linux的免密登录及xshell使用私钥登录
linux免密登录
生成加密秘钥
[root@server ~]# ssh-keygen -t rsa -C '123@163.com'
Generating public/private rsa key pair.
Enter file in which to save the key (/root/.ssh/id_rsa): (文件存放目录 默认就好)
/root/.ssh/id_rsa already exists.
Overwrite (y/n)? y
Enter passphrase (empty for no passphrase): (输入新密码,如果此处不输入密码可实现免密登录)
Enter same passphrase again: (再次输入确认)
Your identification has been saved in /root/.ssh/id_rsa.
Your public key has been saved in /root/.ssh/id_rsa.pub.
The key fingerprint is:
e1:69:3c:cd:e5:18:78:7f:83:eb:a7:4e:1f:66:bb:ed 123@163.com
The key's randomart image is:
+--[ RSA 2048]----+
| |
| . |
| o o . |
| o * * . |
| S + + o |
| . . o . |
| o + |
| o +.+ |
| .+o+oE|
+-----------------+
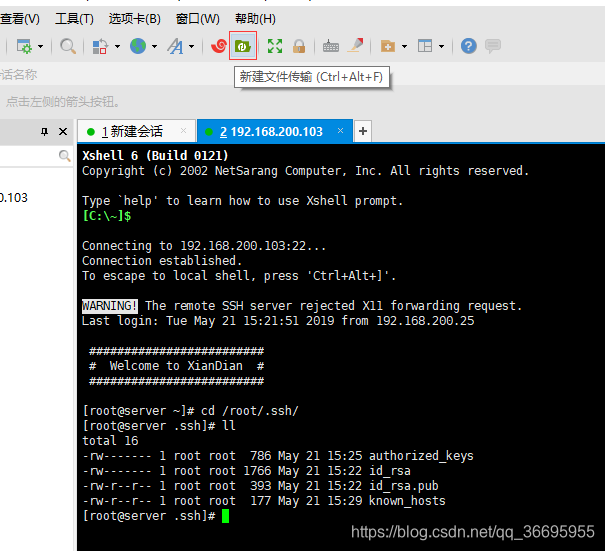
进入密钥文件
[root@server ~]# cd /root/.ssh/
查看authorized_keys文件权限
[root@server .ssh]# ll
total 12
-rw------- 1 root root 393 May 21 15:21 authorized_keys
-rw------- 1 root root 1766 May 21 15:22 id_rsa (私钥)
-rw-r--r-- 1 root root 393 May 21 15:22 id_rsa.pub (公钥)
(如不是600权限则需更改文件权限为600)
chmod 600 authorized_keys
(如属主和属组不是root需改文件的属主和属组)
chown -R root:root .ssh
将公钥文件加入列表
[root@server .ssh]# cat id_rsa.pub >> authorized_keys
把A中生成的公钥文件传送至远程主机B
[root@server ~]# ssh-copy-id 192.168.200.104
