calico、网络策略、server-lngress、lngress TLS
一、calico网络插件
- 官网:https://kubernetes.io/zh/docs/concepts/services-networking/network-policies/
- calico简介:
flannel实现的是网络通信,calico的特性是在pod之间的隔离(网络策略)。
通过BGP路由,但大规模端点的拓扑计算和收敛往往需要一定的时间和计算资源。
纯三层的转发,中间没有任何的NAT和overlay,转发效率最好。
Calico 仅依赖三层路由可达。Calico 较少的依赖性使它能适配所有 VM、Container、白盒或者混合环境场景。
- 安装calico:
# wget https://docs.projectcalico.org/manifests/calico.yaml ##通过官网可以查看(最新版本下载比较慢,所以我使用的是)
# vim calico.yml
- name: CALICO_IPV4POOL_IPIP ##IPIP表示隧道
value: "off"
# kubectl apply -f calico.yaml ##创建
- IPIP工作模式:适用于互相访问的pod不在同一个网段中,跨网段访问的场景。

- BGP工作模式:适用于互相访问的pod在同一个网段,适用于大型网络
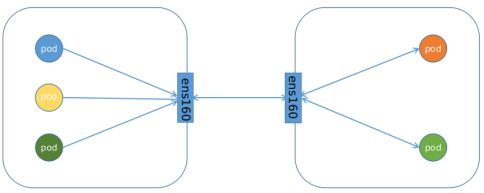
- NetworkPolicy策略模型:控制某个namespace下的pod的网络出入站规则。

1.上传镜像
[root@server1 ~]# lftp 172.25.15.250
lftp 172.25.15.250:~> cd pub/docs/k8s/
lftp 172.25.15.250:/pub/docs/k8s> get calico-v3.19.1.tar
399186944 bytes transferred in 2 seconds (154.88M/s)
lftp 172.25.15.250:/pub/docs/k8s> exit
[root@server1 ~]# ls
[root@server1 ~]# docker load -i calico-v3.19.1.tar
[root@server1 ~]# docker images | grep calico | awk '{system("docker push "$1":"$2"")}' #上传至网络仓库



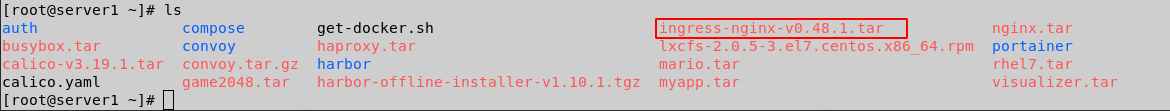
2.网络策略,禁止访问
[root@server4 ~]# mkdir calico
[root@server4 ~]# cd calico/
[root@server4 calico]# ls
[root@server4 calico]# vim calico.yaml
[root@server4 calico]# vim calico.yaml
[root@server4 calico]# kubectl get pod -n kube-system
[root@server4 calico]# mv /etc/cni/net.d/10-flannel.conflist /mnt #移动或者删除server2和server3相同操作
[root@server4 calico]# ssh server2 mv /etc/cni/net.d/10-flannel.conflist /mnt
[root@server4 calico]# ssh server3 mv /etc/cni/net.d/10-flannel.conflist /mnt
[root@server4 calico]# kubectl apply -f calico.yaml #启动
[root@server4 calico]# kubectl get pod -n kube-system
[root@server4 calico]# route -n
[root@server4 calico]# kubectl get svc
[root@server4 calico]# kubectl get pod
[root@server4 calico]# cd
[root@server4 ~]# cd metallb/
[root@server4 metallb]# ls
configmap.yaml ex-svc.yaml ext-ip.yaml lb-svc.yaml metallb.yaml
[root@server4 metallb]# vim lb-svc.yaml
[root@server4 metallb]# kubectl apply -f lb-svc.yaml
service/lb-svc created
[root@server4 metallb]# kubectl get svc




