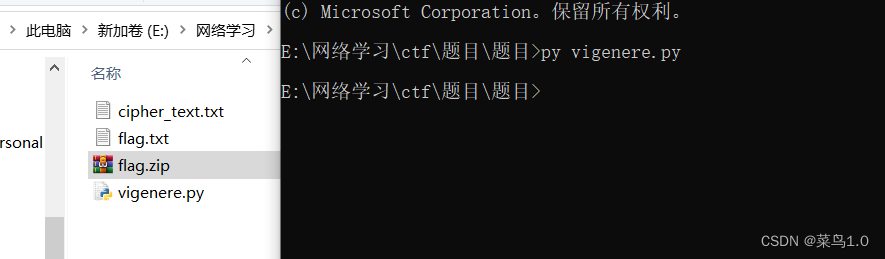
1.解码
打开flag.txt 看着像维吉尼亚加密 应该是变种维吉尼亚

密文在cipher_text.txt中 打开cipher_text.txt 开头就看到504Q0304 不就是504b0304吗 zip压缩包文件头 那就明白了 里面的大写字母被加密了 直接仿维吉尼亚写解密脚本

提示的秘钥是ABCDE 知道明文都是16进制 那肯定就是ABCDEF了 直接简单写个解密脚本
import re
import struct
su = open('cipher_text.txt','r')
su = su.read()
#su = '504Q0304140000000000628I575500000000000000000000000007001300UFENK3U3T0B92Y75700I'
m = ['A','B','C','D','E','F']#横坐标
k = ['A','B','C','D','E']#秘钥
#密文对照表
a = 'PQLNEY'
b = 'HRVKEI'
c = 'SNUKRT'
d = 'JTKQVF'
e = 'JZBLEP'
y = ''
shu = 0#记录大写字母次数
for i in su:
if re.search('[A-Z]',i):#如果是大写字母就执行解密
#print(i)
x = k[shu%len(k)]#获取秘钥
#print(x)
shu = shu+1
if x =='A':
xu = a.find(i)
y = y+m[xu]
if x =='B':
xu = b.find(i)
y = y+m[xu]
if x =='C':
xu = c.find(i)
y = y+m[xu]
if x =='D':
xu = d.find(i)
y = y+m[xu]
if x =='E':
xu = e.find(i)
y = y+m[xu]
#print(y)
else:#不是大写字母不管
y =y+i
res = [y[i:i+2] for i in range(0,len(y),2)]#将解密好的16进制值 两个一组定好格式
with open('flag.zip','wb') as f:#将解密的明文转化为zip文件
for i in res:
s = struct.pack('B',int(i,16))#将整数转化为字节
f.write(s)
直接得到压缩包
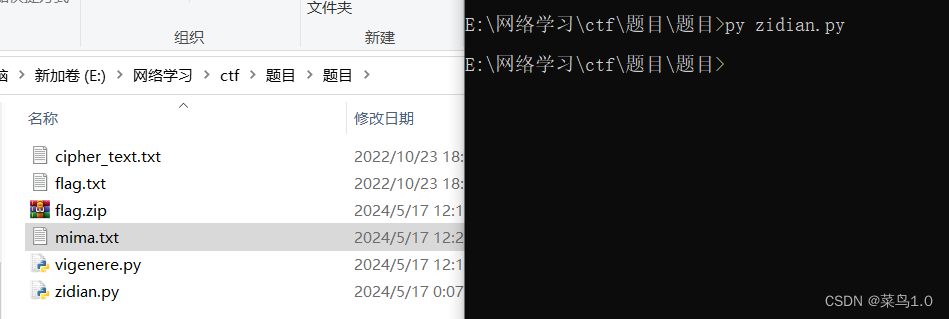
2.爆破
压缩包加密了 看着密码应该就在后面五个txt文件里 每个文件六个字节 八成是crc32爆破

直接crc32爆破脚本走起
爆破脚本:https://github.com/theonlypwner/crc32

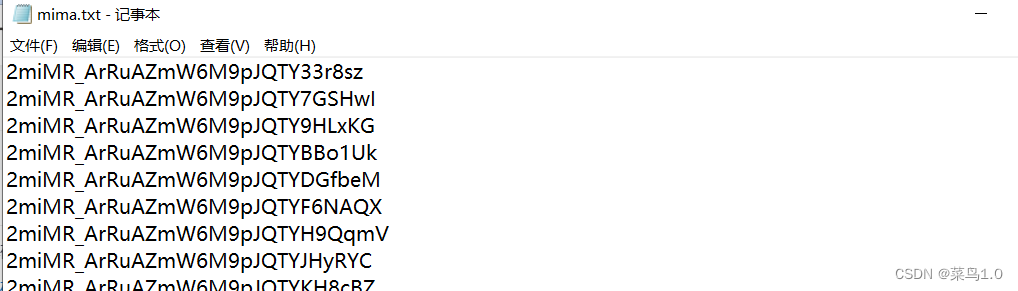
爆破完五个crc32后 解密出来的密码看不出啥规律 不知道哪个组合才是密码 懒得管了 直接将所有组合搞成一个字典直接爆破
a = ['2miMR_', '5tnsxt', 'EiAfA8', 'U4YYYg', 'Uytd4o', 'VE0Kvk', 'WEqzmr', 'Yk0Z80', 'ZWtuz4', 'fZ6p89', 'it6avb', 'jHrN4f', 'kimoF3', 'ompnGP', 'wJBCVw', 'z44aEu', 'zXGLA1']
b = ['ArRuA', 'Bu2vU1', 'GqnFOK', 'JB5Y1A', 'NgvHYn', 'Og7yBw', 'PEM6xo', 'YSU8nJ', 'nhEqbk', 'qVpbYg', 'us3s1H', 'wO6mhU', 'wSy1iA']
c = ['ZmW6M', '1OFImu', '3sCW4h', 'CO2Rdh', 'DJz0OW', 'DV5lNC', 'Iens0I', 'KYkmiT', 'N1Dpwj', 'XTDP7K', 'ZhANnV', 'eYGdn_', 'geBz7B', 'kVXTRQ', 'lO_jxz', 'oREUS2', 'sqjyCv', 'zgrwUS']
d = ['9pJQTY', 'CG9e94', 'CfguPx', 'G_k89C', 'Li9two', 'MixElv', 'RWMVWz', 'dpSrAV', 'qEdPG7', 'rD13mk', 'uAyQFT', 'w0QrrA']
e = ['33r8sz', '7GSHwI', '9HLxKG', 'BBo1Uk', 'DGfbeM', 'F6NAQX', 'H9QqmV', 'JHyRYC', 'KH8cBZ', 'UvLAbO', 'cQRetc', 'h6bHVS', 'jGJkbF', 'u4RE4B']
for x in a:
for y in b:
for z in c:
for i in d:
for o in e:
mima = ''
mima = mima+x+y+z+i+o
#print(mima)
with open('mima.txt','a') as file:
file.write(f'{mima}\n')
开始爆破