/usr/bin/ssh-copy-id: INFO: attempting to log in with the new key(s), to filter out any that are already installed
/usr/bin/ssh-copy-id: INFO: 1 key(s) remain to be installed -- if you are prompted now it is to install the new keys
root@192.168.200.104's password: (输入远程主机B的密码)
Number of key(s) added: 1
Now try logging into the machine, with: "ssh '192.168.200.104'"
and check to make sure that only the key(s) you wanted were added.
验证是否可以通过ssh私钥登录
[root@server .ssh]# ssh 192.168.200.104
Enter passphrase for key '/root/.ssh/id_rsa': (因为之前生成秘钥的时候为私钥设置了密码,所以我们这里需要输入密码)
Last login: Tue May 21 15:26:07 2019 from 192.168.200.25
#########################
# Welcome to Linux ! #
#########################
[root@client ~]#
使用xshell的私钥登录
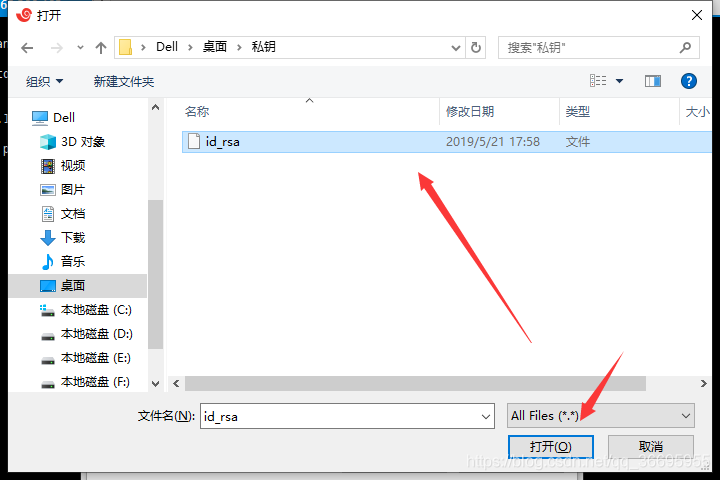
首先将私钥文件传到本地
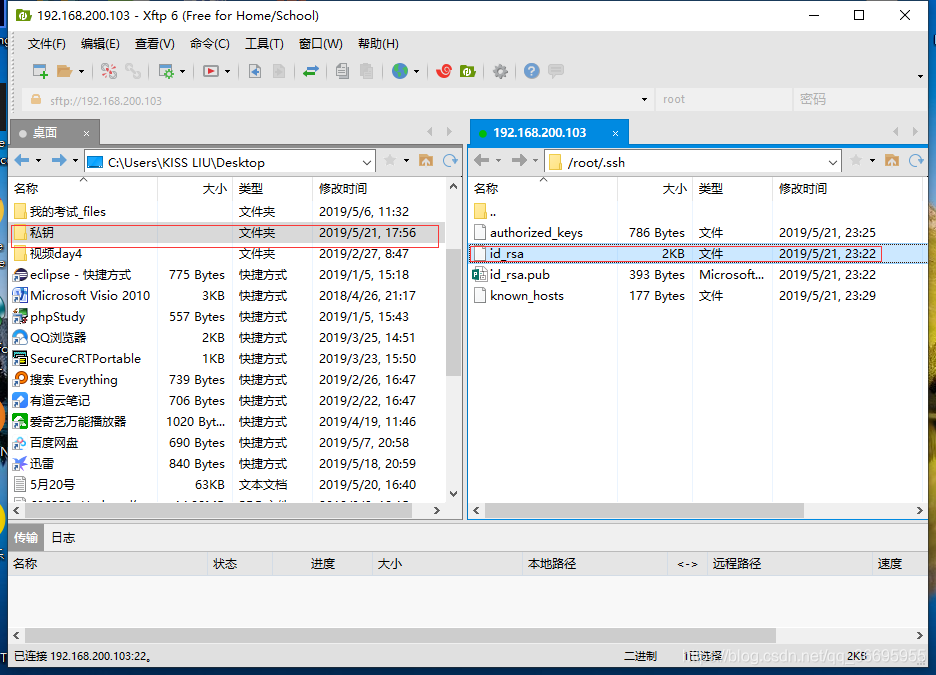
然后重新登录
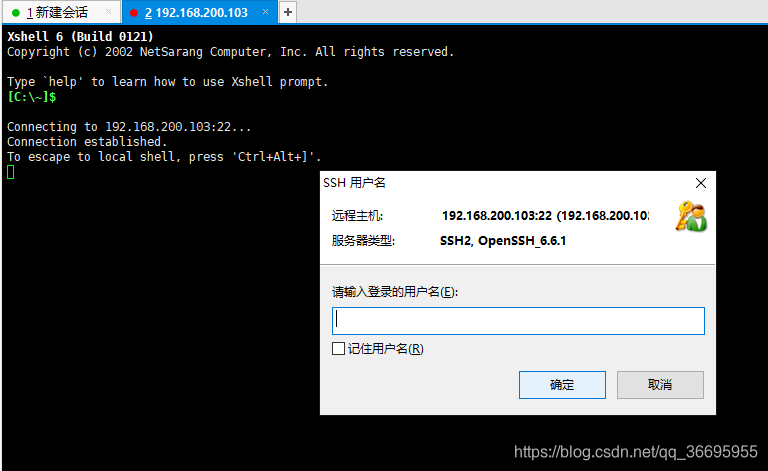
使用私钥登录
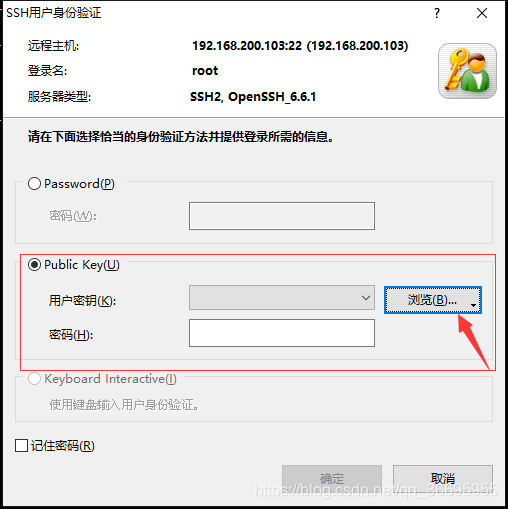
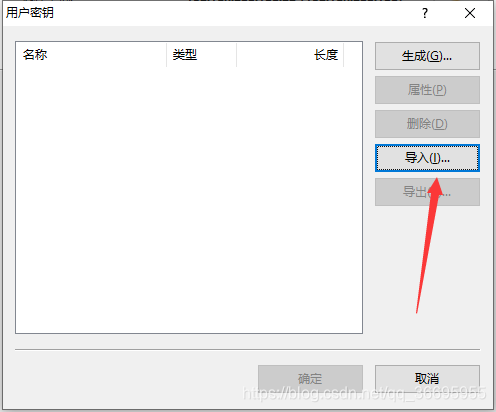
导入私钥
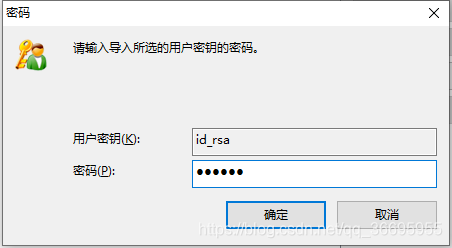
输入私钥的密码

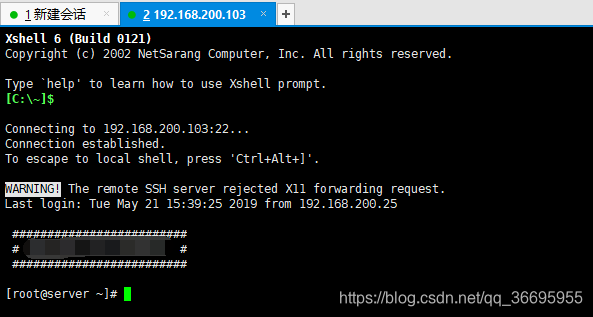
登录成功
大佬关于ssh-key的参数解读
ssh-key 参数解读
首次编写博客,如有不妥的地方欢迎指正~~





















 376
376











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








