文章目录
- 一、相关包下载
- 二、K8S单节点部署
- (一)、部署环境
- (二)、docker引擎部署
- (三)、flannel网络配置
- (四)、部署master组件
- (五)、node节点部署
-
- 1、把 kubelet、kube-proxy拷贝到node节点上去
- 2、复制node.zip到/root目录下再解压
- 在master上操作
- 1、获取token信息
- 2、配置文件修改为tokenID
- 3、设置环境变量(可以写入到/etc/profile中)
- 4、生成配置文件
- 5、拷贝配置文件到node节点
- 6、创建bootstrap角色赋予权限用于连接apiserver请求签名(关键)
- 在node01节点上操作
- master上操作
- 在node1节点操作
- node2节点部署
- 1、在node1节点操作把现成的/opt/kubernetes目录复制到其他节点进行修改
- 2、把kubelet,kube-proxy的service文件拷贝到node2中
- 在node2上操作,进行修改
- 1、首先删除复制过来的证书,等会node02会自行申请证书
- 2、修改配置文件kubelet kubelet.config kube-proxy(三个配置文件)
- 3、启动服务
- 在master上操作
- 1、查看node2的申请证书请求
- 2、授权许可加入群集
- 3、查看群集中的节点
一、相关包下载


二、K8S单节点部署
(一)、部署环境
Master1:192.168.2.3/24 kube-apiserver、kube-controller-manager、kube-scheduler、etcd
Node01:192.168.2.5/24 kubelet、kube-proxy、docker、flannel、etcd
Node02:192.168.2.6/24 kubelet、kube-proxy、docker、flannel、etcd
1、ETCD组件部署
master1上进行操作
Master1:192.168.2.3/24
mkdir k8s
cd k8s/
ls #将以下两个脚本文件上传到该目录下
etcd-cert.sh etcd.sh #etcd-cert.sh为etcd证书的脚本,etcd.sh为etcd服务的脚本
mkdir etcd-cert
ls
etcd-cert etcd-cert.sh etcd.sh
mv etcd-cert.sh etcd-cert

