
Conference:ACM International Conference on the Foundations of Software Engineering (FSE)
CCF level:CCF A
Categories:软件工程/系统软件/程序设计语言
Year:2024
Num:4
1
Title:
Demystifying Invariant Effectiveness for Securing Smart Contracts
揭秘保护智能合约的不变有效性
Authors:
ZHIYANG CHEN, University of Toronto, Canada
YE LIU, Nanyang Technological University, Singapore
SIDI MOHAMED BEILLAHI, University of Toronto, Canada
YI LI, Nanyang Technological University, Singapore
FAN LONG, University of Toronto, Canada
Abstract:
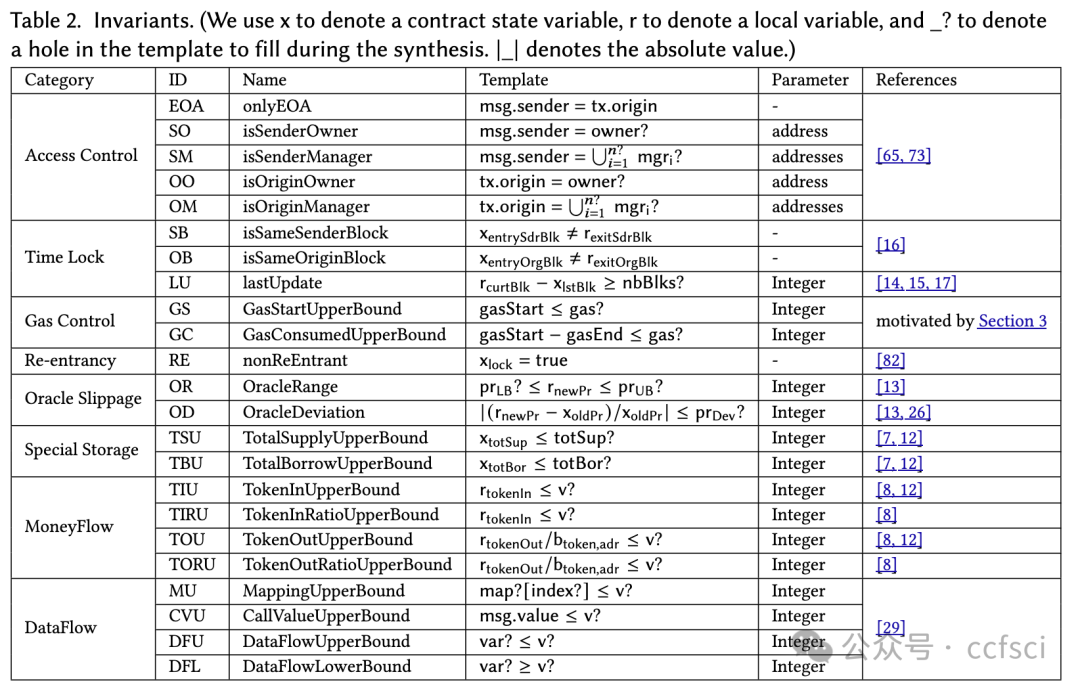
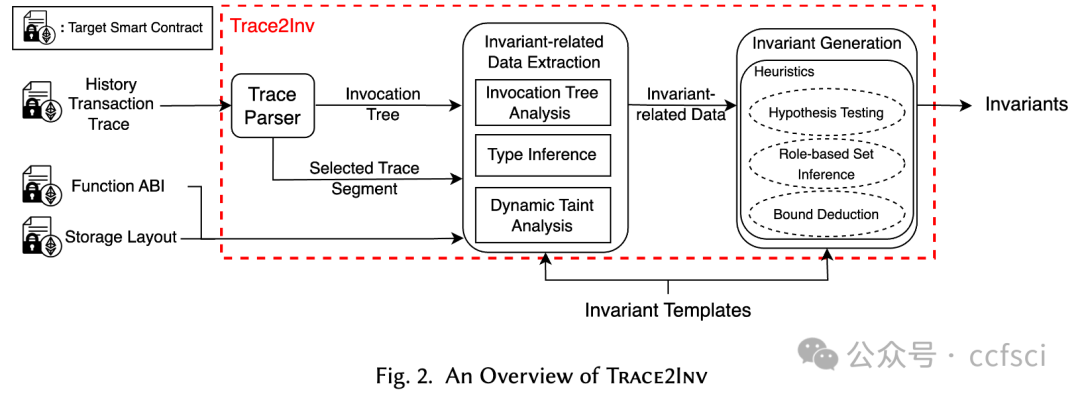
Smart contract transactions associated with security attacks often exhibit distinct behavioral patterns compared with historical benign transactions before the attacking events. While many runtime monitoring and guarding mechanisms have been proposed to validate invariants and stop anomalous transactions on the fly, the empirical effectiveness of the invariants used remains largely unexplored. In this paper, we studied 23 prevalent invariants of 8 categories, which are either deployed in high-profile protocols or endorsed by leading auditing firms and security experts. Using these well-established invariants as templates, we developed a tool which dynamically generates new invariants customized for a given contract based on its historical transaction data. We evaluated our tool on 42 smart contracts that fell victim to 27 distinct exploits on the Ethereum blockchain. Our findings reveal that the most effective invariant guard alone can successfully block 18 of the 27 identified exploits with minimal gas overhead. Our analysis also shows that most of the invariants remain effective even when the experienced attackers attempt to bypass them. Additionally, we studied the possibility of combining multiple invariant guards, resulting in blocking up to 23 of the 27 benchmark exploits and achieving false positive rates as low as 0.32%.
