一、无CA认证
1.配置docker远程连接端口
vi /usr/lib/systemd/system/docker.service
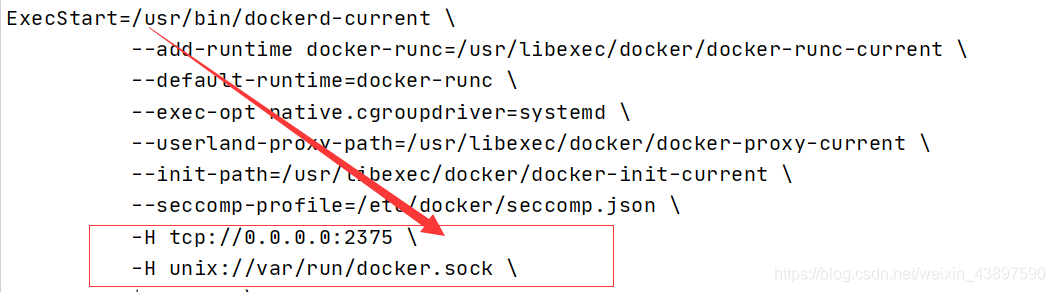
2.找到 ExecStart,在最后面添加 -H tcp://0.0.0.0:2375 \ -H unix://var/run/docker.sock \
如下图所示
3.重启docker
systemctl daemon-reload
systemctl restart docker
4.开放端口
firewall-cmd --zone=public --add-port=2375/tcp --permanent
systemctl restart firewalld.service
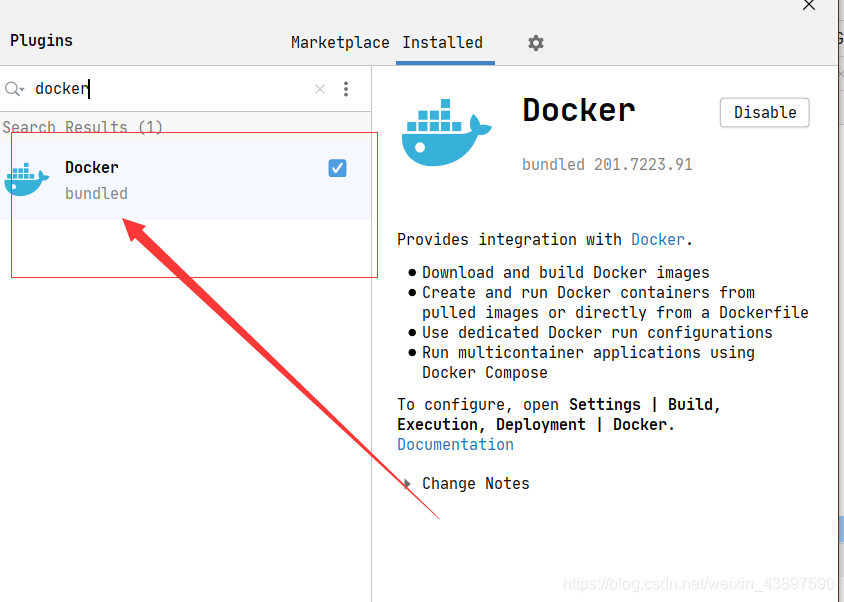
5.Idea安装插件,重启
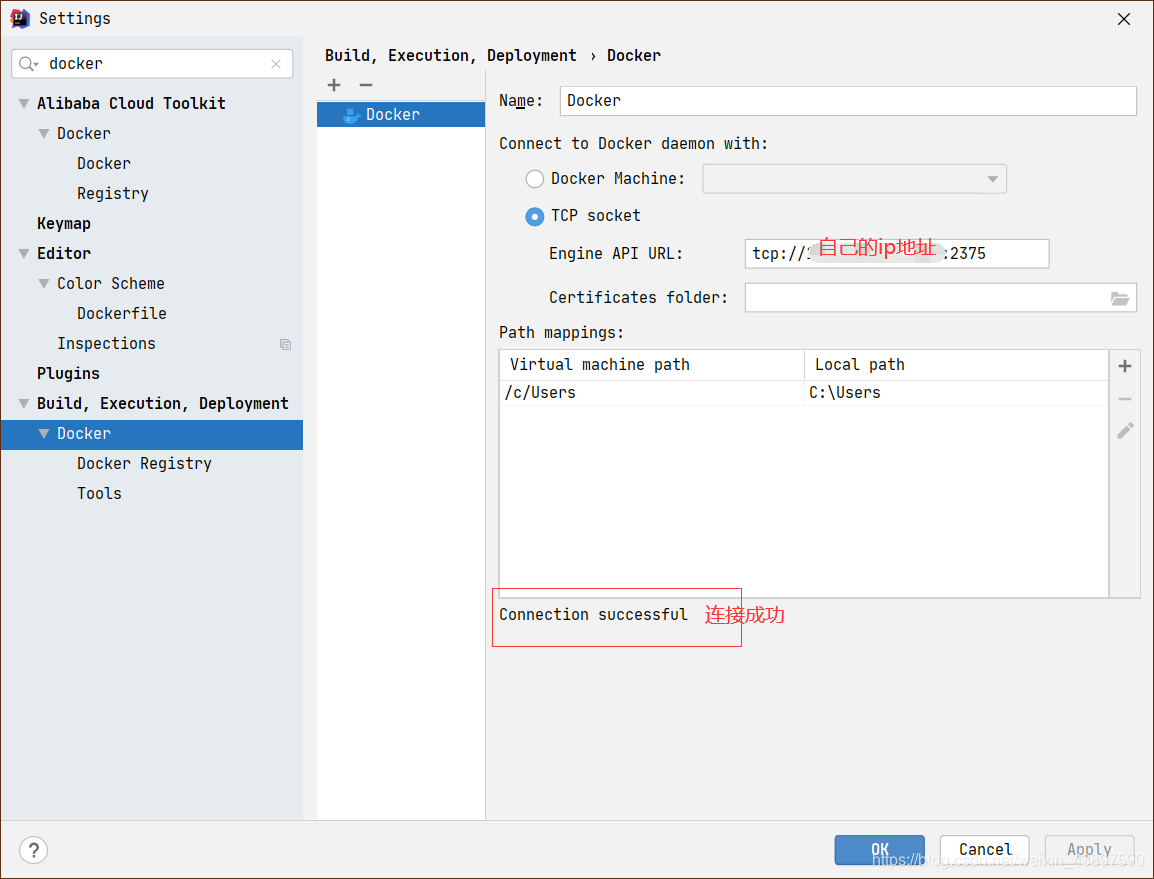
6.连接远程docker
7.编写DockerFile文件,放在src/main/docker下面
# Docker image for springboot application
# VERSION 0.0.1
# Author: sxy
### 基础镜像,后面是jdk版本,可自由选择
FROM openjdk:11.0.6
#作者
MAINTAINER sxy
#系统编码
ENV LANG=C.UTF-8 LC_ALL=C.UTF-8
#声明一个挂载点,容器内此路径会对应宿主机的某个文件夹
VOLUME /tmp
#应用构建成功后的jar文件被复制到镜像内,名字也改成了app.jar
ADD *.jar app.jar
#启动容器时的进程
ENTRYPOINT ["java","-Djava.security.egd=file:/dev/./urandom","-jar","/app.jar","--spring.profiles.active=prod"]
#暴露8080端口
EXPOSE 8081
创建DockerController文件
@RestController
public class DockerController {
static Log log = LogFactory.getLog(DockerController.class);
@RequestMapping("/")
public String index() {
log.info("Hello Docker!");
return "Hello Docker!";
}
}
8.增加配置docker


