前期准备
| 节点名称 | 节点ip | vip | mac地址 |
|---|---|---|---|
| lvs节点 | 10.10.10.3 | 10.10.10.250 | fa:16:3e:a8:a1:27 |
| web servier1 | 10.10.10.4 | 10.10.10.250 | fa:16:3e:2e:0e:ce |
| web servier2 | 10.10.10.5 | 10.10.10.250 | fa:16:3e:62:56:ce |
| client | 10.10.10.10 | - | fa:16:3e:05:b0:38 |
二、配置
2.1、创建vip
neutron port-create --fixed-ip ip_address=10.10.10.250 db647283-85c2-4377-880f-da59d925b430
#更改端口信息
neutron port-update 5392e500-1b61-401a-a157-bb76bed7f83a --allowed-address-pairs type=dict list=true ip_address=10.10.10.250
neutron port-update 1334a7f5-8cd5-425b-a517-c7babd078f0e --allowed-address-pairs type=dict list=true ip_address=10.10.10.250
neutron port-update f6c46789-4c28-4cbe-adc1-1e54eac99602 --allowed-address-pairs type=dict list=true ip_address=10.10.10.250
2.2、web servier安装http
#两台web均操作
#安装httpd
yum install http
#更改配置
echo 'Welcome to Apache 10.10.10.4 !!!' > /var/www/html/index.html
#启动httpd
systemctl start httpd
#测试
curl 10.10.10.4 80
2.3、配置lvs节点
关闭网络管理器
systemctl stop NetworkManager
systemctl disable NetworkManager
给当前网卡取别名
cp /etc/sysconfig/network-scripts/ifcfg-eth0 /etc/sysconfig/network-scripts/ifcfg-eth0:1
#配置如下
cat /etc/sysconfig/network-scripts/ifcfg-eth0:1
OTPROTO="static"
DEVICE="eth0:1"
ONBOOT="yes"
IPADDR="10.10.10.250"
NETMASK="255.255.255.0"

安装 ipvsadm
# 安装ipvsadm
yum install -y ipvsadm
#验证
ipvsadm -ln

配置lvs节点的集群规则
添加lvs集群服务器,配置规则为轮询
ipvsadm --add-service --tcp-service 10.10.10.250:80 --scheduler rr
#查看是否生效
ipvsadm -ln

为虚拟服务器10.10.10.250:80 添加真实服务器节点,配置dr模式
ipvsadm --add-server --tcp-service 10.10.10.250:80 --real-server 10.10.10.4:80 --gatewaying
ipvsadm --add-server --tcp-service 10.10.10.250:80 --real-server 10.10.10.5:80 --gatewaying
#查询是否配置成功
ipvsadm -ln

将配置保存到规则库中,否则重启将失效
ipvsadm --save
配置Real servers节点(4,5)的回环ip
复制一份lo网卡(回环地址网卡),取别名
cp /etc/sysconfig/network-scripts/ifcfg-lo /etc/sysconfig/network-scripts/ifcfg-lo:1
#配置如下
cat ifcfg-lo:1
DEVICE=lo:1
IPADDR=10.10.10.250
NETMASK=255.255.255.255
NETWORK=127.0.0.0
# If you're having problems with gated making 127.0.0.0/8 a martian,
# you can change this to something else (255.255.255.255, for example)
BROADCAST=127.255.255.255
ONBOOT=yes
NAME=loopback
#从新加载环路地址
ifup lo 或者 systemctl restart network
#查看是否生效
ip a

第二台同样的配置

配置Real servers节点(4,5)的ARP响应级别
#打开arp配置文件
vim /etc/sysctl.conf
#添加以下配置
# configration for lvs
net.ipv4.conf.all.arp_ignore = 1
net.ipv4.conf.default.arp_ignore = 1
net.ipv4.conf.lo.arp_ignore = 1
net.ipv4.conf.all.arp_announce = 2
net.ipv4.conf.default.arp_announce = 2
net.ipv4.conf.lo.arp_announce = 2
# 加载arp配置
sysctl -p
ARP(Address Resolution Protocol,地址解析协议) 配置解释
#arp-ignore 级别 筛选请求
0:只要本机配置了ip,就能响应请求
1:请求的目标地址到达对应的网络接口,才会响应请求
#arp-annouce 级别 通告行为
0:本机上任何网络接口都向外通告,所有的网卡都能接受到通告
1:尽可能避免本网卡与不匹配的目标进行通告
2:只在本网卡通告(回环)
增加路由
#用于接收数据报文,当有请求到本机后,会交给lo去处理
route add -host 10.10.10.250 dev lo:1
#配置永久路由
echo "route add -host 10.10.10.250 dev lo:1" >> /etc/rc.local
tail -n 1 /etc/rc.local
source /etc/rc.local
#查看你是否配置成功
route -n

