日常运维账号应该是权限最小化的账号,且有时开发需要登陆生产机,避免开发误操作引起故障,也只应给到开发只读权限的账号。
本文创建一个只具有只读权限的ClusterRole,并重新生成~/.kube/config,将此配置拷贝到日常运维账号or开发账号下,使其只具备只读的操作权限。
安装cfssl和cfssljson工具用于生成证书
wget https://pkg.cfssl.org/R1.2/cfssl_linux-amd64
chmod +x cfssl_linux-amd64
mv cfssl_linux-amd64 /usr/local/bin/cfssl
wget https://pkg.cfssl.org/R1.2/cfssljson_linux-amd64
chmod +x cfssljson_linux-amd64
mv cfssljson_linux-amd64 /usr/local/bin/cfssljson新增用于生成Client证书的Json文件
[root@VM-12-8-centos readonly]# cat readonly.json
{
"CN": "readonly",
"hosts": [],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"ST": "HangZhou",
"L": "HangZhou",
"O": "dev:readonly",
"OU": "dev"
}
]
}
[root@VM-12-8-centos readonly]# cat ca-config-readonly.json
{
"signing": {
"default": {
"expiry": "8760h"
},
"profiles": {
"kubernetes": {
"usages": [
"signing",
"key encipherment",
"server auth",
"client auth"
],
"expiry": "8760h"
}
}
}
}创建readonly用户Client证书和Client私钥
先将集群的ca证书拷贝到当前目录下
[root@VM-12-8-centos pki]# cp /etc/kubernetes/pki/ca.crt /data/readonly/
[root@VM-12-8-centos pki]# cp /etc/kubernetes/pki/ca.key /data/readonly/
随后运行命令生成
cfssl gencert --ca ca.crt --ca-key ca.key --config ca-config-readonly.json --profile=kubernetes readonly.json | cfssljson --bare readonly
k8s相关配置
拷贝config文件到当前目录
cp /root/.kube/config ./readonly.kubeconfig
运行以下命令,添加readonly至K8s集群User用户中,新增只读上下文,及将只读上下文配置到readonly.kubeconfig文件中
[root@VM-12-8-centos readonly]# kubectl config set-credentials readonly --certificate-authority=/data/readonly/ca.crt --embed-certs=true --client-key=/data/readonly/readonly-key.pem --client-certificate=/data/readonly/readonly.pem --kubeconfig=/data/readonly/readonly.kubeconfig
User "readonly" set.
[root@VM-12-8-centos readonly]# kubectl config set-context readonly-context --cluster=kubernetes --user=readonly --kubeconfig=readonly.kubeconfig
Context "readonly-context" created.
[root@VM-12-8-centos readonly]# kubectl config use-context readonly-context --kubeconfig=readonly.kubeconfig
Switched to context "readonly-context".创建clusterrole
[root@VM-12-8-centos readonly]# cat readonly_role.yml
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: ClusterRole
metadata:
name: readonly-clusterrole
rules:
- apiGroups:
- ""
resources:
- pods
- pods/attach
- pods/exec
- pods/portforward
- pods/proxy
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- configmaps
- endpoints
- persistentvolumeclaims
- replicationcontrollers
- replicationcontrollers/scale
- secrets
- serviceaccounts
- services
- services/proxy
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- bindings
- events
- limitranges
- namespaces/status
- pods/log
- pods/status
- replicationcontrollers/status
- resourcequotas
- resourcequotas/status
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- namespaces
verbs:
- get
- list
- watch
- apiGroups:
- apps
resources:
- deployments
- deployments/rollback
- deployments/scale
- statefulsets
verbs:
- get
- list
- watch
- apiGroups:
- autoscaling
resources:
- horizontalpodautoscalers
verbs:
- get
- list
- watch
- apiGroups:
- batch
resources:
- cronjobs
- jobs
- scheduledjobs
verbs:
- get
- list
- watch
- apiGroups:
- extensions
resources:
- daemonsets
- deployments
- ingresses
- replicasets
verbs:
- get
- list
- watch
---
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: ClusterRoleBinding
metadata:
name: cluster-readonly
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: readonly-clusterrole # 将名为readonly-clusterrole的Clusterrole与名为readonly的K8s User进行绑定
subjects:
- apiGroup: rbac.authorization.k8s.io
kind: User
name: readonly[root@VM-12-8-centos readonly]# kubectl apply -f readonly_role.yml
clusterrole.rbac.authorization.k8s.io/readonly-clusterrole created
clusterrolebinding.rbac.authorization.k8s.io/cluster-readonly created
验证
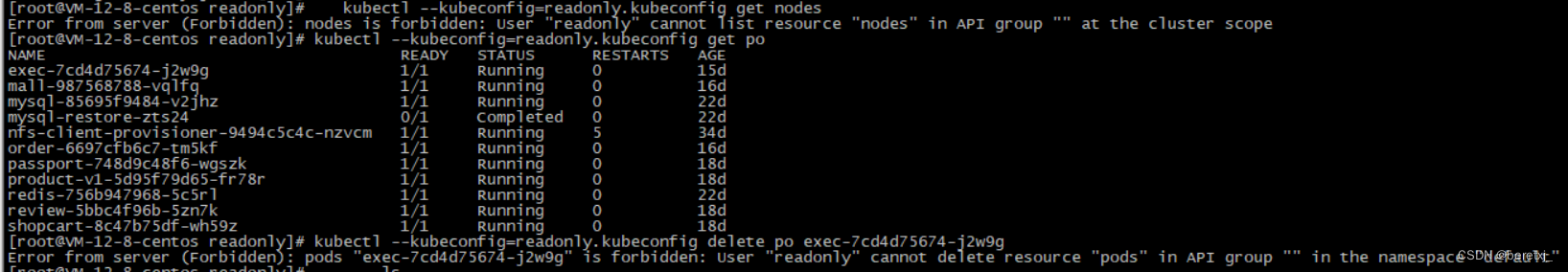
以上可以看到,root账户下,使用此配置权限已被限制
现在配置devis账户,使其只有只读的操作权限
将readonly.kubeconfig拷贝到devis的家目录下
/home/devis/.kube/readonly.kubeconfig
并在.bash_profile下新增配置
KUBECONFIG=/home/devis/.kube/readonly.kubeconfig
export KUBECONFIG
重新登录后,我们的配置是成功的,达到了只有只读操作权限的目的






















 1119
1119











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