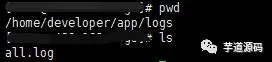
命令解释 Image tag : 指定镜像名称和tag,镜像名称为 docker-demo,tag为1.1 Bind ports : 绑定宿主机端口到容器内部端口。格式为[宿主机端口]:[容器内部端口] Bind mounts : 将宿主机目录挂到到容器内部目录中。格式为[宿主机目录]:[容器内部目录]。这个springboot项目会将日志打印在容器 /home/developer/app/logs/ 目录下,将宿主机目录挂载到容器内部目录后,那么日志就会持久化容器外部的宿主机目录中。
9.在resource目录下创建application.yml文件,添加logback配置文件
logging:
config: classpath:logback-spring.xml
1.logback配置文件内容,可以在application.yml更改生产环境,会根据环境的不同更改日志保存位置,文件名必须为logback-spring.xml

11.配置pom文件
<plugins>
<plugin>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-maven-plugin</artifactId>
<configuration>
<fork>true</fork> <!-- 如果没有该配置,devtools不会生效 -->
<mainClass>com.demo.springboot.SpringbootApplication</mainClass>
</configuration>
<executions>
<execution>
<goals>
//这个不配配置可能找不到主类
<goal>repackage</goal>
</goals>
</execution>
</executions>
</plugin>
<plugin>
<groupId>org.apache.maven.plugins</groupId>
<artifactId>maven-surefire-plugin</artifactId>
<configuration>
<skip>true</skip>
<testFailureIgnore>true</testFailureIgnore>
</configuration>
</plugin>
<!--使用docker-maven-plugin插件-->
<plugin>
<groupId>com.spotify</groupId>
<artifactId>docker-maven-plugin</artifactId>
<version>1.0.0</version>
<configuration>
<dockerDirectory>src/main/docker</dockerDirectory>
<imageTags>
<imageTag>${project.version}</imageTag>
<imageTag>latest</imageTag>
</imageTags>
<resources>
<resource>
<targetPath>/</targetPath>
<directory>${project.build.directory}</directory>
<include>${project.build.finalName}.jar</include>
</resource>
</resources>
</configuration>
</plugin>
<plugin>
<artifactId>maven-antrun-plugin</artifactId>
<executions>
<execution>
<phase>package</phase>
<configuration>
<target>
<copy todir="src/main/docker"
file="target/${project.artifactId}.${project.packaging}"/>
</target>
</configuration>
<goals>
<goal>run</goal>
</goals>
</execution>
</executions>
</plugin>
</plugins>
12.Maven打包

