户的交互报文全部通过防火墙A。如果防火墙A出现故障,内部网络中所有以防火墙A作为默认网关的主机与外部网络之间的通讯将中断,通讯可靠性无法保证
VRRP
基于VRRP的路由器冗余部署方案
VRRP(Virtual Router Redundancy Protocol)是一种容错协议,它保证当主机的下一跳路由器(默认网关)出现故障时,由备份路由器自动代替出现故障的路由器完成报文转发任务,从而保持网络通信的连续性和可靠性。同一VRRP备份组内的路由器有两种角色:master,buackup
实验目的
防火墙使用双击热备,形成主备避免单点故障影响业务报文转发。使用VRRP虚拟出终端的网关地址,并使用VGMP来保证所有VRRP备份组切换的一致性,避免来回路径不一致,防火墙态检测机制检测不通过,报文丢弃。防火墙之间部署心跳链路,用于交互消息了解对端状态,备份配置命令和各种表项通道
实验步骤
IP部署
交换机此场景作为傻瓜交换机的角色,无需配置


FW1:
#
interface GigabitEthernet0/0/0
undo shutdown
ip address 192.168.1.253 255.255.255.0
#
interface GigabitEthernet1/0/0
undo shutdown
ip address 172.16.1.253 255.255.255.0
#
firewall zone trust
set priority 85
add interface GigabitEthernet0/0/0
#
firewall zone untrust
set priority 5
add interface GigabitEthernet1/0/0
FW4:
#
interface GigabitEthernet0/0/0
undo shutdown
ip address 192.168.1.252 255.255.255.0
#
interface GigabitEthernet1/0/0
undo shutdown
ip address 172.16.1.252 255.255.255.0
#
firewall zone trust
set priority 85
add interface GigabitEthernet0/0/0
#
firewall zone untrust
set priority 5
add interface GigabitEthernet1/0/0
VRRP配置
FW1:
#
interface GigabitEthernet0/0/0
vrrp vrid 10 virtual-ip 192.168.1.254 active
#
interface GigabitEthernet1/0/0
vrrp vrid 20 virtual-ip 172.16.1.254 active
FW4:
#
interface GigabitEthernet0/0/0
vrrp vrid 10 virtual-ip 192.168.1.254 standby
#
interface GigabitEthernet1/0/0
vrrp vrid 20 virtual-ip 172.16.1.254 standby
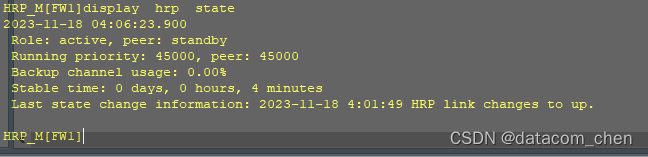
HRP配置
FW1:
#
interface Eth-Trunk1
ip address 1.1.1.1 255.255.255.252
mode lacp-static
#
interface GigabitEthernet1/0/1
eth-trunk 1
#
interface GigabitEthernet1/0/2
eth-trunk 1
#
firewall zone dmz
set priority 50
add interface Eth-Trunk1
#
hrp interface Eth-Trunk1 remote 1.1.1.2
hrp enable
FW4:
#
interface Eth-Trunk1
ip address 1.1.1.2 255.255.255.252
mode lacp-static
#
interface GigabitEthernet1/0/1
eth-trunk 1
#
interface GigabitEthernet1/0/2
eth-trunk 1
#
firewall zone dmz
set priority 50
add interface Eth-Trunk1
#
hrp interface Eth-Trunk1 remote 1.1.1.1
hrp enable


安全策略放行
HRP_M:
#
security-policy
rule name pc
source-zone trust
destination-zone untrust
source-address 192.168.1.0 mask 255.255.255.0
destination-address 172.16.1.0 mask 255.255.255.0
action permit
rule name pc2
source-zone untrust
destination-zone trust
source-address 172.16.1.0 mask 255.255.255.0
destination-address 192.168.1.0 mask 255.255.255.0
action permit
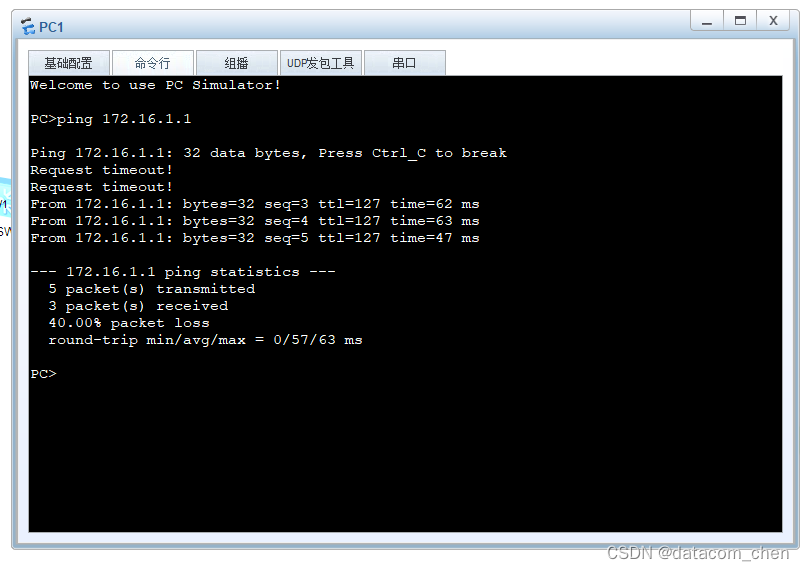
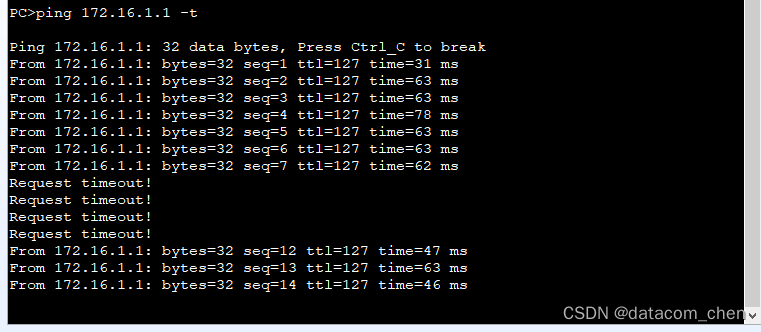
把FW1的 0/0/0接口down之后,FW4成为VRRP组的master,在主备切换的过程中,还是会出现丢包的情况。但很快就恢复了























 411
411











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










