1.对网站进行抓包分析
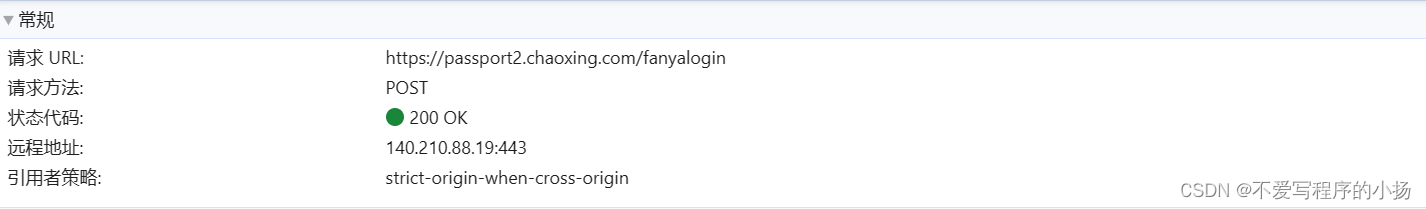
抓包发现每次请求登录都是post这个地址

查看请求提交了这些数据很明显uname和password就是账号和密码其他参数再进行全局搜索

发现先对https://passport2.chaoxing.com/login这个地址进行了get请求获得了一个html
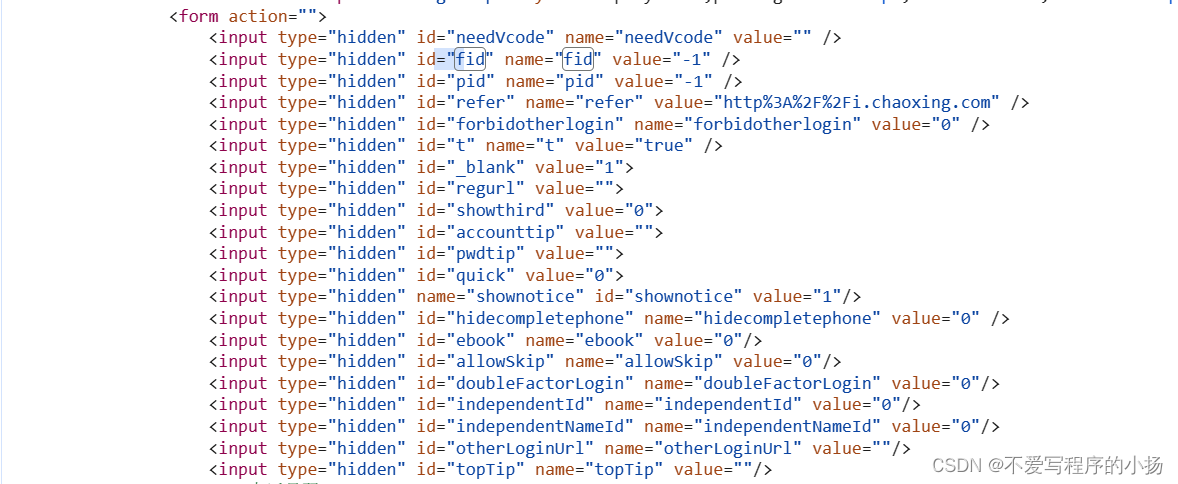
这样就找到了除uname和password的其他值

