- 拉取镜像
docker pull yandex/clickhouse-server
- 创建挂载目录
mkdir -p $HOME/data/docker/clickhouse/{data,logs}
- 临时启动clickhouse
docker run -d --name some-clickhouse-server --ulimit nofile=262144:262144 yandex/clickhouse-server
- 复制文件到挂载目录
docker ps
docker cp 419c15cc3889:/etc/clickhouse-server $HOME/data/docker/clickhouse/
mv $HOME/data/docker/clickhouse/clickhouse-server $HOME/data/docker/clickhouse/config

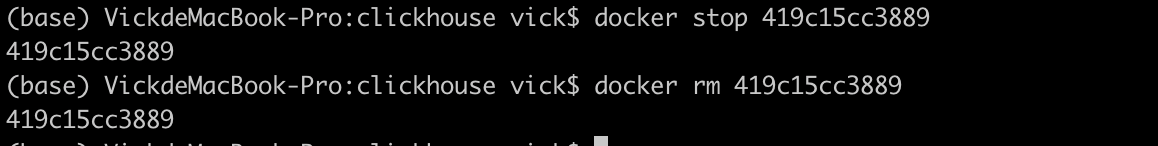
- 停止并删除临时启动的服务
docker stop 419c15cc3889
docker rm 419c15cc3889
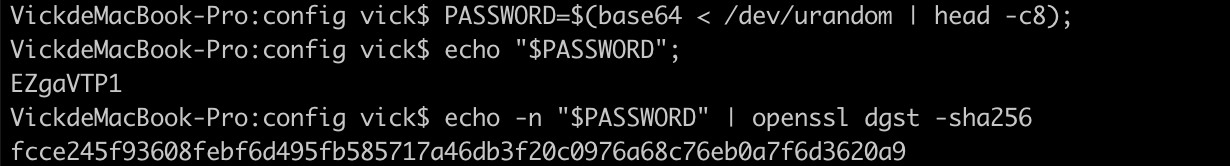
- 准备一个sha256加密的密码
# 例如密码 123456
echo -n 123456 | openssl dgst -sha256
# 输出结果
# 8d969eef6ecad3c29a3a629280e686cf0c3f5d5a86aff3ca12020c923adc6c92
# 或者使用随机密码(二选一)
PASSWORD=$(base64 < /dev/urandom | head -c8);
echo "$PASSWORD";
# 输出
# EZgaVTP1
echo -n "$PASSWORD" | openssl dgst -sha256
#输出结果
# fcce245f93608febf6d495fb585717a46db3f20c0976a68c76eb0a7f6d3620a9
- 修改上面启动后挂载目录中的user.xml文件(路径在config下,主要是配置账号密码)

- 修改config.xml(主要是设置时区、监听设置,解决ipv6可能不能用问题)
<!-- 时区设置 -->
<timezone>Asia/Shanghai</timezone>
<!-- ip支持设置 -->
<listen_host>0.0.0.0</listen_host>
-
修改完成并保存
-
重新启动容器(防止时区异常映射localtime)
docker run -d --name ch-server \
--ulimit nofile=262144:262144 -p 8123:8123 -p 9000:9000 -p 9009:9009 \
-v $HOME/data/docker/clickhouse/data:/var/lib/clickhouse \
-v $HOME/data/docker/clickhouse/config:/etc/clickhouse-server \
-v $HOME/data/docker/clickhouse/logs:/var/log/clickhouse-server \
-v /etc/localtime:/etc/localtime \
yandex/clickhouse-server

如果使用clickhouse-client启动参数如下
clickhouse-client启动常用参数
--host, -h :服务端host名称,默认 localhost
--port :连接端口,默认9000
--user, -u :用户名,默认 default
--password :密码,默认空
--query, -q :非交互模式下的查询语句
--database, -d :默认当前操作的数据库,默认default
--multiline, -m :允许多行语句查询,在clickhouse中默认回车即为sql结束,可使用该参数多行输入
--format, -f :使用指定的默认格式输出结果 csv,以逗号分隔
--time, -t :非交互模式下会打印查询执行的时间
--stacktrace :出现异常会打印堆栈跟踪信息
--config-file :配置文件名称
- 测试连接