3.允许指定pod访问服务
[root@server4 calico]# ls
calico.yaml deny-nginx.yaml
[root@server4 calico]# vim access-demo.yaml
kind: NetworkPolicy
apiVersion: networking.k8s.io/v1
metadata:
name: access-nginx
spec:
podSelector:
matchLabels:
app: nginx
ingress:
- from:
- podSelector:
matchLabels:
app: demo
[root@server4 calico]# kubectl apply -f access-demo.yaml
networkpolicy.networking.k8s.io/access-nginx created
[root@server4 calico]# kubectl get networkpolicies.
[root@server4 calico]# kubectl label pod demo app=demo ##设置标签
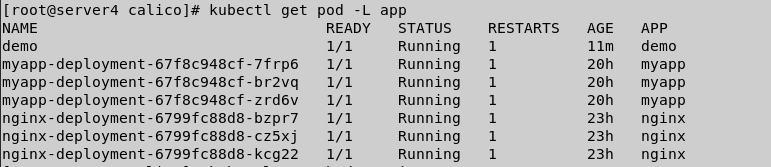
[root@server4 calico]# kubectl get pod -L app
[root@server4 calico]# kubectl get pod -o wide
[root@server4 calico]# kubectl attach demo -it


4.禁止 namespace 中所有 Pod 之间的相互访问
[root@server4 calico]# kubectl create namespace demo 创建新的namespace实验
namespace/demo created
[root@server4 calico]# kubectl get ns
[root@server4 calico]# kubectl run demo1 --image=busyboxplus -it -n demo #创建demo1
If you don't see a command prompt, try pressing enter.
/ # Session ended, resume using 'kubectl attach demo1 -c demo1 -i -t' command when the pod is running
[root@server4 calico]# kubectl run demo2 --image=busyboxplus -it -n demo #创建demo2
If you don't see a command prompt, try pressing enter.
/ # Session ended, resume using 'kubectl attach demo2 -c demo2 -i -t' command when the pod is running
[root@server4 calico]# kubectl -n demo get pod
[root@server4 calico]# kubectl -n demo get pod --show-labels
[root@server4 calico]# kubectl -n demo get pod -L run
[root@server4 calico]# kubectl get pod
[root@server4 calico]# vim deny-pod.yaml
[root@server4 calico]# cat deny-pod.yaml
apiVersion: networking.k8s.io/v1
kind: NetworkPolicy
metadata:
name: default-deny
namespace: demo
spec:
podSelector: {}
[root@server4 calico]# kubectl apply -f deny-pod.yaml
networkpolicy.networking.k8s.io/default-deny created
##测试
[root@server4 calico]# kubectl get networkpolicies. -n demo
[root@server4 calico]# kubectl attach demo1 -it -n demo #测试demo1和demo2之间是否可以相互访问


5.禁止其他 namespace 访问服务
[root@server4 calico]# kubectl get pod -o wide
[root@server4 calico]# kubectl get pod --show-labels
[root@server4 calico]# vim deny-ns.yaml
[root@server4 calico]# cat deny-ns.yaml
kind: NetworkPolicy
apiVersion: networking.k8s.io/v1
metadata:
name: deny-namespace
spec:
podSelector:
matchLabels:
ingress:
- from:
- podSelector: {}
[root@server4 calico]# kubectl apply -f deny-ns.yaml #运行
[root@server4 calico]# kubectl attach demo1 -it -n demo 是否可以访问
If you don't see a command prompt, try pressing enter.
/ # curl 10.244.179.80
^C

