泰山杯 reverse_re1
拿到程序查壳,发现无壳,64位程序,先用ida静态分析,直接看主函数
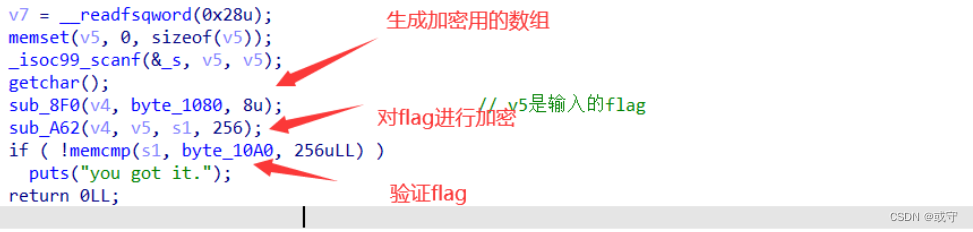
主函数的逻辑很清晰,那么先通过8F0函数计算v4数组,再计算flag
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-Zxu0y6TT-1667972234185)(C:\Users\HP\AppData\Roaming\Typora\typora-user-images\image-20221109132027917.png)]](https://img-blog.csdnimg.cn/e6b1c0af064047dd8f5275176ac01c0f.png)
qmemcpy(
((a1 + 2) & 0xFFFFFFFFFFFFFFF8LL), 、
(qword_F80 - (a1 - ((a1 + 2) & 0xFFFFFFFFFFFFFFF8LL))),
8LL * (((a1 - ((a1 + 8) & 0xFFFFFFF8) + 256) & 0xFFFFFFF8) >> 3));
三个参数,要拷贝的到位置的地址,内容所在的地址,拷贝的长度
8LL * (((a1 - ((a1 + 8) & 0xFFFFFFF8) + 256) & 0xFFFFFFF8) >> 3)
*8相当于<<3 再 >>3相当于没变
此处的就相当于是把qword_F80的数据全部拷贝到a1处,可以先看一下这个数组具体内容
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-7P0n8Tsv-1667972234186)(C:\Users\HP\AppData\Roaming\Typora\typora-user-images\image-20221109132440281.png)]](https://img-blog.csdnimg.cn/7b66bb08347b4ef9914ae8b9e66cd184.png)
看着很吓人,但是当我准备将数据导出时又发现
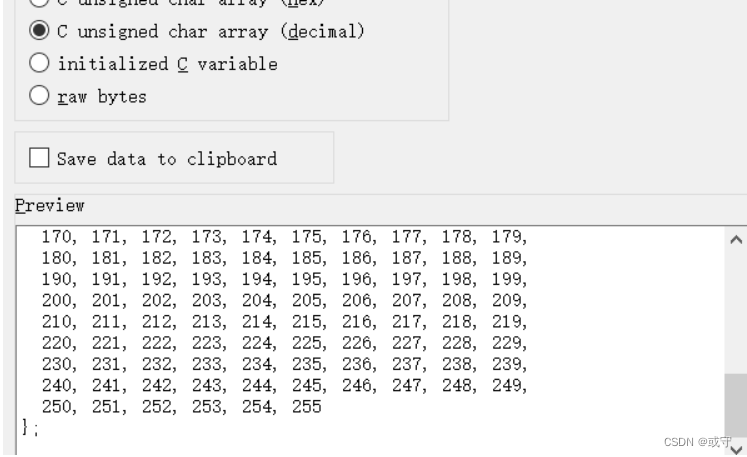
这些数据就是从0-255,结合下面对数组操作的部分,for ( i = 0; i <= 0xFF; ++i )是操作前256个数据
可以判断这前面一大堆东西就是对数组的初始化
for(int i=0;i<256;i++)
num1[i]=i;
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-nH4spcQ6-1667972234188)(C:\Users\HP\AppData\Roaming\Typora\typora-user-images\image-20221109132825013.png)]](https://img-blog.csdnimg.cn/03065e734d754061a2467b7c39e10749.png)
对数组的数据进行位置变换得到数组v4,再看最后一个计算的函数
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-oJR8RQav-1667972234189)(C:\Users\HP\AppData\Roaming\Typora\typora-user-images\image-20221109133512482.png)]](https://img-blog.csdnimg.cn/1f9617bb2b874877b572bb2b4e355f46.png)
#include<stdio.h>
#include<string.h>
int main()
{
int key[]={0x1,0x23,0x45,0x67,0x89,0xAB,0xCD,0xEF};
int num1[256];
int v5,v4=0;
int flag[256] =
{
0x12, 0xF8, 0xA3, 0x80, 0x6B, 0x2E, 0x69, 0x0A, 0x74, 0x24,
0xB7, 0x32, 0x53, 0xFC, 0x7A, 0x9D, 0xE8, 0x7B, 0x9B, 0x2E,
0xEF, 0xF3, 0x0B, 0x45, 0x63, 0x01, 0x35, 0xB7, 0x76, 0x8C,
