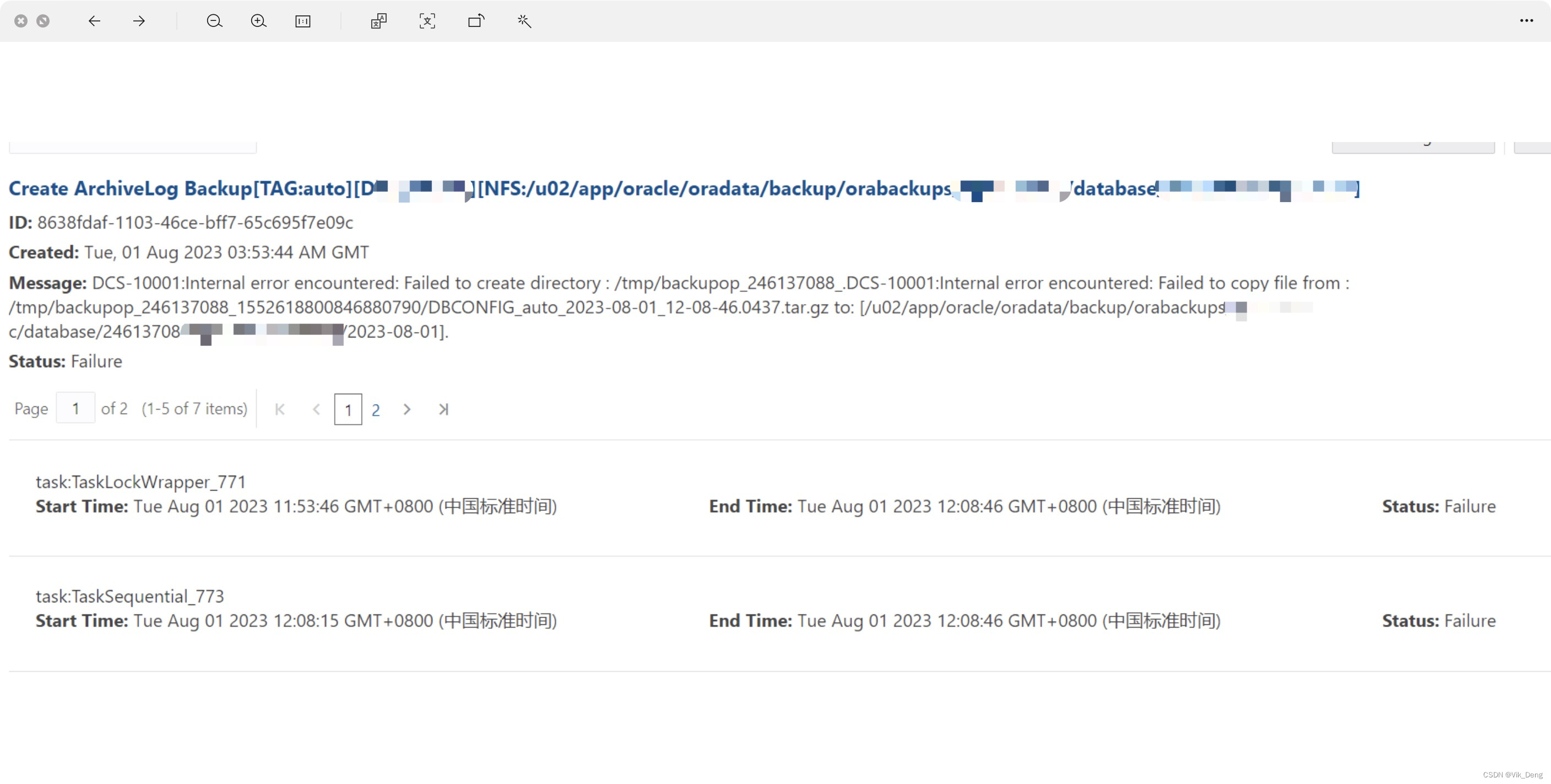
该错误由通过ODA GUI发起数据库备份操作抛出,在ODA内部第一次遇到这类问题,起初怀疑ODA相关配置被修改,随重新做了ODA的认证无果,仔细分析dcs-agent.log发现端倪,
2023-08-02 13:27:57,817 DEBUG [pool-5-dcsrpcworker_thread-11] [] c.o.d.c.u.CommonsUtils:
run: cmd= '[sudo,
-E,
-u,
oracle,
touch,
/u03/app/oracle/orabackup/temp-oda1-2023-08-02_13-27-57.0817]'
2023-08-02 13:27:57,859 DEBUG [Thread-120] [] c.o.d.c.u.CommonsUtils: Output :
sudo: pam_open_session: Permission denied
2023-08-02 13:27:57,859 DEBUG [Thread-120] [] c.o.d.c.u.CommonsUtils: Output :
sudo: policy plugin failed session initialization
2023-08-02 13:27:57,860 DEBUG [pool-5-dcsrpcworker_thread-11] [] c.o.d.c.u.c.DCSProcessBuilder: Return code: 1
2023-08-02 13:27:57,860 DEBUG [pool-5-dcsrpcworker_thread-11] [] c.o.d.c.u.c.CommandExecutor: Return code: 1
2023-08-02 13:27:57,860 DEBUG [pool-5-dcsrpcworker_thread-11] [] c.o.d.c.u.CommonsUtils: Output :
sudo: pam_open_session: Permission denied
sudo: policy plugin failed session initialization
2023-08-02 13:27:57,861 ERROR [pool-5-dcsrpcworker_thread-11] [] c.o.d.c.j.JsonRequestProcessor: RPC request invocation failed on request: {"classz":"com.oracle.dcs.agent.rpc.service.backup.BackupConfigActions","method":"checkNfsLocationAccesibility","params":[{"type":"java.lang.String","value":"/u03/app/oracle/orabackup"},{"type":"java.lang.String","value":"oracle"}],"revertable":false,"threadId":3475,"jsonInfo":{}}
com.oracle.dcs.commons.exception.DcsException: DCS-10074:User oracle does not have permission to access /u03/app/oracle/orabackup.
at com.oracle.dcs.commons.exception.DcsException$Builder.build(DcsException.java:150)
at com.oracle.dcs.agent.utils.AgentCommonUtils.isLocationAccessible(AgentCommonUtils.java:2708)