与攻击事件发生前的历史良性交易相比,与安全攻击相关的智能合约交易往往表现出截然不同的行为模式。虽然已经提出了许多运行时监控和防护机制来验证不变式并即时阻止异常交易,但所用不变式的实证有效性在很大程度上仍未得到探索。在本文中,我们研究了 8 个类别中的 23 个流行不变式,这些不变式或已部署在知名协议中,或已得到领先审计公司和安全专家的认可。以这些成熟的不变式为模板,我们开发了一种工具,可根据历史交易数据动态生成为给定合约定制的新不变式。我们对以太坊区块链上遭受 27 种不同漏洞攻击的 42 个智能合约进行了评估。我们的研究结果表明,仅最有效的不变式防护就能以最小的gas开销成功阻止 27 种已识别漏洞中的 18 种。我们的分析还表明,即使经验丰富的攻击者试图绕过它们,大多数不变式仍然有效。此外,我们还研究了组合多个不变式防护的可能性,结果在 27 个基准漏洞中成功拦截了 23 个,误报率低至 0.32%。

Pdf link:
https://arxiv.org/abs/2404.14580
2
Title:
Efficiently Detecting Reentrancy Vulnerabilities in Complex Smart Contracts
高效检测复杂智能合约中的重入漏洞
Authors:
ZEXU WANG, Sun Yat-sen University, China and Peng Cheng Laboratory, China
JIACHI CHEN, Sun Yat-sen University, China
YANLIN WANG, Sun Yat-sen University, China
YU ZHANG, Harbin Institute of Technology, China and Peng Cheng Laboratory, China
WEIZHE ZHANG, Harbin Institute of Technology, China and Peng Cheng Laboratory, China
ZIBIN ZHENG∗, Sun Yat-sen University, China and GuangDong Engineering Technology Research Center of Blockchain, China
Abstract:
Reentrancy vulnerability as one of the most notorious vulnerabilities, has been a prominent topic in smart contract security research. Research shows that existing vulnerability detection presents a range of challenges, especially as smart contracts continue to increase in complexity. Existing tools perform poorly in terms of efficiency and successful detection rates for vulnerabilities in complex contracts.
