1、tcpdump
tcpdump 是一个很常用的网络包分析工具,可以用来显示通过网络传输到本系统的 TCP/IP 以及其他网络的数据包。tcpdump 使用 libpcap 库来抓取网络报,这个库在几乎在所有的 Linux/Unix 中都有。tcpdump 是一款灵活、功能强大的抓包工具,能有效地帮助排查网络故障问题。
tcpdump 存在于基本的 Linux 系统中,由于它需要将网络界面设置为混杂模式,普通用户不能正常执行,但具备 root 权限的用户可以直接执行它来获取网络上的信息。因此系统中存在网络分析工具主要不是对本机安全的威胁,而是对网络上的其他计算机的安全存在威胁。tcpdump 可以将网络中传送的数据包的 “头” 完全截获下来提供分析。它支持针对网络层、协议、主机、网络或端口的过滤,并提供 and、or、not 等逻辑语句来帮助我们去掉无用的信息。
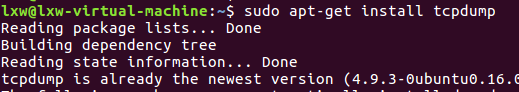
2、tcpdump安装
#centos
[root@VM_0_11_centos ~]# yum -y install tcpdump*
3、tcpdump使用
TCPDUMP(8) System Manager's Manual TCPDUMP(8)
NAME
tcpdump - dump traffic on a network
SYNOPSIS
tcpdump [ -AbdDefhHIJKlLnNOpqStuUvxX# ] [ -B buffer_size ]
[ -c count ]
[ -C file_size ] [ -G rotate_seconds ] [ -F file ]
[ -i interface ] [ -j tstamp_type ] [ -m module ] [ -M secret ]
[ --number ] [ -Q|-P in|out|inout ]
[ -r file ] [ -V file ] [ -s snaplen ] [ -T type ] [ -w file ]
[ -W filecount ]
[ -E spi@ipaddr algo:secret,... ]
[ -y datalinktype ] [ -z postrotate-command ] [ -Z user ]
[ --time-stamp-precision=tstamp_precision ]
[ --immediate-mode ] [ --version ]
[ expression ]
1)-i,监控指定网络端口
#监控所有网卡数据信息
[root@VM_0_11_centos ~]# tcpdump -i any
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode
listening on any, link-type LINUX_SLL (Linux cooked), capture size 262144 bytes
22:18:58.762556 IP VM_0_11_centos.ssh > 36.113.128.53.8461: Flags [P.], seq 1316679858:1316679894, ack 3713556919, win 292, length 36
#监控指定网卡
[root@VM_0_11_centos ~]# tcpdump -i eth0
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode
listening on eth0, link-type EN10MB (Ethernet), capture size 262144 bytes
-w将获得的包数据写入文件中
[root@VM_0_11_centos ~]# tcpdump -i eth0 -w /tmp/eth0.package
tcpdump: listening on eth0, link-type EN10MB (Ethernet), capture size 262144 bytes
^C24 packets captured
26 packets received by filter
0 packets dropped by kernel
[root@VM_0_11_centos ~]#
2)查看整个网络数据包
[root@VM_0_11_centos ~]# tcpdump net 183.60.82.98
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode
listening on eth0, link-type EN10MB (Ethernet), capture size 262144 bytes
22:29:00.202646 IP VM_0_11_centos.53283 > 183.60.82.98.domain: 25943+ A? registry.access.redhat.com. (44)
3)根据ip地址查看网络报文
#不管是源地址还是目的地址,用host
[root@VM_0_11_centos ~]# tcpdump host 183.60.82.98
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode
listening on eth0, link-type EN10MB (Ethernet), capture size 262144 bytes
22:32:42.467074 IP VM_0_11_centos.45371 > 183.60.82.98.domain: 191+ A? update2.agent.tencentyun.com. (46)
#ip作为源地址,即该ip发送到本机的数据包
[root@VM_0_11_centos ~]# tcpdump src 183.60.82.98
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode
listening on eth0, link-type EN10MB (Ethernet), capture size 262144 bytes
#ip作为目的地址,即本机发往目的ip的数据包
[root@VM_0_11_centos ~]# tcpdump dst 183.60.82.98
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode
listening on eth0, link-type EN10MB (Ethernet), capture size 262144 bytes
22:35:03.797669 IP VM_0_11_centos.56635 > 183.60.82.98.domain: 59547+ PTR? 2.0.254.169.in-addr.arpa. (42)
4)查看协议数据包
[root@VM_0_11_centos ~]# tcpdump udp
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode
listening on eth0, link-type EN10MB (Ethernet), capture size 262144 bytes
22:39:03.168139 IP VM_0_11_centos.ntp > gus.buptnet.edu.cn.ntp: NTPv4, Client, length 48