对password进行全局搜索发现有一个encryptByAES函数并且传了一个原始密码还有一个transferKey,再后面的分析中发现这个transferKey是写死的
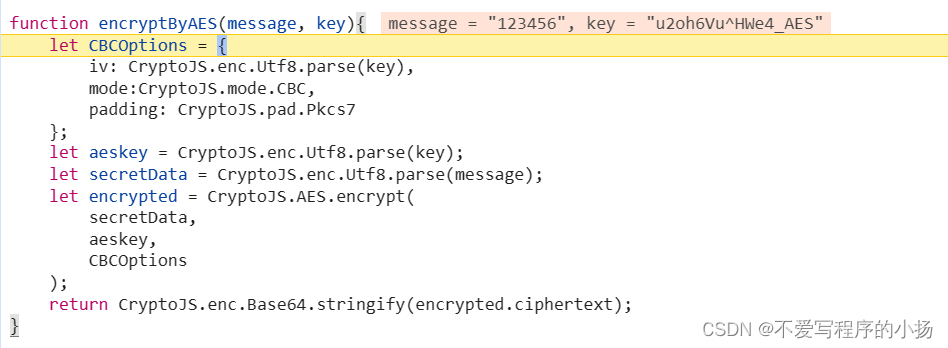
debug进去果然是这个函数,这下请求的参数全部都获取到了,用requsets模拟请求获得cookie进行登录就成功了
2.python代码实现
function encryptByAES(message) {
const CryptoJS = require('crypto-js');
let CBCOptions = {
iv: CryptoJS.enc.Utf8.parse('u2oh6Vu^HWe4_AES'),
mode: CryptoJS.mode.CBC,
padding: CryptoJS.pad.Pkcs7
};
let aeskey = CryptoJS.enc.Utf8.parse('u2oh6Vu^HWe4_AES');
let secretData = CryptoJS.enc.Utf8.parse(message);
let encrypted = CryptoJS.AES.encrypt(
secretData,
aeskey,
CBCOptions
);
return CryptoJS.enc.Base64.stringify(encrypted.ciphertext);
}
这是从网站上抠出来的加密代码,我将transferKey直接写死了,创建一个js文件并且保存
import execjs
def execute_js_file(origin): # 调用js解密
with open('encryptAES.js', 'r') as file:
js_code = file.read()
# 使用 execjs 运行 JavaScript 代码
ctx = execjs.compile(js_code)
# 执行 JavaScript 中的函数或代码
result = ctx.call('encryptByAES', origin) # 例如调用 example.js 中的 add 函数
return result
用python代码执行js程序
def loginding():
login_data = {}
headers = {'Content-Type': 'application/x-www-form-urlencoded; charset=UTF-8',
'User-Agent': 'Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/120.0.0.0 Safari/537.36 Edg/120.0.0.0'}
re = requests.get('https://passport2.chaoxing.com/login')
soup = BeautifulSoup(re.text, 'html.parser')
top = soup.find('form')
body = top.find_all('input')
for item in body:
data = item.get('id')
if data in ['fid', 'refer', 't', 'forbidotherlogin', 'validate', 'doubleFactorLogin', 'independentId',
'independentNameId']:
login_data[data] = item.get('value')
uname = execute_js_file(input('uname:'))
password = execute_js_file(input('password:'))
login_data['uname'] = uname
login_data['password'] = password
re = requests.post('https://passport2.chaoxing.com/fanyalogin', data=login_data,
headers=headers)
if not re.json()['status']:
print('PasswordError')
return False
with open('cookie.pkl', 'wb') as f:
pickle.dump(re.cookies, f)
return True这就是登录代码
3.总代码
import requests
from bs4 import BeautifulSoup
import execjs
import pickle
def execute_js_file(origin): # 调用js解密
with open('encryptAES.js', 'r') as file:
js_code = file.read()
# 使用 execjs 运行 JavaScript 代码
ctx = execjs.compile(js_code)
# 执行 JavaScript 中的函数或代码
result = ctx.call('encryptByAES', origin) # 例如调用 example.js 中的 add 函数
return result
def loginding():
login_data = {}
headers = {'Content-Type': 'application/x-www-form-urlencoded; charset=UTF-8',
'User-Agent': 'Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/120.0.0.0 Safari/537.36 Edg/120.0.0.0'}
re = requests.get('https://passport2.chaoxing.com/login')
soup = BeautifulSoup(re.text, 'html.parser')
top = soup.find('form')
body = top.find_all('input')
for item in body:
data = item.get('id')
if data in ['fid', 'refer', 't', 'forbidotherlogin', 'validate', 'doubleFactorLogin', 'independentId',
'independentNameId']:
login_data[data] = item.get('value')
uname = execute_js_file(input('uname:'))
password = execute_js_file(input('password:'))
login_data['uname'] = uname
login_data['password'] = password
re = requests.post('https://passport2.chaoxing.com/fanyalogin', data=login_data,
headers=headers)
if not re.json()['status']:
print('PasswordError')
return False
with open('cookie.pkl', 'wb') as f:
pickle.dump(re.cookies, f)
return True
if __name__ == '__main__':
while True:
if loginding():
print('Success')
break




















 2万+
2万+











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