三、测试
client节点访问vip的80端口
curl 10.10.10.250:80

lvs节点查看转发到real servier1上

client节点抓包,有出包没有回包
client—>lvs节点

lvs节点抓包,有进有出
lvs节点返回了real servier1节点的mac地址
client—>lvs
lvs–real servier1 mac–>client

real servier节点无进包也无出包

lvs对应的计算节点抓包
tap口有进包和出包
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-UdStZBlS-1663390744496)(lvs+dr直接路由模式测试.assets/image-20220915144822044.png)]](https://img-blog.csdnimg.cn/dada1bed571343d793183b64a79529f7.png)
qbr抓包有进有出
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-5JyBCNbl-1663390744497)(lvs+dr直接路由模式测试.assets/image-20220915150452532.png)]](https://img-blog.csdnimg.cn/f661bdd6d3df4ba5bc08a9da413f0a1f.png)
qvb有进包无回包
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-8dqEz3yz-1663390744497)(lvs+dr直接路由模式测试.assets/image-20220915144644439.png)]](https://img-blog.csdnimg.cn/fe93a0803b9249a39cca4a47a56945a5.png)
lvs节点vip及虚机安全组规则全放
四、结论
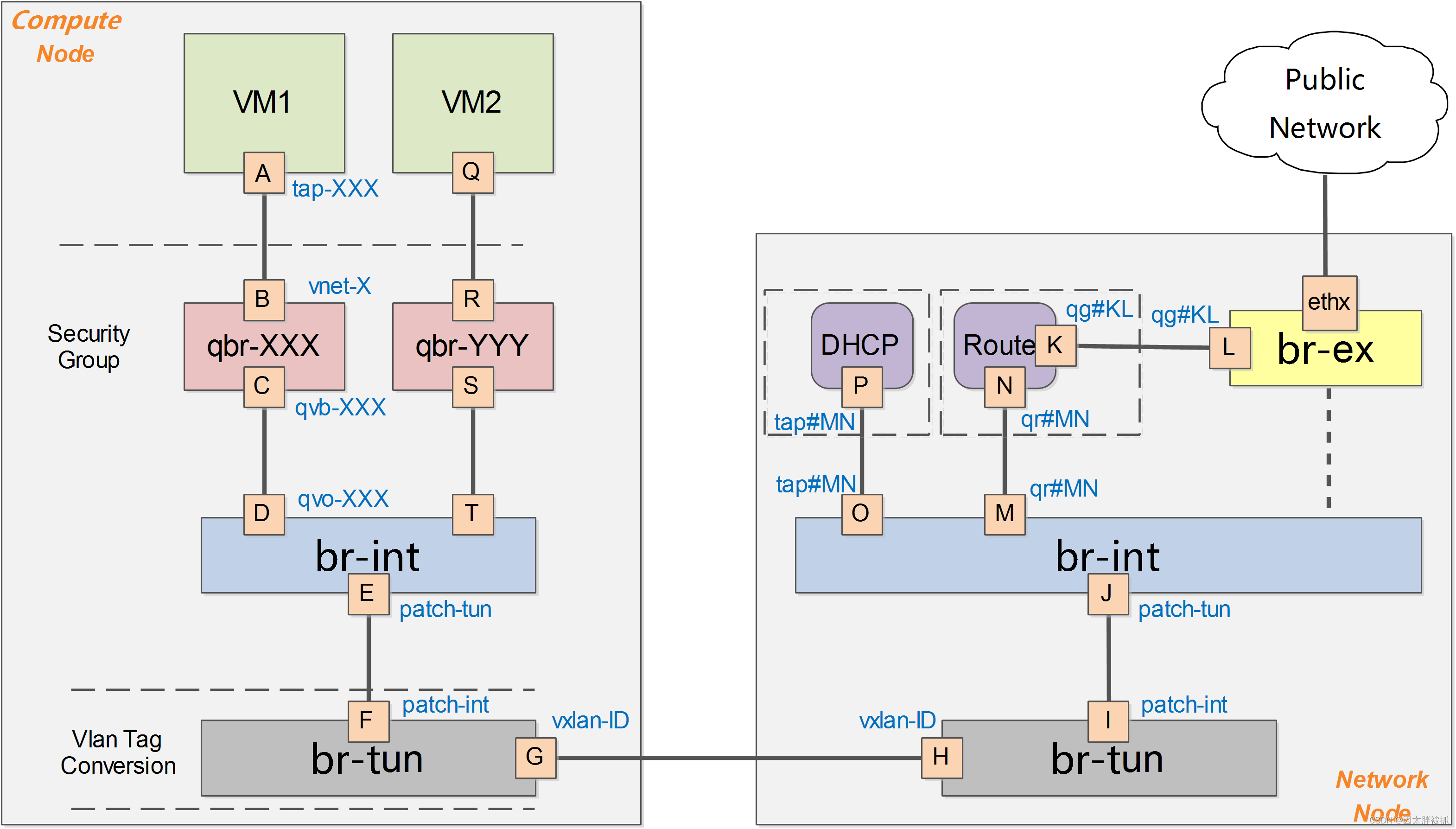
lvs虚机对应的计算节点qbr到qvb之间把回包丢弃了,导致client没有收到回报导致超时
五、解决方法
5.1、概述
根据抓包情况基本判断,在LVS DR模式下,Direct会产生不完整的TCP连接(RS直接回包给Client),计算节点上Neutron默认会在安全组规则中添加一条防火墙策略检测TCP连接状态,经过状态检测后认为连接是无效状态的,就会将包丢弃,导致无法正常通信,因此需要修改Neutron代码使其不添加相关防火墙策略,并更新所有节点节点的Neutron服务
5.2、变更
方法一
备份计算节点neutron代码
- lvs计算节点
#备份neutron代码
cp /usr/lib/python2.7/site-packages/neutron/agent/linux/iptables_firewall.py /usr/lib/python2.7/site-packages/neutron/agent/linux/iptables_firewall.py-20220915
更改代码
#注释
sed -i 's/ self._setup_spoof_filter_chain/ #self._setup_spoof_filter_chain/g' /usr/lib/python2.7/site-packages/neutron/agent/linux/iptables_firewall.py