5)查看特定端口数据包
[root@VM_0_11_centos ~]# tcpdump port 22
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode
listening on eth0, link-type EN10MB (Ethernet), capture size 262144 bytes
22:39:40.701809 IP VM_0_11_centos.ssh > 36.113.128.53.8461: Flags [P.], seq 1316900326:1316900514, ack 3713566635, win 292, length 188
22:39:40.753734 IP 36.113.128.53.8461 > VM_0_11_centos.ssh: Flags [.], ack 188, win 16519, length 0
6)使用 “与” (and,&&)、“或” (or,|| ) 和 “非”(not,!) 来将两个条件组合起来
[root@VM_0_11_centos ~]# tcpdump host 183.60.82.98 && port 22 -w /tmp/test
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode
listening on eth0, link-type EN10MB (Ethernet), capture size 262144 bytes
7)列出网络接口
[root@VM_0_11_centos ~]# tcpdump -D
1.eth0
2.docker0
3.nflog (Linux netfilter log (NFLOG) interface)
4.nfqueue (Linux netfilter queue (NFQUEUE) interface)
5.usbmon1 (USB bus number 1)
6.any (Pseudo-device that captures on all interfaces)
7.lo [Loopback]
[root@VM_0_11_centos ~]#
8)限制抓包次数 -c
[root@VM_0_11_centos ~]# tcpdump host 183.60.82.98 -c 10
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode
listening on eth0, link-type EN10MB (Ethernet), capture size 262144 bytes
22:47:10.203892 IP VM_0_11_centos.48876 > 183.60.82.98.domain: 38715+ A? registry.access.redhat.com. (44)
22:47:10.206967 IP VM_0_11_centos.51334 > 183.60.82.98.domain: 65192+ PTR? 11.0.17.172.in-addr.arpa. (42)
22:47:10.208419 IP 183.60.82.98.domain > VM_0_11_centos.51334: 65192 NXDomain* 0/1/0 (101)
22:47:10.290120 IP 183.60.82.98.domain > VM_0_11_centos.48876: 38715 3/0/0 CNAME registry.access.redhat.com.edgekey.net., CNAME e14353.d.akamaiedge.net., A 23.204.45.225 (146)
22:47:10.290654 IP VM_0_11_centos.42036 > 183.60.82.98.domain: 9032+ A? registry.access.redhat.com. (44)
22:47:10.321802 IP 183.60.82.98.domain > VM_0_11_centos.42036: 9032 3/0/0 CNAME registry.access.redhat.com.edgekey.net., CNAME e14353.d.akamaiedge.net., A 23.204.45.225 (146)
22:47:10.322424 IP VM_0_11_centos.55344 > 183.60.82.98.domain: 7152+ A? registry.access.redhat.com. (44)
22:47:10.323860 IP 183.60.82.98.domain > VM_0_11_centos.55344: 7152 3/0/0 CNAME registry.access.redhat.com.edgekey.net., CNAME e14353.d.akamaiedge.net., A 23.204.45.225 (146)
22:47:53.203240 IP VM_0_11_centos.55849 > 183.60.82.98.domain: 10213+ A? registry.access.redhat.com. (44)
22:47:53.206932 IP 183.60.82.98.domain > VM_0_11_centos.55849: 10213 3/0/0 CNAME registry.access.redhat.com.edgekey.net., CNAME e14353.d.akamaiedge.net., A 23.204.45.225 (146)
10 packets captured
10 packets received by filter
0 packets dropped by kernel
4、数据包解析
22:39:42.295682 IP VM_0_11_centos.ssh > 36.113.128.53.8461: Flags [P.], seq 21840:21996, ack 37, win 292, length 156
22:39:42.295835 IP VM_0_11_centos.ssh > 36.113.128.53.8461: Flags [P.], seq 21996:22256, ack 37, win 292, length 260
字段解析:
1) 22:39:42.295682:时间戳;
2)IP:IP 是网络层协议类型,这里是 IPv4,如果是 IPv6 协议,该字段值是 IP6;
3)VM_0_11_centos.ssh:源地址与端口;
4)36.113.128.53.8461:目的地址与端口;
5)Flags [P.]:TCP 报文标记段 Flags [P.];
6)seq 21840:21996:对于抓取的第一个数据包,该字段值是一个绝对数字,后续包使用相对数值,以便更容易查询跟踪;
7)ack 37:数据包确认序号
8)win 292:窗口大小 win ,它表示接收缓冲区中可用的字节数;
9)length 156:length 代表数据包有效载荷字节长度;






















 271
271











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








