目录
二、创建Role、Rolebinding,设置权限访问confluence和jira名称空间
准备
1、 名称空间
kubectl create ns confluence
kubectl create ns jira

2、ssl证书工具准备
1)下载证书工具
链接:https://pan.baidu.com/s/1gDRQuxekvgInplLkpjvhQw?pwd=f31x
提取码:f31x
或者去github地址下载:Releases · cloudflare/cfssl · GitHub
# 上传到服务器
[devops@master2 ~]$ mkdir ~/ssl && cd ~/ssl
[devops@master2 ssl]$ rz
[devops@master2 ssl]$ ll
total 10556
-r-------- 1 devops devops 10808877 Apr 25 11:01 cfssl.zip
2)解压、删除压缩包
[devops@master2 ~]$ mkdir ~/ssl && cd ~/ssl
[devops@master2 ssl]$ rz
[devops@master2 ssl]$ ll
total 39128
-rw-rw-r-- 1 devops devops 12054528 Aug 30 2023 cfssl_1.6.4_linux_amd64
-rw-rw-r-- 1 devops devops 9560064 Aug 30 2023 cfssl-certinfo_1.6.4_linux_amd64
-rw-rw-r-- 1 devops devops 7643136 Aug 30 2023 cfssljson_1.6.4_linux_amd64
-r-------- 1 devops devops 10808877 Apr 25 11:01 cfssl.zip
[devops@master2 ssl]$ rm -rf cfssl.zip
3)重命名cfssl相关文件
目的是为了后续操作文件名短一点,可读性好点,也省事
[devops@master2 ssl]$ rename _1.6.4_linux_amd64 "" *
[devops@master2 ssl]$ ll
total 28572
-rw-rw-r-- 1 devops devops 12054528 Aug 30 2023 cfssl
-rw-rw-r-- 1 devops devops 9560064 Aug 30 2023 cfssl-certinfo
-rw-rw-r-- 1 devops devops 7643136 Aug 30 2023 cfssljson
4)将cfssl文件编程全局命令
将这三个文件,移动到/usr/local/bin目录下,编程全局命令~
[devops@master2 ssl]$ sudo mv ./* /usr/local/bin/
[sudo] password for devops:
[devops@master2 ssl]$ ls -l /usr/local/bin | grep cfssl
-rw-rw-r-- 1 devops devops 12054528 Aug 30 2023 cfssl
-rw-rw-r-- 1 devops devops 9560064 Aug 30 2023 cfssl-certinfo
-rw-rw-r-- 1 devops devops 7643136 Aug 30 2023 cfssljson
5)给cfssl执行文件加执行权限
[devops@master2 ssl]$ sudo chmod +x /usr/local/bin/cfssl*
[devops@master2 ssl]$ ls -l /usr/local/bin | grep cfssl
-rwxrwxr-x 1 devops devops 12054528 Aug 30 2023 cfssl
-rwxrwxr-x 1 devops devops 9560064 Aug 30 2023 cfssl-certinfo
-rwxrwxr-x 1 devops devops 7643136 Aug 30 2023 cfssljson
一、创建altassion用户
1、编辑cfssl工具的生成用户ssl证书的配置文件
根证书
[devops@master2 user-altassion]$ cat ca-config.json
{
"signing": {
"default": {
"expiry": "87600h"
},
"profiles": {
"kubernetes": {
"usages": [
"signing",
"key encipherment",
"server auth",
"client auth"
],
"expiry": "87600h"
}
}
}
}
客户签名证书
[devops@master2 user-altassion]$ cat csr.json
{
"CN": "altassion",
"hosts": [],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"ST": "BeiJing",
"L": "BeiJing",
"O": "k8s",
"OU": "System"
}
]
}
2、使用cfssl工具生成用户的ssl证书
命令中用到的两个文件

# 需要切换root用户来执行
[root@master2 user-altassion]# cfssl gencert -ca=/etc/kubernetes/pki/ca.crt -ca-key=/etc/kubernetes/pki/ca.key -config=ca-config.json -profile=kubernetes csr.json | cfssljson -bare altassion
注意:这里创建的是用户,所以最后的altassion是上面配置csr.json中CN对应的值;如果要创建的是用户组,那么就应该写的是k8s(csr.json中O对应的值)
生成了3个证书文件