2、下载证书制作工具
vim cfssl.sh
curl -L https://pkg.cfssl.org/R1.2/cfssl_linux-amd64 -o /usr/local/bin/cfssl
curl -L https://pkg.cfssl.org/R1.2/cfssljson_linux-amd64 -o /usr/local/bin/cfssljson
curl -L https://pkg.cfssl.org/R1.2/cfssl-certinfo_linux-amd64 -o /usr/local/bin/cfssl-certinfo
chmod +x /usr/local/bin/cfssl /usr/local/bin/cfssljson /usr/local/bin/cfssl-certinfo
3、下载cfssl官方包
bash cfssl.sh
ls /usr/local/bin/
cfssl cfssl-certinfo cfssljson
4、开始制作证书
//cfssl 生成证书工具 , cfssljson通过传入json文件生成证书,cfssl-certinfo查看证书信息
#定义ca证书
cd /root/k8s/etcd-cert
cat > ca-config.json <<EOF
{
"signing": {
"default": {
"expiry": "87600h"
},
"profiles": {
"www": {
"expiry": "87600h",
"usages": [
"signing",
"key encipherment",
"server auth",
"client auth"
]
}
}
}
}
EOF
#实现证书签名
cd /root/k8s/etcd-cert
cat > ca-csr.json <<EOF
{
"CN": "etcd CA",
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "Beijing",
"ST": "Beijing"
}
]
}
EOF
#生成证书,生成ca-key.pem ca.pem
cfssl gencert -initca ca-csr.json | cfssljson -bare ca -
2021/04/13 13:19:48 [INFO] generating a new CA key and certificate from CSR
2021/04/13 13:19:48 [INFO] generate received request
2021/04/13 13:19:48 [INFO] received CSR
2021/04/13 13:19:48 [INFO] generating key: rsa-2048
2021/04/13 13:19:49 [INFO] encoded CSR
2021/04/13 13:19:49 [INFO] signed certificate with serial number 36828712204036107587321214078699700178250931588
5、指定etcd三个节点之间的通信验证
cd /root/k8s/etcd-cert
cat > server-csr.json <<EOF
{
"CN": "etcd",
"hosts": [
"192.168.2.3",
"192.168.2.5",
"192.168.2.6"
],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "BeiJing",
"ST": "BeiJing"
}
]
}
EOF
6、生成ETCD证书 server-key.pem server.pem
cd /root/k8s/etcd-cert
[root@localhost etcd-cert]# cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=www server-csr.json | cfssljson -bare server
2021/04/13 13:21:25 [INFO] generate received request
2021/04/13 13:21:25 [INFO] received CSR
2021/04/13 13:21:25 [INFO] generating key: rsa-2048
2021/04/13 13:21:25 [INFO] encoded CSR
2021/04/13 13:21:25 [INFO] signed certificate with serial number 488589095033954658131322858624660543066591287663
2021/04/13 13:21:25 [WARNING] This certificate lacks a "hosts" field. This makes it unsuitable for
websites. For more information see the Baseline Requirements for the Issuance and Management
of Publicly-Trusted Certificates, v.1.1.6, from the CA/Browser Forum (https://cabforum.org);
specifically, section 10.2.3 ("Information Requirements").
[root@localhost etcd-cert]# ls
ca-config.json ca-key.pem server.csr server.pem
ca.csr ca.pem server-csr.json
ca-csr.json etcd-cert.sh server-key.pem
#ETCD 二进制包地址
https://github.com/etcd-io/etcd/releases
7、将以下三个压缩包上传到 /root/k8s 目录中
cd ~/k8s/
ls
cfssl.sh etcd.sh flannel-v0.10.0-linux-amd64.tar.gz
etcd-cert etcd-v3.3.10-linux-amd64.tar.gz kubernetes-server-linux-amd64.tar.gz
tar zxvf etcd-v3.3.10-linux-amd64.tar.gz
ls etcd-v3.3.10-linux-amd64
Documentation etcdctl README.md
etcd README-etcdctl.md READMEv2-etcdctl.md
mkdir /opt/etcd/{
cfg,bin,ssl} -p //cfg:配置文件,bin:命令文件,ssl:证书
mv etcd-v3.3.10-linux-amd64/etcd etcd-v3.3.10-linux-amd64/etcdctl /opt/etcd/bin/
ls /opt/etcd/bin/
etcd etcdctl
8、证书拷贝
cp etcd-cert/*.pem /opt/etcd/ssl/
ls /opt/etcd/ssl/
ca-key.pem ca.pem server-key.pem server.pem
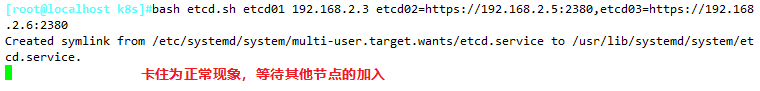
9、进入卡住状态等待其他节点加入
bash etcd.sh etcd01 192.168.2.3 etcd02=https://192.168.2.5:2380,etcd03=https://192.168.2.6:2380
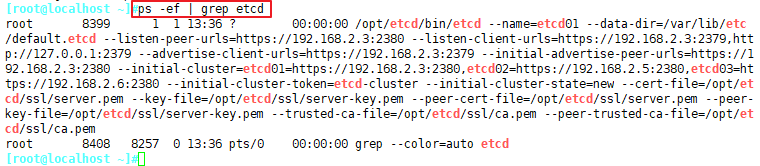
#新开master1的一个会话终端,会发现etcd进程已经开启
ps -ef | grep etcd
10、拷贝证书去其他节点
scp -r /opt/etcd/ root@192.168.2.5:/opt/
scp -r /opt/etcd/ root@192.168.2.6:/opt/
11、启动脚本拷贝其他节点
scp /usr/lib/systemd/system/etcd.service root@192.168.2.5:/usr/lib/systemd/system/
scp /usr/lib/systemd/system/etcd.service root@192.168.2.6:/usr/lib/systemd/system/
12、修改etcd配置文件
在node1节点与node2节点均需修改
Node1:192.168.2.5/24
###在node1节点修改
cd /opt/etcd/cfg/
vim etcd
#[Member]
ETCD_NAME="etcd02"
ETCD_DATA_DIR="/var/lib/etcd/default.etcd"
ETCD_LISTEN_PEER_URLS="https://192.168.2.5:2380"
ETCD_LISTEN_CLIENT_URLS="https://192.168.2.5:2379"
#[Clustering]
ETCD_INITIAL_ADVERTISE_PEER_URLS="https://192.168.2.5:2380"
ETCD_ADVERTISE_CLIENT_URLS="https://192.168.2.5:2379"
ETCD_INITIAL_CLUSTER="etcd01=https://192.168.2.3:2380,etcd02=https://192.168.2.5:2380,etcd03=https://192.168.2.6:2380"
ETCD_INITIAL_CLUSTER_TOKEN="etcd-cluster"
ETCD_INITIAL_CLUSTER_STATE="new"
Node2:192.168.2.6/24
###在node2节点修改
cd /opt/etcd/cfg/
vim etcd
#[Member]
ETCD_NAME="etcd03"
ETCD_DATA_DIR="/var/lib/etcd/default.etcd"
ETCD_LISTEN_PEER_URLS="https://192.168.2.6:2380"
ETCD_LISTEN_CLIENT_URLS="https://192.168.2.6:2379"
#[Clustering]
ETCD_INITIAL_ADVERTISE_PEER_URLS="https://192.168.2.6:2380"
ETCD_ADVERTISE_CLIENT_URLS="https://192.168.2.6:2379"
ETCD_INITIAL_CLUSTER="etcd01=https://192.168.2.3:2380,etcd02=https://192.168.2.5:2380,etcd03=https://192.168.2.6:2380"
ETCD_INITIAL_CLUSTER_TOKEN="etcd-cluster"
ETCD_INITIAL_CLUSTER_STATE="new"
13、启动
Master1:192.168.2.3/24
#首先在master1节点上进行启动
cd /root/k8s/
bash etcd.sh etcd01 192.168.2.3 etcd02=https://192.168.2.5:2380,etcd03=https://192.168.2.6:2380








 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章















 1934
1934











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