sed -i 's/ mac_ipv4_pairs, ipv4_rules/ #mac_ipv4_pairs, ipv4_rules/g' /usr/lib/python2.7/site-packages/neutron/agent/linux/iptables_firewall.py
sed -i 's/ mac_ipv6_pairs, ipv6_rules/ #mac_ipv6_pairs, ipv6_rules/g' /usr/lib/python2.7/site-packages/neutron/agent/linux/iptables_firewall.py
sed -i 's/ self._drop_invalid_packets/ #self._drop_invalid_packets/g' /usr/lib/python2.7/site-packages/neutron/agent/linux/iptables_firewall.py
#查看是否注释
grep -rn "self._setup_spoof_filter_chain" /usr/lib/python2.7/site-packages/neutron/agent/linux/iptables_firewall.py
grep -rn "mac_ipv4_pairs, ipv4_rules" /usr/lib/python2.7/site-packages/neutron/agent/linux/iptables_firewall.py
grep -rn "mac_ipv6_pairs, ipv6_rules" /usr/lib/python2.7/site-packages/neutron/agent/linux/iptables_firewall.py
grep -rn "self._drop_invalid_packets" /usr/lib/python2.7/site-packages/neutron/agent/linux/iptables_firewall.py
##重启服务
systemctl status neutron-openvswitch-agent.service
方法二
获取lvs虚机的端口
#获取port uuid
nova interface-list fbdd2f7e-f7c9-4a9b-9d81-9ddac0e2e6d6
# neutron port-show 查看
neutron port-show 5392e500-1b61-401a-a157-bb76bed7f83a
关闭安全组
#清除allowed-address
openstack port set --no-allowed-address 5392e500-1b61-401a-a157-bb76bed7f83a
#删除安全组
neutron port-update 5392e500-1b61-401a-a157-bb76bed7f83a --no-security-groups
neutron port-update 5392e500-1b61-401a-a157-bb76bed7f83a --port-security-enabled=False
(lvs+dr直接路由模式测试.assets/image-20220915163421428.png)]](https://img-blog.csdnimg.cn/050377f2a58a4c8c91260a4b8cfc22f1.png)






















 549
549











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