得到压缩包密码:5tnsxtGqnFOKN1DpwjdpSrAVh6bHVS
3.base解码
解压 又是一堆 最后三个等号看着像base加密 这么长八成进行了多次base加密
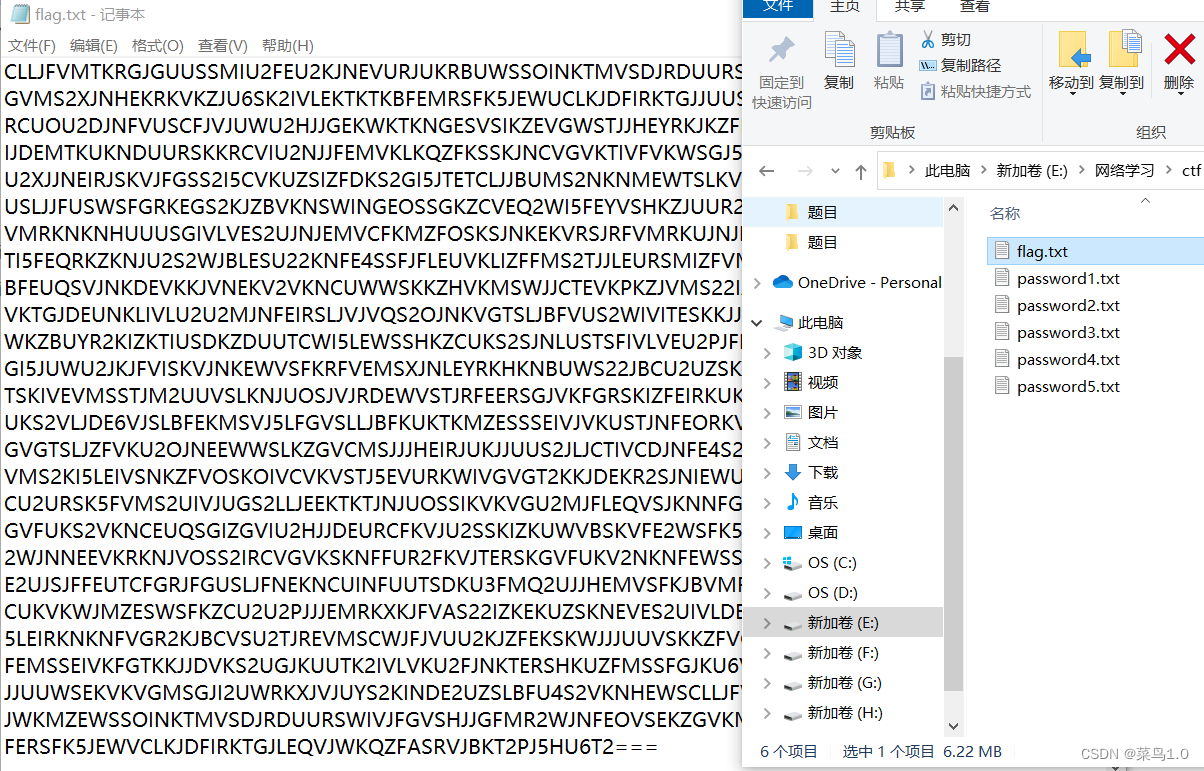
这里我直接网上借鉴了一个脚本 循环base解码
import base64
s = ''
with open('flag.txt','r') as f:
s = "".join(f)
x = s.encode('utf-8')#将读取的base编码字符串转换为bytes类型
while True:
try:
x = s
s = base64.b16decode(s)#base16解码
continue
except:
pass
try:
x = s
s = base64.b32decode(s)#base32解码
continue
except:
pass
try:
x = s
s = base64.b64decode(s)#base64解码
continue
except:
pass
break
print(x.decode('utf-8'))#直接输出解码内容
#将解码内容写入txt文本
'''
with open('basejie.txt','w') as file:
file.write(x.decode('utf-8'))#将bytes类型转换为str类型
'''

得到了flag:F{__y_4Lyav_StAo4esm!Gue4oa} 不过不太对劲 看着像栅栏加密
flag在第三栏 flag:FLAG{you_a4e_ve4y_so_Sma4t!}注:提交的时候FLAG小写






















 901
901











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