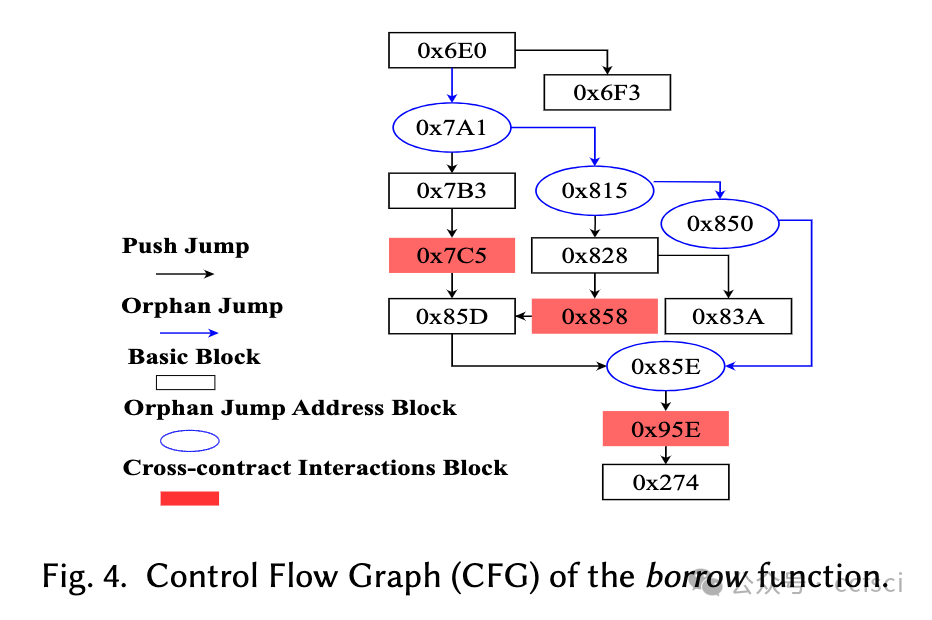
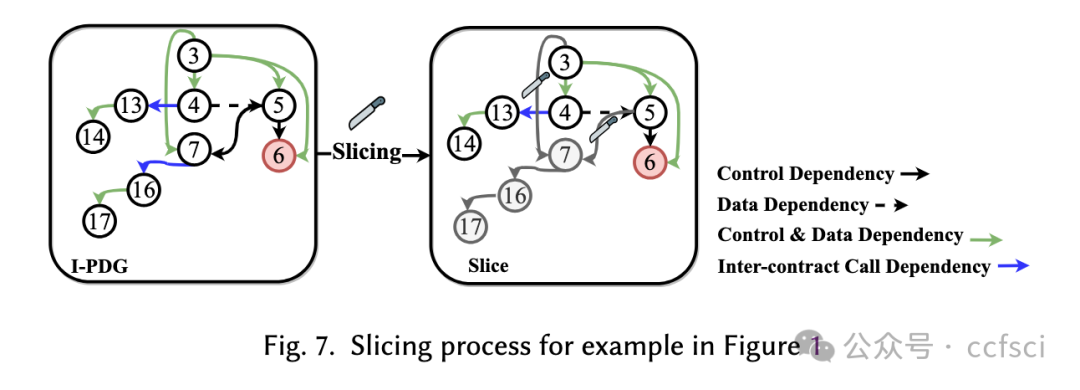
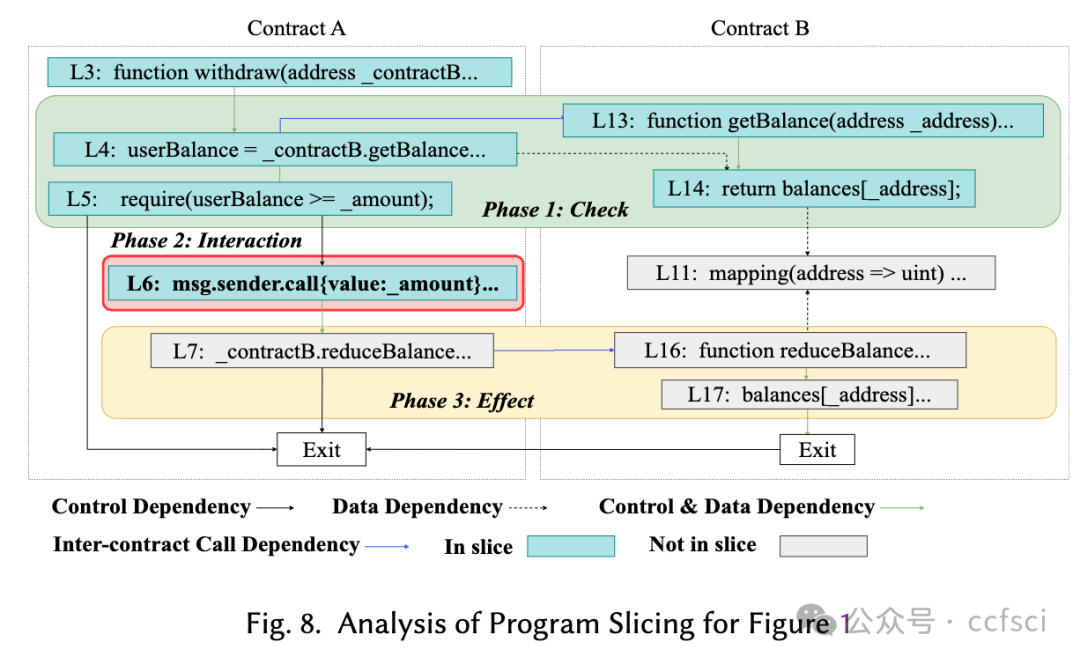
To effectively detect reentrancy vulnerabilities in contracts with complex logic, we propose a tool named SliSE. SliSE’s detection process consists of two stages: Warning Search and Symbolic Execution Verification. In Stage I, SliSE utilizes program slicing to analyze the Inter-contract Program Dependency Graph (I-PDG) of the contract, and collects suspicious vulnerability information as warnings. In Stage II, symbolic execution is employed to verify the reachability of these warnings, thereby enhancing vulnerability detection accuracy. SliSE obtained the best performance compared with eight state-of-the-art detection tools. It achieved an F1 score of 78.65%, surpassing the highest score recorded by an existing tool of 9.26%. Additionally, it attained a recall rate exceeding 90% for detection of contracts on Ethereum. Overall, SliSE provides a robust and efficient method for detection of Reentrancy vulnerabilities for complex contracts.
重入漏洞作为最臭名昭著的漏洞之一,一直是智能合约安全研究中的一个突出话题。研究表明,现有的漏洞检测存在一系列挑战,尤其是随着智能合约的复杂性不断增加。现有工具在复杂合约漏洞的效率和成功检测率方面表现不佳。为了有效检测具有复杂逻辑的合约中的重入漏洞,我们提出了一种名为 SliSE 的工具。SliSE 的检测过程包括两个阶段:警告搜索和符号执行验证。在第一阶段,SliSE 利用程序切片分析合约的合约间程序依赖图(I-PDG),并收集可疑的漏洞信息作为警告。在第二阶段,采用符号执行来验证这些警告的可达性,从而提高漏洞检测的准确性。与八种最先进的检测工具相比,SliSE 的性能最佳。它的 F1 得分为 78.65%,超过了现有工具记录的最高得分 9.26%。此外,在检测以太坊上的合约时,它的召回率超过了 90%。总体而言,SliSE 为复杂合约的重入漏洞检测提供了一种稳健高效的方法。



Pdf link:
https://arxiv.org/abs/2403.11254
3
Title:
SmartAxe: Detecting Cross-Chain Vulnerabilities in Bridge Smart Contracts via Fine-Grained Static Analysis
SmartAxe:通过细粒度静态分析检测 Bridge 智能合约中的跨链漏洞
Authors:
Zeqin Liao (Sun Yat-sen University), Henglong Liang, Yuhong Nan, Sicheng Hao, Zibin Zheng, Juan Zhai, Jiajing Wu
Abstract:
With the increasing popularity of blockchain, different blockchain platforms coexist in the ecosystem (e.g., Ethereum, BNB, EOSIO, etc.), which prompts the high demand for cross-chain communication. Cross-chain bridge is a specific type of decentralized application for asset exchange across different blockchain platforms. Securing the smart contracts of cross-chain bridges is in urgent need, as there are a number of recent security incidents with heavy financial losses caused by vulnerabilities in bridge smart contracts, as we call them Cross-Chain Vulnerabilities (CCVs). However, automatically identifying CCVs in smart contracts poses several unique challenges. Particularly, it is non-trivial to (1) identify application-specific access control constraints needed for cross-bridge asset exchange, and (2) identify inconsistent cross-chain semantics between the two sides of the bridge. In this paper, we propose SmartAxe, a new framework to identify vulnerabilities in cross-chain bridge smart contracts. Particularly, to locate vulnerable functions that have access control incompleteness, SmartAxe models the heterogeneous implementations of access control and finds necessary security checks in smart contracts through probabilistic pattern inference. Besides, SmartAxe constructs cross-chain control-flow graph (xCFG) and data-flow graph (xDFG), which help to find semantic inconsistency during cross-chain data communication. To evaluate SmartAxe, we collect and label a dataset of 88 CCVs from real-attacks cross-chain bridge contracts. Evaluation results show that SmartAxe achieves a precision of 84.95% and a recall of 89.77%. In addition, SmartAxe successfully identifies 278 new/unknown CCVs from 128 real-world cross-chain bridge applications (i.e., from 1,703 smart contracts). These identified CCVs affect a total amount of digital assets worth 1,885,250 USD