6.只允许指定namespace访问服务
[root@server4 calico]# kubectl create namespace test
namespace/test created
[root@server4 calico]# kubectl run demo3 --image=busyboxplus -it -n test
If you don't see a command prompt, try pressing enter.
/ # curl 10.244.179.80 #无法访问
^C
/ # Session ended, resume using 'kubectl attach demo3 -c demo3 -i -t' command when the pod is running
[root@server4 calico]# vim access-ns.yaml
[root@server4 calico]# cat access-ns.yaml
kind: NetworkPolicy
apiVersion: networking.k8s.io/v1
metadata:
name: access-namespace
spec:
podSelector:
matchLabels:
run: nginx #指定标签
ingress:
- from:
- namespaceSelector:
matchLabels:
role: prod #指定ns的角色名字
[root@server4 calico]# kubectl label ns test role=prod #设置namespace标签
namespace/test labeled
[root@server4 calico]# kubectl get ns --show-labels
[root@server4 calico]# kubectl apply -f access-ns.yaml #访问指定标签的pod
networkpolicy.networking.k8s.io/access-namespace created
[root@server2 calico]# kubectl apply -f access-ns.yaml ##访问指定标签的pod
[root@server2 calico]# kubectl attach demo3 -it -n test
[ root@demo3:/ ]$ curl 10.244.179.80
Hello MyApp | Version: v2 | <a href="hostname.html">Pod Name</a> ##标签为run=nginx的pod节点,且访问成功
[root@server2 calico]# kubectl attach demo2 -it -n demo
[ root@demo2:/ ]$ curl 10.244.179.80 ##标签不为run=nginx的pod节点,访问不成功
^C

7. 允许外网访问服务
[root@server4 ingress]# vim demo.yaml
[root@server4 ingress]# cat demo.yaml
apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
name: ingress-demo
spec:
# tls:
# - hosts:
# - www1.westos.org
# secretName: tls-secret
rules:
- host: www1.westos.org
http:
paths:
- path: /
backend:
serviceName: nginx-svc
servicePort: 80
[root@server4 ingress]# kubectl apply -f demo.yaml
Warning: networking.k8s.io/v1beta1 Ingress is deprecated in v1.19+, unavailable in v1.22+; use networking.k8s.io/v1 Ingress
ingress.networking.k8s.io/ingress-demo created
[root@server4 ingress]# kubectl get ingress
##外网测试
[root@foundation15 ~]# ping www1.westos.org
[root@foundation15 ~]# curl www1.westos.org


二、 service—lngress-nginx
-
一种全局的、为了代理不同后端 Service 而设置的负载均衡服务,就是 Kubernetes 里的Ingress 服务。
Ingress由两部分组成:Ingress controller和Ingress服务。Ingress Controller 会根据你定义的 Ingress 对象,提供对应的代理能力。业界常用的各种反向代理项目,比如 Nginx、HAProxy、Envoy、Traefik 等,都已经为Kubernetes 专门维护了对应的 Ingress Controller。
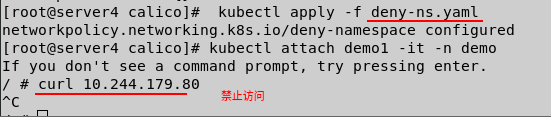
1.上传镜像
[root@server1 ~]# ls
[root@server1 ~]# docker load -i ingress-nginx-v0.48.1.tar #加载镜像
[root@server1 ~]# docker push reg.westos.org/ingress-nginx/kube-webhook-certgen:v1.5.1
[root@server1 ~]# docker push reg.westos.org/ingress-nginx/controller:v0.48.1
创建仓库


导入镜像

上传

上传成功,查看

2.部署Ingress服务
[root@server4 ~]# mkdir ingress #创建对应文件夹方便实验
[root@server4 ~]# cd ingress/
[root@server4 ingress]# ls
[root@server4 ingress]# pwd
/root/ingress
[root@server4 ingress]# ls
deploy.yaml
[root@server4 ingress]# vim deploy.yaml
[root@server4 ingress]# kubectl apply -f deploy.yaml
[root@server4 ingress]# kubectl -n ingress-nginx get pod
[root@server4 ingress]# kubectl -n ingress-nginx get svc
ingress-nginx-controller NodePort 10.99.121.194 <none> 80:30148/TCP,443:32730/TCP 3m49s
ingress-nginx-controller-admission ClusterIP 10.108.189.151 <none> 443/TCP 3m49s
[root@server4 ingress]# kubectl -n ingress-nginx describe pod ingress-nginx-controller-5f476b6d87-svpj5
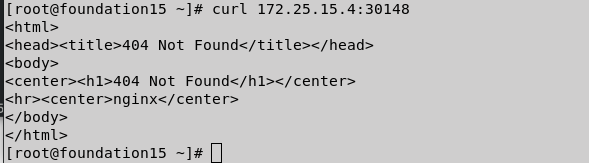
## 真实主机访问
[root@foundation15 ~]# curl 172.25.15.4:30148