3、生成用户的kubeconfig文件
编写kubeconfig.sh脚本
[root@master2 user-altassion]# cat kubeconfig.sh
#!/bin/bash# 配置集群;
# --certificate-authority:指定K8s的ca根证书文件路径
# --embed-certs:
# 1,true,表示将根证书文件的内容写入到配置文件中,
# 2,false,则只是引用配置文件,将kubeconfig
# --server:指定APIServer的地址。
# --kubeconfig:指定kubeconfig的配置文件名称
kubectl config set-cluster altassion-cluster \
--certificate-authority=/etc/kubernetes/pki/ca.crt \
--embed-certs=true \
--server=https://172.16.2.232:6443 \
--kubeconfig=altassion.kubeconfig
# 设置客户端认证,客户端将来需要携带证书让服务端验证
kubectl config set-credentials altassion-client \
--client-key=altassion-key.pem \
--client-certificate=altassion.pem \
--embed-certs=true \
--kubeconfig=altassion.kubeconfig# 设置默认上下文,可以用于绑定多个客户端和服务端的对应关系(客户端和服务端绑定)。
kubectl config set-context altassion \
--cluster=altassion-cluster \
--user=altassion-client \
--kubeconfig=altassion.kubeconfig# 设置当前使用的上下文(正式生效)
kubectl config use-context altassion --kubeconfig=altassion.kubeconfig
执行脚本生成用户证书文件
#文件有小错误,报错啦...
[root@master2 user-altassion]# bash kubeconfig.sh
Cluster "altassion-cluster" set.
error: could not stat client-key file dolphin-key.pem: stat dolphin-key.pem: no such file or directory
Context "altassion" created.
Switched to context "altassion".# 重新编辑z
[root@master2 user-altassion]# vi kubeconfig.sh
[root@master2 user-altassion]# bash kubeconfig.sh
Cluster "altassion-cluster" set.
User "altassion-client" set.
Context "altassion" modified.
Switched to context "altassion".
查看证书文件生成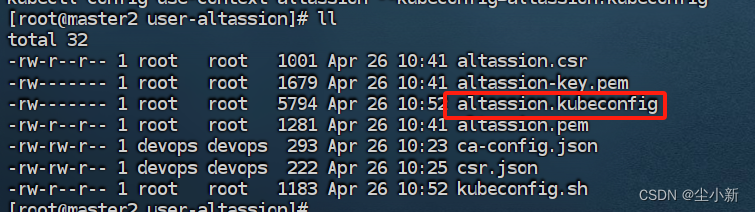