13.运行

14.先pull基础镜像,然后再打包镜像,并将镜像部署到远程docker运行

15.运行成功

16.浏览器访问
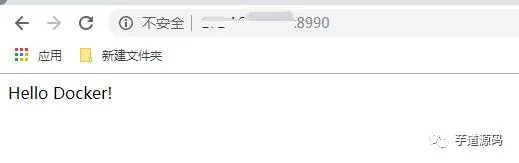
日志查看
二、Docker CA认证
前面提到的配置是允许所有人都可以访问的,因为docker默认是root权限的,你把2375端口暴露在外面,意味着别人随时都可以提取到你服务器的root权限,是很容易被黑客黑的,因此,docker官方推荐使用加密的tcp连接,以Https的方式与客户端建立连接
官方demo
1、创建ca文件夹,存放CA私钥和公钥
[root@localhost ~]# mkdir -p /usr/local/ca
[root@localhost ~]# cd /usr/local/ca/
2、创建密码
需要连续输入两次相同的密码
[root@localhost ca]# openssl genrsa -aes256 -out ca-key.pem 4096
Generating RSA private key, 4096 bit long modulus
...................++
..........................................................................................................................................................................................................................................................................................................................................................++
e is 65537 (0x10001)
Enter pass phrase for ca-key.pem:
Verifying - Enter pass phrase for ca-key.pem:
3、依次输入密码、国家、省、市、组织名称等
[root@localhost ca]# openssl req -new -x509 -days 365 -key ca-key.pem -sha256 -out ca.pem
Enter pass phrase for ca-key.pem:
Enter pass phrase for ca-key.pem:
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [XX]:CN
State or Province Name (full name) []:zj
Locality Name (eg, city) [Default City]:hz
Organization Name (eg, company) [Default Company Ltd]:qdsg
Organizational Unit Name (eg, section) []:qdsg
Common Name (eg, your name or your server's hostname) []:qdsg
Email Address []:1@qq.com
[root@localhost ca]# openssl genrsa -out server-key.pem 4096
Generating RSA private key, 4096 bit long modulus
...........................++
................++
e is 65537 (0x10001)
4、生成server-key.pem
[root@localhost ca]# openssl genrsa -out server-key.pem 4096
Generating RSA private key, 4096 bit long modulus
.................................................................................................................................................++
.................................................++
e is 65537 (0x10001)
5、把下面的$Host换成你自己服务器外网的IP或者域名
openssl req -subj “/CN=$HOST” -sha256 -new -key server-key.pem -out server.csr
比如
openssl req -subj “/CN=192.168.1.106” -sha256 -new -key server-key.pem -out server.csr
或
openssl req -subj “/CN=www.baidu.com” -sha256 -new -key server-key.pem -out server.csr
我这里使用局域网进行测试
[root@localhost ca]# openssl req -subj "/CN=192.168.1.106" -sha256 -new -key server-key.pem -out server.csr
6、配置白名单
也就是你接下来要允许那些ip可以连接到服务器的docker,因为已经是ssl连接,所以我推荐配置0.0.0.0,也就是所有ip都可以连接(但只有拥有证书的才可以连接成功),这样配置好之后公司其他人也可以使用。如果你不想这样,那你可以配置ip,用逗号分隔开。下面的$Host依旧是你服务器外网的IP或者域名,请自行替换。
注意!!!!这里我踩了坑
如果你填写的是ip地址的话命令如下echo subjectAltName = IP:$HOST,IP:0.0.0.0 >> extfile.cnf
如果你填写的是ip地址的话命令如下echo subjectAltName = IP:$HOST,IP:0.0.0.0 >> extfile.cnf
我这里使用局域网进行测试
[root@localhost ca]# echo subjectAltName = IP:192.168.1.106,IP:0.0.0.0 >> extfile.cnf
7、执行命令,将Docker守护程序密钥的扩展使用属性设置为仅用于服务器身份验证
[root@localhost ca]# echo extendedKeyUsage = serverAuth >> extfile.cnf
8、执行命令,并输入之前设置的密码,生成签名证书
[root@localhost ca]# openssl x509 -req -days 365 -sha256 -in server.csr -CA ca.pem -CAkey ca-key.pem \-CAcreateserial -out server-cert.pem -extfile extfile.cnf
Signature ok
subject=/CN=192.168.1.106
Getting CA Private Key
Enter pass phrase for ca-key.pem:
9、生成客户端的key.pem,到时候把生成好的几个公钥私钥拷出去即可
[root@localhost ca]# openssl genrsa -out key.pem 4096
Generating RSA private key, 4096 bit long modulus
...........................................................................................................................................................................................................................................................................................................................................................................++