3.配置基本的测试文件
[root@server4 ingress]# vim ingress.yaml
[root@server4 ingress]# cat ingress.yaml
apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
name: ingress-nginx
spec:
rules:
- host: www1.westos.org
http:
paths:
- path: /
backend:
serviceName: nginx-svc
servicePort: 80
---
apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
name: ingress-myapp
spec:
rules:
- host: www2.westos.org
http:
paths:
- path: /
backend:
serviceName: myapp-svc
servicePort: 80
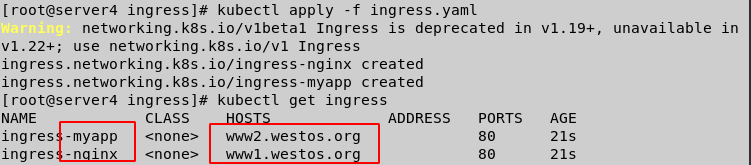
[root@server4 ingress]# kubectl apply -f ingress.yaml
[root@server4 ingress]# kubectl get ingress
[root@server4 ingress]# kubectl -n ingress-nginx get svc
[root@server4 ingress]# kubectl -n ingress-nginx edit svc ingress-nginx-controller
type: LoadBalancer #修改为
[root@server4 ingress]# kubectl -n ingress-nginx get svc


172.25.15.10 ip 会添加到server2和server3

4.配置lngress-nginx七层均衡
根据域名定义到不同后端,两个不同镜像nginx和myapp
[root@server4 pod]# vim svc.yaml
[root@server4 pod]# cat svc.yaml
apiVersion: v1
kind: Service
metadata:
name: myapp-svc
spec:
ports:
- protocol: TCP
port: 80
targetPort: 80
selector:
app: myapp
---
apiVersion: v1
kind: Service
metadata:
name: nginx-svc
spec:
ports:
- protocol: TCP
port: 80
targetPort: 80
selector:
app: nginx
[root@server4 pod]# kubectl apply -f svc.yaml
service/myapp-svc created
service/nginx-svc created
[root@server4 pod]# kubectl get svc
## 查看节点endpoint服务是否健康
[root@server4 pod]# kubectl describe svc myapp-svc
[root@server4 pod]# kubectl describe svc nginx-svc


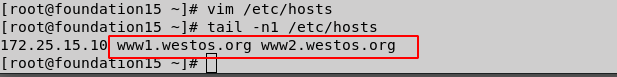
5.真机配置解析
[root@foundation15 ~]# vim /etc/hosts
[root@foundation15 ~]# tail -n1 /etc/hosts
172.25.15.10 www1.westos.org www2.westos.org
[root@foundation15 ~]#
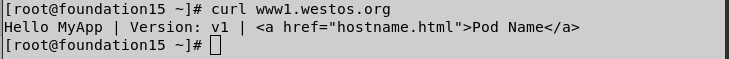
真机访问,不同域名不同后端
###deployment.yaml 镜像为 niginx和 myapp:v2
[root@foundation15 ~]# curl www1.westos.org
[root@foundation15 ~]# curl www2.westos.org
Hello MyApp | Version: v2 | <a href="hostname.html">Pod Name</a>
[root@foundation15 ~]# curl www2.westos.org
Hello MyApp | Version: v2 | <a href="hostname.html">Pod Name</a>
## 负载均衡
[root@foundation15 ~]# curl www2.westos.org/hostname.html
myapp-deployment-67f8c948cf-zrd6v
[root@foundation15 ~]# curl www2.westos.org/hostname.html
myapp-deployment-67f8c948cf-7frp6
[root@foundation15 ~]# curl www2.westos.org/hostname.html
myapp-deployment-67f8c948cf-br2vq
[root@foundation15 ~]# curl www2.westos.org/hostname.html
myapp-deployment-67f8c948cf-zrd6v
[root@foundation15 ~]# curl www2.westos.org/hostname.html
myapp-deployment-67f8c948cf-7frp6
[root@foundation15 ~]# curl www2.westos.org/hostname.html
myapp-deployment-67f8c948cf-br2vq