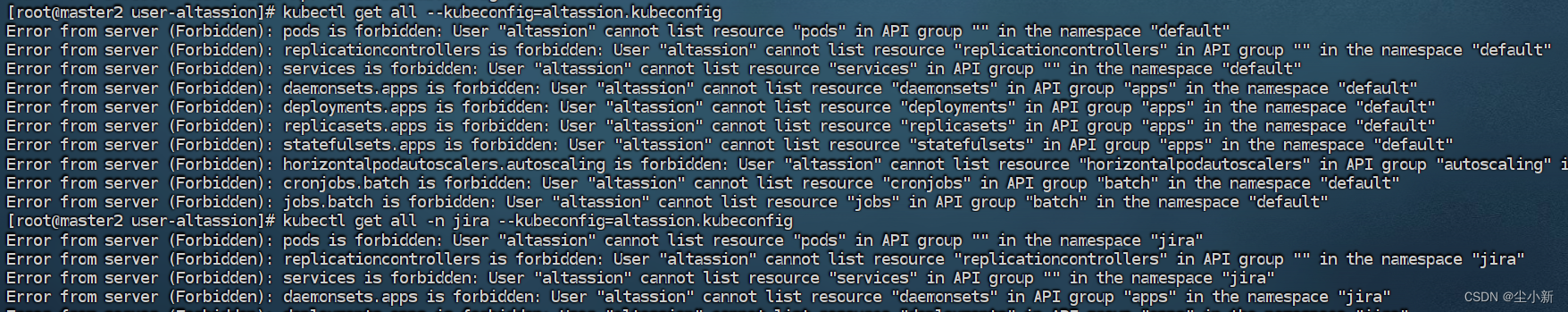
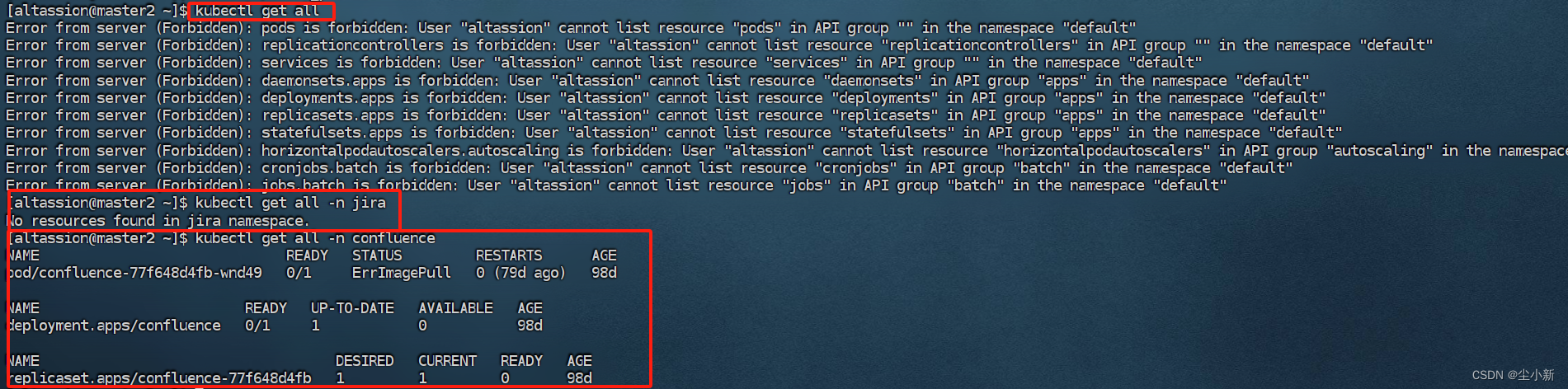
测试查看资源访问,所有资源都无法访问,因为没有进行角色绑定
二、创建Role、Rolebinding,设置权限访问confluence和jira名称空间
1、jira命名空间的访问权限资源文件
[devops@master2 user-altassion]$ cat role-jira-admin.yaml
kind: Role
apiVersion: rbac.authorization.k8s.io/v1
metadata:
# cluster是针对集群范围对象,不需要namespace字段
name: role-jira-admin
namespace: jira# 访问命名空间下的所有资源
rules:
- apiGroups:
- '*'
resources:
- '*'
verbs:
- '*'
---
kind: RoleBinding
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: rolebinding-jira-admin
namespace: jira
subjects:
- kind: User
name: altassion
apiGroup: rbac.authorization.k8s.io
roleRef:
kind: Role
name: role-jira-admin
apiGroup: rbac.authorization.k8s.io
2、confluence名称空间下的访问权限资源文件
[devops@master2 user-altassion]$ cat role-confluence-admin.yaml
kind: Role
apiVersion: rbac.authorization.k8s.io/v1
metadata:
# cluster是针对集群范围对象,不需要namespace字段
name: role-confluence-admin
namespace: confluence
rules:
- apiGroups:
- '*'
resources:
- '*'
verbs:
- '*'
---
kind: RoleBinding
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: rolebinding-confluence-admin
namespace: confluence
subjects:
- kind: User
name: altassion
apiGroup: rbac.authorization.k8s.io
roleRef:
kind: Role
name: role-confluence-admin
apiGroup: rbac.authorization.k8s.io
3、创建资源
[devops@master2 user-altassion]$ kubectl apply -f role-confluence-admin.yaml
[devops@master2 user-altassion]$ kubectl apply -f role-jira-admin.yaml
4、测试访问资源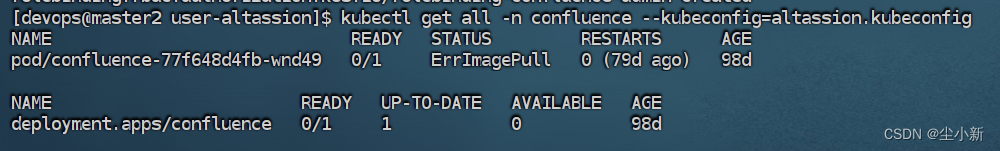