0xCB, 0xD9, 0xC6, 0x8B, 0x8C, 0x2A, 0xA8, 0xAD, 0x67, 0x09,
0x5C, 0x0F, 0x52, 0xD4, 0x9D, 0x27, 0xC3, 0xD0, 0xC5, 0x91,
0xC0, 0xEA, 0xBF, 0x0D, 0xE7, 0x6C, 0x1A, 0x6A, 0x1A, 0x12,
0xB7, 0xB8, 0x18, 0xB9, 0x46, 0xC3, 0x5B, 0x90, 0x45, 0x7B,
0x94, 0xE6, 0x5F, 0x4F, 0xF0, 0x66, 0x78, 0xCC, 0xE9, 0xBE,
0x0B, 0x94, 0x84, 0x0F, 0x33, 0xAE, 0x97, 0x88, 0x45, 0x4E,
0xD2, 0x76, 0x11, 0x8E, 0x99, 0xFC, 0xCA, 0xD5, 0xE6, 0x27,
0x57, 0x74, 0x01, 0x98, 0x0A, 0xCD, 0x7F, 0x0D, 0xA2, 0xC5,
0xAB, 0xA2, 0x05, 0xA2, 0x86, 0xD3, 0x0E, 0x3A, 0x8E, 0xBA,
0xCC, 0x43, 0xA0, 0xBC, 0x30, 0x1C, 0x7B, 0x42, 0x02, 0xDC,
0xA4, 0xAA, 0x06, 0x89, 0x97, 0xAF, 0x81, 0xC0, 0x8A, 0x0B,
0xF7, 0x6C, 0xFE, 0x30, 0x97, 0x17, 0xEA, 0x79, 0x4F, 0x48,
0x5B, 0xD3, 0xCF, 0x91, 0xD6, 0xF6, 0x73, 0xA9, 0x16, 0x46,
0xB7, 0x5E, 0x63, 0x08, 0x3A, 0x1F, 0x0C, 0xB8, 0xE4, 0xBB,
0x52, 0x2E, 0xAE, 0xED, 0x46, 0x51, 0x82, 0x22, 0xE7, 0x70,
0x33, 0x7C, 0xF8, 0x45, 0x45, 0x33, 0xCA, 0x72, 0x66, 0xCF,
0xC9, 0x2E, 0x5C, 0x45, 0xC1, 0xD1, 0x0A, 0x66, 0xD7, 0x51,
0xA1, 0x74, 0xCC, 0x4A, 0x71, 0xDF, 0xDC, 0x76, 0xEA, 0x9A,
0x11, 0x22, 0x1A, 0x6A, 0x5A, 0x75, 0x12, 0x46, 0x38, 0x6C,
0x63, 0x88, 0x75, 0x20, 0xD5, 0x3C, 0xF8, 0xB5, 0x2F, 0x45,
0x6F, 0x34, 0x8F, 0x9D, 0x10, 0xA8, 0xB3, 0x19, 0x4F, 0xCA,
0xEE, 0x0D, 0xD9, 0xE6, 0xA9, 0x76, 0xEE, 0x97, 0x8E, 0x12,
0x91, 0xED, 0x9A, 0x3C, 0x34, 0xA4
};
char str[]="";
for(int i=0;i<256;i++)
num1[i]=i;
for(int i=0;i<256;i++)
{
v4=(v4+(num1[i]+key[i%8]))%256;
v5=num1[i];
num1[i]=num1[v4];
num1[v4]=v5;
}
int a=1;int b=0;int c;
for(int i=1;i<257;i++)
{
b=(b+num1[i])%256;
c=num1[i];
num1[i]=num1[b];
num1[b]=c;
//flag[i-1]=in[i-1]^num1[num1[b]+num1[i]]
str[i-1]=flag[i-1]^num1[(num1[b]+num1[i])%256];
}
printf("%s\n",str);
flag{easyobaasdasasfas7214}




















 2833
2833











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