......................................................................................................................................++
e is 65537 (0x10001)
10、执行命令
[root@localhost ca]# openssl req -subj '/CN=client' -new -key key.pem -out client.csr
11、执行命令,要使密钥适合客户端身份验证,请创建扩展配置文件
[root@localhost ca]# echo extendedKeyUsage = clientAuth >> extfile.cnf
12、生成cert.pem,需要输入前面设置的密码,生成签名证书
[root@localhost ca]# openssl x509 -req -days 365 -sha256 -in client.csr -CA ca.pem -CAkey ca-key.pem \-CAcreateserial -out cert.pem -extfile extfile.cnf
Signature ok
subject=/CN=client
Getting CA Private Key
Enter pass phrase for ca-key.pem:
13、删除不需要的文件,两个证书签名请求
[root@localhost ca]# rm -v client.csr server.csr
rm:是否删除普通文件 "client.csr"?y
已删除"client.csr"
14、修改权限,要保护您的密钥免受意外损坏,请删除其写入权限。要使它们只能被您读取,更改文件模式
[root@localhost ca]# chmod -v 0400 ca-key.pem key.pem server-key.pem
mode of "ca-key.pem" changed from 0644 (rw-r--r--) to 0400 (r--------)
mode of "key.pem" changed from 0644 (rw-r--r--) to 0400 (r--------)
mode of "server-key.pem" changed from 0644 (rw-r--r--) to 0400 (r--------)
证书可以是对外可读的,删除写入权限以防止意外损坏
[root@localhost ca]# chmod -v 0444 ca.pem server-cert.pem cert.pem
mode of "ca.pem" changed from 0644 (rw-r--r--) to 0444 (r--r--r--)
mode of "server-cert.pem" changed from 0644 (rw-r--r--) to 0444 (r--r--r--)
mode of "cert.pem" changed from 0644 (rw-r--r--) to 0444 (r--r--r--)
15、归集服务器证书
[root@localhost ca]# cp server-*.pem /etc/docker/
[root@localhost ca]# cp ca.pem /etc/docker/
16、修改Docker配置,使Docker守护程序仅接受来自提供CA信任的证书的客户端的连接
[root@localhost ca]# vim /lib/systemd/system/docker.service
将
ExecStart=/usr/bin/dockerd或者ExecStart=/usr/bin/dockerd-current
替换为:
ExecStart=/usr/bin/dockerd --tlsverify --tlscacert=/etc/docker/ca.pem --tlscert=/etc/docker/server-cert.pem --tlskey=/etc/docker/server-key.pem -H tcp://0.0.0.0:2376 -H unix:///var/run/docker.sock
或者
ExecStart=/usr/bin/dockerd-current --tlsverify --tlscacert=/etc/docker/ca.pem --tlscert=/etc/docker/server-cert.pem --tlskey=/etc/docker/server-key.pem -H tcp://0.0.0.0:2376 -H unix:///var/run/docker.sock
17、重新加载daemon并重启docker
[root@localhost ~]# systemctl daemon-reload
[root@localhost ~]# systemctl restart docker
18、开放2376端口
[root@localhost ca]# /sbin/iptables -I INPUT -p tcp --dport 2376 -j ACCEPT
[root@localhost ca]# iptables-save
# Generated by iptables-save v1.4.21 on Wed Oct 17 14:47:38 2018
*nat
:PREROUTING ACCEPT [225:14836]
:INPUT ACCEPT [225:14836]
:OUTPUT ACCEPT [1:76]
:POSTROUTING ACCEPT [1:76]
:DOCKER - [0:0]
-A PREROUTING -m addrtype --dst-type LOCAL -j DOCKER
-A OUTPUT ! -d 127.0.0.0/8 -m addrtype --dst-type LOCAL -j DOCKER
-A POSTROUTING -s 172.17.0.0/16 ! -o docker0 -j MASQUERADE
-A DOCKER -i docker0 -j RETURN
COMMIT
# Completed on Wed Oct 17 14:47:38 2018
# Generated by iptables-save v1.4.21 on Wed Oct 17 14:47:38 2018
*filter
:INPUT ACCEPT [8:2858]
:FORWARD DROP [0:0]
:OUTPUT ACCEPT [39:30400]
:DOCKER - [0:0]
:DOCKER-ISOLATION-STAGE-1 - [0:0]
:DOCKER-ISOLATION-STAGE-2 - [0:0]
:DOCKER-USER - [0:0]
-A INPUT -p tcp -m tcp --dport 2376 -j ACCEPT
-A INPUT -p tcp -m tcp --dport 2375 -j ACCEPT
-A FORWARD -j DOCKER-USER
-A FORWARD -j DOCKER-ISOLATION-STAGE-1
-A FORWARD -o docker0 -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT
-A FORWARD -o docker0 -j DOCKER
-A FORWARD -i docker0 ! -o docker0 -j ACCEPT
-A FORWARD -i docker0 -o docker0 -j ACCEPT
-A DOCKER-ISOLATION-STAGE-1 -i docker0 ! -o docker0 -j DOCKER-ISOLATION-STAGE-2
-A DOCKER-ISOLATION-STAGE-1 -j RETURN
-A DOCKER-ISOLATION-STAGE-2 -o docker0 -j DROP
-A DOCKER-ISOLATION-STAGE-2 -j RETURN
-A DOCKER-USER -j RETURN
COMMIT
# Completed on Wed Oct 17 14:47:38 2018
19、重启docker
[root@localhost ca]# service docker restart
20、保存相关客户端的pem文件到本地

21、idea的配置,注意使用的https连接的

22、若出现以下错误,请查看前面的步骤是否遗漏或出错






















 2279
2279











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