随着区块链的日益普及,不同的区块链平台(如以太坊、BNB、EOSIO 等)共存于生态系统中,这促使人们对跨链通信提出了很高的要求。跨链桥是一种特殊的去中心化应用,用于在不同区块链平台之间进行资产交换。由于近期发生了多起因跨链桥智能合约漏洞(我们称之为跨链漏洞(CCV))而造成重大经济损失的安全事件,因此迫切需要确保跨链桥智能合约的安全。然而,自动识别智能合约中的 CCV 带来了一些独特的挑战。特别是,要(1)识别跨桥资产交换所需的特定于应用程序的访问控制约束,以及(2)识别桥双方之间不一致的跨链语义,并非易事。在本文中,我们提出了一个新框架 SmartAxe,用于识别跨链桥智能合约中的漏洞。SmartAxe 对访问控制的异构实现进行建模,并通过概率模式推理在智能合约中找到必要的安全检查。此外,SmartAxe 还构建了跨链控制流图(xCFG)和数据流图(xDFG),有助于发现跨链数据通信过程中的语义不一致问题。为了评估 SmartAxe,我们从真实攻击的跨链桥合约中收集并标注了 88 个 CCV 数据集。评估结果表明,SmartAxe 的精确度为 84.95%,召回率为 89.77%。此外,SmartAxe 还成功地从 128 个真实跨链桥接应用(即 1,703 个智能合约)中识别出 278 个新的/未知 CCV。这些被识别的 CCV 影响的数字资产总价值为 1,885,250 美元
Pdf link:
暂未公布
4
Title:
Static Application Security Testing (SAST) Tools for Smart Contracts: How Far Are We?
智能合约的静态应用安全测试 (SAST) 工具:我们还有多远?
Authors:
KAIXUAN LI, Shanghai Key Laboratory of Trustworthy Computing, East China Normal University, China
YUE XUE, MetaTrust Labs, Singapore
SEN CHEN∗, College of Intelligence and Computing, Tianjin University, China
HAN LIU, Shanghai Key Laboratory of Trustworthy Computing, East China Normal University, China
KAIRAN SUN, Nanyang Technological University, Singapore
MING HU, Nanyang Technological University, Singapore
HAIJUN WANG, Xi’an Jiaotong University, China
YANG LIU, Nanyang Technological University, Singapore
YIXIANG CHEN, Shanghai Key Laboratory of Trustworthy Computing, East China Normal University, China
Abstract:
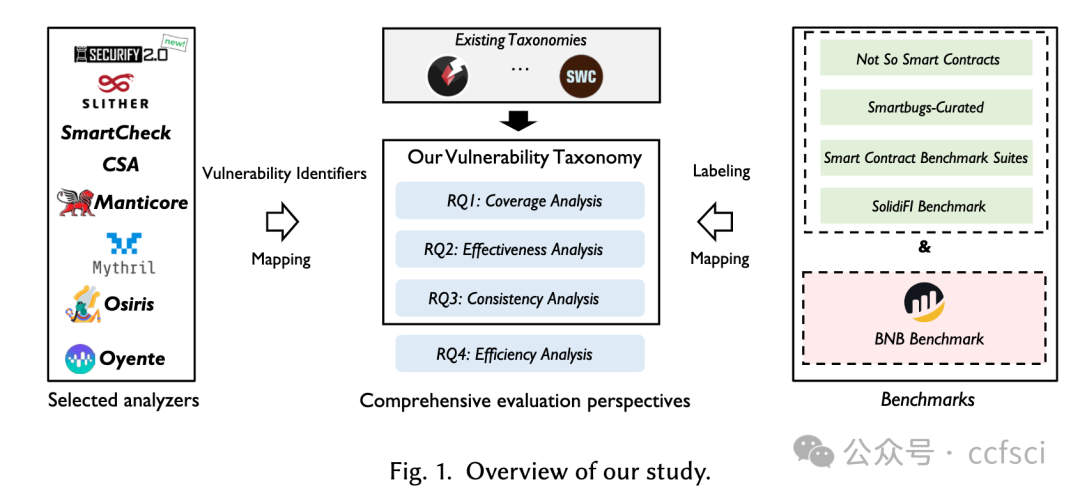
In recent years, the importance of smart contract security has been heightened by the increasing number of attacks against them. To address this issue, a multitude of static application security testing (SAST) tools have been proposed for detecting vulnerabilities in smart contracts. However, objectively comparing these tools to determine their effectiveness remains challenging. Existing studies often fall short due to the taxonomies and benchmarks only covering a coarse and potentially outdated set of vulnerability types, which leads to evaluations that are not entirely comprehensive and may display bias.