at com.oracle.dcs.agent.rpc.service.backup.BackupConfigActions.checkNfsLocationAccesibility(BackupConfigActions.java:308)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at com.oracle.dcs.commons.jrpc.JsonRequestProcessor.invokeRequest(JsonRequestProcessor.java:155)
at com.oracle.dcs.commons.jrpc.JsonRequestProcessor.process(JsonRequestProcessor.java:197)
at com.oracle.dcs.commons.jrpc.JsonRequestProcessor.process(JsonRequestProcessor.java:217)
at com.oracle.dcs.agent.rpc.DcsZkRpcWorker.run(DcsZkRpcWorker.java:161)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
at java.lang.Thread.run(Thread.java:7. 50
后经分析发现该错误由操作系统层权限引发,随检查/etc/pam.d/system-auth-ac文件并恢复到正确状态,
[root@oda2 pam.d]# more system-auth-ac
#%PAM-1.0
# This file is auto-generated.
# User changes will be destroyed the next time authconfig is run.
auth required pam_tally2.so deny=5 unlock_time=180 even_deny_root root_unlock_time=180
auth required pam_env.so
auth required pam_faildelay.so delay=2000000
auth sufficient pam_unix.so nullok try_first_pass
auth requisite pam_succeed_if.so uid >= 1000 quiet_success
auth required pam_deny.so
account required pam_unix.so
account sufficient pam_localuser.so
account sufficient pam_succeed_if.so uid < 1000 quiet
account required pam_permit.so
pssword requisite pam_cracklib.so try_first_pass retry=3 minlen=8 ucredit=-1 lcredit=-2 dcredit=-1 ocredit=-1
password requisite pam_pwquality.so try_first_pass local_users_only retry=3 authtok_type=
password sufficient pam_unix.so sha512 shadow nullok try_first_pass use_authtok
password required pam_deny.so
session optional pam_keyinit.so revoke
session required pam_limits.so
-session optional pam_systemd.so
session [success=1 default=ignore] pam_succeed_if.so service in crond quiet use_uid
session required pam_unix.so






















 915
915











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