测试结果,我们可以访问jira和confluence的资源,其它名称空间资源无法访问
三、配置linux用户(altassion)访问资源
1、创建linux用户altassion
[devops@master2 user-altassion]$ sudo useradd -g devops altassion
2、设置用户密码
[devops@master2 home]$ sudo passwd altassion
Changing password for user altassion.
New password:
Retype new password:
passwd: all authentication tokens updated successfully.
3、配置~/.kube/config文件
将生成的用户文件的altassion.kubeconfig文件拷贝并重命名到altassion用户的 ~/.kube/config(/home/altassion/.kube/config)文件中
[altassion@master2 .kube]$ pwd
/home/altassion/.kube[altassion@master2 .kube]$ sudo cp /home/devops/ssl/user-altassion/altassion.kubeconfig ./config
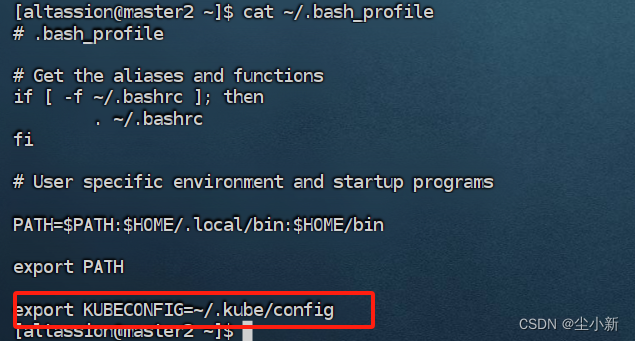
4、修改并生效~/.bash_profile (这一步一般不需要配置,特殊情况如有访问不到需要配置)
[altassion@master2 ~]$ echo "export KUBECONFIG=~/.kube/config" >> ~/.bash_profile
[altassion@master2 ~]$ source ~/.bash_profile
5、测试查看访问资源情况,配置成功
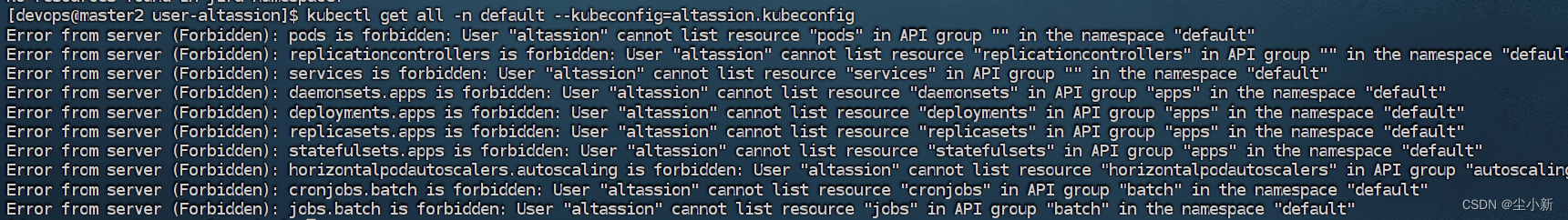
如下图,我们看到无法访问默认命名空间资源,可以访问jira和confluence,配置成功








 本文详细介绍了如何准备ssl证书工具,生成altassion用户的SSL证书和kubeconfig文件,创建Role和Rolebinding以访问confluence和jira命名空间,以及配置Linux用户altassion以访问相关资源。
本文详细介绍了如何准备ssl证书工具,生成altassion用户的SSL证书和kubeconfig文件,创建Role和Rolebinding以访问confluence和jira命名空间,以及配置Linux用户altassion以访问相关资源。














 1605
1605

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