In this paper, we fill this gap by proposing an up-to-date and fine-grained taxonomy that includes 45 unique vulnerability types for smart contracts. Taking it as a baseline, we develop an extensive benchmark that covers 40 distinct types and includes a diverse range of code characteristics, vulnerability patterns, and application scenarios. Based on them, we evaluated 8 SAST tools using this benchmark, which comprises 788 smart contract files and 10,394 vulnerabilities. Our results reveal that the existing SAST tools fail to detect around 50% of vulnerabilities in our benchmark and suffer from high false positives, with precision not surpassing 10%. We also discover that by combining the results of multiple tools, the false negative rate can be reduced effectively, at the expense of flagging 36.77 percentage points more functions. Nevertheless, many vulnerabilities, especially those beyond Access Control and Reentrancy vulnerabilities, remain undetected. We finally highlight the valuable insights from our study, hoping to provide guidance on tool development, enhancement, evaluation, and selection for developers, researchers, and practitioners.
近年来,由于针对智能合约的攻击日益增多,智能合约安全的重要性也随之提高。为了解决这个问题,人们提出了许多静态应用安全测试(SAST)工具来检测智能合约中的漏洞。然而,客观地比较这些工具以确定其有效性仍然具有挑战性。现有的研究往往存在不足,因为分类标准和基准只涵盖了一组粗略的、可能已经过时的漏洞类型,这导致评估并不完全全面,而且可能存在偏差。在本文中,我们提出了一种最新的细粒度分类法,其中包括 45 种独特的智能合约漏洞类型,从而填补了这一空白。以此为基线,我们开发了一个广泛的基准,涵盖 40 种不同类型,包括各种代码特征、漏洞模式和应用场景。在此基础上,我们使用该基准评估了 8 个 SAST 工具,其中包括 788 个智能合约文件和 10,394 个漏洞。我们的结果表明,现有的 SAST 工具无法检测到基准中约 50% 的漏洞,而且误报率很高,精度不超过 10%。我们还发现,通过合并多个工具的结果,可以有效降低误报率,但代价是标记的功能要多出 36.77 个百分点。尽管如此,许多漏洞,尤其是访问控制和重入性漏洞之外的漏洞,仍然没有被发现。最后,我们强调了研究中的宝贵见解,希望能为开发人员、研究人员和从业人员提供工具开发、增强、评估和选择方面的指导。


Pdf link:
https://arxiv.org/abs/2404.18186
详情:https://2024.esec-fse.org/track/fse-2024-research-papers

关注我们,持续接收区块链最新论文
洞察区块链技术发展趋势
Follow us to keep receiving the latest blockchain papers
Insight into Blockchain Technology Trends

























 867
867











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