6.vim deployment.yaml

镜像都改为 myapp (v1和v2)

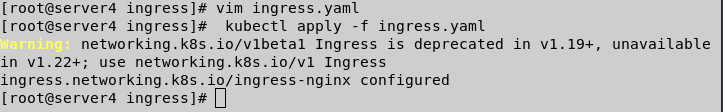
三、lngress TLS
[root@server4 ~]# cd ingress/
[root@server4 ingress]# ls
deploy.yaml ingress.yaml
[root@server4 ingress]# vim ingress.yaml
[root@server4 ingress]# kubectl apply -f ingress.yaml
Warning: networking.k8s.io/v1beta1 Ingress is deprecated in v1.19+, unavailable in v1.22+; use networking.k8s.io/v1 Ingress
ingress.networking.k8s.io/ingress-nginx configured
ingress.networking.k8s.io/ingress-myapp configured
[root@server4 ingress]# kubectl get ingress
NAME CLASS HOSTS ADDRESS PORTS AGE
ingress-myapp <none> www2.westos.org 172.25.15.2 80 19h
ingress-nginx <none> www1.westos.org 172.25.15.2 80 19h
[root@server4 ingress]#
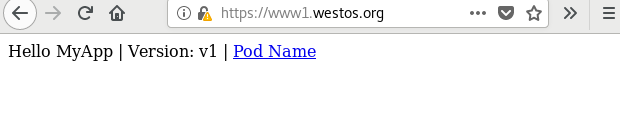
[root@foundation15 ~]# curl www1.westos.org
Hello MyApp | Version: v1 | <a href="hostname.html">Pod Name</a>
[root@foundation15 ~]#

1.lngress加密 +认证
## 查看认证
[root@server4 ingress]# openssl req -x509 -sha256 -nodes -days 365 -newkey rsa:2048 -keyout tls.key -out tls.crt -subj "/CN=nginxsvc/O=nginxsvc"
Generating a 2048 bit RSA private key
...............................+++
..................................+++
writing new private key to 'tls.key'
-----
[root@server4 ingress]# ls
deploy.yaml ingress.yaml tls.crt tls.key
[root@server4 ingress]#
[root@server4 ingress]# kubectl create secret tls tls-secret --key tls.key --cert tls.crt
secret/tls-secret created
[root@server4 ingress]# kubectl get secrets
[root@server4 ingress]# kubectl get ingress
[root@server4 ingress]# kubectl delete ingress ingress-myapp
[root@server4 ingress]# ls
deploy.yaml ingress.yaml tls.crt tls.key
[root@server4 ingress]# vim ingress.yaml
[root@server4 ingress]# kubectl get secrets
[root@server4 ingress]# kubectl apply -f ingress.yaml
[root@server4 ingress]# kubectl describe ingress