- docker安装clickhouse官方文档
- 原始user.xml文件内容
<?xml version="1.0"?>
<yandex>
<!-- Profiles of settings. -->
<profiles>
<!-- Default settings. -->
<default>
<!-- Maximum memory usage for processing single query, in bytes. -->
<max_memory_usage>10000000000</max_memory_usage>
<!-- How to choose between replicas during distributed query processing.
random - choose random replica from set of replicas with minimum number of errors
nearest_hostname - from set of replicas with minimum number of errors, choose replica
with minimum number of different symbols between replica's hostname and local hostname
(Hamming distance).
in_order - first live replica is chosen in specified order.
first_or_random - if first replica one has higher number of errors, pick a random one from replicas with minimum number of errors.
-->
<load_balancing>random</load_balancing>
</default>
<!-- Profile that allows only read queries. -->
<readonly>
<readonly>1</readonly>
</readonly>
</profiles>
<!-- Users and ACL. -->
<users>
<!-- If user name was not specified, 'default' user is used. -->
<default>
<!-- Password could be specified in plaintext or in SHA256 (in hex format).
If you want to specify password in plaintext (not recommended), place it in 'password' element.
Example: <password>qwerty</password>.
Password could be empty.
If you want to specify SHA256, place it in 'password_sha256_hex' element.
Example: <password_sha256_hex>65e84be33532fb784c48129675f9eff3a682b27168c0ea744b2cf58ee02337c5</password_sha256_hex>
Restrictions of SHA256: impossibility to connect to ClickHouse using MySQL JS client (as of July 2019).
If you want to specify double SHA1, place it in 'password_double_sha1_hex' element.
Example: <password_double_sha1_hex>e395796d6546b1b65db9d665cd43f0e858dd4303</password_double_sha1_hex>
If you want to specify a previously defined LDAP server (see 'ldap_servers' in the main config) for authentication,
place its name in 'server' element inside 'ldap' element.
Example: <ldap><server>my_ldap_server</server></ldap>
If you want to authenticate the user via Kerberos (assuming Kerberos is enabled, see 'kerberos' in the main config),
place 'kerberos' element instead of 'password' (and similar) elements.
The name part of the canonical principal name of the initiator must match the user name for authentication to succeed.
You can also place 'realm' element inside 'kerberos' element to further restrict authentication to only those requests
whose initiator's realm matches it.
Example: <kerberos />
Example: <kerberos><realm>EXAMPLE.COM</realm></kerberos>
How to generate decent password:
Execute: PASSWORD=$(base64 < /dev/urandom | head -c8); echo "$PASSWORD"; echo -n "$PASSWORD" | sha256sum | tr -d '-'
In first line will be password and in second - corresponding SHA256.
How to generate double SHA1:
Execute: PASSWORD=$(base64 < /dev/urandom | head -c8); echo "$PASSWORD"; echo -n "$PASSWORD" | sha1sum | tr -d '-' | xxd -r -p | sha1sum | tr -d '-'
In first line will be password and in second - corresponding double SHA1.
-->
<password></password>
<!-- List of networks with open access.
To open access from everywhere, specify:
<ip>::/0</ip>
To open access only from localhost, specify:
<ip>::1</ip>
<ip>127.0.0.1</ip>
Each element of list has one of the following forms:
<ip> IP-address or network mask. Examples: 213.180.204.3 or 10.0.0.1/8 or 10.0.0.1/255.255.255.0
2a02:6b8::3 or 2a02:6b8::3/64 or 2a02:6b8::3/ffff:ffff:ffff:ffff::.
<host> Hostname. Example: server01.yandex.ru.
To check access, DNS query is performed, and all received addresses compared to peer address.
<host_regexp> Regular expression for host names. Example, ^server\d\d-\d\d-\d\.yandex\.ru$
To check access, DNS PTR query is performed for peer address and then regexp is applied.
Then, for result of PTR query, another DNS query is performed and all received addresses compared to peer address.
Strongly recommended that regexp is ends with $
All results of DNS requests are cached till server restart.
-->
<networks>
<ip>::/0</ip>
</networks>
<!-- Settings profile for user. -->
<profile>default</profile>
<!-- Quota for user. -->
<quota>default</quota>
<!-- User can create other users and grant rights to them. -->
<!-- <access_management>1</access_management> -->
</default>
</users>
<!-- Quotas. -->
<quotas>
<!-- Name of quota. -->
<default>
<!-- Limits for time interval. You could specify many intervals with different limits. -->
<interval>
<!-- Length of interval. -->
<duration>3600</duration>
<!-- No limits. Just calculate resource usage for time interval. -->
<queries>0</queries>
<errors>0</errors>
<result_rows>0</result_rows>
<read_rows>0</read_rows>
<execution_time>0</execution_time>
</interval>
</default>
</quotas>
</yandex>

























 2592
2592











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