访问

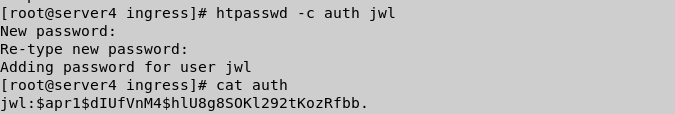
[root@server4 ingress]# yum install -y httpd-tools
[root@server4 ingress]# htpasswd -c auth jwl #创建用户
New password:
Re-type new password:
Adding password for user jwl
[root@server4 ingress]# cat auth
jwl:$apr1$dIUfVnM4$hlU8g8SOKl292tKozRfbb.
[root@server4 ingress]# kubectl create secret generic basic-auth --from-file=auth
secret/basic-auth created
[root@server4 ingress]# kubectl get secrets
NAME TYPE DATA AGE
basic-auth Opaque 1 70s
default-token-rnpl9 kubernetes.io/service-account-token 3 5d
tls-secret kubernetes.io/tls 2 19m
[root@server4 ingress]# vim ingress.yaml
apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
name: ingress-nginx
annotations:
nginx.ingress.kubernetes.io/auth-type: basic
nginx.ingress.kubernetes.io/auth-secret: basic-auth
nginx.ingress.kubernetes.io/auth-realm: 'Authentication Required - jwl'
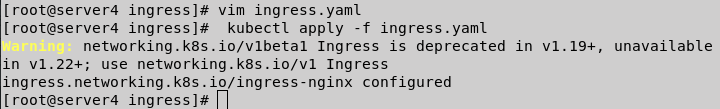
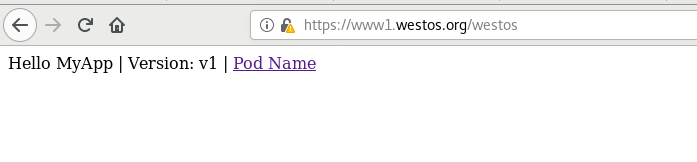
[root@server4 ingress]# kubectl apply -f ingress.yaml
Warning: networking.k8s.io/v1beta1 Ingress is deprecated in v1.19+, unavailable in v1.22+; use networking.k8s.io/v1 Ingress
ingress.networking.k8s.io/ingress-nginx configured


浏览器访问认证

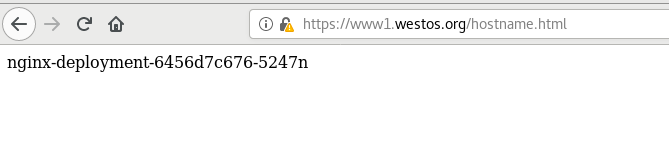
2.lngrees 地址重写
[root@server4 ingress]# vim ingress.yaml
apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
name: ingress-nginx
annotations:
nginx.ingress.kubernetes.io/app-root: /hostname.html
nginx.ingress.kubernetes.io/auth-type: basic
nginx.ingress.kubernetes.io/auth-secret: basic-auth
nginx.ingress.kubernetes.io/auth-realm: 'Authentication Required - jwl'
[root@server4 ingress]# kubectl apply -f ingress.yaml
Warning: networking.k8s.io/v1beta1 Ingress is deprecated in v1.19+, unavailable in v1.22+; use networking.k8s.io/v1 Ingress
ingress.networking.k8s.io/ingress-nginx configured


[root@server4 ingress]# vim ingress.yaml
apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
name: ingress-nginx
annotations:
nginx.ingress.kubernetes.io/rewrite-target: /$2
#nginx.ingress.kubernetes.io/app-root: /hostname.html
nginx.ingress.kubernetes.io/auth-type: basic
nginx.ingress.kubernetes.io/auth-secret: basic-auth
nginx.ingress.kubernetes.io/auth-realm: 'Authentication Required - jwl'
[root@server4 ingress]# kubectl apply -f ingress.yaml
Warning: networking.k8s.io/v1beta1 Ingress is deprecated in v1.19+, unavailable in v1.22+; use networking.k8s.io/v1 Ingress
ingress.networking.k8s.io/ingress-nginx configured
[root@server4 ingress]#
##真机测试
[root@foundation15 ~]# curl https://www1.westos.org
[root@foundation15 ~]# curl -k -I https://www1.westos.org
[root@foundation15 ~]# curl -k -u jwl:westos -I https://www1.westos.org
[root@foundation15 ~]# curl -k -u jwl:westos -I https://www1.westos.org/westos


























 1万+
1万+











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








